Windows Projected File System has quietly become one of the more interesting pieces of the Windows storage stack, and that matters because the latest MSRC entry for CVE-2026-27927 puts a familiar but still serious class of flaw back in the spotlight: local privilege escalation. Microsoft’s own description frames the issue as a Windows Projected File System Elevation of Privilege Vulnerability, but the accompanying confidence metric is what really tells the story, because it measures how certain we can be that the flaw exists and how much technical detail is already in the public domain. In practice, that means defenders should treat this as a potentially exploitable local security boundary problem even before every implementation detail is fully understood.
Windows Projected File System, or ProjFS, is a user-mode virtualization framework that lets an application present hierarchical data as files and folders in a normal Windows namespace. Microsoft describes it as a way for a “provider” to project backing-store data into the file system so it appears local, which is exactly why it’s attractive for large-scale developer workflows and virtualized content systems. Microsoft’s own examples include registry virtualization and Git-related workloads, which tell you immediately that ProjFS is designed for convenience, scale, and transparency rather than for highly defensive isolation.
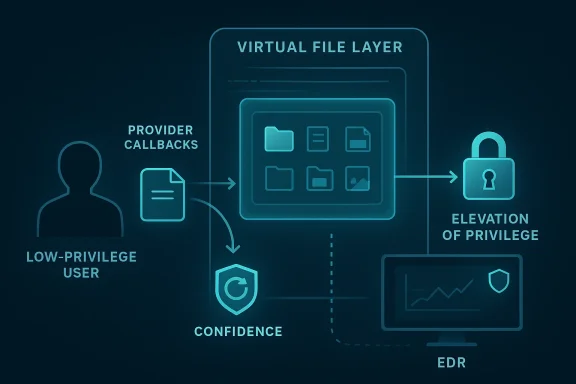
That design choice is also what makes ProjFS security-relevant. When a file system abstraction is meant to hide the fact that data may be remote or synthesized, any bug in the transition between user-mode provider logic and kernel-facing file operations can become an escalation path. Microsoft’s ProjFS documentation emphasizes that the system is intended to make projected data appear as if it exists locally, and that creates a broad surface for path handling, notification processing, enumeration, and provider callbacks. Those are all classic places where small mistakes can become security boundary failures.
Microsoft’s disclosure model has also become more informative in recent years. In 2024, MSRC said it would begin publishing CWE root-cause information for Microsoft CVEs, a move intended to improve transparency and help customers understand vulnerability classes rather than just individual numbers. That matters here because the confidence metric on a CVE page is not just a metadata curiosity; it is part of Microsoft’s broader effort to tell defenders how much technical certainty exists behind a report. If the page shows a high-confidence issue, defenders can prioritize it more aggressively than a speculative or partially understood case.
The reason local elevation bugs continue to matter so much is simple: attackers rarely need them on day one, but they often need them on day two. Microsoft’s 2025 analysis of a CLFS zero-day showed how a local elevation issue can be chained into ransomware deployment once an initial foothold is obtained. That pattern is important context for ProjFS issues too, because file-system-centric bugs tend to sit exactly where post-compromise operators try to turn basic access into privileged access. (microsoft.com)
That confidence framing also changes how organizations should respond internally. Security teams often triage by CVSS or by whether a bug is being exploited in the wild, but confidence in the underlying flaw should affect prioritization too. A kernel-adjacent or file-system-adjacent elevation issue with strong vendor certainty is a better candidate for immediate patching, compensating controls, and exposure review than a vague advisory that lacks technical corroboration.
The feature’s design goal is to hide locality, not to maximize trust transparency. That can be excellent for usability, but it can also obscure the difference between a benign placeholder and a security-sensitive file operation, especially if the provider is privileged or interacts with elevated services. In practical terms, any flaw in ProjFS handling may become a bridge from ordinary user activity to privileged file-system behavior.
That’s why ProjFS deserves special attention. It is not just “another filesystem feature.” It is a programmable abstraction layer that intentionally changes the meaning of what a file or directory is, and that means the attack surface is not limited to content parsing alone. Bugs can arise from state transitions, placeholder handling, provider callbacks, and interactions with higher-privilege processes that assume the projected view is trustworthy.
There is also a strategic reason Microsoft publishes these flaws with more structured metadata now. By exposing standardized root-cause categories and clearer advisory details, MSRC helps customers understand whether a problem is likely to be isolated or whether it belongs to a recurring family of mistakes. That makes it easier to build longer-term defenses instead of treating every patch as a one-off event.
Microsoft’s own documentation points to scenarios like VFS for Git, which is a reminder that ProjFS is used in real-world developer workflows where large repos and projected content are commonplace. That makes the feature valuable, but it also means the ecosystem has legitimate reasons to deploy it widely. A vulnerability in such a feature is therefore not an edge case; it can affect a broad set of productivity and enterprise tooling scenarios.
In a security review, that is the kind of feature where small assumptions become dangerous. Does the provider validate names exactly once, or multiple times? Does a privileged service consume projected content with elevated trust? Can a standard user influence a path or placeholder in a way that changes the behavior of a privileged consumer? Those are not theoretical questions; they are the core of how local escalation bugs tend to materialize.
This is why file-system EoP bugs tend to be more dangerous in managed environments than in casual consumer settings. A home user who lacks privileged services may face inconvenience or localized compromise. An enterprise endpoint, by contrast, may have many privileged agents that touch files, indexes, caches, repos, logs, and synced content all day long. That dramatically increases the opportunities for exploitation chains. (microsoft.com)
From an operational perspective, the best response is to ask which systems actually use ProjFS or associated software stacks. Not every Windows machine will have the same exposure, and that makes inventory a crucial part of response. The real risk often lies in the subset of endpoints running developer tooling, virtualization layers, or synchronized file projections alongside privileged agents.
There is also a subtle point here: consumers often assume Windows security is mostly about antivirus and safe browsing, but local escalation bugs are what turn a simple compromise into a system takeover. That is why patching matters even when the flaw is not actively exploited in a headline-grabbing way. A vulnerability that is “only local” is often exactly what attackers want once they have any user-level foothold. (microsoft.com)
The consumer lesson is straightforward: if Windows Update offers a fix tied to a local elevation issue, take it seriously. Local does not mean harmless. It usually means the attacker first needs some way in, and once they are in, the flaw can make everything else worse. (microsoft.com)
The flip side is that every newly documented class of bug reminds competitors and researchers that modern Windows features are deeply layered. That may sound obvious, but the market impact is real: if virtualization, projection, and content abstraction are secure enough, they remain viable strategic capabilities; if not, enterprises begin to view them as risk multipliers that need compensating controls.
For now, the prudent reading is that the vulnerability reinforces a broader trend: modern platform security depends on making sophisticated abstractions safer, not on avoiding abstractions entirely. Windows cannot abandon features like ProjFS, but it can keep narrowing the gap between usability and trust. That is the real competitive message hidden inside disclosures like this one.
It also suggests how much technical knowledge adversaries may already have. If the issue is well understood enough for Microsoft to assign it a clear vulnerability type, threat actors may be able to reproduce or adapt the weakness faster than if the report were still largely speculative. That is exactly why defenders should avoid waiting for proof-of-concept code before responding. Waiting is a strategy attackers love.
That is the kind of triage discipline Microsoft has been encouraging through its update-guide ecosystem and advisory improvements. The point of clearer CVE metadata is to help teams make fast decisions under uncertainty. In that respect, the confidence score becomes a way to rank not just vulnerability seriousness, but response urgency.
The broader trend is also clear: Microsoft is pushing more vulnerability context into the open, and that benefits defenders who know how to use it. If CVE-2026-27927 follows the pattern of recent local escalation disclosures, expect the operational focus to shift quickly from “what is it?” to “where is it used?” and then to “how do we remove exploitable trust chains before attackers find them?” That is the right way to think about modern Windows security, because the boundary that matters is rarely the one you first notice.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Windows Projected File System, or ProjFS, is a user-mode virtualization framework that lets an application present hierarchical data as files and folders in a normal Windows namespace. Microsoft describes it as a way for a “provider” to project backing-store data into the file system so it appears local, which is exactly why it’s attractive for large-scale developer workflows and virtualized content systems. Microsoft’s own examples include registry virtualization and Git-related workloads, which tell you immediately that ProjFS is designed for convenience, scale, and transparency rather than for highly defensive isolation.That design choice is also what makes ProjFS security-relevant. When a file system abstraction is meant to hide the fact that data may be remote or synthesized, any bug in the transition between user-mode provider logic and kernel-facing file operations can become an escalation path. Microsoft’s ProjFS documentation emphasizes that the system is intended to make projected data appear as if it exists locally, and that creates a broad surface for path handling, notification processing, enumeration, and provider callbacks. Those are all classic places where small mistakes can become security boundary failures.
Microsoft’s disclosure model has also become more informative in recent years. In 2024, MSRC said it would begin publishing CWE root-cause information for Microsoft CVEs, a move intended to improve transparency and help customers understand vulnerability classes rather than just individual numbers. That matters here because the confidence metric on a CVE page is not just a metadata curiosity; it is part of Microsoft’s broader effort to tell defenders how much technical certainty exists behind a report. If the page shows a high-confidence issue, defenders can prioritize it more aggressively than a speculative or partially understood case.
The reason local elevation bugs continue to matter so much is simple: attackers rarely need them on day one, but they often need them on day two. Microsoft’s 2025 analysis of a CLFS zero-day showed how a local elevation issue can be chained into ransomware deployment once an initial foothold is obtained. That pattern is important context for ProjFS issues too, because file-system-centric bugs tend to sit exactly where post-compromise operators try to turn basic access into privileged access. (microsoft.com)
What the CVE-2026-27927 Entry Signals
At a minimum, CVE-2026-27927 tells us Microsoft believes a ProjFS-related elevation-of-privilege condition is real enough to track as a formal vulnerability. The wording is important because an elevation issue in a Windows component usually means a local attacker may be able to execute code in a more privileged context than intended. Even without a public exploit write-up, that is enough for enterprise defenders to think in terms of privilege boundaries, service accounts, and post-compromise hardening.Confidence Is Its Own Risk Signal
The metric you highlighted is not about severity alone. It measures how confident Microsoft is that the vulnerability exists and how much technical detail is known about the weakness, which is useful because attackers also use public detail to gauge feasibility. In other words, a vulnerability can be dangerous even if the root cause is still being mapped out, but a high-confidence disclosure usually gives both defenders and adversaries a clearer path toward action.That confidence framing also changes how organizations should respond internally. Security teams often triage by CVSS or by whether a bug is being exploited in the wild, but confidence in the underlying flaw should affect prioritization too. A kernel-adjacent or file-system-adjacent elevation issue with strong vendor certainty is a better candidate for immediate patching, compensating controls, and exposure review than a vague advisory that lacks technical corroboration.
Why ProjFS Is a Nontrivial Surface
ProjFS is not a minor accessory feature. It exposes a provider model, virtualization instance lifecycle, directory enumeration, file data retrieval, and asynchronous callbacks, all of which create multiple boundaries between user-mode logic and Windows filesystem semantics. That is a rich attack surface because the security of the whole feature depends on how correctly the provider and the OS interpret state, path identity, and metadata transitions.The feature’s design goal is to hide locality, not to maximize trust transparency. That can be excellent for usability, but it can also obscure the difference between a benign placeholder and a security-sensitive file operation, especially if the provider is privileged or interacts with elevated services. In practical terms, any flaw in ProjFS handling may become a bridge from ordinary user activity to privileged file-system behavior.
- The issue is local, not remote, which means initial access may still be needed.
- The vulnerable surface is tied to file system projection logic.
- The likely impact is privilege escalation, not just service instability.
- The practical risk rises if a privileged service depends on ProjFS-backed paths.
Why File-System EoP Bugs Keep Coming Back
Windows has a long history of elevation-of-privilege flaws clustered around filesystem and kernel-adjacent components. That is not accidental; the operating system’s security model relies on a vast amount of path interpretation, object translation, and access mediation. Each of those steps can become a bug class if the wrong identity, namespace, or redirection state is trusted.The Pattern Microsoft Keeps Warning About
Microsoft’s 2025 RedirectionGuard work is a good example of the company describing the broader problem rather than a single CVE. MSRC explained that unsafe junction traversal becomes dangerous when privileged services access filesystem paths without realizing they can be redirected, especially when an attacker can influence those paths from a lower privilege context. That is the same underlying theme behind a lot of Windows local privilege escalation research: the attacker cannot directly do the privileged operation, so they manipulate the privileged process into doing it for them.That’s why ProjFS deserves special attention. It is not just “another filesystem feature.” It is a programmable abstraction layer that intentionally changes the meaning of what a file or directory is, and that means the attack surface is not limited to content parsing alone. Bugs can arise from state transitions, placeholder handling, provider callbacks, and interactions with higher-privilege processes that assume the projected view is trustworthy.
Historical Precedent Matters
Microsoft’s own CLFS zero-day response in 2025 showed how attackers value elevation bugs because they convert an initial foothold into broad system control. The company explicitly noted that ransomware threat actors prize post-compromise EoP exploits for escalating from commodity access to privileged access and then pushing ransomware across an environment. That lesson transfers directly to ProjFS: even if the flaw starts as a local issue, the operational payoff can be much higher in a real enterprise breach. (microsoft.com)There is also a strategic reason Microsoft publishes these flaws with more structured metadata now. By exposing standardized root-cause categories and clearer advisory details, MSRC helps customers understand whether a problem is likely to be isolated or whether it belongs to a recurring family of mistakes. That makes it easier to build longer-term defenses instead of treating every patch as a one-off event.
- File-system EoP bugs often involve identity confusion.
- They frequently affect privileged services rather than ordinary apps.
- They are attractive to ransomware operators after initial compromise.
- Vendor transparency now gives defenders more usable context than in past years.
What ProjFS Actually Does
To understand the security implications of ProjFS, it helps to step back from the CVE and look at the feature itself. Microsoft says a provider can project hierarchical backing-store data into the file system so the result appears as files and directories. In practical terms, ProjFS lets software create a virtual file-system view that is controlled by a user-mode provider, which can be incredibly powerful but also risky if that provider is exposed to attacker-controlled inputs.Virtualization Is Powerful, but It Blurs Boundaries
The central tradeoff is that virtualization reduces friction for users while increasing the complexity of trust decisions. If an application or service assumes a projected path behaves exactly like a local path, then it can be tricked into processing data or metadata in ways it never intended. That matters because elevation bugs often emerge when a privileged component trusts a representation rather than the underlying reality.Microsoft’s own documentation points to scenarios like VFS for Git, which is a reminder that ProjFS is used in real-world developer workflows where large repos and projected content are commonplace. That makes the feature valuable, but it also means the ecosystem has legitimate reasons to deploy it widely. A vulnerability in such a feature is therefore not an edge case; it can affect a broad set of productivity and enterprise tooling scenarios.
The Provider Model Creates Attack Surface
The provider model is where the technical complexity becomes security-relevant. ProjFS providers must manage enumeration, content delivery, and change notifications, and those callbacks can be asynchronous. That means the system depends on the correctness of both the provider implementation and Windows’ own mediation logic, which expands the number of ways a bug can appear.In a security review, that is the kind of feature where small assumptions become dangerous. Does the provider validate names exactly once, or multiple times? Does a privileged service consume projected content with elevated trust? Can a standard user influence a path or placeholder in a way that changes the behavior of a privileged consumer? Those are not theoretical questions; they are the core of how local escalation bugs tend to materialize.
- Projection makes remote or virtual data appear local.
- Providers can influence what the file system presents.
- Asynchronous callbacks add complexity to trust boundaries.
- Enterprise deployments may use ProjFS without realizing the attack implications.
Likely Enterprise Impact
For enterprises, CVE-2026-27927 is best understood as a privilege-chain risk. If the affected ProjFS path can be reached by a standard user and then consumed by a more privileged component, the vulnerability could become a stepping stone to SYSTEM-level or admin-level execution. That is the kind of flaw defenders care about because it can turn a limited compromise into a domain-adjacent event if credentials, tokens, or service accounts are exposed afterward. (microsoft.com)Service Accounts and Automation Are the Pressure Points
Enterprise environments rely heavily on services, agents, build systems, endpoint tools, and virtualization workflows that run with elevated privileges. If any of those components interact with ProjFS-backed content, even indirectly, the risk profile changes dramatically. The issue is not only whether the workstation is vulnerable, but whether a privileged workload might touch attacker-influenced projected paths.This is why file-system EoP bugs tend to be more dangerous in managed environments than in casual consumer settings. A home user who lacks privileged services may face inconvenience or localized compromise. An enterprise endpoint, by contrast, may have many privileged agents that touch files, indexes, caches, repos, logs, and synced content all day long. That dramatically increases the opportunities for exploitation chains. (microsoft.com)
Patch Priority Should Reflect Exposure
Microsoft has repeatedly urged organizations to prioritize EoP updates when threat actors might already have a foothold. That guidance is sensible because the attacker does not need to land directly in a privileged context if they can first gain standard-user execution. Once in, local elevation bugs become force multipliers for persistence, credential access, and ransomware staging. (microsoft.com)From an operational perspective, the best response is to ask which systems actually use ProjFS or associated software stacks. Not every Windows machine will have the same exposure, and that makes inventory a crucial part of response. The real risk often lies in the subset of endpoints running developer tooling, virtualization layers, or synchronized file projections alongside privileged agents.
- Inventory systems that use ProjFS-dependent workflows.
- Check whether privileged services touch projected paths.
- Prioritize endpoints with developer tooling or sync-heavy workloads.
- Assume local EoP can become a ransomware enabler after foothold.
Consumer Impact Is Different, but Still Real
Consumer exposure is usually less dramatic than enterprise exposure, but that does not make it negligible. A local elevation bug still matters if malware has already landed, because it can bypass user-level containment and tamper with security tools, browser data, or persistence mechanisms. In other words, consumers may not be the primary target, but they are still in the blast radius once an initial compromise occurs. (microsoft.com)The Home User Scenario
For a home user, the issue likely translates into the classic “malware becomes admin” problem. A malicious attachment, script, or trojan that gets standard-user execution can sometimes chain into a local privilege escalation to disable defenses, install persistence, or steal sensitive data. The severity is lower than a wormable remote exploit, but the practical impact can still be severe. (microsoft.com)There is also a subtle point here: consumers often assume Windows security is mostly about antivirus and safe browsing, but local escalation bugs are what turn a simple compromise into a system takeover. That is why patching matters even when the flaw is not actively exploited in a headline-grabbing way. A vulnerability that is “only local” is often exactly what attackers want once they have any user-level foothold. (microsoft.com)
Why Security Messaging Matters
Microsoft’s broader transparency push helps here because consumers rarely read raw CVE pages, but security tooling and update channels can translate that into action. More structured disclosure of root cause and vulnerability class helps endpoints, EDR platforms, and IT administrators decide how urgently to deploy fixes. That is especially useful for a feature like ProjFS, where the average user may have no idea the component exists until a problem is disclosed.The consumer lesson is straightforward: if Windows Update offers a fix tied to a local elevation issue, take it seriously. Local does not mean harmless. It usually means the attacker first needs some way in, and once they are in, the flaw can make everything else worse. (microsoft.com)
- Keep Windows Update current.
- Treat malicious downloads as potentially privilege-escalating.
- Remember that local EoP can defeat endpoint protections.
- Do not assume “consumer systems” are too small to matter.
Competitive and Platform Implications
A vulnerability in ProjFS also has ecosystem implications beyond pure security response. Windows continues to compete on developer workflows, enterprise manageability, and filesystem extensibility, and projected file systems are part of that story. The more Microsoft encourages advanced virtualization and projection models, the more important it becomes to prove those abstractions are safe under adversarial conditions.Microsoft’s Security Posture as a Platform Signal
Microsoft’s move to publish more root-cause data and more advisory context is not just a documentation exercise. It is part of a platform trust story, showing that the company wants customers to understand not only what failed, but why it failed. For enterprise buyers, that transparency can be a differentiator, because it supports better patch management, risk modeling, and fleet-wide hardening.The flip side is that every newly documented class of bug reminds competitors and researchers that modern Windows features are deeply layered. That may sound obvious, but the market impact is real: if virtualization, projection, and content abstraction are secure enough, they remain viable strategic capabilities; if not, enterprises begin to view them as risk multipliers that need compensating controls.
What Rivals Will Watch
Security vendors, endpoint teams, and alternative platform providers will pay attention to whether the flaw appears to stem from path handling, namespace confusion, or provider interaction. Those categories matter because they inform both detection strategies and long-term engineering changes. If the issue is in the operating system’s mediation layer, then mitigations may need to live closer to the kernel; if it is in provider assumptions, then secure coding guidance becomes the main lever.For now, the prudent reading is that the vulnerability reinforces a broader trend: modern platform security depends on making sophisticated abstractions safer, not on avoiding abstractions entirely. Windows cannot abandon features like ProjFS, but it can keep narrowing the gap between usability and trust. That is the real competitive message hidden inside disclosures like this one.
- Security transparency is now a platform differentiator.
- Developer-oriented file virtualization remains strategically important.
- Better root-cause disclosure helps both defenders and rivals.
- Abstractions must become safer, not simpler, to remain viable.
How Defenders Should Read the Confidence Metric
The confidence metric is one of the most useful but least discussed parts of a CVE disclosure. It tells you whether the vendor is speaking from a fully confirmed vulnerability report, a partially validated research claim, or something in between. For CVE-2026-27927, that means defenders should focus not only on the severity label but on how much confidence Microsoft has in the technical reality of the flaw.From “Possible” to “Actionable”
A vulnerability with strong confidence is actionable even before all exploit details are public. That is because organizations do not need the exploit chain to be complete in order to reduce risk; they need enough certainty to patch, segment, monitor, and review exposure. In that sense, confidence is a practical operational signal, not just a research footnote.It also suggests how much technical knowledge adversaries may already have. If the issue is well understood enough for Microsoft to assign it a clear vulnerability type, threat actors may be able to reproduce or adapt the weakness faster than if the report were still largely speculative. That is exactly why defenders should avoid waiting for proof-of-concept code before responding. Waiting is a strategy attackers love.
Practical Triage Questions
A useful response is to ask a short series of questions in order. Is the affected endpoint exposed to ProjFS? Does it host privileged services that touch projected paths? Can standard users influence inputs to those paths? And if the answer is yes, what compensating controls can be applied before the patch lands across the fleet?That is the kind of triage discipline Microsoft has been encouraging through its update-guide ecosystem and advisory improvements. The point of clearer CVE metadata is to help teams make fast decisions under uncertainty. In that respect, the confidence score becomes a way to rank not just vulnerability seriousness, but response urgency.
- Confirm whether ProjFS is present on affected systems.
- Identify privileged processes that consume projected content.
- Apply the update as soon as it is available.
- Add telemetry around unusual filesystem redirection or projection behavior.
- Treat standard-user compromise as potentially one step away from admin compromise.
Strengths and Opportunities
Microsoft’s handling of CVE metadata, combined with the operational context around filesystem-based privilege escalation, gives defenders a better chance to move quickly and intelligently. The opportunity here is not just to patch one bug, but to reassess how projected filesystem technologies are used, monitored, and isolated across the fleet.- Better transparency through Microsoft’s expanded CVE/root-cause disclosures.
- Clearer risk prioritization from the confidence metric.
- Stronger incentive to inventory ProjFS exposure across endpoints.
- Opportunity to harden privileged services that touch virtualized file paths.
- Better alignment between EDR telemetry and filesystem attack patterns.
- Improved security posture for developer and enterprise workflows that rely on projected content.
- A chance to reduce attack surface by revisiting legacy trust assumptions in file handling.
Risks and Concerns
The biggest concern is that this kind of flaw can be underestimated because it is local, technical, and easy for non-specialists to overlook. But history shows that local escalation bugs are often the missing ingredient in serious intrusions, especially once attackers have already obtained a foothold through phishing, stolen credentials, or a software supply-chain compromise.- Attackers may chain the flaw with initial-access malware.
- Privileged services could turn a local bug into SYSTEM-level compromise.
- Organizations may miss exposure if they do not know they use ProjFS.
- The feature’s abstraction layer may obscure security review.
- Overconfidence in endpoint protections may delay remediation.
- A public confidence metric could help adversaries gauge feasibility.
- Enterprise environments with many automation agents may have more attack paths than they realize.
Looking Ahead
The most important question now is not whether ProjFS is useful; it clearly is. The question is whether Microsoft and the enterprise ecosystem can keep making these advanced Windows abstractions safer without sacrificing the flexibility that made them attractive in the first place. That balance will shape how much trust organizations place in projected filesystems and related virtualization features over the next several Windows release cycles.The broader trend is also clear: Microsoft is pushing more vulnerability context into the open, and that benefits defenders who know how to use it. If CVE-2026-27927 follows the pattern of recent local escalation disclosures, expect the operational focus to shift quickly from “what is it?” to “where is it used?” and then to “how do we remove exploitable trust chains before attackers find them?” That is the right way to think about modern Windows security, because the boundary that matters is rarely the one you first notice.
- Watch for a full MSRC update with patch details and affected versions.
- Monitor whether Microsoft publishes root-cause or CWE information for the flaw.
- Check whether enterprise tools or developer stacks rely on ProjFS.
- Review privileged services that interact with projected paths.
- Follow any guidance on detections, mitigations, or exploitation indicators.
Source: MSRC Security Update Guide - Microsoft Security Response Center