When CVE-2026-31461 landed, it looked like a small kernel hygiene issue with a very specific trigger: in amdgpu_dm, the driver could overwrite
That architecture matters because display drivers are stateful. They track sinks, connectors, display modes, and EDID data across power transitions, hotplug events, and resume cycles. If a connector’s EDID pointer is refreshed at the wrong time or without cleaning up the previous object, the bug may not crash the machine immediately, but it can still accumulate leaked memory every time the system resumes. In kernel terms, that is not just untidy; it is a lifecycle mistake in a privileged component that is expected to be boringly correct.
EDID itself is central to how monitors and GPUs negotiate capabilities. It tells the system what resolutions, refresh rates, and features a connected sink supports. Because the AMD display manager caches and refreshes that information, the code path has to survive repeated suspend/resume events and connector revalidation without leaving stale allocations behind. The CVE description says the leak on a sink was connected and the previous
This is the kind of bug that rarely makes headlines on its own, but it fits a familiar pattern in kernel maintenance: a narrow fix in a widely used subsystem becomes security-relevant because it affects object lifetime, repeated transitions, and the correctness of memory ownership. The stable patch note attached to the CVE makes it clear the repair was intentionally minimal, which maintainers saw a precise bug rather than a design flaw.
Microsoft’s Security Update Guide now routinely publishes Linux-related CVEs alongside Windows and other ecosystem items, reflecting a broader reality: vulnerability management is cross-platform, and the same identifier often needs to flow through multiple vendor channels before defenders can act. Microsoft’s own guidance notes that the Security Update Guide is built around CVSS-style descriptions and machine-readable security data, which is why a Linux kernel bug can still show up in an MSRC update page.
At the technical core of CVE-2026-31461 is a simple ownership mistake.
That sounds like a small error, but kernel bugs that involve repeated allocation and replacement are often the ones that slip past code review. The code still “works” in the functional sense: the monitor still appears, the system still resumes, and the display still comes back. The leak is hidden because the visible user experience is largely intact, even as memory asens over time. That is why these bugs are operationally annoying and occasionally security-relevant even when they do not look dramatic.
A leak on resume is not the same as a leak on boot. Resume cycles can happen many times per day on laptops, docks, and mobile workstations. That makes the defn the real world than the phrase “memory leak” might imply. The vulnerability therefore belongs to the class of issues that are narrow in exploit shape but broad in recurrence.
The important question is not only “does memory leak?” but “how often does the system revisit the buggy path?” On devices that sleep and wake repeatedly, the answer can be often enough to matter. In the kernel, repetition is what turns a tiny flaw into something administrators eventually notice. That is the quiet danger here.
In practical terms, the bug is about correctness before it is about confidentiality or integrity. Bnel memory management is not a cosmetic matter. The kernel is responsible for orderly object ownership, and a leak in a core graphics path affects long-lived machines, especially those that routinely sleep and resume.
The NVD entry also matters because it situates the disclosure in a broader vulnerability-tracking pipeline. NVD had not yet assigned a CVSS score at the time of publication, but the fact that the record was already ingested suggessed from upstream kernel maintenance into the formal security ecosystem. That is usually when enterprise teams begin to notice, even if the technical severity remains modest.
That distinction matters because a lot of defenders still mentally sort CVEs into “urgent exploit” and “ignore later.” The Linux kernel does not always cooperate with that binary thinking. A subtle leak can be enough to justify a CVE if it affects a core subsystem, lands in stable, and is plausibly exploitable as part of a broader reliability or resource exhaustion story. Small does not mean irrelevant.
Stable backports also reduce ambiguity for downstream vendors. Instead of having to infer intent from a bug report, distro maintainers can pick up the same patch and track it across release lines. In a world where most Linux users consume kernels through vendors, not from mainline git, that backport path is often the difference between a theoretical fix and a deployed one.
The kernel documentation for AMDGPU display contributions emphasizes that the code is shared and heavily validated, including CI and IGT testing across multiple architectures and GPU families. That is a reminder that even in a mature subsystem, regressions can slip through because the test matrix is enormous and real-world display setups are wonderfully messy.
That’s why seemingly tiny cleanup mistakes become meaningful in this layer. A bug can sit dormant until a user closes a lid, wakes a machine, disconnects a display, or resumes from sleep with the exact connector topology that triggers the stale allocation path. This is what makes graphics bugs feel intermittent eve flaw is deterministic.
That is also why these bugs often get fixed in the most direct way possible. The best patch is usually not architectural. It is a precise ownership correction that restores the invariant the driver was already supposed to maintain. In this case, that invariant is simple: the previous
For individual desktops, the practical risk may be low unless suspend/resume is frequent and the system is running an affected kernel version. But laptops, developer workstations, and mobile systems are exactly the machines that sleep often. If the bug is triggered every time the machine wakes, the leak can become an operational headache even if no user ever notices a visible symptom.
Still, consumer devices are increasingly Linux-based in places users do not think about: thin clients, kiosks, docks, embedded boxes, and appliance-style systems. In those environments, a graphics driver leak is less about “my laptop uses a few extra megabytes” and more about “this device should be stable for months.” The latter is where kernel housekeeping problems become visible.
The enterprise angle is also about trust in the platform. Kernel memory management bugs raise questions about baseline hygiene, and even when the bug is not immediately exploitable, it can become part of a larger patch backlog. That is why CVEs like this get attention in vulnerability management systems: they may not be high-severity, but they are still indicators that a fleet is running on stale code.
The more subtle risk is operational drift. When teams assume “nothing bad happened,” they may stop auditing whally released what it should have. The result is that small leaks become accepted background noise, which is a dangerous habit in systems programming. Kernel leaks are never just about bytes; they are about discipline.
That simplicity is important because it suggests maintainers were dealing with a localized bug rather than a design-level flaw. In kernel work, the most valuable patches are ofthe least necessary surgery. When the bug is about a missing free, the best solution is almost always to make the lifetime explicit and unambiguous.
This is also a maintainability win. Future readers of the code can understand the ownership expectation quickly, which reduces the odds of a later regressi recur when ownership rules are implicit; the best fixes make those rules obvious. Explicit cleanup is a form of documentation.
Backportability matters more than dramatic language in the CVE text. Most organizations will never build the upstream kernel commit themselves. They will wait for a distro kernel, an OEM image update, or a vendor advisory. When a fix is this contained, the odds of it reaching deployed systems rise quickly.
That matters because the audience for this information is not just Linux kernel developers. It includes enterprise teams using Microsoft tools for compliance, asset management, and vulnerability tracking. A single CVE entry that is visible in a familiar ecosystem can move patching from “someone else’s problem” to an item on an administrator’s weekly queue.
There is also a practical benefit for operators who depend on structured vulnerability data. If the record is available in a consistent feed, it becomes easier to track which assets may be affected, which images need rebuilding, and which remediation owners should be notified. Metadata is boring until you need it.
This is especially is, where the practical impact depends more on the deployment pattern than on the headline severity. A leak in a laptop display stack and a leak in a fleet of docking-station workstations are not the same operational story. The score will matter, but so will context.
That makes it comparable to many stable-patch CVEs that involve leaks, stale state, or object lifetime mistakes. These issues rarely attract the same attention as use-after-free or out-of-bounds writes, but they are just as representative of the kind of engineering work that keeps mature kernels safe.
That is especially true in display code, where the user tends to blame a driver only when something visibly goes wrong. If the system seems fine, there is less incentive to investigate deeper, which is why correctness bugs can survive across release cycles until someone spots them in tooling or review. Silent failures are the most stubborn ones.
It also shows how the stable process works in practice. A developer finds a leak, backports the fix, and the CVE machinery turns that fix into a trackable security event. That pipeline is noisy, but it is also one of the best mechanisms open-source software has for turning code review into real-world defense.
There is also an indirect benefit: bugs like this tend to improve code review habits. Once maintainers see a leak pattern in one branch, they often look more carefully at adjacent code. That can uncover additional lifetime issues before they become public CVEs.
The risk is amplified by the fact that display bugs are often blamed on hardware or docking quirks rather than on the kernel. That can delay investigation, especially if users only notice the issue indirectly through performance degradation or inconsistent support tickets.
The lesson for defenders is simple: do not wait for the bug to manifest. Review the kernel version, check vendor advisories, and prioritize systems that routinely suspend and resume. That is where this CVE has the most realistic chance of causing practical trouble.
A second area to watch is whether downstream maintainers identify any adjacent cleanup opportunities in the AMD display path. Small ownership bugs often cluster, and once one is found, related code often gets more scrutiny. That is a good thing, because kernel maintenance is frequently about eliminating whole classes of lifecycle mistakes rather than one-off fixes.
It also shows the value of treating routine subsystems with unusual seriousness. Display code is easy to ignore until it fails, but its state transitions are as security-relevant as anything in networking or storage when memory ownership goes wrong. This CVE is a reminder that the safest kernel is the one that keeps even the quiet paths honest.
The most likely outcome here is uneventful, and that is exactly what a good fix should produce. If the patch reaches the kernels that matter,
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
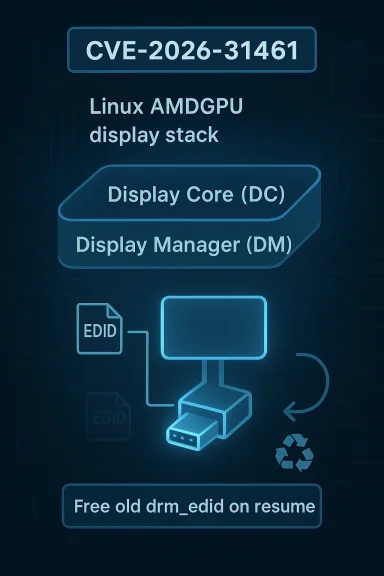
aconnector->drm_edid on resume without freeing the previous allocation first. The result was a memory leak in the Linux kernel’s AMD display path, and the fix was as straightforward as the bug itself: free the old drm_edid before storing the new one. The public record says the issue was assigned by kernel.org, published to NVD on April 22, 2026, and backported from commit 52024a94e7111366141cfc5d888b2ef011f879e5 into stable fixes referenced by kernel.org. AMD display stack in Linux is not a single monolithic block, but a layered system that splits Display Core (DC) from Display Manager (DM). DC handles the hardware-agnostic display logic, while DM provides the Linux- and DRM-specific glue that connects that logic to the rest of the graphics subsystem. Kernel documentation describes DM as the component that sits between DRM and DC, and it is this layer that the CVE touches.That architecture matters because display drivers are stateful. They track sinks, connectors, display modes, and EDID data across power transitions, hotplug events, and resume cycles. If a connector’s EDID pointer is refreshed at the wrong time or without cleaning up the previous object, the bug may not crash the machine immediately, but it can still accumulate leaked memory every time the system resumes. In kernel terms, that is not just untidy; it is a lifecycle mistake in a privileged component that is expected to be boringly correct.
EDID itself is central to how monitors and GPUs negotiate capabilities. It tells the system what resolutions, refresh rates, and features a connected sink supports. Because the AMD display manager caches and refreshes that information, the code path has to survive repeated suspend/resume events and connector revalidation without leaving stale allocations behind. The CVE description says the leak on a sink was connected and the previous
drm_edid was overwritten on resume.This is the kind of bug that rarely makes headlines on its own, but it fits a familiar pattern in kernel maintenance: a narrow fix in a widely used subsystem becomes security-relevant because it affects object lifetime, repeated transitions, and the correctness of memory ownership. The stable patch note attached to the CVE makes it clear the repair was intentionally minimal, which maintainers saw a precise bug rather than a design flaw.
Microsoft’s Security Update Guide now routinely publishes Linux-related CVEs alongside Windows and other ecosystem items, reflecting a broader reality: vulnerability management is cross-platform, and the same identifier often needs to flow through multiple vendor channels before defenders can act. Microsoft’s own guidance notes that the Security Update Guide is built around CVSS-style descriptions and machine-readable security data, which is why a Linux kernel bug can still show up in an MSRC update page.
 What the Bug Actually Does
What the Bug Actually Does
At the technical core of CVE-2026-31461 is a simple ownership mistake. aconnector->drm_edid was assigned a new allocation while the old one remained live, which meant eacheak kernel memory tied to the prior EDID object. The CVE record’s own description is blunt about the mechanism: free the previous drm_edid before updating it.That sounds like a small error, but kernel bugs that involve repeated allocation and replacement are often the ones that slip past code review. The code still “works” in the functional sense: the monitor still appears, the system still resumes, and the display still comes back. The leak is hidden because the visible user experience is largely intact, even as memory asens over time. That is why these bugs are operationally annoying and occasionally security-relevant even when they do not look dramatic.
Why resume paths are fragile
Suspend and resume logic is one of the hardest places to keep clean in a kernel driver. A normal runtime path may allocate, free, and refresh data in a predictable order, but resume code often has to reconcile hardware state, software cache state, and connector state all at once. In a display driver, that means the code can be forced to revisit the same EDID object repeatedly, which makes stale references easy to miss.A leak on resume is not the same as a leak on boot. Resume cycles can happen many times per day on laptops, docks, and mobile workstations. That makes the defn the real world than the phrase “memory leak” might imply. The vulnerability therefore belongs to the class of issues that are narrow in exploit shape but broad in recurrence.
The important question is not only “does memory leak?” but “how often does the system revisit the buggy path?” On devices that sleep and wake repeatedly, the answer can be often enough to matter. In the kernel, repetition is what turns a tiny flaw into something administrators eventually notice. That is the quiet danger here.
Why EDID handling is special
EDID data is not arbitrary driver state. It is the kernel’s negotiated understanding of the attached display. That means the object often sits at the boundary between hardware discovery and user-visible behavior, which is exactly where lifetime errors become hard to reason about. A pointer swap that forgets to release the old object can remain invisible until memory pressure, validation tooling, or repeated suspend/resume cycles expose it.In practical terms, the bug is about correctness before it is about confidentiality or integrity. Bnel memory management is not a cosmetic matter. The kernel is responsible for orderly object ownership, and a leak in a core graphics path affects long-lived machines, especially those that routinely sleep and resume.
Why This Became a CVE
Not every kernel bug earns a CVE, so the assignment itself is telling. This one crossed the threshold because it is a security-relevant kernel defect in a widely deployed driver path, and because its behavior is concrete, reproducible, and suitable for stapublic record shows the CVE was received from kernel.org and immediately tied to stable patch references, which is the kind of paper trail that usually accompanies legitimate security maintenance.The NVD entry also matters because it situates the disclosure in a broader vulnerability-tracking pipeline. NVD had not yet assigned a CVSS score at the time of publication, but the fact that the record was already ingested suggessed from upstream kernel maintenance into the formal security ecosystem. That is usually when enterprise teams begin to notice, even if the technical severity remains modest.
CVE assignment is not just about dramatic exploits
Kernel CVEs are not reserved for remote code execution or privilege escalation. They also cover defects that create memory pressure, destabilize subsystems, or expose correctness failures that can be chained with other problems. A memory leak in a trusted driver path is a classic example of a bug that is not flashy but still worth tracking.That distinction matters because a lot of defenders still mentally sort CVEs into “urgent exploit” and “ignore later.” The Linux kernel does not always cooperate with that binary thinking. A subtle leak can be enough to justify a CVE if it affects a core subsystem, lands in stable, and is plausibly exploitable as part of a broader reliability or resource exhaustion story. Small does not mean irrelevant.
The stable backport signal
The CVE description explicitly references a cherry-pick from an upstream commit, and the published referenernel commits rather than a speculative future fix. That usually tells operators two things: the bug is understood, and the maintainers are comfortable shipping a narrowly scoped correction without disturbing unrelated code.Stable backports also reduce ambiguity for downstream vendors. Instead of having to infer intent from a bug report, distro maintainers can pick up the same patch and track it across release lines. In a world where most Linux users consume kernels through vendors, not from mainline git, that backport path is often the difference between a theoretical fix and a deployed one.
The Display Stack Context
The AMD GPU display stack is one of those subsystems where functionality and reliability are tightly intertwined. It has to manage connector discovery, monitor negotiation, power state transitions, and a steady stream of edge cases from docks, adapters, and hotplug events. That makes it a fertile place for lifetime bugs, especially in code that runs after suspend or resume.The kernel documentation for AMDGPU display contributions emphasizes that the code is shared and heavily validated, including CI and IGT testing across multiple architectures and GPU families. That is a reminder that even in a mature subsystem, regressions can slip through because the test matrix is enormous and real-world display setups are wonderfully messy.
Why display code sees so many edge cases
Display code has to handle hardware diversity, driver complexity, and user behavior all at once. A monitor can be attached directly, through a dock, through a KVM, or through adapters that change the timing and state sequence in unpredictable ways. Every one of those variations can cause a connector to be revalidated or an EDID object to be refreshed.That’s why seemingly tiny cleanup mistakes become meaningful in this layer. A bug can sit dormant until a user closes a lid, wakes a machine, disconnects a display, or resumes from sleep with the exact connector topology that triggers the stale allocation path. This is what makes graphics bugs feel intermittent eve flaw is deterministic.
Resume and reconnection are where state bugs hide
Power management paths are particularly good at exposing wrong assumptions. A driver may treat the resume path as a re-entry into an already-initialized state, but the hardware and cached software objects are often only partially valid. If the driver then replaces an EDID pointer without first freeing the old one, the leak is baked into the restore sequence.That is also why these bugs often get fixed in the most direct way possible. The best patch is usually not architectural. It is a precise ownership correction that restores the invariant the driver was already supposed to maintain. In this case, that invariant is simple: the previous
drm_edid he new one is installed. That is the whole fix, and also the whole lesson.Security Impact in Practice
The immediate impact of this CVE is a memory leak, not a memory corruption flaw. That means the likely security profile is more about resource exhaustion and driver hygiene than direct code execution. Still, kernel leaks matter because they occur in privileged code and can accumulate silently over time.For individual desktops, the practical risk may be low unless suspend/resume is frequent and the system is running an affected kernel version. But laptops, developer workstations, and mobile systems are exactly the machines that sleep often. If the bug is triggered every time the machine wakes, the leak can become an operational headache even if no user ever notices a visible symptom.
Consumer impact
For consumers, the issue is mostly about stability and long-term memory usage. A desktop system with a monitor attached and occasional sleep cycles may never show an obvious effect, especially if the leak is small. That can make the bug easy to dismiss, which is exactly how leaks survive in the wild.Still, consumer devices are increasingly Linux-based in places users do not think about: thin clients, kiosks, docks, embedded boxes, and appliance-style systems. In those environments, a graphics driver leak is less about “my laptop uses a few extra megabytes” and more about “this device should be stable for months.” The latter is where kernel housekeeping problems become visible.
Enterprise impact
Enterprises care because a leak in a graphics driver is not isolated from fleet management. Workstations with docking stations, remote desktop hosts, and mixed GPU endpoints often have repeated resume cycles, especially in hybrid work environments. A memory leak that only shows up on wake can still cost admin time, support tickets, and confidence in the device image.The enterprise angle is also about trust in the platform. Kernel memory management bugs raise questions about baseline hygiene, and even when the bug is not immediately exploitable, it can become part of a larger patch backlog. That is why CVEs like this get attention in vulnerability management systems: they may not be high-severity, but they are still indicators that a fleet is running on stale code.
Why “just a leak” is not always harmless
A leak is often treated as a low-grade issue, but that view can be misleading. Repeated leaks can create performance degradation, trigger OOM conditions in constrained environments, or combine with other bugs to make exploitation easier. Even when none of that happens, the bug represents a failure of resource ownership in a privileged subsystem.The more subtle risk is operational drift. When teams assume “nothing bad happened,” they may stop auditing whally released what it should have. The result is that small leaks become accepted background noise, which is a dangerous habit in systems programming. Kernel leaks are never just about bytes; they are about discipline.
The Fix and Why It Matters
The fix for CVE-2026-31461 is refreshingly narrow. It does not restructure the AMD display manager or change how EDID discovery works. It simply frees the olddrm_edid before assigning the new one, restoring correct ownership semantics around the connector object.That simplicity is important because it suggests maintainers were dealing with a localized bug rather than a design-level flaw. In kernel work, the most valuable patches are ofthe least necessary surgery. When the bug is about a missing free, the best solution is almost always to make the lifetime explicit and unambiguous.
What a correct ownership fix looks like
A proper fix in this context means the driver must treat the old EDID allocation as disposable once a fresh sink read occurs. That ensures the connector state reflects the current hardware rather than accumulating stale allocations from prior resume events. The CVE record’s wording matches exactly that approach.This is also a maintainability win. Future readers of the code can understand the ownership expectation quickly, which reduces the odds of a later regressi recur when ownership rules are implicit; the best fixes make those rules obvious. Explicit cleanup is a form of documentation.
Why the patch is easy to backport
Because the change is so localized, it is a strong candidate for stable and vendor backports. The fix changes no user-facing behavior beyond removing the leak, and it does not depend on large architectural changes or new APIs. That makes it safer for long-term-support kernels that need security fixes without churn.Backportability matters more than dramatic language in the CVE text. Most organizations will never build the upstream kernel commit themselves. They will wait for a distro kernel, an OEM image update, or a vendor advisory. When a fix is this contained, the odds of it reaching deployed systems rise quickly.
Microsoft’s Role in the Disclosure
It may seem odd at first glance that a Linux kernel CVE appears on Microsoft’s update guide, but that is normal in modern vulnerability management. Microsoft’s Security Update Guide now catalogs a broad range of third-party vulnerabilities and uses CVSS-oriented metadata to help customers and defenders track them consistently.That matters because the audience for this information is not just Linux kernel developers. It includes enterprise teams using Microsoft tools for compliance, asset management, and vulnerability tracking. A single CVE entry that is visible in a familiar ecosystem can move patching from “someone else’s problem” to an item on an administrator’s weekly queue.
Why cross-vendor publication helps
Cross-vendor publication reduces the risk that a Linux issue gets lost in Linux-only channels. Many enterprises run mixed environments, and their security tooling often ingests Microsoft-flavored advisories alongside Red Hat, Ubuntu, SUSE, and upstream kernel notices. A CVE page in Microsoft’s guide helps anchor the issue in that broader workflow.There is also a practical benefit for operators who depend on structured vulnerability data. If the record is available in a consistent feed, it becomes easier to track which assets may be affected, which images need rebuilding, and which remediation owners should be notified. Metadata is boring until you need it.
What the missing CVSS score means
At the time reflected in the record, NVD had not yet provided a final score. That does not mean the issue is unimportant; it means the formal enrichment process had not finished. For administrators, this is a reminder not to wait passively for a number before reviewing exposure.This is especially is, where the practical impact depends more on the deployment pattern than on the headline severity. A leak in a laptop display stack and a leak in a fleet of docking-station workstations are not the same operational story. The score will matter, but so will context.
Comparison With Other Kernel Fixes
Linux kernel security work often falls into two broad categories: bugs that clearly threaten memory safety, and bugs that are “just” correctness problems but still deserve attention because they happen in privileged code. CVE-2026-31461 sits in the second bucket. It is not a wild exploit primitive, but it is still a real defect in the kernel’s resource-management discipline.That makes it comparable to many stable-patch CVEs that involve leaks, stale state, or object lifetime mistakes. These issues rarely attract the same attention as use-after-free or out-of-bounds writes, but they are just as representative of the kind of engineering work that keeps mature kernels safe.
Why modest bugs still matter
The Linux kernel is large, heavily optimized, and constantly exposed to real hardware behavior. A bug that leaks memory during a resume path can remain invisible for a long time because it does not explode immediately. But the absence of a crash is not the same as the absence of impact.That is especially true in display code, where the user tends to blame a driver only when something visibly goes wrong. If the system seems fine, there is less incentive to investigate deeper, which is why correctness bugs can survive across release cycles until someone spots them in tooling or review. Silent failures are the most stubborn ones.
What this says about kernel maintenance
The patch shows that upstream maintainers continue to focus on small but meaningful cleanup in core subsystems. That is a sign of kernel maturity, not weakness. Mature software is not defined by the absence of bugs; it is defined by how quickly it detects and corrects tg]It also shows how the stable process works in practice. A developer finds a leak, backports the fix, and the CVE machinery turns that fix into a trackable security event. That pipeline is noisy, but it is also one of the best mechanisms open-source software has for turning code review into real-world defense.
Strengths and Opportunities
The positive side of this disclosure is that it demonstrates a healthy maintenance pipeline. The fix is straightforward, the affected code path is known, and the backport path is already visible, which gives downstream vendors a clear target for remediation. That kind of clarity is worth a lot in kernel security, where ambiguity often costs more time than the patch itself.- The root cause is narrow and easy to understand.
- The fix is small enough to backport safely.
- The issue sits in a well-defined driver path rather than a sprawling subsystem.
- The CVE provides a clear ownership lesson for kernel maintainers.
- Enterprise patch teams can map it to resume-heavy endpoints quickly.
- Microsoft’s publication model helps centralize visibility for mixed environments.
- The event reinforces the value of stable kernel maintenance and lifecycle hygiene.
- Because the bug is a leak, not corruption, it is less likely to introduce regression risk when fixed carefully.
Why this is still a useful security event
A low-drama CVE can still improve the ecosystem. It pushes vendors to audit connector-state handling, encourages betdiscipline, and reminds operators that repeated suspend/resume cycles are a real workload. Those are not dramatic benefits, but they are durable ones.There is also an indirect benefit: bugs like this tend to improve code review habits. Once maintainers see a leak pattern in one branch, they often look more carefully at adjacent code. That can uncover additional lifetime issues before they become public CVEs.
Risks and Concerns
The main concern is underestimation. Because the issue is “only” a memory leak, organizations may rank it below more explosive vulnerabilities and defer patching, especially if there is no visible user impact. That would be a mistake, because repetitive leaks in a kernel driver can still degrade stability and complicate fleet support.- The bug may be dismissed as low priority because it lacks a crash or exploit.
- Long-lived systems with frequent sleep cycles may accumulate the leak over time.
- Distros and OEMs may backport at different speeds, creating patch unevenness.
- Vulnerability scanners may not clearly reflect local kernel backports.
- Device owners may not realize they are affected because the symptom is silent resource growth.
- Resume-related bugs are easy to miss in testing unless suspend cycles are explicitly exercised.
- Consumers may think the issue is irrelevant, while the real exposure is in laptops, docks, and appliance-like devices.
Why operational visibility is limited
This is not the kind of bug that screams for attention. There is no obvious pop-up, no failed login, no obvious security alert. The machine resumes, the monitor lights up, and everything seems normal. That makes the issue easy to miss in environments that do not monitor kernel memory behavior closely.The risk is amplified by the fact that display bugs are often blamed on hardware or docking quirks rather than on the kernel. That can delay investigation, especially if users only notice the issue indirectly through performance degradation or inconsistent support tickets.
Why patch lag still matters
Even with a clean fix, the real-world exposure persists until vendors ship it. Linux systems live through distro channels, OEM images, appliances, astreams, so there is often a delay between upstream resolution and on-device remediation. That gap is where many CVEs remain operationally relevant.The lesson for defenders is simple: do not wait for the bug to manifest. Review the kernel version, check vendor advisories, and prioritize systems that routinely suspend and resume. That is where this CVE has the most realistic chance of causing practical trouble.
What to Watch Next
The immediate thing to watch is how quickly the fix propagates into distribution kernels and vendor advisories. For most organizations, that will matter far more than the upstream commit hash itself, because the deployed kernel version is the only version that counts in production.A second area to watch is whether downstream maintainers identify any adjacent cleanup opportunities in the AMD display path. Small ownership bugs often cluster, and once one is found, related code often gets more scrutiny. That is a good thing, because kernel maintenance is frequently about eliminating whole classes of lifecycle mistakes rather than one-off fixes.
Key developments to monitor
- Vendor backports for long-term-support kernels.
- Distribution advisories that name affected AMDGPU release streams.
- Any follow-up fixes in amdgpu_dm or neighboring display code.
- Whether enterprise tools classify the issue as a memory-management concern or a more general stability bug.
- The appearance of a finalized CVSS score in NVD or vendor guidance.
- Whether laptop and dock-heavy fleets report any suspend/resume anomalies after patch rollout.
Why this CVE matters beyond the immediate bug
The broader story is not that one EDID pointer leaked memory. It is that the Linux kernel continues to mature through a relentless series of exact, targeted corrections. That is how a large, long-lived codebase gets safer: not with sweeping rewrites, but with thousands of small decisions that preserve ownership, correctness, and predictability.It also shows the value of treating routine subsystems with unusual seriousness. Display code is easy to ignore until it fails, but its state transitions are as security-relevant as anything in networking or storage when memory ownership goes wrong. This CVE is a reminder that the safest kernel is the one that keeps even the quiet paths honest.
The most likely outcome here is uneventful, and that is exactly what a good fix should produce. If the patch reaches the kernels that matter,
drm_edid will be freed correctly, the resume path will stop leaking memory, and one more small but real defect will disappear from the long tail of Linux maintenance. In kernel security, that kind of boring success is not a footnote; it is the whole point.Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center