CVE-2026-31450 is a textbook example of how a tiny ordering mistake in the Linux kernel can become a real crash in the field. The bug lives in ext4’s journaling glue, where
The Linux kernel is full of places where state has to become visible in the right order, not just the right final form. That is especially true in ext4, where the filesystem must coordinate inode metadata, journaling state, and writeback behavior under heavy concurrency. In this case, the issue is not a malformed input or a logic error in a user-facing feature. It is a publication bug: a pointer became observable before its associated state was safe for use.
The published description makes the sequence plain.
The crash path matters because it lands in the fast commit flush code, not some obscure debug path. The flush logic can call into
There is also a broader lesson here about journaling filesystems in 2026. The biggest bugs are often no longer the old-school buffer overruns. They are sequencing defects caused by concurrency, publication, and memory ordering. The ext4 patch described in the advisory uses
The filesystem’s durability model relies on a careful relationship between the VFS layer, the journal, and writeback. When the kernel attaches journaling metadata to an inode, it has to do so in an order that prevents other CPUs from observing a half-built state. If that ordering slips, the consequences may not appear immediately. They may surface later, under stress, on a different CPU, in a completely different part of the code path. That is what makes these bugs so expensive to diagnose and so frustrating to reproduce.
That is why the bug description emphasizes publication timing rather than data corruption. The mistake was not that ext4 created the wrong object. It was that ext4 made the object visible too soon. In concurrent kernel code, visibility is everything. Once a pointer is published, other CPUs may assume the object is fair game, even if the publishing thread still has more work to do.
The key risk is that fast commit logic tends to run under pressure, often alongside write-heavy workloads, sync operations, and metadata churn. Those are exactly the conditions under which a concurrency flaw becomes more likely to bite. A race that appears rare in testing can become much more visible on real machines, especially on systems that mix high write rates with periodic fsync or fdatasync activity.
That matters for administrators because it suggests the fix is not speculative. It has already moved through the upstream review and stable pipeline, which means downstream vendors can anchor their patches on a known-good kernel change. In the Linux world, that is often the difference between a vague advisory and a concrete remediation plan.
What makes the bug tricky is that the object is not obviously malformed. The pointer is there, and the structure exists. The problem is that one of the embedded relationships the structure depends on has not been safely established yet. That is a much subtler failure mode than a null dereference, and in some ways it is more dangerous because it can survive static inspection and only appear under real concurrency.
Why
The published description specifically calls out that a reader could see a non-NULL
This is a good example of why kernel developers care so much about object lifetime and initialization order. The object may be allocated, but allocation is not initialization. The object may be named in a structure, but naming it is not publication. The object may pass a sanity check, but sanity checks do not replace memory ordering. Those distinctions sound academic until they become a production outage.
In other words, the system is trying to be careful, and the bug punishes that caution. That makes it more than a narrow programmer error. It becomes an operational reliability risk, because the code path can be exercised by routine file sync behavior in workloads that rely on ext4’s journaling guarantees.
A crash in this region is especially disruptive because it sits on the boundary between application I/O and filesystem metadata handling. Applications may see a failed sync, a hung flush, or a sudden kernel panic depending on the surrounding conditions and platform policy. That is not just a bug in one function; it is a fault in the trust chain between the filesystem and the rest of the kernel.
That is the core of the patch’s correctness story. It does not add a global lock, does not slow the subsystem down with heavy serialization, and does not change the data model. It simply ensures the publication point matches the object’s true readiness. In a codebase as performance-sensitive as the kernel, that is the right kind of repair.
For non-kernel readers, the practical meaning is simple: the kernel is teaching itself not to lie about readiness. Once the pointer is visible, the object must already be safe to use. The fence and one-time access macros are the machinery that make that guarantee believable on real hardware, not just in source code.
This is especially true in filesystem code, where many operations already contend on shared data structures. A fix that preserves the existing concurrency model while tightening visibility is almost always preferable to a patch that globally narrows throughput. The CVE’s patch text suggests exactly that philosophy.
That is especially true when the bug lives in a widely used filesystem. ext4 underpins countless Linux servers, virtual machines, and appliance images. If a race like this can be hit through ordinary sync or writeback activity, then the blast radius is wider than the line count of the patch suggests. Availability is a security property, and this CVE hits it directly.
There is also a lifecycle issue. Systems running older vendor kernels may have the bug for some time even after the upstream fix is known, because backporting depends on distribution cadence, QA cycles, and product support policies. A published CVE only helps if the actual deployed kernel contains the fix. That is a recurring operational lesson, and it applies here as well.
The consumer risk is not primarily about exploitation by a remote attacker. It is about reliability on systems that are expected to just keep working. Linux users often value ext4 precisely because it is stable and predictable, so any kernel race that undermines that reputation deserves attention.
That is not a sign that Linux is failing. It is a sign that the codebase is mature enough that the remaining problems are subtle. Mature systems tend to be attacked by the edges of their state machines, not by the obvious center. This CVE is one of those edge cases.
The fact that the fix was published alongside a crash report also suggests the maintainers had a concrete reproduction scenario, not just a theoretical race hypothesis. Kernel teams tend to move more decisively when they can point to an observable fault path. That makes the bug easier for downstream vendors to assess and less likely to be dismissed as a harmless corner case.
That said, easy to backport does not mean already fixed everywhere. Kernel ecosystems are fragmented by design. OEMs, cloud providers, and distro vendors all move on different schedules, which is why operators should always confirm the actual runtime kernel rather than assume that a CVE announcement equals protection.
The upside is visibility. The downside is that organizations can mistakenly believe that a published advisory means their deployed kernel is protected, when in reality the fix may still be pending in a vendor branch or a custom build. For this reason, the safest interpretation of a CVE is always: check the exact kernel build you run.
That distinction is important because severity is not only about attacker sophistication. It is also about operational dependence. If your production workload depends on ext4 to keep a database, VM image, or transaction log coherent, then a crash in its journal handoff path is very much a security and reliability issue.
They are also hard to reason about during code review. A reviewer can see that the code sets a pointer and initializes a structure, but the danger lies in the ordering of those two steps relative to concurrent readers. That is why memory barriers and
That is what makes ext4’s fast commit path so interesting here. It is a feature designed to improve responsiveness, but it also inherits the burden of proving that every pointer it touches is fully initialized. The more aggressive the optimization, the stricter the safety discipline has to be.
It is also worth watching whether this CVE prompts additional cleanup around ext4’s fast commit and journal attachment paths. Bugs like this often serve as a reminder that a subsystem’s state transitions need regular hardening, especially as features evolve and concurrency patterns become more complex. The best-case outcome is not just a patch, but a sharper mental model across the maintainer community for how and when inode-related state should be exposed.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
ext4_inode_attach_jinode() could expose a partially initialized jinode to concurrent readers before the embedded jbd2_inode had been fully set up. In the fast commit flush path, that race could feed an unready pointer into jbd2_wait_inode_data(), which then dereferences i_vfs_inode->i_mapping and can fault hard, exactly as the reported crash shows. The CVE was published on April 22, 2026, and the upstream fix is already in the stable kernel record, which makes this one of those small-but-serious filesystem bugs that operators ignore at their own risk.
 Overview
Overview
The Linux kernel is full of places where state has to become visible in the right order, not just the right final form. That is especially true in ext4, where the filesystem must coordinate inode metadata, journaling state, and writeback behavior under heavy concurrency. In this case, the issue is not a malformed input or a logic error in a user-facing feature. It is a publication bug: a pointer became observable before its associated state was safe for use.The published description makes the sequence plain.
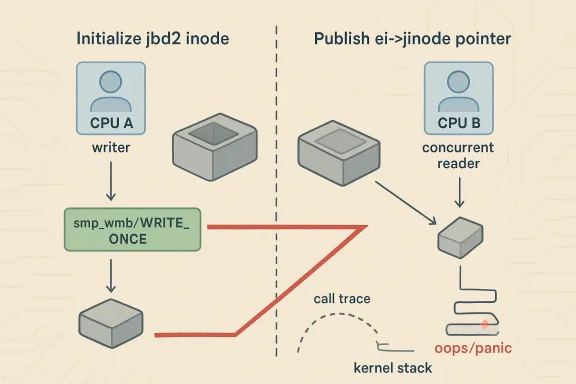
ext4_inode_attach_jinode() assigned ei->jinode too early, before jbd2_journal_init_jbd_inode() had finished initializing the journal inode wrapper. That meant a racing reader could see a non-NULL pointer and assume the object was valid, even though i_vfs_inode inside it had not yet been set. In kernel code, “non-NULL” is not the same thing as “ready”, and this CVE is a reminder that those two ideas must be kept separate with great care.The crash path matters because it lands in the fast commit flush code, not some obscure debug path. The flush logic can call into
jbd2_wait_inode_data(), which eventually looks at the VFS inode mapping and walks memory that should only be touched once the object is fully initialized. The reported oops in the CVE entry is consistent with exactly that sort of race: a reader reached xas_find_marked() through the filemap wait path after being handed a jinode too early. That is not just ugly; it is an availability problem that can take down a workload in the middle of normal filesystem activity.There is also a broader lesson here about journaling filesystems in 2026. The biggest bugs are often no longer the old-school buffer overruns. They are sequencing defects caused by concurrency, publication, and memory ordering. The ext4 patch described in the advisory uses
smp_wmb() and WRITE_ONCE() to publish ei->jinode only after initialization, while readers use READ_ONCE() to fetch it. That is the kernel’s way of saying: the object can exist, but nobody gets to trust it until the writer says it is fully formed.Background
Why ext4 still matters
ext4 remains one of the most widely deployed Linux filesystems because it balances maturity, performance, and operational familiarity. Enterprises like it because it is boring in the best possible way: well understood, battle-tested, and supported across nearly every mainstream distribution. That popularity is exactly why even narrow races deserve attention. A bug in ext4 is not a niche concern; it can affect cloud images, VM templates, servers, appliances, and embedded systems alike.The filesystem’s durability model relies on a careful relationship between the VFS layer, the journal, and writeback. When the kernel attaches journaling metadata to an inode, it has to do so in an order that prevents other CPUs from observing a half-built state. If that ordering slips, the consequences may not appear immediately. They may surface later, under stress, on a different CPU, in a completely different part of the code path. That is what makes these bugs so expensive to diagnose and so frustrating to reproduce.
What the journal inode does
The journal inode is not just a bookkeeping detail. It is part of the machinery ext4 uses to coordinate data and metadata durability, especially in features like fast commit. The kernel expects the journal-side wrapper and the VFS inode to be in sync before the wrapper is exposed to another subsystem. If that contract is broken, a consumer can follow the pointer into a structure that looks valid from the outside but still lacks the internal state needed for safe use.That is why the bug description emphasizes publication timing rather than data corruption. The mistake was not that ext4 created the wrong object. It was that ext4 made the object visible too soon. In concurrent kernel code, visibility is everything. Once a pointer is published, other CPUs may assume the object is fair game, even if the publishing thread still has more work to do.
Why fast commit makes this sharper
Fast commit exists to improve ext4 performance by reducing the amount of metadata that must be flushed in some scenarios. That makes the feature attractive, but it also narrows the margin for sloppy sequencing. If a fast-path flush routine pulls on ajinode before the inode wrapper is fully initialized, the crash can happen in the very mechanism meant to make the filesystem feel faster and more efficient. That is a classic trade-off in kernel engineering: the more performance you squeeze from a path, the more ruthless you have to be about ordering guarantees.The key risk is that fast commit logic tends to run under pressure, often alongside write-heavy workloads, sync operations, and metadata churn. Those are exactly the conditions under which a concurrency flaw becomes more likely to bite. A race that appears rare in testing can become much more visible on real machines, especially on systems that mix high write rates with periodic fsync or fdatasync activity.
The upstream record
The public record attached to the CVE is unusually helpful because it includes both the symptom and the fix strategy. It also links to several stable kernel commits, which is a good sign that the issue was treated as a genuine production problem rather than as a theoretical cleanup item. Stable backporting tends to follow bugs that can cause crashes or serious reliability issues, and this one fits that profile cleanly.That matters for administrators because it suggests the fix is not speculative. It has already moved through the upstream review and stable pipeline, which means downstream vendors can anchor their patches on a known-good kernel change. In the Linux world, that is often the difference between a vague advisory and a concrete remediation plan.
What Actually Broke
The race window
At the heart of CVE-2026-31450 is a simple but dangerous race window.ext4_inode_attach_jinode() used to assign ei->jinode before the journal inode had been fully initialized by jbd2_journal_init_jbd_inode(). A concurrent reader could therefore observe a pointer that looked legitimate even though the object behind it was still mid-construction. In kernel space, that kind of publish-before-ready bug is often enough to trigger a crash.What makes the bug tricky is that the object is not obviously malformed. The pointer is there, and the structure exists. The problem is that one of the embedded relationships the structure depends on has not been safely established yet. That is a much subtler failure mode than a null dereference, and in some ways it is more dangerous because it can survive static inspection and only appear under real concurrency.
Why i_vfs_inode matters
The published description specifically calls out that a reader could see a non-NULL jinode while i_vfs_inode was still unset. That is the key technical detail. Once the fast commit flush path passes that jinode to jbd2_wait_inode_data(), the downstream code expects to be able to access the VFS inode and its mapping. Instead, it can end up dereferencing a pointer that has not been safely established, which is how the crash reaches xas_find_marked() and the filemap code.This is a good example of why kernel developers care so much about object lifetime and initialization order. The object may be allocated, but allocation is not initialization. The object may be named in a structure, but naming it is not publication. The object may pass a sanity check, but sanity checks do not replace memory ordering. Those distinctions sound academic until they become a production outage.
The fast commit flush path
The fast commit flush path is the place where this bug turns from a theoretical race into a practical fault. It is already in the business of waiting on inode data and metadata state, so it naturally assumes the pointers it sees are sound. When that assumption fails, the code can crash while trying to synchronize data that the filesystem believes is safe to flush. That is particularly unpleasant because the failure occurs during a correctness-preserving operation, not during some exotic edge-case API call.In other words, the system is trying to be careful, and the bug punishes that caution. That makes it more than a narrow programmer error. It becomes an operational reliability risk, because the code path can be exercised by routine file sync behavior in workloads that rely on ext4’s journaling guarantees.
The crash signature
The reported oops is important because it demonstrates that the issue was not hypothetical. The call trace runs throughfilemap_get_folios_tag(), __filemap_fdatawait_range(), and filemap_fdatawait_range_keep_errors() before landing in ext4_fc_commit() and then ext4_sync_file(). That stack is exactly what you would expect if a flush or fsync path hit a poisoned inode state while trying to wait on outstanding data.A crash in this region is especially disruptive because it sits on the boundary between application I/O and filesystem metadata handling. Applications may see a failed sync, a hung flush, or a sudden kernel panic depending on the surrounding conditions and platform policy. That is not just a bug in one function; it is a fault in the trust chain between the filesystem and the rest of the kernel.
The Fix Strategy
Initialize first, publish later
The fix is elegant in the way good kernel fixes often are. Instead of exposingei->jinode before its embedded journal state is ready, ext4 now initializes the jbd2_inode first and only then publishes the pointer. That reorders the steps so that any concurrent reader sees either no pointer at all or a fully initialized one. There is no middle state in which another CPU can get a half-baked object and mistakenly treat it as valid.That is the core of the patch’s correctness story. It does not add a global lock, does not slow the subsystem down with heavy serialization, and does not change the data model. It simply ensures the publication point matches the object’s true readiness. In a codebase as performance-sensitive as the kernel, that is the right kind of repair.
Memory ordering matters
The description says the fix uses smp_wmb() and WRITE_ONCE() to publishei->jinode after initialization, while readers use READ_ONCE() to fetch it. That combination is important because this is not just a logic-order issue; it is a cross-CPU visibility issue. The writer needs to ensure earlier initialization stores become visible before the pointer publication becomes visible, and the reader needs to avoid compiler or CPU-level assumptions that could reorder the access.For non-kernel readers, the practical meaning is simple: the kernel is teaching itself not to lie about readiness. Once the pointer is visible, the object must already be safe to use. The fence and one-time access macros are the machinery that make that guarantee believable on real hardware, not just in source code.
Why not a heavier lock?
It is tempting to ask why the kernel did not just wrap the whole operation in a larger lock and be done with it. The answer is that heavy locking would probably solve this bug, but at a cost. ext4’s hot paths are carefully tuned, and adding broad serialization around inode attachment would risk dragging down performance for a problem that can be solved with correct ordering instead. That is why the kernel often prefers precise publication discipline over blunt synchronization.This is especially true in filesystem code, where many operations already contend on shared data structures. A fix that preserves the existing concurrency model while tightening visibility is almost always preferable to a patch that globally narrows throughput. The CVE’s patch text suggests exactly that philosophy.
Numbered summary of the repair
- Initialize the
jbd2_inodefully. - Ensure the VFS inode relationship is established.
- Publish
ei->jinodeonly after initialization completes. - Use memory-ordering primitives to preserve that sequencing across CPUs.
- Let readers fetch the pointer with
READ_ONCE()so they either see nothing or a valid object.
Why This Becomes a Security Issue
Crash bugs are still security bugs
CVE-2026-31450 is not a classic code-execution vulnerability, but that does not make it trivial. A kernel crash in a filesystem fast path can still be a serious security issue because it can produce denial of service, data loss, and service interruption. In infrastructure environments, those outcomes are often far more expensive than a narrow local crash report makes them seem.That is especially true when the bug lives in a widely used filesystem. ext4 underpins countless Linux servers, virtual machines, and appliance images. If a race like this can be hit through ordinary sync or writeback activity, then the blast radius is wider than the line count of the patch suggests. Availability is a security property, and this CVE hits it directly.
The enterprise angle
For enterprise operators, the immediate worry is not whether the crash is remotely exploitable. It is whether a busy filesystem can panic under load, force a reboot, or take a critical service offline. Those effects can cascade into lost transactions, failed batch jobs, and recovery procedures that consume far more time than a routine patch window. That is why kernel CVEs like this one belong in standard remediation workflows.There is also a lifecycle issue. Systems running older vendor kernels may have the bug for some time even after the upstream fix is known, because backporting depends on distribution cadence, QA cycles, and product support policies. A published CVE only helps if the actual deployed kernel contains the fix. That is a recurring operational lesson, and it applies here as well.
The consumer angle
Consumers are less likely to hit this bug in everyday desktop use, but that does not make it irrelevant. Home servers, developer workstations, NAS devices, and lab machines often use ext4 heavily and may exercise sync behavior under workloads that feel ordinary to their owners. A crash in one of those systems can still cause downtime, data corruption, or unpleasant recovery work.The consumer risk is not primarily about exploitation by a remote attacker. It is about reliability on systems that are expected to just keep working. Linux users often value ext4 precisely because it is stable and predictable, so any kernel race that undermines that reputation deserves attention.
The bigger pattern
This CVE fits a broader trend in kernel security: more vulnerabilities are rooted in concurrency, sequencing, and object lifetime than in obviously malicious input processing. That makes them harder to spot and easier to underestimate. It also means the kernel community’s most valuable fixes increasingly look like ordering corrections, memory barriers, and lifetime cleanup rather than flashy rewrites.That is not a sign that Linux is failing. It is a sign that the codebase is mature enough that the remaining problems are subtle. Mature systems tend to be attacked by the edges of their state machines, not by the obvious center. This CVE is one of those edge cases.
Upstream and Stable-Branch Implications
What the stable links suggest
The CVE entry points to multiple stable kernel commits, which is usually a strong signal that the maintainers saw the bug as suitable for broad backporting. That matters because ext4 is everywhere, and a fix that remains upstream-only would not protect the majority of deployed systems. Stable inclusion is the bridge from “known bug” to “available remediation.”The fact that the fix was published alongside a crash report also suggests the maintainers had a concrete reproduction scenario, not just a theoretical race hypothesis. Kernel teams tend to move more decisively when they can point to an observable fault path. That makes the bug easier for downstream vendors to assess and less likely to be dismissed as a harmless corner case.
Why this is easy to backport
This kind of change is usually a good candidate for backporting because it is narrow. It does not alter on-disk formats, does not change ext4’s user-visible semantics, and does not require a new feature flag or migration logic. Instead, it corrects an internal sequencing bug. Those are the patches distribution maintainers like to ship because they are easier to validate and less likely to break existing workloads.That said, easy to backport does not mean already fixed everywhere. Kernel ecosystems are fragmented by design. OEMs, cloud providers, and distro vendors all move on different schedules, which is why operators should always confirm the actual runtime kernel rather than assume that a CVE announcement equals protection.
The advisory ecosystem
The fact that Microsoft’s vulnerability guide surfaced the CVE underscores how Linux kernel issues now travel through a broad advisory ecosystem. Enterprises increasingly rely on a mix of upstream kernel reports, vendor security trackers, and central vulnerability catalogs. That fragmentation is inconvenient, but it also helps surface issues to teams that manage heterogeneous fleets.The upside is visibility. The downside is that organizations can mistakenly believe that a published advisory means their deployed kernel is protected, when in reality the fix may still be pending in a vendor branch or a custom build. For this reason, the safest interpretation of a CVE is always: check the exact kernel build you run.
Comparing the Risk to Other Kernel Bugs
Not the flashiest, but still serious
This is not a remote-code-execution headline, and it will not dominate security conference talks. But filesystem crashes matter, especially in infrastructure, virtualization, and storage-heavy environments. A bug that can panic the kernel in a common sync path can be just as disruptive as a more dramatic memory-safety flaw if it lands at the wrong time.That distinction is important because severity is not only about attacker sophistication. It is also about operational dependence. If your production workload depends on ext4 to keep a database, VM image, or transaction log coherent, then a crash in its journal handoff path is very much a security and reliability issue.
Why object publication bugs are hard
Publication bugs are tricky because they live at the boundary between data structure correctness and concurrency correctness. A structure can be internally valid in one thread and externally unsafe in another. That means traditional testing may miss them unless it deliberately stresses races, reorderings, and synchronization windows.They are also hard to reason about during code review. A reviewer can see that the code sets a pointer and initializes a structure, but the danger lies in the ordering of those two steps relative to concurrent readers. That is why memory barriers and
READ_ONCE()/WRITE_ONCE() usage remain so central to kernel engineering.Why fast paths attract these bugs
Fast paths are optimized because they are used a lot, and they are used a lot because performance matters. Unfortunately, optimization usually increases the number of assumptions the code must make about the state around it. If those assumptions are not guarded by solid ordering rules, the fast path can become the easiest place for a race to escape into the wild.That is what makes ext4’s fast commit path so interesting here. It is a feature designed to improve responsiveness, but it also inherits the burden of proving that every pointer it touches is fully initialized. The more aggressive the optimization, the stricter the safety discipline has to be.
Strengths and Opportunities
The good news is that this looks like a well-contained, well-understood bug with a clean upstream fix. The patch does not require a redesign, and the published crash trace gives downstream maintainers enough detail to validate the issue quickly. For administrators, that means the path to remediation is straightforward once the right kernel build is identified.- The fix is narrow and low-risk.
- It preserves ext4’s existing design and performance model.
- It addresses a genuine concurrency defect rather than papering over symptoms.
- It uses standard kernel publication primitives, which are easy to audit.
- It already appears in stable kernel references, improving backport prospects.
- It reduces the odds of a hard crash during normal sync activity.
- It reinforces a better discipline for object visibility in filesystem code.
Risks and Concerns
The main concern is that a race like this can be highly workload-dependent and therefore easy to underestimate. Systems that appear stable during ordinary testing may still hit the bug under real sync pressure, especially on machines with active writeback and fast-commit activity. That means the issue can remain hidden until it lands in production.- The crash may be rare but still operationally serious.
- Older kernels and vendor branches may remain exposed for some time.
- Users may misread the bug as a harmless filesystem annoyance.
- The failure can emerge only under concurrency, making QA coverage difficult.
- Affected systems may experience outages during routine I/O, not just exotic workloads.
- Backport timing will vary across distributions and OEM images.
- Misplaced confidence in “non-NULL” pointers can hide similar bugs elsewhere.
Looking Ahead
The next thing to watch is downstream adoption. The upstream fix is clear enough, but real-world protection depends on how quickly distributions and OEMs pull it into shipping kernels. For enterprise teams, the only meaningful question is whether the kernel image in production includes the corrected publication order.It is also worth watching whether this CVE prompts additional cleanup around ext4’s fast commit and journal attachment paths. Bugs like this often serve as a reminder that a subsystem’s state transitions need regular hardening, especially as features evolve and concurrency patterns become more complex. The best-case outcome is not just a patch, but a sharper mental model across the maintainer community for how and when inode-related state should be exposed.
- Confirm distro and vendor kernel backports.
- Check whether fast commit-heavy workloads show regression or stability improvements after the patch.
- Watch for follow-on ext4 fixes involving initialization order or object publication.
- Track whether other kernel subsystems adopt similar ordering cleanup after this case.
- Verify that production images, not just upstream trees, contain the correction.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center