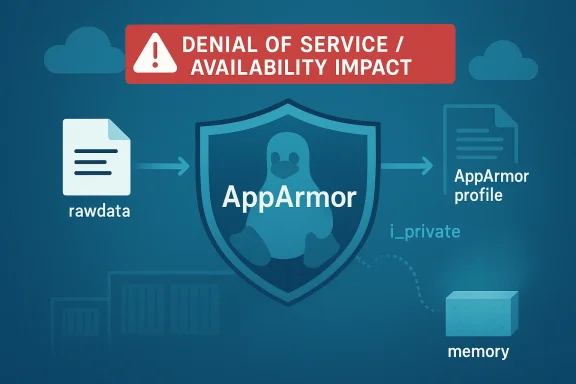
In this article, I'll explain the significance of CVE-2026-23410, a Linux kernel AppArmor race condition that can turn into a use-after-free and, under the right circumstances, a serious denial-of-service or even broader compromise vector. The issue sits in a subtle corner of AppArmor’s profile-loading machinery, where a file open can race against profile removal and leave a stale pointer behind. Microsoft’s update guide frames the impact in availability terms, but the upstream kernel description and downstream advisories suggest the risk profile is broader than a simple crash bug, especially on systems that rely heavily on AppArmor-managed policy churn. (nvd.nist.gov)
CVE-2026-23410 is one of those kernel vulnerabilities that looks narrow on the surface and deeply architectural underneath. The immediate flaw is a race in AppArmor’s rawdata handling: rawdata inodes were not refcounted, so an attacker could begin opening one of the rawdata files while another thread or process removed the last reference to the underlying data structure. That left
The vulnerability matters because it hits a security boundary component that is supposed to enforce policy, not become a source of instability. AppArmor is an LSM, so weaknesses in its lifecycle management can affect systems that assume kernel-enforced confinement is dependable even under hostile local activity. Ubuntu’s April 9, 2026 advisory for its Azure FIPS kernel explicitly groups CVE-2026-23410 with other AppArmor issues and warns that an unprivileged local attacker could use them to load, replace, or remove arbitrary profiles, leading to denial of service, memory exposure, local privilege escalation, or possible container escape. (ubuntu.com)
The kernel fix is conceptually elegant: move to a double refcount scheme. In other words, AppArmor needed a way to preserve the rawdata object long enough for open file handles to finish safely, without reintroducing the circular dependency that original design tried to avoid. That design tension is important because it shows the bug was not a typo-level mistake, but a correctness compromise in lifecycle ownership. (nvd.nist.gov)
What makes this especially relevant for WindowsForum readers is the broader lesson for mixed-platform infrastructure. If you run Linux guests, containers, or edge workloads under Microsoft Azure or alongside Windows management tooling, kernel security issues like this are not isolated Linux problems; they can become workload, tenancy, and availability problems at the platform level. Microsoft’s own update guide for the CVE emphasizes total loss of availability as the impact class, which is exactly the kind of operationally visible failure admins care about most when a local bug can destabilize shared or protected services.
The rawdata subsystem exists to represent loaded AppArmor profile data in a form that can be inspected and managed. The challenge is that the rawdata object is referenced by both the profile and the inodes exposed to userspace, and those relationships can easily become circular if they are modeled too naively. The kernel note says rawdata inodes were intentionally left unrefcounted to avoid circular refcounting, but that tradeoff created a race window during profile removal. (nvd.nist.gov)
That tradeoff is common in kernel engineering. Refcounting solves lifetime management, but overdoing it can create leaks, while underdoing it creates use-after-free conditions or stale pointer dereferences. In this case, the object graph was stable most of the time, which is exactly why bugs like this survive: the failure mode only appears when one thread is opening rawdata while another is tearing down the corresponding profile. That kind of timing sensitivity is the hallmark of a hard-to-reproduce kernel race.
Downstream vendors quickly recognized the issue as part of a larger AppArmor cleanup cycle. Ubuntu’s advisory packages CVE-2026-23410 with several adjacent AppArmor vulnerabilities, suggesting a focused review of profile lifecycle and mediation logic rather than an isolated one-off flaw. That clustering matters because vulnerabilities often emerge in families: once one race is found, adjacent state transitions tend to deserve suspicion too. (ubuntu.com)
The timing also matters. NVD records the CVE as received from kernel.org on April 1, 2026, with a later modification on April 2 to add the CNA’s CVSS 3.1 score of 7.8 High. Ubuntu published its corresponding advisory on April 9, 2026. That sequence tells us the issue moved from upstream disclosure to vendor response quickly, but not instantaneously, which is typical for kernel flaws that require downstream packaging and validation. (nvd.nist.gov)
A useful mental model is this: the inode is like a library card, while the underlying rawdata is like the book. If the library card is still valid but the book has already been destroyed, the next reader gets a meaningless pointer instead of content. The kernel description makes clear that AppArmor intended the profile’s rawdata reference to keep things alive, but teardown created a gap where VFS and profile destruction could race each other. (nvd.nist.gov)
What makes that gap exploitable is not just the race itself, but the ability to influence timing. Local attackers can often stress the kernel with repeated opens, concurrent removals, or workload patterns that increase the chance of hitting the critical window. Once a race is in play, reliability becomes part of exploitability.
The important insight is that “avoid circular refcounts” is not the same as “avoid all extra refcounts.” The fix introduces a double refcount scheme, where one counter handles the inode-level lifetime and another uses the profile reference to break the cycle. That is a classic kernel compromise: preserve correctness without resurrecting the very leak pattern the original code was trying to dodge. (nvd.nist.gov)
NVD has not yet assigned its own score, but the CNA scoring from kernel.org is CVSS 3.1 7.8 High with
The key distinction is between theoretical severity and operational exploitability. Even if the most obvious outcome is a crash, a local attacker who can repeatedly trigger the condition may still create persistent service instability, especially in container hosts or appliance-style deployments where AppArmor is heavily used. That is why administrators should treat this as a kernel memory-safety issue, not merely a nuisance bug.
Downstream vendors also treat it as part of a broader AppArmor risk surface. Ubuntu’s advisory states that a local attacker could use several AppArmor issues to load, replace, and remove profiles, with consequences ranging from denial of service to privilege escalation or container escape. While that statement covers multiple CVEs, it reinforces the idea that AppArmor lifecycle bugs can have more than one operational outcome. (ubuntu.com)
That said, double refcounting is not a free lunch. It adds bookkeeping, and bookkeeping bugs can be introduced elsewhere if the release paths are not symmetrical. Kernel maintainers typically accept that tradeoff when the alternative is a use-after-free in a security-sensitive subsystem, but it reinforces how hard lifecycle management can be in mature codebases.
The change also reveals a subtle lesson about security engineering: the right fix is often not “add a lock everywhere.” Locks can serialize behavior, but they do not automatically solve ownership semantics across multiple subsystems. In this case, the authors chose a lifetime model repair instead of a concurrency band-aid, which is usually a healthier long-term answer.
That is why Microsoft’s framing is useful: it maps a kernel bug to a business outage. Even if the exploit is local, the blast radius can be much wider when the vulnerable system is part of a larger service fabric. The practical consequence is often not “someone got a shell,” but “a node became unreliable at exactly the wrong time.”
It is also important not to overread the Microsoft text as the complete technical story. The upstream and downstream Linux sources describe a use-after-free, and the CNA score suggests high confidentiality and integrity impact as well. The best reading is that Microsoft is emphasizing the observable impact class, while the kernel community is characterizing the underlying memory-safety risk more broadly. (nvd.nist.gov)
For cloud operators, that means maintenance windows, workload autoscaling, and rolling deployments all deserve more scrutiny. Systems that frequently load and unload AppArmor profiles could be more exposed to practical race conditions simply because they hit the dangerous timing more often. Higher operational churn often equals higher bug discoverability.
That does not mean organizations should avoid AppArmor. It means they should recognize that mandatory access control is only as reliable as its lifecycle management. Patching these bugs is part of preserving the credibility of the hardening story, not an admission that the model itself failed.
The CVE also shows why kernel hardening is rarely a one-line story. The upstream fix is simple to describe, but the surrounding design question is hard: how do you keep object ownership explicit while avoiding deadlocks, leaks, and cycles? That balancing act is where many kernel bugs hide.
This is also a reminder that the Linux kernel security model is layered. AppArmor can be a powerful protective control, but it is still code, and code can be raced, stressed, and mismanaged. The right conclusion is not distrust; it is disciplined maintenance.
Administrators should also review whether AppArmor profile management is delegated to automation or runtime systems. Automated profile churn can make an exploitable race more feasible by increasing the number of attempts per unit of time. The more repeatable the trigger, the more practical the bug.
It is also worth watching whether further AppArmor lifecycle issues emerge from the same audit trail. When one race in profile management is found, reviewers often revisit neighboring transitions, and that can surface sibling bugs or reinforce the correctness of the chosen fix pattern. Subsystem-level reviews often reveal more than the original headline issue.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
CVE-2026-23410 is one of those kernel vulnerabilities that looks narrow on the surface and deeply architectural underneath. The immediate flaw is a race in AppArmor’s rawdata handling: rawdata inodes were not refcounted, so an attacker could begin opening one of the rawdata files while another thread or process removed the last reference to the underlying data structure. That left seq_rawdata_open() holding a dangling pointer and reading freed memory. (nvd.nist.gov)The vulnerability matters because it hits a security boundary component that is supposed to enforce policy, not become a source of instability. AppArmor is an LSM, so weaknesses in its lifecycle management can affect systems that assume kernel-enforced confinement is dependable even under hostile local activity. Ubuntu’s April 9, 2026 advisory for its Azure FIPS kernel explicitly groups CVE-2026-23410 with other AppArmor issues and warns that an unprivileged local attacker could use them to load, replace, or remove arbitrary profiles, leading to denial of service, memory exposure, local privilege escalation, or possible container escape. (ubuntu.com)
The kernel fix is conceptually elegant: move to a double refcount scheme. In other words, AppArmor needed a way to preserve the rawdata object long enough for open file handles to finish safely, without reintroducing the circular dependency that original design tried to avoid. That design tension is important because it shows the bug was not a typo-level mistake, but a correctness compromise in lifecycle ownership. (nvd.nist.gov)
What makes this especially relevant for WindowsForum readers is the broader lesson for mixed-platform infrastructure. If you run Linux guests, containers, or edge workloads under Microsoft Azure or alongside Windows management tooling, kernel security issues like this are not isolated Linux problems; they can become workload, tenancy, and availability problems at the platform level. Microsoft’s own update guide for the CVE emphasizes total loss of availability as the impact class, which is exactly the kind of operationally visible failure admins care about most when a local bug can destabilize shared or protected services.
Background
AppArmor is designed to confine processes through mandatory access control, and that means it touches a lot of sensitive kernel paths. Profile loading and unloading are routine administrative operations, but they are also the moment when reference counting, virtual filesystem state, and security policy objects all meet. When those ownership relationships are even slightly off, races can turn ordinary policy maintenance into memory safety bugs. (nvd.nist.gov)The rawdata subsystem exists to represent loaded AppArmor profile data in a form that can be inspected and managed. The challenge is that the rawdata object is referenced by both the profile and the inodes exposed to userspace, and those relationships can easily become circular if they are modeled too naively. The kernel note says rawdata inodes were intentionally left unrefcounted to avoid circular refcounting, but that tradeoff created a race window during profile removal. (nvd.nist.gov)
That tradeoff is common in kernel engineering. Refcounting solves lifetime management, but overdoing it can create leaks, while underdoing it creates use-after-free conditions or stale pointer dereferences. In this case, the object graph was stable most of the time, which is exactly why bugs like this survive: the failure mode only appears when one thread is opening rawdata while another is tearing down the corresponding profile. That kind of timing sensitivity is the hallmark of a hard-to-reproduce kernel race.
Downstream vendors quickly recognized the issue as part of a larger AppArmor cleanup cycle. Ubuntu’s advisory packages CVE-2026-23410 with several adjacent AppArmor vulnerabilities, suggesting a focused review of profile lifecycle and mediation logic rather than an isolated one-off flaw. That clustering matters because vulnerabilities often emerge in families: once one race is found, adjacent state transitions tend to deserve suspicion too. (ubuntu.com)
The timing also matters. NVD records the CVE as received from kernel.org on April 1, 2026, with a later modification on April 2 to add the CNA’s CVSS 3.1 score of 7.8 High. Ubuntu published its corresponding advisory on April 9, 2026. That sequence tells us the issue moved from upstream disclosure to vendor response quickly, but not instantaneously, which is typical for kernel flaws that require downstream packaging and validation. (nvd.nist.gov)
How the Race Happens
The vulnerable path is deceptively simple. An attacker opens a rawdata file, and beforeseq_rawdata_open() finishes, the last reference to the underlying aa_loaddata object disappears because the associated profile is removed. Since the inode was not independently refcounted, the i_private pointer can outlive the object it points to, and the next access becomes a use-after-free. (nvd.nist.gov)The Lifetime Bug in Plain English
The bug is not about malformed input or exotic hardware behavior. It is about two normal operations happening at the wrong time: one thread reading, another thread deleting. In systems programming, those are exactly the sort of operations that should be safe, which is why a race here is so concerning. A broken lifetime model is often more dangerous than a parsing bug because it can be exploited repeatedly and with relatively little noise.A useful mental model is this: the inode is like a library card, while the underlying rawdata is like the book. If the library card is still valid but the book has already been destroyed, the next reader gets a meaningless pointer instead of content. The kernel description makes clear that AppArmor intended the profile’s rawdata reference to keep things alive, but teardown created a gap where VFS and profile destruction could race each other. (nvd.nist.gov)
What makes that gap exploitable is not just the race itself, but the ability to influence timing. Local attackers can often stress the kernel with repeated opens, concurrent removals, or workload patterns that increase the chance of hitting the critical window. Once a race is in play, reliability becomes part of exploitability.
Why the Old Design Was Fragile
The original design avoided refcounting the inode because the developers wanted to prevent a circular dependency. That is understandable, but it created a dependency on the profile reference alone, which is not strong enough during concurrent removal. When one cleanup path assumes another object is still present, even a short overlap can be catastrophic. (nvd.nist.gov)The important insight is that “avoid circular refcounts” is not the same as “avoid all extra refcounts.” The fix introduces a double refcount scheme, where one counter handles the inode-level lifetime and another uses the profile reference to break the cycle. That is a classic kernel compromise: preserve correctness without resurrecting the very leak pattern the original code was trying to dodge. (nvd.nist.gov)
- The vulnerable object is
struct aa_loaddata. - The stale pointer appears in
i_private. - The trigger is concurrent open and profile removal.
- The failure mode is use-after-free, not just a null dereference.
- The design flaw is lifetime ownership, not parsing.
Impact and Severity
From Microsoft’s update-guide perspective, the headline consequence is total loss of availability. That is an important framing because it signals that the issue is not merely theoretical memory corruption; it can translate into complete denial of service for an impacted component if the attacker continues the attack or repeats it enough times. The user-supplied Microsoft description aligns with the broader class of kernel bugs where local exploitation can repeatedly destabilize a system.NVD has not yet assigned its own score, but the CNA scoring from kernel.org is CVSS 3.1 7.8 High with
AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H. That vector is noteworthy because it reflects local exploitability with high integrity and confidentiality impact as well as availability impact, which is more serious than a simple crash-only assessment. (nvd.nist.gov)Availability Is Only the First Layer
A denial-of-service interpretation is easy to understand because the kernel can fail, panic, or otherwise become unusable. But the upstream description explicitly says freed memory is accessed, and that kind of bug can do more than crash if the attacker can shape or observe the resulting memory state. On some kernels and some builds, use-after-free bugs are stepping stones to controlled corruption rather than one-shot panics. (nvd.nist.gov)The key distinction is between theoretical severity and operational exploitability. Even if the most obvious outcome is a crash, a local attacker who can repeatedly trigger the condition may still create persistent service instability, especially in container hosts or appliance-style deployments where AppArmor is heavily used. That is why administrators should treat this as a kernel memory-safety issue, not merely a nuisance bug.
Downstream vendors also treat it as part of a broader AppArmor risk surface. Ubuntu’s advisory states that a local attacker could use several AppArmor issues to load, replace, and remove profiles, with consequences ranging from denial of service to privilege escalation or container escape. While that statement covers multiple CVEs, it reinforces the idea that AppArmor lifecycle bugs can have more than one operational outcome. (ubuntu.com)
- Local access is required, which lowers the remote attack surface.
- Privilege level is low but not zero; the attacker still needs local execution.
- Availability impact is immediate and easy to understand.
- Memory safety makes the bug more dangerous than a benign crash.
- Containerized environments may see outsized operational impact.
The Fix
The kernel fix replaces the fragile single-lifetime assumption with a double refcount scheme. That is the practical answer to a reference-cycle problem: one reference path protects the object while it is in use by the VFS, and another preserves the relationship needed by the profile until every inode reference is gone. The end result is that rawdata can be freed safely only after all inode references have been dropped. (nvd.nist.gov)Why Double Refcounting Works
This kind of fix is often less exciting than a dramatic rewrite, but in kernel land it is usually the right kind of boring. The goal is to make object lifetime explicit and deterministic instead of implicit and race-prone. By ensuring the rawdata object survives until the last inode reference disappears, the patch closes the precise window that the exploit depends on. (nvd.nist.gov)That said, double refcounting is not a free lunch. It adds bookkeeping, and bookkeeping bugs can be introduced elsewhere if the release paths are not symmetrical. Kernel maintainers typically accept that tradeoff when the alternative is a use-after-free in a security-sensitive subsystem, but it reinforces how hard lifecycle management can be in mature codebases.
The change also reveals a subtle lesson about security engineering: the right fix is often not “add a lock everywhere.” Locks can serialize behavior, but they do not automatically solve ownership semantics across multiple subsystems. In this case, the authors chose a lifetime model repair instead of a concurrency band-aid, which is usually a healthier long-term answer.
Practical Meaning for Administrators
For administrators, the practical meaning is straightforward: once the patched kernel is deployed, the specific open-versus-remove race should no longer leave a danglingi_private pointer. The security benefit is strongest in environments where AppArmor policies are actively loaded and removed, or where untrusted local users can provoke profile churn. (nvd.nist.gov)- The fix addresses the root cause, not just the crash site.
- It preserves the original goal of avoiding circular ownership.
- It reduces the chance of repeated race-triggered failures.
- It is especially relevant on multi-tenant or container-heavy systems.
- It should be treated as a kernel stability and security update, not optional hardening.
Microsoft’s Severity Framing
The wording supplied in the Microsoft update guide is worth paying attention to because it emphasizes a particular consequence class: denial of access to resources. Microsoft’s description is more operational than the kernel’s technical note, and that matters because many enterprise teams triage by business impact first and exploit primitive second. If a flaw can deny service in a shared component, it becomes a platform reliability issue even before it is a security escalation concern.Availability as a Business Risk
In real deployments, total availability loss rarely means every machine goes dark. More often, it means the affected component can no longer handle requests, queue work, or keep policy enforcement stable enough for normal operation. For a security module like AppArmor, that can be enough to take a host, a container node, or a policy-driven workflow out of rotation.That is why Microsoft’s framing is useful: it maps a kernel bug to a business outage. Even if the exploit is local, the blast radius can be much wider when the vulnerable system is part of a larger service fabric. The practical consequence is often not “someone got a shell,” but “a node became unreliable at exactly the wrong time.”
What the Severity Does and Does Not Mean
The severity language does not mean every affected system will be trivial to crash. It means that if an attacker can reach the vulnerable path, the result can be severe enough to deny service in a meaningful way. In security operations, availability-only bugs are often underappreciated because they do not always look like classic compromise, yet they can still produce major incident response costs.It is also important not to overread the Microsoft text as the complete technical story. The upstream and downstream Linux sources describe a use-after-free, and the CNA score suggests high confidentiality and integrity impact as well. The best reading is that Microsoft is emphasizing the observable impact class, while the kernel community is characterizing the underlying memory-safety risk more broadly. (nvd.nist.gov)
Enterprise and Cloud Implications
Enterprise Linux deployments are where AppArmor bugs tend to get real attention, especially when they intersect with containers, orchestrators, and compliance-driven profiles. A local attacker on a shared host is never a good thing, but a local attacker on a node hosting multiple workloads can turn a kernel flaw into a platform outage. That is why this CVE should be viewed through the lens of workload density, not just endpoint count. (ubuntu.com)Container Hosts and Multi-Tenant Nodes
Container hosts are especially sensitive because security modules often mediate per-container policy and profile transitions. If profile removal can be raced into a use-after-free, then workload churn becomes part of the attack surface. The issue is therefore not only about deliberate malicious access; it is about how often the platform performs profile maintenance under normal operations.For cloud operators, that means maintenance windows, workload autoscaling, and rolling deployments all deserve more scrutiny. Systems that frequently load and unload AppArmor profiles could be more exposed to practical race conditions simply because they hit the dangerous timing more often. Higher operational churn often equals higher bug discoverability.
Compliance and Hardening Context
Azure FIPS and similarly hardened Linux images usually exist precisely because organizations expect a stronger security baseline. That makes the presence of AppArmor lifecycle vulnerabilities especially awkward: the same policies intended to raise confidence can increase the number of code paths exercised under production load. In other words, hardening does not eliminate complexity; it often concentrates it.That does not mean organizations should avoid AppArmor. It means they should recognize that mandatory access control is only as reliable as its lifecycle management. Patching these bugs is part of preserving the credibility of the hardening story, not an admission that the model itself failed.
- Multi-tenant hosts deserve faster prioritization.
- Containers amplify the consequence of local kernel bugs.
- Compliance images still need timely kernel patching.
- Policy churn can increase real-world race exposure.
- Security modules require the same lifecycle rigor as filesystems or networking.
What the Broader Bug Family Suggests
The fact that Ubuntu groups CVE-2026-23410 with multiple AppArmor issues is telling. Vulnerabilities rarely appear in complete isolation when they are rooted in shared object ownership, profile state transitions, or parser/loading code. Once one path shows a race, adjacent code often deserves a second look. (ubuntu.com)A Pattern of Lifecycle Complexity
Security modules are unusually prone to this kind of problem because they sit at the intersection of policy, file operations, and process lifecycle. Profile loading, replacement, deletion, and inspection all interact with data structures that need to survive just long enough for the kernel to do the right thing. That makes reference counting and teardown choreography central to security, not just implementation detail.The CVE also shows why kernel hardening is rarely a one-line story. The upstream fix is simple to describe, but the surrounding design question is hard: how do you keep object ownership explicit while avoiding deadlocks, leaks, and cycles? That balancing act is where many kernel bugs hide.
Why Associated CVEs Matter
When vendors mention several related CVEs at once, administrators should not treat the list as noise. It usually means a subsystem review surfaced multiple issues in a common area, and patching one without understanding the rest leaves residual risk. In practice, the most efficient response is to update the kernel package set that contains the full fix series rather than trying to cherry-pick a single patch.This is also a reminder that the Linux kernel security model is layered. AppArmor can be a powerful protective control, but it is still code, and code can be raced, stressed, and mismanaged. The right conclusion is not distrust; it is disciplined maintenance.
Operational Response
For defenders, the response to CVE-2026-23410 is primarily about patching, validation, and exposure management. Since the issue requires local execution, the first question is which systems actually allow untrusted or semi-trusted local code to run, especially in containers or shared shell environments. The second question is where AppArmor profile load/unload activity is common enough to make the race practically reachable.Triage Priorities
A good triage workflow starts with kernel version inventory. Identify distributions and images that include the vulnerable AppArmor code paths, then map them to vendor advisories and fixed builds. Ubuntu has already published guidance for its Azure FIPS kernel line, and the NVD entry lists upstream references to the kernel.org fix commits. (nvd.nist.gov)Administrators should also review whether AppArmor profile management is delegated to automation or runtime systems. Automated profile churn can make an exploitable race more feasible by increasing the number of attempts per unit of time. The more repeatable the trigger, the more practical the bug.
Practical Hardening Steps
- Inventory Linux kernels that include AppArmor.
- Patch to vendor builds that incorporate the upstream fix.
- Restrict untrusted local execution where feasible.
- Review container and multi-tenant host exposure.
- Monitor for unexpected crashes or policy-management failures.
- Prioritize systems with high profile churn or active hardening automation.
Strengths and Opportunities
The upside of this disclosure is that it demonstrates a clean upstream understanding of the failure mode and a targeted fix path. It also gives defenders a concrete remediation target rather than a vague advisory about instability. In a mature kernel ecosystem, that is a genuine strength, because clear root-cause analysis accelerates patch uptake and reduces guesswork.- Clear root cause: the race is well described and technically specific.
- Targeted remediation: the double refcount scheme directly addresses lifetime safety.
- Vendor responsiveness: downstream advisories appeared quickly after upstream disclosure.
- Operational clarity: administrators can focus on kernel patching and local exposure.
- Broader hardening benefit: fixing this bug improves confidence in AppArmor’s lifecycle handling.
- Triage simplicity: local execution requirement helps scope the highest-risk systems.
- Subsystem learning value: the bug highlights patterns useful for future code review.
Risks and Concerns
The concern is that this is not just one bad pointer, but a sign of a fragile object-lifetime boundary inside a security module. A bug in teardown logic can be harder to observe than a parsing flaw, and that means it may persist in the field longer than it should. It also reinforces how dangerous local kernel bugs can be even when the initial access vector seems limited.- Local attacker requirement can still be dangerous on shared systems.
- Use-after-free behavior may vary across builds, making detection inconsistent.
- Repeatability can turn a crash into persistent availability loss.
- Container hosts may experience broader blast radius than single-user endpoints.
- Adjacent AppArmor issues suggest more subsystem scrutiny may be needed.
- Operational churn can make the race easier to trigger in real environments.
- Underestimating availability loss may delay patching in some enterprises.
Looking Ahead
The next thing to watch is how quickly distributors close the gap between upstream fixes and fleet-wide deployment. Kernel bugs of this sort are rarely “fixed” the moment the patch lands; they are fixed when production images, cloud kernels, and appliance builds actually absorb the change. For organizations with managed Linux estates, the real metric is patch propagation, not CVE publication.It is also worth watching whether further AppArmor lifecycle issues emerge from the same audit trail. When one race in profile management is found, reviewers often revisit neighboring transitions, and that can surface sibling bugs or reinforce the correctness of the chosen fix pattern. Subsystem-level reviews often reveal more than the original headline issue.
Indicators to Monitor
- Vendor kernel package releases that include the AppArmor fix.
- Repeated mentions of AppArmor profile load/unload races.
- Follow-on advisories covering adjacent CVEs in the same subsystem.
- Crash reports involving
seq_rawdata_open()oraa_loaddata. - Container host stability after kernel rollout.
Source: MSRC Security Update Guide - Microsoft Security Response Center