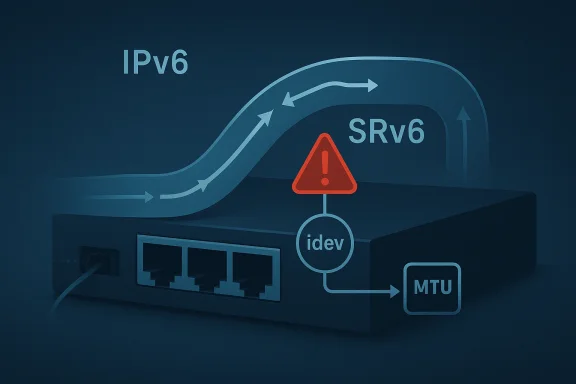
CVE-2026-23442 is a small-looking Linux kernel fix with the kind of operational consequences that make networking teams sit up and take notice. The vulnerability centers on IPv6 Segment Routing over IPv6 (SRv6) paths, where the kernel can end up dereferencing a NULL idev pointer if the device has no IPv6 configuration. In practical terms, that can mean a kernel crash in code paths that should have been defensive all along, especially on devices with unusual MTU settings or during unregister transitions. The upstream remedy is straightforward—add NULL checks in the SRv6 receive and validation paths—but the reason it matters is much larger than the patch itself.
The published description is concise:
The most important technical clue in the advisory is the mention of devices with MTU below
This CVE also fits a broader pattern in Linux kernel security reporting over the past year: many newly published issues are not dramatic exploit primitives, but crisp, narrowly scoped robustness bugs that still matter because they can crash core subsystems. A NULL pointer dereference in the networking stack is still a denial-of-service risk, and in infrastructure, denial of service is not “just a crash.” It can take out routers, appliances, containers, or hosts that carry traffic for entire applications.
For Microsoft customers, the appearance of the CVE in the Microsoft Security Update Guide is a reminder that upstream Linux issues can appear downstream in cloud images, appliances, and managed environments even when the patch originates entirely outside Redmond. The exact product scope may differ by build and packaging, but the relevant lesson is the same: if your fleet runs a kernel branch that includes the vulnerable code, you need to map the fix, not just read the headline.
That tension matters because the Linux networking stack has a long history of bugs involving missing checks on per-device or per-route IPv6 state. The recurring theme is not complexity alone; it is the interaction between packet-processing speed and lifecycle correctness. When interfaces come and go, or when IPv6 support is absent, incomplete, or disabled, the kernel must be careful about every pointer it dereferences. In many past fixes, maintainers have added exactly the sort of guard now seen in CVE-2026-23442.
The SRv6 code path is especially sensitive because it combines extension-header parsing, HMAC validation, and routing behavior in a tight receive path. A miss in any one of those stages can become a system-level event, not just a packet drop. The kernel’s job is to be conservative when state is missing; the bug here is that the code apparently assumed the device context existed when it might not.
There is also a historical lesson in how this vulnerability was surfaced. The bug was received from kernel.org and then carried into the NVD dataset, which is the normal upstream-to-downstream route for Linux kernel CVEs. That makes the kernel maintainers’ wording important: it is not a theoretical concern, but a resolved defect with specific functions named and specific conditions described.
The exploitability profile appears to be limited to availability impact, not remote code execution, at least from the information currently published. That does not make it minor. In a kernel, a crash in a packet path can still be a meaningful security event, especially on systems where uptime is the product. For edge appliances, distributed systems, and virtualized routers, a repeated crash can be enough to trigger failover loops or traffic loss.
The published condition list is revealing. If the device has no IPv6 configuration because its MTU is too small, the IPv6 device object may not exist. If the device has already been unregistered, the object may also be gone. Those are mundane states, but they are exactly the kind that show up in real operations during reconfiguration, maintenance, or failure recovery.
This is why the vulnerability is worth treating as a correctness issue with security consequences. The kernel should never require a perfectly ordinary lifecycle edge to become fatal. When a network stack makes that mistake, attackers may not need sophisticated input; they may only need to reach a path that the code failed to harden.
The advisory’s wording suggests that the problem is not in the concept of SRv6 itself, but in the handling of device context lookup within the SRv6 receive logic. That is a subtle distinction. It means the protocol can be sound while the implementation still fails under a lifecycle edge the authors did not fully guard against.
For consumers, the exposure is more indirect but still real. Home users are less likely to run SRv6 intentionally, but they may still inherit the vulnerable code in vendor kernels, appliances, or embedded devices built on Linux networking components. The risk there is less about targeted exploitation and more about unexpected instability after a firmware update, a reconfiguration, or a router teardown event.
The bigger lesson is that kernel networking bugs are rarely isolated to one product family. Linux appears everywhere: in cloud images, virtual switches, firewall appliances, orchestration nodes, and carrier gear. A fix in the upstream kernel may need to move through multiple vendor trees before operators actually get relief, which is why patch tracking matters more than CVE labels alone.
There is also a reliability dimension that often gets underplayed. When operators see a NULL dereference, they may think “crash only.” But in a routed environment, crashing the wrong node can cause reconvergence storms, temporary packet loss, and cascading failures in dependent services. That is the kind of quiet operational pain that security teams should care about.
Small fixes like this can look boring compared with memory-corruption headlines, but they are often the most important maintenance work in a mature kernel. They close off crash primitives, reduce fuzzing fallout, and make the code more consistent with surrounding checks. In the Linux IPv6 stack especially, that consistency matters because many functions share the same fragile assumptions about device state.
The presence of stable-kernel coverage also matters. The patch surfaced in a stable update listing, which is a sign that maintainers considered it suitable for supported branches rather than leaving it only in a bleeding-edge release. That tends to accelerate ecosystem remediation, especially for vendors who mirror upstream stable commits into their own kernels.
That pattern is especially visible in IPv6 because the stack is broad, fast-moving, and widely reused by advanced features. SRv6, extension headers, VRF integration, routing, multicast, and tunnel logic all touch similar kinds of state. As a result, one family of defensive fixes often reveals where other code paths deserve a second look.
If you run infrastructure that enables SRv6, especially on routing nodes or advanced edge devices, this should be treated as a priority maintenance item. Even if you are not intentionally using SRv6, the vulnerable code may still be present in the kernel image. If you cannot patch immediately, the safest interim measure is to reduce exposure on systems where IPv6 routing features are unnecessary or where the affected code path is not operationally required.
It is also worth watching for additional IPv6 hardening patches that may be adjacent to this one. When maintainers find a missing NULL check in one SRv6 path, they often discover closely related assumptions elsewhere in the same subsystem. That does not mean another CVE is inevitable, but it does mean defenders should expect more defensive maintenance in the IPv6 stack as kernel auditors keep tightening lifecycle handling.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The published description is concise: __in6_dev_get() can return NULL when a device has no IPv6 configuration, and the fix adds NULL checks in both seg6_hmac_validate_skb() and ipv6_srh_rcv() to prevent potential NULL pointer dereferences. That is classic kernel hardening work, but it also signals a deeper truth about the IPv6 stack: the most dangerous bugs are often not exotic memory-corruption exploits, but overlooked assumptions about object lifetime and protocol state. In this case, the assumption was that an IPv6 device context would always exist when SRv6 code needed it.The most important technical clue in the advisory is the mention of devices with MTU below
IPV6_MIN_MTU and devices after NETDEV_UNREGISTER. That means the vulnerable path is tied to lifecycle edges, not steady-state traffic. Those are exactly the kind of conditions that slip past normal testing, because they usually require unusual interface configurations, hot-unplug or teardown timing, or a packet arriving just as the kernel is tearing state down.This CVE also fits a broader pattern in Linux kernel security reporting over the past year: many newly published issues are not dramatic exploit primitives, but crisp, narrowly scoped robustness bugs that still matter because they can crash core subsystems. A NULL pointer dereference in the networking stack is still a denial-of-service risk, and in infrastructure, denial of service is not “just a crash.” It can take out routers, appliances, containers, or hosts that carry traffic for entire applications.
For Microsoft customers, the appearance of the CVE in the Microsoft Security Update Guide is a reminder that upstream Linux issues can appear downstream in cloud images, appliances, and managed environments even when the patch originates entirely outside Redmond. The exact product scope may differ by build and packaging, but the relevant lesson is the same: if your fleet runs a kernel branch that includes the vulnerable code, you need to map the fix, not just read the headline.
Background
SRv6 is one of those networking technologies that sounds abstract until you deploy it. It extends IPv6 with segment-routing metadata so operators can steer packets through specific service chains or topological paths, which makes it useful for carrier networks, data centers, and advanced overlay designs. Because SRv6 lives close to the kernel’s forwarding path, it inherits the same pressure that all fast-path code faces: high throughput, low tolerance for overhead, and a constant temptation to assume the state you want is already there.That tension matters because the Linux networking stack has a long history of bugs involving missing checks on per-device or per-route IPv6 state. The recurring theme is not complexity alone; it is the interaction between packet-processing speed and lifecycle correctness. When interfaces come and go, or when IPv6 support is absent, incomplete, or disabled, the kernel must be careful about every pointer it dereferences. In many past fixes, maintainers have added exactly the sort of guard now seen in CVE-2026-23442.
The SRv6 code path is especially sensitive because it combines extension-header parsing, HMAC validation, and routing behavior in a tight receive path. A miss in any one of those stages can become a system-level event, not just a packet drop. The kernel’s job is to be conservative when state is missing; the bug here is that the code apparently assumed the device context existed when it might not.
There is also a historical lesson in how this vulnerability was surfaced. The bug was received from kernel.org and then carried into the NVD dataset, which is the normal upstream-to-downstream route for Linux kernel CVEs. That makes the kernel maintainers’ wording important: it is not a theoretical concern, but a resolved defect with specific functions named and specific conditions described.
Why NULL checks keep recurring
A NULL check is the simplest fix in software, but in kernel security it often represents the closure of a long, messy chain of assumptions. The code may have been written for a “normal” device state and later exposed to edge cases where the object could disappear. Once that happens, every dereference becomes a crash candidate. The danger is not just the pointer itself; it is the false confidence that upstream layers will always provide valid state.Why SRv6 is a high-value path
SRv6 is not a niche toy feature. It is part of the modern toolkit for traffic engineering and service chaining, and that gives it outsized importance in environments where Linux acts as a router, edge node, or virtual appliance. When a vulnerability lands in SRv6 receive logic, the blast radius can include infrastructure that operators assumed was “just routing,” not a security-sensitive attack surface.What the Vulnerability Actually Is
At the center of CVE-2026-23442 is a classic kernel hazard: a helper returns NULL, and downstream code treats the result as guaranteed. Here, the helper is__in6_dev_get(), which can legitimately return no IPv6 device context under certain conditions. The fix is to check the return value before using it in seg6_hmac_validate_skb() and ipv6_srh_rcv().The exploitability profile appears to be limited to availability impact, not remote code execution, at least from the information currently published. That does not make it minor. In a kernel, a crash in a packet path can still be a meaningful security event, especially on systems where uptime is the product. For edge appliances, distributed systems, and virtualized routers, a repeated crash can be enough to trigger failover loops or traffic loss.
The published condition list is revealing. If the device has no IPv6 configuration because its MTU is too small, the IPv6 device object may not exist. If the device has already been unregistered, the object may also be gone. Those are mundane states, but they are exactly the kind that show up in real operations during reconfiguration, maintenance, or failure recovery.
This is why the vulnerability is worth treating as a correctness issue with security consequences. The kernel should never require a perfectly ordinary lifecycle edge to become fatal. When a network stack makes that mistake, attackers may not need sophisticated input; they may only need to reach a path that the code failed to harden.
Functions in the patch
The two functions named in the advisory matter because they sit in different SRv6 subpaths.seg6_hmac_validate_skb() handles authentication-related validation, while ipv6_srh_rcv() is part of the receive path for Segment Routing Headers. Fixing both closes the obvious dereference spots and reduces the chance that a nearby code path can still stumble over the same missing state.Why “NULL pointer dereference” still matters
A NULL-pointer crash is not glamorous, but it is very often how robust systems die. In kernel space, a panic or oops can be just as disruptive as a memory corruption issue if it brings down a critical host. The key difference is that the attack surface is usually easier to reason about, which is exactly why these bugs keep getting fixed upstream and backported.How SRv6 Paths Expose the Bug
SRv6 processing works only when the kernel is already doing a lot of work on behalf of the packet. That includes parsing extension headers, understanding local versus transit behavior, and deciding whether HMAC checks or segment-list handling should occur. Every one of those steps assumes the surrounding device state is sane, and every assumption is a place where a missing NULL check can become a crash.The advisory’s wording suggests that the problem is not in the concept of SRv6 itself, but in the handling of device context lookup within the SRv6 receive logic. That is a subtle distinction. It means the protocol can be sound while the implementation still fails under a lifecycle edge the authors did not fully guard against.
Lifecycle edge cases
Interface registration and teardown are notoriously tricky in the kernel. Code paths that are safe when a device is fully initialized can behave very differently when the device disappears, is being unregistered, or never had the relevant subsystem enabled in the first place. The presence ofNETDEV_UNREGISTER in the advisory tells you this bug belongs to that class of teardown-sensitive problems.Packet-path assumptions
The fast path tends to be optimized around the assumption that common cases are common. That is good for performance and bad for resilience if the slow-path checks are incomplete. In this bug, the missing defense was not a sophisticated logic gate; it was a simple validation step that should have been there before dereference. That simplicity is part of what makes the fix a high-value hardening update.Why This Is an Operational Risk
For enterprises, the immediate question is not whether this looks flashy on a vulnerability scanner. It is whether a host that participates in SRv6 forwarding, packet inspection, or advanced routing can be knocked over by malformed traffic or a configuration edge. A kernel oops in a network-facing role can quickly become a service outage, and that is especially true in cluster ingress, virtual routing, and edge appliance scenarios.For consumers, the exposure is more indirect but still real. Home users are less likely to run SRv6 intentionally, but they may still inherit the vulnerable code in vendor kernels, appliances, or embedded devices built on Linux networking components. The risk there is less about targeted exploitation and more about unexpected instability after a firmware update, a reconfiguration, or a router teardown event.
The bigger lesson is that kernel networking bugs are rarely isolated to one product family. Linux appears everywhere: in cloud images, virtual switches, firewall appliances, orchestration nodes, and carrier gear. A fix in the upstream kernel may need to move through multiple vendor trees before operators actually get relief, which is why patch tracking matters more than CVE labels alone.
There is also a reliability dimension that often gets underplayed. When operators see a NULL dereference, they may think “crash only.” But in a routed environment, crashing the wrong node can cause reconvergence storms, temporary packet loss, and cascading failures in dependent services. That is the kind of quiet operational pain that security teams should care about.
Enterprise impact
- SRv6-enabled routers and appliances deserve priority review.
- Cloud images may inherit the vulnerable code even if the product branding differs.
- Reconfiguration windows are riskier than steady-state traffic.
- Failover clusters can amplify a single crash into wider service disruption.
- Vendor backports may lag the upstream fix by days or weeks.
- Monitoring alerts should look for recurring kernel oopses, not only exploit signatures.
The Fix and Why It Is Small but Important
The remediation is exactly what kernel engineers usually do when a helper can return NULL: add checks before dereferencing the returned pointer. In this case, the patch covers bothseg6_hmac_validate_skb() and ipv6_srh_rcv(), which suggests maintainers found the risk in more than one SRv6 touchpoint. The narrowness of the fix is reassuring, because it indicates the issue was likely contained rather than deeply entangled.Small fixes like this can look boring compared with memory-corruption headlines, but they are often the most important maintenance work in a mature kernel. They close off crash primitives, reduce fuzzing fallout, and make the code more consistent with surrounding checks. In the Linux IPv6 stack especially, that consistency matters because many functions share the same fragile assumptions about device state.
What the patch tells us
The wording “Add NULL checks for idev returned by__in6_dev_get()” is itself informative. It tells us the authors are not changing protocol behavior; they are only ensuring the kernel handles absence safely. That usually means low regression risk, which is one reason these fixes are often backported aggressively to stable trees.The presence of stable-kernel coverage also matters. The patch surfaced in a stable update listing, which is a sign that maintainers considered it suitable for supported branches rather than leaving it only in a bleeding-edge release. That tends to accelerate ecosystem remediation, especially for vendors who mirror upstream stable commits into their own kernels.
How It Compares With Other Recent IPv6 Kernel Bugs
This CVE is not an outlier; it is part of a recurring stream of IPv6 robustness fixes. Recent kernel issues have repeatedly involved missing NULL checks, invalid assumptions about route-device state, or teardown races in adjacent networking code. The technical shape changes, but the lesson stays the same: when the kernel crosses a lifecycle boundary, it must verify every pointer again.That pattern is especially visible in IPv6 because the stack is broad, fast-moving, and widely reused by advanced features. SRv6, extension headers, VRF integration, routing, multicast, and tunnel logic all touch similar kinds of state. As a result, one family of defensive fixes often reveals where other code paths deserve a second look.
Why the pattern matters
If one helper can return NULL under legitimate conditions, then any other helper with similar lifetime semantics may deserve audit attention. That is why kernel security teams often treat a CVE like this as a signal, not just a one-off patch. The security value is not only in the fix, but in the audit trail it creates for adjacent code.What Administrators Should Do
The first priority is to determine whether your kernel build includes the vulnerable SRv6 code paths and whether your vendor has already backported the fix. On Linux fleets, the practical answer is rarely “check the CVE page and move on.” You need to map the upstream commit to your distro kernel, appliance firmware, or cloud image. That is the only reliable way to know whether you are exposed.If you run infrastructure that enables SRv6, especially on routing nodes or advanced edge devices, this should be treated as a priority maintenance item. Even if you are not intentionally using SRv6, the vulnerable code may still be present in the kernel image. If you cannot patch immediately, the safest interim measure is to reduce exposure on systems where IPv6 routing features are unnecessary or where the affected code path is not operationally required.
A practical response plan
- Identify all kernels that contain the affected upstream code.
- Check whether your vendor package already includes the stable backport.
- Prioritize SRv6-enabled routers, gateways, and appliances.
- Watch for kernel oopses tied to IPv6 packet processing.
- Validate whether IPv6 is active on devices that should not be handling it.
- Confirm that hot-unplug and teardown procedures do not leave unexpected packet paths exposed.
Strengths and Opportunities
The good news is that this vulnerability is narrow, understandable, and easy to validate once you know where to look. It does not suggest a broad architectural weakness so much as a missing guard in a couple of well-defined functions. That makes remediation comparatively straightforward and gives operators a clear action path.- The fix is small and low-risk to backport.
- The affected functions are specific and easy to audit.
- The conditions are clear: absent IPv6 device state.
- The operational impact is well understood: potential kernel crash.
- The issue reinforces better lifecycle discipline in fast-path code.
- The patch improves consistency with other IPv6 null-check logic.
- Stable-tree publication should speed vendor uptake.
Risks and Concerns
The concern, of course, is that small kernel bugs often have large operational effects when they live on the packet path. Even a simple NULL dereference can take down the wrong router, VM host, or appliance at the wrong time. And because the bug is in IPv6 SRv6 handling, the real-world impact depends heavily on how much of that feature set is exposed in your environment.- Kernel crashes can trigger cascading service failures.
- Vendor backport timing may lag upstream publication.
- SRv6 deployments are niche but high-value targets.
- Appliances may ship with vulnerable code long after disclosure.
- Configuration-driven bugs are easy to miss in testing.
- Monitoring may not distinguish crash causes cleanly.
- Operators may falsely assume “not using SRv6” means “not affected.”
Looking Ahead
The next few days will likely be about backports, vendor advisories, and confirmation that the fix is landing across supported Linux branches. The important question is not whether the upstream code is fixed—it is—but how quickly downstream distributions and appliance vendors move to absorb the change. That timeline will determine whether CVE-2026-23442 remains a footnote or becomes a real operational event for the people running IPv6-heavy infrastructure.It is also worth watching for additional IPv6 hardening patches that may be adjacent to this one. When maintainers find a missing NULL check in one SRv6 path, they often discover closely related assumptions elsewhere in the same subsystem. That does not mean another CVE is inevitable, but it does mean defenders should expect more defensive maintenance in the IPv6 stack as kernel auditors keep tightening lifecycle handling.
What to watch next
- Vendor backport announcements for major enterprise distributions
- Cloud image refreshes that pull in the stable kernel fix
- Any follow-on IPv6/SRv6 hardening commits
- Reports of kernel oopses involving
ipv6_srh_rcv()orseg6_hmac_validate_skb() - Appliance firmware advisories that map the CVE to shipped kernel builds
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
Last edited: