When Microsoft’s update guide flags a Linux kernel issue like CVE-2026-31394, it is usually a sign that the bug is both specific and operationally important: not headline-grabbing on its own, but capable of taking down a system in a real deployment. This one sits in mac80211, the Linux wireless stack, and the problem appears in the path that handles bandwidth changes for stations connected through AP_VLAN interfaces. The result is a crash risk during channel switch activity, a corner case that matters most to administrators running wireless infrastructure with advanced AP features and layered virtual interfaces.
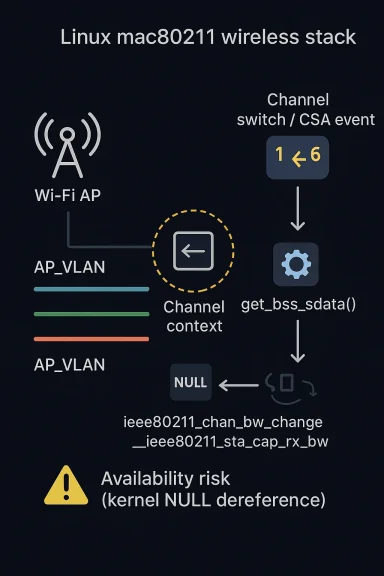
The vulnerability description points to a NULL pointer dereference during ieee80211_chan_bw_change(), with the failure surfacing in __ieee80211_sta_cap_rx_bw() when the code tries to read the channel band from an uninitialized reserved channel context. In practical terms, the bug is not about unauthorized code execution or data theft; it is about availability, stability, and trust in the wireless stack. That makes it less glamorous than remote compromise, but still highly relevant to anyone operating APs, mesh nodes, or wireless virtualization setups at scale.
The Linux mac80211 subsystem is the software framework that many Wi‑Fi drivers rely on for 802.11 logic, including station management, AP behavior, bandwidth negotiation, and channel context handling. Its design lets drivers focus on hardware specifics while mac80211 coordinates higher-level wireless behavior, which is why bugs here can affect a broad range of devices without living in a single vendor driver. The subsystem documentation shows how deeply mac80211 is involved in AP mode, station state transitions, and channel-aware operations, including the exact kinds of callbacks and state handling that make bandwidth changes nontrivial.
AP VLAN support is one of those features that looks simple from the outside and becomes intricate the moment you trace the code paths. The kernel documentation notes that multiple transmission keys and per-station handling can be involved when VLANs are configured for an access point, which reflects how the stack maintains separate logical views for traffic and policy. In this bug, that abstraction boundary matters: a station on an AP_VLAN interface points at VLAN-specific sdata, but the bandwidth-change code expected AP-side reservation state. That mismatch is what created the crash condition.
The vulnerability has already been tracked by multiple security databases and distro ecosystems, which is typical once a kernel crash lands in a common subsystem. Public writeups consistently describe the same failure mode:
This specific issue is tied to channel switch announcements and bandwidth transitions, which are not everyday operations for a home laptop but are common enough in managed wireless deployments. When those transitions collide with AP VLAN station handling, the stack can walk the wrong data structure and fault. In other words, the bug is narrow in trigger conditions but broad in consequence once the wrong conditions are met.
That distinction is subtle, and it is exactly why bugs like this can survive until a CSA or bandwidth event. Most of the time, the code paths line up cleanly. Under the right interface topology, though, the pointer that “should” represent an AP station instead resolves to VLAN-associated state that never took part in chanctx reservation at all.
Once the code reaches __ieee80211_sta_cap_rx_bw(), it tries to read
That kind of fix is common in kernel networking code. The kernel often has multiple logical views of the same object, and the safest repair is to ensure the helper function walks back to the canonical owner before dereferencing deep state. It is a reminder that in mac80211, the right pointer in the right context matters more than the nominal object type.
The bug appears during that orchestration because bandwidth capability checks are being performed while the system is still reconciling station state and channel state. If the code looks at the wrong sdata instance, it can conclude that a channel reservation exists when it does not, or simply follow a NULL pointer and die. The failure mode is therefore tied to the intersection of topology, configuration, and runtime channel management.
That matters because it lowers the bar from exotic exploit craft to ordinary administrative activity. A crash that only happens during channel migration might seem niche, but in enterprise wireless, channel migration is not rare. It is part of the normal life cycle of a well-managed WLAN.
That difference is important because it changes how operators should think about risk. In the consumer case, the problem is mostly about futureproofing and receiving vendor fixes. In the enterprise case, it is about whether a wireless outage could be triggered during routine channel management, site surveys, or radio optimization windows.
The AP mode documentation also highlights how complex the subsystem becomes once power-save, station transitions, and interface-specific state are layered on top of each other. That is the environment in which
This issue shows why those helpers matter. The wrong direct pointer was not merely inconvenient; it was semantically wrong for the reservation data being accessed. The helper restored the correct ownership chain and eliminated the mismatch that led to the NULL dereference.
But complexity also creates places where assumptions become stale. If a function assumes a station belongs directly to the AP context and then encounters a VLAN indirection, it can read state that was never meant for that branch. In kernel code, that kind of mistaken assumption is often all it takes to produce a crash.
The main threat model is an attacker who can influence the conditions under which bandwidth changes or channel switches occur, or an administrator who unknowingly triggers them in a vulnerable configuration. In other words, the bug may be more about operational exposure than about an internet-scale exploit. That does not make it trivial; it makes it situational, which is often how infrastructure bugs behave.
For defenders, that means a security scan alone is not enough. You need to understand the wireless role of the host, the configuration of virtual interfaces, and whether the radio management stack might naturally encounter the edge case during day-to-day use.
That is why even a medium-severity issue can matter disproportionately. In wireless infrastructure, downtime often spreads beyond the device that actually faulted. A single AP reboot can cause client reauthentication churn, roaming instability, and cascading service complaints.
Because this is a Linux kernel issue, remediation timing will vary sharply by vendor. Some distributions will backport the fix quickly, while others may mark affected packages with the usual “patched upstream, awaiting vendor integration” status. For operators, the practical answer is simple: do not wait for a generic kernel update notice; verify whether your exact build has absorbed the mac80211 fix.
That likely explains why the published remediation centers on resolving the correct BSS sdata before reading link state. It is a contained change, easy to reason about, and aligned with the subsystem’s ownership model. Minimal but correct is usually the right answer in kernel security backports.
This is one reason kernel CVEs are hard to manage operationally. The vulnerability identifier is shared, but the fix state is specific to each vendor’s kernel tree, build number, and backport policy. A host can be “fixed” in one enterprise repository and vulnerable in another even if they share the same underlying kernel version string.
It also gives vendors a concrete scenario to encode into regression tests. Reproducing a CSA on an AP with VLAN-backed station handling is now a valuable test case, not just a theoretical edge condition.
The result is a subtle but important lesson: in kernel networking, the edge case is the product. A fix that appears tiny on paper may be defending a critical production path that only shows up under specific conditions.
It is also worth watching for follow-up kernel notes that tighten related link-state assumptions elsewhere in the wireless stack. Bugs like this often lead to adjacent hardening work, especially when maintainers see that one pointer-resolution mistake can remain dormant until a CSA or bandwidth-change event. That means the story is not only about one CVE; it is about the maturity of the whole wireless object model.
That is why this bug matters beyond the one CVE entry. It shows how a single mistaken assumption about interface ancestry can ripple into a visible service failure. And in the Linux kernel, that is often enough to turn an ordinary logic bug into a security event.
CVE-2026-31394 is not the kind of flaw that rewrites the threat landscape, but it does sharpen a familiar truth: the most dangerous kernel issues are often the ones that sit quietly in high-trust plumbing until a normal administrative action wakes them up. For wireless operators, that should prompt a sober review of AP VLAN usage, channel-switch behavior, and patch status. For kernel maintainers, it is another reminder that correct parent resolution is not a detail; it is a security boundary.
Source: MSRC Security Update Guide - Microsoft Security Response Center
The vulnerability description points to a NULL pointer dereference during ieee80211_chan_bw_change(), with the failure surfacing in __ieee80211_sta_cap_rx_bw() when the code tries to read the channel band from an uninitialized reserved channel context. In practical terms, the bug is not about unauthorized code execution or data theft; it is about availability, stability, and trust in the wireless stack. That makes it less glamorous than remote compromise, but still highly relevant to anyone operating APs, mesh nodes, or wireless virtualization setups at scale.
 Overview
Overview
The Linux mac80211 subsystem is the software framework that many Wi‑Fi drivers rely on for 802.11 logic, including station management, AP behavior, bandwidth negotiation, and channel context handling. Its design lets drivers focus on hardware specifics while mac80211 coordinates higher-level wireless behavior, which is why bugs here can affect a broad range of devices without living in a single vendor driver. The subsystem documentation shows how deeply mac80211 is involved in AP mode, station state transitions, and channel-aware operations, including the exact kinds of callbacks and state handling that make bandwidth changes nontrivial.AP VLAN support is one of those features that looks simple from the outside and becomes intricate the moment you trace the code paths. The kernel documentation notes that multiple transmission keys and per-station handling can be involved when VLANs are configured for an access point, which reflects how the stack maintains separate logical views for traffic and policy. In this bug, that abstraction boundary matters: a station on an AP_VLAN interface points at VLAN-specific sdata, but the bandwidth-change code expected AP-side reservation state. That mismatch is what created the crash condition.
The vulnerability has already been tracked by multiple security databases and distro ecosystems, which is typical once a kernel crash lands in a common subsystem. Public writeups consistently describe the same failure mode:
sta->sdata on AP_VLAN interfaces resolves to VLAN data whose link never participates in chanctx reservations, leaving link->reserved.oper zeroed and chan unset. The fix is equally consistent across reports: resolve VLAN sdata to its parent AP sdata via get_bss_sdata() before the code dereferences link data.Why this bug matters
At first glance, a NULL pointer dereference sounds routine, almost mundane. In a kernel wireless path, though, even a “simple crash” can mean a dropped access point, a transient outage across connected clients, or a reboot if the system is configured to panic on kernel faults. That is why stability bugs in networking code often receive security identifiers: they can be weaponized into denial of service, and they impact infrastructure that tends to sit in production for long periods.This specific issue is tied to channel switch announcements and bandwidth transitions, which are not everyday operations for a home laptop but are common enough in managed wireless deployments. When those transitions collide with AP VLAN station handling, the stack can walk the wrong data structure and fault. In other words, the bug is narrow in trigger conditions but broad in consequence once the wrong conditions are met.
The role of AP_VLAN interfaces
AP VLANs are used when an access point needs per-station or per-service separation without collapsing everything into one monolithic BSS view. They are especially relevant in environments that rely on 4addr WDS clients or advanced segmentation patterns. The problem here is that the VLAN layer has its own interface state, but the bandwidth-change path expected the parent AP’s reservation context.That distinction is subtle, and it is exactly why bugs like this can survive until a CSA or bandwidth event. Most of the time, the code paths line up cleanly. Under the right interface topology, though, the pointer that “should” represent an AP station instead resolves to VLAN-associated state that never took part in chanctx reservation at all.
What Actually Failed
The core failure is a straightforward pointer lifetime and ownership mismatch. The function ieee80211_chan_bw_change() iterates through stations and then accesseslink->reserved.oper through sta->sdata->link[link_id]. For ordinary AP-side stations, that path is valid. For AP_VLAN stations, however, sta->sdata points to the VLAN sdata, and that structure never had a corresponding channel reservation, so its reserved operation context remains zero-initialized.Once the code reaches __ieee80211_sta_cap_rx_bw(), it tries to read
chandef->chan->band, but chan is NULL. That is the classic crash signature: an object was assumed to be fully initialized because the code followed the wrong interface branch. The bug is therefore not about a corrupted buffer or a race in the traditional sense; it is about a valid object graph being interpreted with the wrong parent relationship.The fix in plain English
The remediation is conceptually simple: when the station belongs to an AP_VLAN interface, the code should resolve the parent BSS data first, then read the link data from the AP-side structure. Security trackers summarizing the patch note exactly that approach: use get_bss_sdata() before accessing the channel context-dependent fields. The reports also mention a secondary cleanup wheresta->sdata is adjusted in ARRAY_SIZE handling even though it does not materially change the bug’s behavior, which suggests the patch was made a bit more robust than the minimal crash fix.That kind of fix is common in kernel networking code. The kernel often has multiple logical views of the same object, and the safest repair is to ensure the helper function walks back to the canonical owner before dereferencing deep state. It is a reminder that in mac80211, the right pointer in the right context matters more than the nominal object type.
Why a NULL dereference is still security-relevant
A NULL dereference does not always mean an attacker gets code execution. But in kernels, a reliable crash can still be a security issue because it can terminate critical services, force reboots, or induce a persistent denial-of-service state. The CVSS ratings that have been published for this issue reflect that logic, scoring the flaw as a medium-severity availability problem rather than a confidentiality or integrity issue. That is exactly the sort of bug that can still be operationally painful even when it is not dramatic.How Channel Switches Interact With the Bug
Channel switch announcements, or CSAs, are routine in managed Wi‑Fi environments where APs need to move clients to a different channel without tearing down the network. They are part of the machinery that lets wireless networks adapt to congestion, regulatory events, or hardware constraints. In mac80211, the bandwidth-change logic is part of this orchestration, which makes it a highly sensitive path for any station-type confusion.The bug appears during that orchestration because bandwidth capability checks are being performed while the system is still reconciling station state and channel state. If the code looks at the wrong sdata instance, it can conclude that a channel reservation exists when it does not, or simply follow a NULL pointer and die. The failure mode is therefore tied to the intersection of topology, configuration, and runtime channel management.
Why CSAs are a favorite crash trigger
CSAs are disruptive enough that drivers and AP stacks have to coordinate them carefully, yet they are common enough that edge cases eventually surface in production. Any code path that combines station iteration, per-link state, and context reservation is susceptible to mismatched assumptions. In this case, the bug did not require a malformed packet; it required the correct operational event in the wrong interface topology.That matters because it lowers the bar from exotic exploit craft to ordinary administrative activity. A crash that only happens during channel migration might seem niche, but in enterprise wireless, channel migration is not rare. It is part of the normal life cycle of a well-managed WLAN.
Consumer versus enterprise impact
For consumer routers, the issue is probably obscure unless the firmware exposes AP VLAN or sophisticated multi-SSID behavior under the hood. Many home users will never meet the triggering combination. For enterprise deployments, however, AP VLANs and 4addr clients are much more plausible, especially in environments that segment guests, IoT devices, and corporate devices across logical interfaces.That difference is important because it changes how operators should think about risk. In the consumer case, the problem is mostly about futureproofing and receiving vendor fixes. In the enterprise case, it is about whether a wireless outage could be triggered during routine channel management, site surveys, or radio optimization windows.
The Kernel Context Behind the Bug
mac80211’s internal design deliberately separates low-level driver capability from higher-level wireless policy. The documentation shows how the subsystem manages per-station state, AP behavior, rate-control updates, and channel context callbacks. That flexibility is powerful, but it also means that one station can exist in multiple logical “forms” depending on which callback is examining it.The AP mode documentation also highlights how complex the subsystem becomes once power-save, station transitions, and interface-specific state are layered on top of each other. That is the environment in which
chanctx reservations live. Bugs like CVE-2026-31394 are not random accidents; they are the predictable result of a system where several layers of abstraction have to agree on what a station “really” is.The importance of helper functions
The kernel’s use of helpers like get_bss_sdata() is not just stylistic. It encodes a rule: when code is operating on station or channel logic, it should ask the subsystem for the authoritative parent object rather than assuming the immediate interface pointer is sufficient. That is especially true when VLAN or virtual interface layers are present.This issue shows why those helpers matter. The wrong direct pointer was not merely inconvenient; it was semantically wrong for the reservation data being accessed. The helper restored the correct ownership chain and eliminated the mismatch that led to the NULL dereference.
What the docs tell us about the design
The documentation emphasizes that mac80211 handles a broad range of wireless tasks, from station callbacks to AP lifecycle events. It also notes that AP and VLAN configurations can involve multiple keys and station-specific behaviors, which means the stack already expects a complex object graph. That complexity is not a bug by itself; it is the cost of supporting real-world wireless topologies.But complexity also creates places where assumptions become stale. If a function assumes a station belongs directly to the AP context and then encounters a VLAN indirection, it can read state that was never meant for that branch. In kernel code, that kind of mistaken assumption is often all it takes to produce a crash.
Exploitability and Threat Model
This issue is generally described as a crash or NULL pointer dereference rather than a remotely exploitable memory corruption flaw. That distinction matters. The likely impact is denial of service, not arbitrary code execution, and the published severity ratings reflect that narrower scope. Still, availability attacks can be business-critical when they affect access infrastructure.The main threat model is an attacker who can influence the conditions under which bandwidth changes or channel switches occur, or an administrator who unknowingly triggers them in a vulnerable configuration. In other words, the bug may be more about operational exposure than about an internet-scale exploit. That does not make it trivial; it makes it situational, which is often how infrastructure bugs behave.
Practical attack surface
The attack surface is not a simple socket exposed to the internet. Instead, it lives inside wireless management and interface topology. That means the effective risk depends on whether the target system uses AP_VLAN features, whether it performs CSA or similar bandwidth transitions, and whether the vulnerable kernel build includes the fix.For defenders, that means a security scan alone is not enough. You need to understand the wireless role of the host, the configuration of virtual interfaces, and whether the radio management stack might naturally encounter the edge case during day-to-day use.
Why this is not “just a bug”
Kernel crash issues are sometimes dismissed as noisy but harmless. That view ignores how much modern networking depends on long-lived kernel services that can be harder to restart cleanly than user-space daemons. A crash in the wireless stack can knock out remote access, management planes, and field devices that depend on stable radio links.That is why even a medium-severity issue can matter disproportionately. In wireless infrastructure, downtime often spreads beyond the device that actually faulted. A single AP reboot can cause client reauthentication churn, roaming instability, and cascading service complaints.
Patch Status and Ecosystem Response
The vulnerability has already been incorporated into public security tracking pipelines, and distro ecosystems appear to be classifying or patching it according to their own maintenance cadence. Multiple trackers reference fixed upstream commits, which suggests the kernel fix has been circulated into stable branches and downstream packaging systems. That is a good sign for remediation, but it does not mean every deployed kernel is clean yet.Because this is a Linux kernel issue, remediation timing will vary sharply by vendor. Some distributions will backport the fix quickly, while others may mark affected packages with the usual “patched upstream, awaiting vendor integration” status. For operators, the practical answer is simple: do not wait for a generic kernel update notice; verify whether your exact build has absorbed the mac80211 fix.
What downstreams typically do
Downstream maintainers usually backport the smallest safe patch that addresses the fault without dragging in unrelated wireless changes. That is especially true in stable branches, where maintaining ABI and minimizing regressions are important. When a bug lives in mac80211, backporters tend to prefer a surgical fix over a broader refactor.That likely explains why the published remediation centers on resolving the correct BSS sdata before reading link state. It is a contained change, easy to reason about, and aligned with the subsystem’s ownership model. Minimal but correct is usually the right answer in kernel security backports.
Why distro status can lag
A downstream vendor may already know about the issue while still shipping a vulnerable package in some channels. Security advisories often lag the upstream fix by days or weeks, especially when testing, staging, and certification are required. That lag is normal, but it creates a visibility gap for administrators who assume a CVE page automatically means a patched package.This is one reason kernel CVEs are hard to manage operationally. The vulnerability identifier is shared, but the fix state is specific to each vendor’s kernel tree, build number, and backport policy. A host can be “fixed” in one enterprise repository and vulnerable in another even if they share the same underlying kernel version string.
Strengths and Opportunities
The good news is that this issue looks highly amenable to patching, and the broader mac80211 architecture gives maintainers a clear path to correct the pointer resolution without redesigning the subsystem. It also exposes a class of edge-case bugs that can be audited more broadly across the wireless stack.- The fix is narrow and comprehensible, which reduces the risk of regression.
- The failure mode is well-defined, making validation and testing easier.
- The subsystem already has helper functions that point to the correct parent object.
- Downstream backports should be straightforward for stable branches.
- The bug highlights a reusable audit pattern for VLAN and AP-context mismatches.
- Enterprise operators can test for exposure by reviewing AP VLAN and CSA usage.
- The issue reinforces the value of subsystem ownership rules in kernel code.
A chance to harden more than one path
This is the sort of bug that can become an audit catalyst. Once maintainers trace how AP_VLAN stations were misresolved in one path, they can look for similar assumptions elsewhere in mac80211 and cfg80211. That is a net positive for the ecosystem, because one crash report can reveal a family resemblance of bugs.It also gives vendors a concrete scenario to encode into regression tests. Reproducing a CSA on an AP with VLAN-backed station handling is now a valuable test case, not just a theoretical edge condition.
Risks and Concerns
The largest concern is not that this particular flaw is devastating, but that it sits in an area where small logic mistakes can have outsized effects. Wireless stacks are already sensitive to timing, topology, and interface state, and bugs in that space can be triggered by ordinary maintenance activities.- Kernel crashes in wireless code can take down access points and interrupt service.
- Enterprise environments are more exposed because AP VLANs and advanced WLAN features are common.
- Backport divergence can leave some builds vulnerable even after upstream fixes land.
- A stable-looking CVE page can hide vendor-specific patch gaps.
- Regression testing may miss the edge case if AP VLAN and CSA are not both exercised.
- Operators may underestimate availability risk because the flaw is not remote code execution.
- Wireless outage impact can cascade into roaming failures and management-plane disruptions.
The operational blind spot
Many organizations test Wi‑Fi for throughput, coverage, and authentication reliability, but not for the weird state transitions that only happen during channel moves or interface reconfiguration. That is the blind spot this CVE exposes. If a patch is rolled out without validating AP VLAN behavior during channel changes, a regression could survive all the usual smoke tests.The result is a subtle but important lesson: in kernel networking, the edge case is the product. A fix that appears tiny on paper may be defending a critical production path that only shows up under specific conditions.
What to Watch Next
The first thing to watch is whether your vendor has explicitly backported the mac80211 fix into your kernel stream. The second is whether your wireless infrastructure uses AP VLANs, WDS-like 4addr behavior, or automated channel management that could exercise the faulty path. If both are true, the issue deserves priority attention.It is also worth watching for follow-up kernel notes that tighten related link-state assumptions elsewhere in the wireless stack. Bugs like this often lead to adjacent hardening work, especially when maintainers see that one pointer-resolution mistake can remain dormant until a CSA or bandwidth-change event. That means the story is not only about one CVE; it is about the maturity of the whole wireless object model.
- Confirm your exact kernel build and backport level.
- Check whether AP VLAN or 4addr features are enabled.
- Review whether CSAs or automated channel changes are used in production.
- Test wireless failover and roaming behavior after updates.
- Monitor for subsequent mac80211 hardening patches.
The bigger lesson for Linux wireless
The deeper lesson is that mac80211 is both a strength and a source of complexity. It gives Linux a rich, portable wireless framework, but that same abstraction layer means object ownership has to be right every time. When the AP and VLAN views diverge, kernel code needs to be explicit about which layer it is using.That is why this bug matters beyond the one CVE entry. It shows how a single mistaken assumption about interface ancestry can ripple into a visible service failure. And in the Linux kernel, that is often enough to turn an ordinary logic bug into a security event.
CVE-2026-31394 is not the kind of flaw that rewrites the threat landscape, but it does sharpen a familiar truth: the most dangerous kernel issues are often the ones that sit quietly in high-trust plumbing until a normal administrative action wakes them up. For wireless operators, that should prompt a sober review of AP VLAN usage, channel-switch behavior, and patch status. For kernel maintainers, it is another reminder that correct parent resolution is not a detail; it is a security boundary.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: