Linux has published another small but important kernel security fix in CVE-2026-31487, and on the surface it looks like the kind of change that only kernel maintainers and driver authors would notice. Underneath that modest title, though, lies a classic use-after-free risk in the SPI subsystem, triggered by the way
What makes CVE-2026-31487 worth attention is not that it introduces a brand-new security primitive, but that it exposes a lifetime-management flaw in the path that decides which driver should bind to which SPI device. The upstream description says that when a driver is probed through
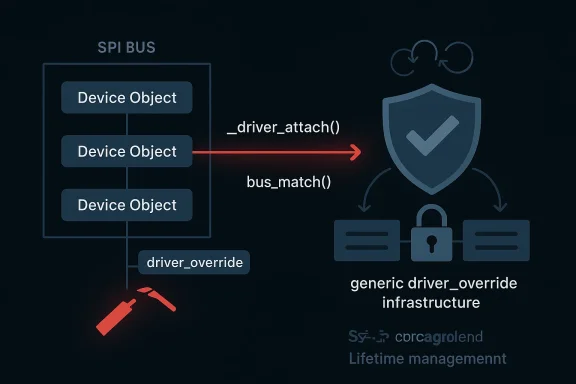
The most interesting detail is that the bug is not being fixed by adding a little more hand-written locking to SPI. Instead, the subsystem is being moved to the driver-core’s driver_override helper path, which already knows how to manage the lifetime and locking of that field safely. That is a signal of maturity from the maintainers: rather than duplicate the logic, they are delegating the responsibility to a piece of the kernel that already exists for exactly this purpose. The result is simpler code and fewer opportunities for future regressions.
There is also a subtle SPI-specific caveat in the advisory text. The SPI bus does not simply opt into the driver-core’s override behavior in the same way as many other buses, because SPI historically prints an empty string when the override pointer is
Use-after-free bugs remain among the most security-sensitive classes in kernel code because they sit at the intersection of concurrency, object ownership, and trust in internal pointers. Unlike a simple NULL dereference, a UAF can sometimes be turned into more than a crash if an attacker can influence allocation patterns or timing. Even when exploitability is unclear, the kernel community treats UAFs seriously because they often represent the sort of bug that downstream users do not want to discover the hard way. The SPI issue is narrow, but narrow is not the same as harmless.
The important technical point is that
This also explains why the patch is framed as a transition to the generic infrastructure rather than a local band-aid. The driver core already knows how to enforce the correct locking semantics for
The bus’s unusual sysfs behavior is also worth noting. The advisory explains that SPI emits an empty string when the
That choice matters because even “small” changes in the driver model can ripple into tooling, diagnostics, and automation. A sysfs field is not just a string; it is part of the contract between kernel and userspace. If a subsystem changes that contract casually, the consequence may be a support problem rather than a security issue, but support problems in kernel space can be expensive and persistent. In other words, the patch is not merely safer; it is also more careful about operational stability.
The driver model documentation lays out the intended pattern: buses that support driver override should use
There is also a broader software-engineering lesson here: if a subsystem’s bug is fundamentally about object lifetime and ownership, the best fix is often to align that subsystem with a shared abstraction rather than patching around the symptoms. Kernel code is full of such compromises because performance and compatibility matter, but the best fixes are the ones that leave fewer future traps behind. This patch looks like one of those.
The main downside is that this kind of bug often gets labeled “narrow” and therefore deprioritized. Narrow is not the same as low value, especially in a kernel. A single UAF in a subsystem that touches lots of hardware permutations can become a real reliability or security issue once it reaches broad deployments. That is exactly why the kernel community prefers to get these fixes into stable trees quickly.
The SPI fix therefore says something important about kernel maintenance philosophy. When the driver core already has a correct, lock-aware implementation, using it is not just convenient; it is safer than carrying a bus-local variant with subtly different assumptions. That matters because bugs in this part of the kernel tend to be hard to spot in code review unless someone is already thinking about concurrency edges.
This is also why the patch is interesting even to people who never touch SPI directly. The same pattern appears all over the kernel: a subsystem starts with a local mechanism, later discovers that the driver core already has a better abstraction, and then migrates to the shared helper. These migrations are usually dull in the best possie code, reduce ambiguity, and make the system easier to reason about.
If you manage devices, appliances, or embedded boards, this is the kind of issue that deserves a release-note review rather than a casual “we’ll get to it later.” Driver binding bugs can surface during boot, on reprobe, or after a hardware state change, so they may be invisible until the wrong timing lines up. That makes testing important even when the patch looks small.
Another strength is that this issue is easy to explain to downstream maintainers. There is a clear lifetime hazard, a clear locking gap, and a clear reason to use shared infrastructure. Those are the best kinds of kernel fixes because they are easy to audit, easy to justify, and less likely to diverge across vendor trees.
A second concern is patch lag. Enterprises often run vendor kernels, appliance builds, or long-term support images, which means the vulnerability can remain present long after the upstream fix is available. If administrators assume “the CVE exists, so we’re safe once it’s published,” they may miss the fact that their exact kernel build still lacks the backport.
It is also worth watching whether the SPI maintainers or driver-core maintainers use this as an opportunity to audit similar override or match paths elsewhere. Once a subsystem reveals a mismatch between local assumptions and generic infrastructure, adjacent code often deserves a second look. That is especially true in the kernel, where one synchronization mistake can hint at a broader pattern rather than an isolated typo.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
__driver_attach calls a bus match callback without holding the device lock. The fix moves SPI onto the generic driver_override infrastructure, which handles the locking internally and closes the race without redesigning the bus model. The CVE is now public in Microsoft’s update guide, and the underlying issue is described in the Linux kernel’s own stable backport trail, underscoring that this is a real production hardening issue rather than a hypothetical code-style tweak. Linux kernel’s driver model is built around a simple idea with complicated consequences: devices and drivers are matched, bound, unbound, and re-bound constantly, often across concurrency boundaries that are easy to overlook. The SPI subsystem is no exception. It sits under a standard Linux driver model and uses the same core infrastructure as other buses, but it also has a few bus-specific quirks that make its behavior slightly different from the norm. The kernel documentation explicitly frames SPI as a generalized interface for declaring devices, managing them through the driver model, and performing I/O, which means any flaw in its matching logic affects a foundational part of the system rather than a niche helper.What makes CVE-2026-31487 worth attention is not that it introduces a brand-new security primitive, but that it exposes a lifetime-management flaw in the path that decides which driver should bind to which SPI device. The upstream description says that when a driver is probed through
__driver_attach, the bus match callback is invoked without the device lock held, and that the SPI code was accessing driver_override in a way that could turn into a use-after-free. In kernel land, that is exactly the kind of bug that looks mundane until it isn’t. A stale pointer in the wrong context can be enough to destabilize a system, crash a host, or crey-safety issue.The most interesting detail is that the bug is not being fixed by adding a little more hand-written locking to SPI. Instead, the subsystem is being moved to the driver-core’s driver_override helper path, which already knows how to manage the lifetime and locking of that field safely. That is a signal of maturity from the maintainers: rather than duplicate the logic, they are delegating the responsibility to a piece of the kernel that already exists for exactly this purpose. The result is simpler code and fewer opportunities for future regressions.
There is also a subtle SPI-specific caveat in the advisory text. The SPI bus does not simply opt into the driver-core’s override behavior in the same way as many other buses, because SPI historically prints an empty string when the override pointer is
NULL, while the generic infrastructure would otherwise show "(null)". That detail sounds cosmetic, but in kernel-user interface design, cosmetic differences often become compatibility commitments. The fix therefore keeps the generic locking benefits without enabling the higher-level bus flag in a way that woue behavior. That is a careful compromise, not a half-measure.
 Why this category of bug matters
Why this category of bug matters
Use-after-free bugs remain among the most security-sensitive classes in kernel code because they sit at the intersection of concurrency, object ownership, and trust in internal pointers. Unlike a simple NULL dereference, a UAF can sometimes be turned into more than a crash if an attacker can influence allocation patterns or timing. Even when exploitability is unclear, the kernel community treats UAFs seriously because they often represent the sort of bug that downstream users do not want to discover the hard way. The SPI issue is narrow, but narrow is not the same as harmless.What the Vulnerability Actually Is
At the center of the issue is thedriver_override field, a kernel mechanism that lets a specific device be forced to bind to a specific driver name rather than follow the normal matching rules. The Linux documentation says userspace can override standard matching by writing a driver name to the driver_override sysfs attribute, and the driver core provides helpers such as device_match_driver_override and device_set_driver_override so subsystems do not have to reinvent the wheel. SPI’s bug arose because its matching path was touching that state in a way that assumed the object remained safe to read without the device lock.The important technical point is that
__driver_attach intentionally calls match without holding the device lock. That is not a defect in itself; it is part of the design of the driver model. The problem appears when a bus-specific match callback reaches into fields whose lifetime or synchronization rules depend on the lock thaer words, the bug was not the absence of a lock in __driver_attach; it was SPI’s reliance on a field that needed more careful handling than the subsystem was giving it.How the race can become dangerous
When the bus callback examinesdriver_override without the correct protection, it can race with another operation that clears, changes, or frees that field. If the object is torn down or reconfigured at just the wrong moment, the callback can end up dereferencing memory that no longer belongs to the device. That is the textbook shape of a xact exploitability will depend on surrounding kernel state, but from a defensive standpoint the mere existence of the race is enough to warrant a fix.This also explains why the patch is framed as a transition to the generic infrastructure rather than a local band-aid. The driver core already knows how to enforce the correct locking semantics for
driver_override, so letting SPI continue to do its own thing would just preserve a fragile duplication. Kernel code ages badly when two different subsystems each maintain slightly different versions of the same ownership logic. The maintainers are effectively choosing consistency over subsystem special-casing.Why SPI Is a Special Case
SPI is not the biggest or flashiest Linux bus, but it matters because it underpins a wide range of embedded and peripheral hardware. It is common in boards that use sensors, flash chips, controllers, and other devices that depend on predictable low-level transport. That makes SPI a quiet part of the stack with an outsized footprint across products that consumers never think about as “SPI systems.” The documentation describes SPI as a generalized interface that follows the standard Linux driver model, which means any defect in the bus logic can propagate into a large number of device-specific deployments.The bus’s unusual sysfs behavior is also worth noting. The advisory explains that SPI emits an empty string when the
driver_override pointer is NULL, unlike many other buses that may emit "(null)" or use a different convention. That means the maintainers coul generic driver_override flag on struct bus_type and call it a day, because that would subtly alter the user-visible interface. In kernel maintenance, compatibility details like this are often the difference between a clean migration and a regression.Compatibility versus correctness
This is one of those situations where the kernel is balancing two valid goals at once. On one side is correctness: stop the race, avoid the UAF, centralize the locking, and make the matching path safe. On the other side is compatibility: preserve SPI’s existing sysfs semantics so userspace tools do not suddenly see an unexpected change in how an override is printed. The patch chooses both when possible, which is exactly what a mature subsystem should do.That choice matters because even “small” changes in the driver model can ripple into tooling, diagnostics, and automation. A sysfs field is not just a string; it is part of the contract between kernel and userspace. If a subsystem changes that contract casually, the consequence may be a support problem rather than a security issue, but support problems in kernel space can be expensive and persistent. In other words, the patch is not merely safer; it is also more careful about operational stability.
What the Fix Changes
The upstream description is clear that the generic driver_override infrastructure instead of accessing SPI’s own override handling in a way that sidesteps the locking guarantees. That shifts responsibility to code in the driver core that was designed to handle this exact sort of state safely. It is the sort of fix that is small in terms of lines changed but large in terms of architectural significance.The driver model documentation lays out the intended pattern: buses that support driver override should use
device_match_driver_override in their matching logic, and driver-core helpers are available to set or clear the override. That makes the SPI fix look less like a one-off and more like a correction toward the kernel’s preferred design. When a subsystem is already close to the canonical pattern, moving the last few pieces into alignment is often the safest possible route.Why not just lock it locally?
A local lock might appear to solve the immediate bug, but that would likely leave SPI maintaining a special rule that other buses do not need. Those custom lock rules tend to calcify, and once they do, they become hard to reason about during future changes. The generic helper exists precisely to reduce that maintenance burden. By using it, SPI benefits from the same locking discipline the rest of the driver core already relies on.There is also a broader software-engineering lesson here: if a subsystem’s bug is fundamentally about object lifetime and ownership, the best fix is often to align that subsystem with a shared abstraction rather than patching around the symptoms. Kernel code is full of such compromises because performance and compatibility matter, but the best fixes are the ones that leave fewer future traps behind. This patch looks like one of those.
Security and Operational Impacrity perspective, CVE-2026-31487 matters because it is a kernel memory-safety bug in a core subsystem. Even if the practical exploitability turns out to be limited by timing or by the specific hardware involved, the existence of a UAF in driver binding code is enough to demand patching. Kernel bugs in attach and match paths are especially important because they can be reached during normal device lifecycle events, not just during unusual admin actions.
Operationally, the likely impact is broader than the average desktop user may notice. SPI is much more relevant in embedded devices, appliances, industrial systems, and hardware-adjacent Linux deployments than on mainstream office PCs. That means the systems most likely to care about this CVE are often the ones that are hardest to update and the ones where downtime is least convenient. In practice, that increases the importance of vendor backports and tested rollouts.Enterprise versus consumer exposure
On consumer Linux systems, the issue may never be exercised often enough to be visible. On managed infrastructure or embedded platforms, however, device probing and driver rebinding can happen as part of boot, hotplug, firmware management, or hardware lifecycle events. That makes the enterprise and embedded exposure profile meaningfully different from the casual desktop case. A bug like this is easy to only think in terms of laptops and workstations.The main downside is that this kind of bug often gets labeled “narrow” and therefore deprioritized. Narrow is not the same as low value, especially in a kernel. A single UAF in a subsystem that touches lots of hardware permutations can become a real reliability or security issue once it reaches broad deployments. That is exactly why the kernel community prefers to get these fixes into stable trees quickly.
The Driver-Core Angle
This CVE is a good example of the kernel’s trend toward centralizing common logic in the driver core instead of letting each bus manage everything independently. The documentation fordriver_override shows that the generic model already defines a standard path for matching a device against a forced driver name. That model gives bus authors a stable set of helpers andhat each bus will invent its own slightly different synchronization scheme.The SPI fix therefore says something important about kernel maintenance philosophy. When the driver core already has a correct, lock-aware implementation, using it is not just convenient; it is safer than carrying a bus-local variant with subtly different assumptions. That matters because bugs in this part of the kernel tend to be hard to spot in code review unless someone is already thinking about concurrency edges.
Why generic infrastructure wins
Generic infrastructure is not just about code reuse. It is about reducing the number of places where critical lifecycle rules can be violated. Every duplicate implementation of a locking-sensitive feature creates another place where a regression can creep in during future maintenance. By leaning on the driver core, SPI narrows the surface area where those errors can reappear.This is also why the patch is interesting even to people who never touch SPI directly. The same pattern appears all over the kernel: a subsystem starts with a local mechanism, later discovers that the driver core already has a better abstraction, and then migrates to the shared helper. These migrations are usually dull in the best possie code, reduce ambiguity, and make the system easier to reason about.
What Administrators Should Do
Administrators do not need to panic over this CVE, but they should treat it as a normal kernel update item with a hardware-specific wrinkle. The first question is whether any of your Linux systems actually depend on SPI devices or SPI-heavy embedded workloads. If they do, the next question is whether your vendor kernel has already backported the fix or whether you still need a package or firmware update. Published CVEs often arrive before downstream distributions have fully propagated the patch.If you manage devices, appliances, or embedded boards, this is the kind of issue that deserves a release-note review rather than a casual “we’ll get to it later.” Driver binding bugs can surface during boot, on reprobe, or after a hardware state change, so they may be invisible until the wrong timing lines up. That makes testing important even when the patch looks small.
Practical checklist
- Verify whether your kernel tree includes the upstream SPI override fix.
- Check vendor advisories for backports rather than relying only on mainline version numbers.
- Prioritize systems with SPI-dependent peripherals, especially in embedded or appliance deployments.
- Validate boot, reprobe, and device hotplug paths after patching.
- Confirm that sysfs behavior around
driver_overridestill matches your automation expectations.
Strengths and Opportunities
The most encouraging part of this CVE is that the fix is conceptually straightforward. The kernel already has the right machinery for safedriver_override handling, and SPI is being brought into line with that machinery rather than patched around the edges. That is a strong sign that the vulnerability can be resolved cleanly and backported without dramatic side effects.Another strength is that this issue is easy to explain to downstream maintainers. There is a clear lifetime hazard, a clear locking gap, and a clear reason to use shared infrastructure. Those are the best kinds of kernel fixes because they are easy to audit, easy to justify, and less likely to diverge across vendor trees.
- The fix is small and surgical, which helps stable backports.
- The bug maps cleanly to a known class of use-after-free problems.
- The patch aligns SPI with driver-core best practices.
- Vendor maintainers can validate it without redesigning SPI.
- The change reduces long-term maintenance risk.
- The existing docs already describe the intend
- The patch improves kernel consistency across buses.
Risks and Concerns
The biggest risk is underestimation. A UAF in driver binding code may not sound glamorous, and the SPI bus is not the sort of subsystem that generates headlines, but that does not make the issue trivial. Kernel memory-safety bugs are exactly the sort that deserve prompt attention even when their public description looks narrow.A second concern is patch lag. Enterprises often run vendor kernels, appliance builds, or long-term support images, which means the vulnerability can remain present long after the upstream fix is available. If administrators assume “the CVE exists, so we’re safe once it’s published,” they may miss the fact that their exact kernel build still lacks the backport.
- Vendor backports may not arrive at the same time across distributions.
- Some devices may never receive a convenient in-place kernel update.
- The issue may be overlooked if SPI is treated as an obscure bus.
- Compatibility assumptions around sysfs output could create regressions if handled badly.
- Device-binding races are harder to reproduce than obrity teams may deprioritize the CVE if no exploit proof is available.
- Specialized hardware fleets often update more slowly than servers.
Looking Ahead
The next thing to watch is how quickly the fix spreads into supported stable branches and vendor-maintained kernels. The upstream record and the Microsoft vulnerability guide both indicate that the bug is now public, but public disclosure does not by itself mean every deployed system is protected. For administrators, the meaningful milestone is the appearance of the fix in the exact build they run.It is also worth watching whether the SPI maintainers or driver-core maintainers use this as an opportunity to audit similar override or match paths elsewhere. Once a subsystem reveals a mismatch between local assumptions and generic infrastructure, adjacent code often deserves a second look. That is especially true in the kernel, where one synchronization mistake can hint at a broader pattern rather than an isolated typo.
- Track downstream advisories for your distribution or vendor kernel.
- Confirm whether SPI-heavy hardware is in your production fleet.
- Validate that sysfs behavior still matches your automation and tooling.
- Watch for related cleanup in other bus or driver-model code.
- Re-test device probing and reprobe paths after updates.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center