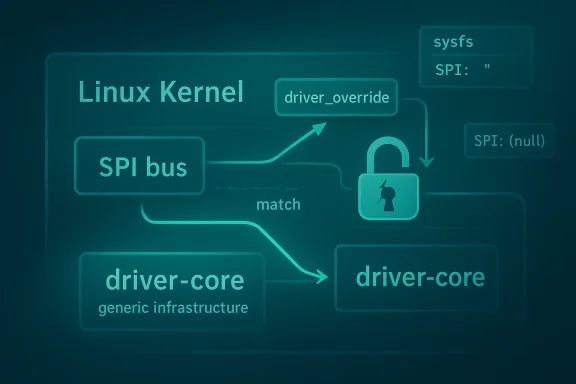
CVE-2026-31487 is a reminder that some of the most consequential Linux kernel bugs are not loud crashes or dramatic memory-corruption chains, but quiet lifetime mistakes hidden inside core infrastructure. In this case, the issue sits in the SPI subsystem’s interaction with the kernel’s driver-core override machinery, where a match callback can read
The SPI bus is one of those kernel subsystems that rarely makes headlines until something goes wrong, yet it underpins a huge amount of embedded, industrial, and board-level hardware. Unlike a desktop-facing feature that can be swapped out easily, SPI is often the glue between the CPU and sensors, flash chips, controllers, and custom peripherals. That means bugs in SPI are not just theoretical correctness issues; they can affect the reliability of devices that users never see directly but depend on every day.
The vulnerability description says the problem arises when a driver is probed through
The fix is to use the generic driver_override infrastructure in the driver core, which is designed to handle the locking correctly internally. The kernel’s own change note makes clear that the
There is also an SPI-specific wrinkle that makes this case more interesting than a standard driver-core cleanup. The advisory notes that SPI does not enable the
Another reason this CVE matters is that it landed through the normal upstream-to-stable pipeline. The change history shows the CVE record was newly received from kernel.org and immediately linked to multiple stable references, which strongly suggests the kernel community already treated it as a production-relevant fix rather than a speculative concern . For operators, that usually matters more than the formal CVSS number, especially when NVD has not yet assigned one.
The detail that
The fact that SPI is a driver-facing subsystem makes the exposure profile more nuanced. A malicious local actor with the ability to influence driver binding, or an environment with unusual hot-plug and reprobe behavior, may be more likely to encounter the bug than a typical consumer desktop. Still, the broader lesson is not about attacker creativity; it is about how easy it is for lifetime bugs to emerge when low-level subsystems mix legacy behavior with newer infrastructure.
That matters because locking is not just about preventing races in the abstract. It determines whether the kernel can reason about the validity of a pointer at a specific moment. If the generic layer already knows when the override state can be observed and when it can be mutated, then bus code becomes less error-prone and easier to audit. The fix therefore improves both safety and maintainability.
Preserving that behavior means the patch had to avoid breaking tooling, scripts, or diagnostics that already expect the SPI-specific presentation. In other words, the fix had to improve locking without changing the subsystem’s external semantics. That is often the hardest kind of kernel change to land cleanly.
A few practical implications follow from that design choice:
The important part is that the patch is not trying to make every call site locked in the same way. Instead, it acknowledges that
This CVE also reflects a broader truth about kernel hardening: many of the best fixes are not dramatic rewrites, but migrations toward shared infrastructure. Each time the kernel centralizes a pattern like override handling, it reduces the number of places where a race can hide. The result is less code to audit and fewer subsystem-specific edge cases.
For enterprise environments, the story is broader. SPI is common in embedded Linux, industrial control, appliances, network gear, and specialized systems where uptime matters more than novelty. In those settings, a use-after-free in driver binding can become a real operational risk even if the bug is hard to weaponize in a conventional sense. The impact is often stability-first, but stability is exactly what critical infrastructure depends on.
The point is not simply that SPI is “different.” The point is that its external behavior has become part of its interface contract. Any attempt to turn on the generic
It also makes the code easier to reason about going forward. If SPI no longer owns the locking story for this field, future maintainers have one less local rule to remember. In a codebase as large as the kernel, that reduction in cognitive overhead is a real security benefit.
Some practical takeaways:
This is especially true when the upstream description is specific enough to reveal the risk surface. Here, we know the bug involves a
For enterprise customers, that turns kernel maintenance into a procurement concern. If one platform vendor consistently backports driver-core fixes cleanly and another drifts, the difference can show up in uptime, support costs, and security audit outcomes. In other words, the impact of CVE-2026-31487 extends beyond one subsystem; it reflects the operational maturity of the vendor stack.
The bigger ecosystem lesson is that security quality is also maintenance quality. Vendors that can prove they track upstream bug lifecycles closely are usually the ones that earn trust in enterprise environments. That trust is built one patch at a time.
It also creates an opportunity for administrators and vendors to tighten their kernel hygiene around driver binding paths. Small bugs like this one are often the ones that get deferred because they do not look dramatic, but they are exactly the kind that can accumulate into reliability problems if left unpatched.
There is also a long-tail exposure problem. Many systems run vendor kernels, appliance images, or older LTS branches where upstream fixes arrive only after backport work. That means the existence of a public CVE does not guarantee immediate protection in the field.
It will also be worth watching whether maintainers audit neighboring code for similar driver-core assumptions. Once one callback path is found to depend on state that can be observed without the device lock, it is reasonable to look for other places where subsystem code is still handling ownership rules locally instead of delegating them to the core.
CVE-2026-31487 is the kind of vulnerability that rewards careful engineering rather than dramatic response. It is a small patch with a large lesson: when lifetime rules live in the kernel, the safest place for them is often the generic infrastructure layer, not a subsystem’s local code. That is good news for Linux users, good news for maintainers, and a useful reminder that the quietest kernel bugs are sometimes the ones worth taking most seriously.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
driver_override without the protection it needs and potentially trigger a use-after-free. The upstream fix moves SPI onto the generic driver_override infrastructure so the locking is handled internally, while preserving SPI’s unusual sysfs behavior of emitting an empty string instead of (null) when no override is set . That makes the patch both technically narrow and operationally important, especially for systems that rely on stable kernel backports rather than mainline releases.
 Background
Background
The SPI bus is one of those kernel subsystems that rarely makes headlines until something goes wrong, yet it underpins a huge amount of embedded, industrial, and board-level hardware. Unlike a desktop-facing feature that can be swapped out easily, SPI is often the glue between the CPU and sensors, flash chips, controllers, and custom peripherals. That means bugs in SPI are not just theoretical correctness issues; they can affect the reliability of devices that users never see directly but depend on every day.The vulnerability description says the problem arises when a driver is probed through
__driver_attach(), which calls the bus’ match() callback without the device lock held. That matters because the SPI implementation historically accessed driver_override in that callback path without adequate synchronization, creating a race window that can become a use-after-free . In kernel terms, that is the kind of bug that hides in plain sight because the control flow is intentional, but the object lifetime assumptions are not.The fix is to use the generic driver_override infrastructure in the driver core, which is designed to handle the locking correctly internally. The kernel’s own change note makes clear that the
match() call from __driver_attach() without the device lock is intentional, so the real problem is not the call site itself, but the SPI bus implementation’s handling of override state in that context . That distinction is important because it explains why the patch is architectural rather than merely cosmetic.There is also an SPI-specific wrinkle that makes this case more interesting than a standard driver-core cleanup. The advisory notes that SPI does not enable the
driver_override feature of struct bus_type, because unlike most other buses it passes "" to sysfs_emit() when the pointer is NULL, rather than printing (null) . That means the fix had to preserve user-visible behavior while still adopting the safer generic locking model.Another reason this CVE matters is that it landed through the normal upstream-to-stable pipeline. The change history shows the CVE record was newly received from kernel.org and immediately linked to multiple stable references, which strongly suggests the kernel community already treated it as a production-relevant fix rather than a speculative concern . For operators, that usually matters more than the formal CVSS number, especially when NVD has not yet assigned one.
What Actually Went Wrong
At a high level, this is a use-after-free risk caused by readingdriver_override in the wrong protection context. The SPI bus’ match logic could examine that field while another thread or subsystem was concurrently changing or releasing it, and the kernel would not necessarily catch the bad lifetime until memory had already been repurposed. That is exactly the sort of bug that can stay latent for a long time and then surface as a rare, hard-to-reproduce crash.The detail that
__driver_attach() intentionally calls match() without the device lock held is what makes this subtle. In normal developer intuition, “no lock” often sounds like a bug in itself, but here the absence of that lock is part of the driver-core design . The safety guarantee therefore has to come from the override infrastructure, not from every bus implementation reinventing its own locking rules.Why this is a kernel-security problem
A use-after-free in kernel space is not automatically a remote exploit primitive, but it is still a serious security issue. Even when the immediate impact is “just” a crash, the practical consequences can include denial of service, service restarts, watchdog resets, or a corrupted state that takes a system offline. In infrastructure or embedded deployments, that kind of instability can be just as damaging as a more sensational exploit.The fact that SPI is a driver-facing subsystem makes the exposure profile more nuanced. A malicious local actor with the ability to influence driver binding, or an environment with unusual hot-plug and reprobe behavior, may be more likely to encounter the bug than a typical consumer desktop. Still, the broader lesson is not about attacker creativity; it is about how easy it is for lifetime bugs to emerge when low-level subsystems mix legacy behavior with newer infrastructure.
Why Generic Driver-Override Infrastructure Matters
The phrase generic driver_override infrastructure sounds mundane, but in practice it is the right kind of boring. The kernel has learned, over years of bug fixing, that every subsystem-specific copy of a basic lifecycle pattern becomes a place where subtle differences creep in. By consolidating override handling in the driver core, SPI inherits locking discipline instead of reimplementing it manually.That matters because locking is not just about preventing races in the abstract. It determines whether the kernel can reason about the validity of a pointer at a specific moment. If the generic layer already knows when the override state can be observed and when it can be mutated, then bus code becomes less error-prone and easier to audit. The fix therefore improves both safety and maintainability.
The SPI exception is not trivial
The advisory’s note about SPI not enabling thedriver_override feature of struct bus_type is the kind of detail that tells you this patch was carefully engineered, not mechanically applied. SPI’s sysfs output convention is different: when the pointer is NULL, it emits an empty string rather than the more common (null) text used elsewhere . That sounds cosmetic, but in kernel interfaces, user-visible text can become ABI-adjacent behavior very quickly.Preserving that behavior means the patch had to avoid breaking tooling, scripts, or diagnostics that already expect the SPI-specific presentation. In other words, the fix had to improve locking without changing the subsystem’s external semantics. That is often the hardest kind of kernel change to land cleanly.
A few practical implications follow from that design choice:
- The fix is likely to be backport-friendly because it is narrow.
- It reduces the chance of subsystem-specific locking drift.
- It avoids changing sysfs-visible output unexpectedly.
- It strengthens the case for generic core helpers over bespoke code.
How the Bug Fits the Linux Kernel Pattern
Kernel vulnerability stories often look different from user-space bugs, but the pattern underneath is familiar. A subsystem evolves over time, compatibility hooks remain in place, and a new abstraction exposes a hidden assumption that had not been dangerous before. CVE-2026-31487 fits that pattern almost perfectly, because the bug is not in SPI device semantics themselves; it is in the way SPI handled a shared core concept before the generic infrastructure was fully used.The important part is that the patch is not trying to make every call site locked in the same way. Instead, it acknowledges that
match() from __driver_attach() is deliberately called in an unlocked context and adjusts the ownership model accordingly . That is a mature kernel fix: respect the architecture, don’t fight it.Lifetime bugs are often harder than buffer bugs
Buffer overflow fixes are often visually obvious. Lifetime bugs are much trickier because the code can look “right” to a casual reviewer while still being wrong under concurrency. A field may be perfectly valid during one code path and completely invalid a few instructions later, especially when callback chains are involved. That is why use-after-free issues continue to appear even in code that has already survived years of review.This CVE also reflects a broader truth about kernel hardening: many of the best fixes are not dramatic rewrites, but migrations toward shared infrastructure. Each time the kernel centralizes a pattern like override handling, it reduces the number of places where a race can hide. The result is less code to audit and fewer subsystem-specific edge cases.
Enterprise, Embedded, and Consumer Impact
For most consumers, the immediate exposure may be limited simply because SPI driver override paths are not exercised constantly in everyday desktop use. A laptop that never binds unusual SPI peripherals may never hit the dangerous sequence at all. That said, consumers should still update when their vendor ships the fix, because “unlikely” is not the same thing as “impossible.”For enterprise environments, the story is broader. SPI is common in embedded Linux, industrial control, appliances, network gear, and specialized systems where uptime matters more than novelty. In those settings, a use-after-free in driver binding can become a real operational risk even if the bug is hard to weaponize in a conventional sense. The impact is often stability-first, but stability is exactly what critical infrastructure depends on.
Where the risk is highest
The highest exposure is likely to be in systems that:- Use vendor kernels with delayed backports.
- Run embedded or appliance workloads with custom driver stacks.
- Rely on hot-plug or reprobe behavior.
- Ship with SPI-connected peripherals that may be bound dynamically.
- Have tight uptime expectations and limited local recovery options.
The Sysfs Detail Is a Clue, Not a Footnote
One of the most revealing parts of the advisory is the note that SPI passes"" to sysfs_emit() when driver_override is NULL, instead of the more common (null) output . That detail looks tiny, but in kernel work, tiny details often explain why a bug persisted and why the fix had to be careful.The point is not simply that SPI is “different.” The point is that its external behavior has become part of its interface contract. Any attempt to turn on the generic
driver_override bus feature wholesale could change that contract and create user-visible regressions. So the developers took a more surgical route: adopt the generic locking benefit without exposing the generic formatting behavior.Why this matters to maintainers
This kind of patch is a good example of modern Linux maintenance discipline. The kernel increasingly prefers to reuse core mechanisms while keeping subsystem quirks intact where those quirks are already observable by userspace. That is the difference between a dangerous abstraction and a useful one.It also makes the code easier to reason about going forward. If SPI no longer owns the locking story for this field, future maintainers have one less local rule to remember. In a codebase as large as the kernel, that reduction in cognitive overhead is a real security benefit.
Some practical takeaways:
- Consistency in core helpers reduces race conditions.
- Subsystem quirks must be preserved when they are ABI-relevant.
- Generic locking usually beats duplicated local logic.
- Careful backports can improve security without destabilizing behavior.
Why NVD Scoring Lag Should Not Delay Action
The current record notes that NVD has not yet assigned a CVSS score, which is common for fresh kernel CVEs while enrichment catches up . That should not be interpreted as a signal to wait. In kernel security, upstream fix availability and stable-tree propagation are usually better indicators of operational urgency than a placeholder score.This is especially true when the upstream description is specific enough to reveal the risk surface. Here, we know the bug involves a
driver_override lifetime issue during driver attachment, and we know the fix has already been engineered into the SPI path . That is enough for most organizations to treat the issue as a normal kernel patch item.What admins should do now
A sensible response is straightforward:- Identify whether your Linux fleet uses SPI-connected hardware or SPI-heavy embedded images.
- Check whether your vendor kernel includes the CVE-2026-31487 fix or the relevant backport.
- Prioritize the update in the next maintenance cycle if the affected path is present.
- Verify that the vendor’s patch does not alter SPI sysfs behavior unexpectedly.
- Watch for follow-on advisories if your distribution bundles the fix under a different package revision.
Competitive and Ecosystem Implications
Although this is a Linux kernel CVE, it has broader implications for the ecosystem around Linux distribution, appliance shipping, and managed infrastructure. Vendors increasingly compete on patch velocity and patch quality, not just on feature lists. A narrow, understandable fix like this one becomes a test of whether a vendor can ingest upstream security improvements quickly and safely.For enterprise customers, that turns kernel maintenance into a procurement concern. If one platform vendor consistently backports driver-core fixes cleanly and another drifts, the difference can show up in uptime, support costs, and security audit outcomes. In other words, the impact of CVE-2026-31487 extends beyond one subsystem; it reflects the operational maturity of the vendor stack.
Why this helps the Linux model
The Linux kernel’s stable process is built for exactly this kind of issue: a small, well-understood change that can be shipped widely with low regression risk. The advisory’s references to multiple stable commits reinforce that pattern and suggest the fix is already moving through the normal support channels . That is good news for users because it shortens the time between disclosure and practical protection.The bigger ecosystem lesson is that security quality is also maintenance quality. Vendors that can prove they track upstream bug lifecycles closely are usually the ones that earn trust in enterprise environments. That trust is built one patch at a time.
Strengths and Opportunities
The good news is that this vulnerability appears to have a clean, contained remedy. The fix leverages established driver-core infrastructure, keeps SPI-specific output behavior intact, and reduces the chance of future locking mistakes in the same area . That combination makes the patch valuable both technically and operationally.It also creates an opportunity for administrators and vendors to tighten their kernel hygiene around driver binding paths. Small bugs like this one are often the ones that get deferred because they do not look dramatic, but they are exactly the kind that can accumulate into reliability problems if left unpatched.
- Narrow patch scope makes backporting easier.
- Generic locking reduces the chance of future races.
- SPI semantics remain stable for userspace and tooling.
- Stable-tree propagation improves real-world protection.
- Kernel maintainers gain a cleaner long-term model.
- Operators can fold the fix into ordinary patch windows.
- Security teams get a concrete CVE to track across fleets.
Risks and Concerns
The primary risk is that teams may underestimate the issue because it does not sound like a classic remote exploit. That would be a mistake. Kernel use-after-free bugs are serious even when the first visible symptom is a crash, because they can destabilize privileged code paths and create hard-to-diagnose outages.There is also a long-tail exposure problem. Many systems run vendor kernels, appliance images, or older LTS branches where upstream fixes arrive only after backport work. That means the existence of a public CVE does not guarantee immediate protection in the field.
- The bug may be dismissed as a stability issue rather than a security issue.
- Vendor backports may arrive on different schedules.
- Some fleets may not know they rely on SPI-bound hardware.
- Regression concerns could slow patch adoption.
- Operators may assume the CVE is irrelevant if NVD scoring is still pending.
- Embedded systems often receive updates less frequently than general-purpose servers.
- A rare driver-binding path can still create high-impact downtime.
What to Watch Next
The immediate next step is straightforward: watch for vendor kernel advisories and backports that carry the SPIdriver_override fix into supported branches. Because the patch is narrow and based on driver-core infrastructure, it should travel well across stable releases, but operators should still verify actual package builds rather than relying on version assumptions alone.It will also be worth watching whether maintainers audit neighboring code for similar driver-core assumptions. Once one callback path is found to depend on state that can be observed without the device lock, it is reasonable to look for other places where subsystem code is still handling ownership rules locally instead of delegating them to the core.
Practical watch list
- Stable and vendor backports for CVE-2026-31487.
- Any follow-up SPI cleanups involving driver_override.
- Distribution advisories that clarify affected kernel branches.
- Regression reports about SPI sysfs output or driver binding behavior.
- Enterprise patch guidance for embedded and appliance kernels.
CVE-2026-31487 is the kind of vulnerability that rewards careful engineering rather than dramatic response. It is a small patch with a large lesson: when lifetime rules live in the kernel, the safest place for them is often the generic infrastructure layer, not a subsystem’s local code. That is good news for Linux users, good news for maintainers, and a useful reminder that the quietest kernel bugs are sometimes the ones worth taking most seriously.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center