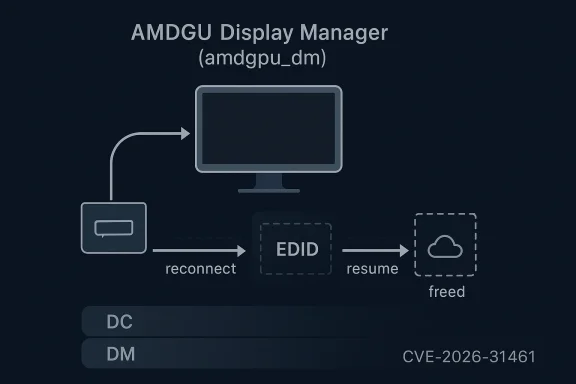
Linux has just gained another narrowly scoped but still important security fix in its AMD display stack, and this time the issue is a memory leak rather than a crash or a classic memory corruption bug. CVE-2026-31461 tracks a drm_edid leak in amdgpu_dm, where reconnect or resume handling could overwrite
That architecture also helps explain why lifecycle bugs in display code are so common. The driver is constantly juggling hotplug events, resume operations, EDID parsing, atomic state updates, and multiple layers of helper infrastructure. AMD’s own documentation emphasizes how heavily the display stack is validated, including suspend/resume testing and extensive IGT coverage, which is a good sign—but also a reminder that even well-tested code can still miss a subtle ownership error.
EDID handling is especially sensitive because it is tied to display discovery and mode setting. The Linux DRM KMS documentation makes clear that connector state includes EDID-related data and that these fields are managed through specific helper families rather than casual direct mutation. That makes the bug in CVE-2026-31461 look small on the surface, but it also shows why the fix is important: if a connector’s EDID pointer is replaced during resume without releasing the previous object, the leak repeats each time the path is hit.
This kind of issue is not the kind of defect that makes a dramatic exploit demo. It is quieter than that, but in many fleets quiet bugs are the ones that create the most operational friction. A leak in a resume path may not be visible during a normal desktop session, yet it can still matter on laptops, docks, workstation systems, and fleet images that suspend and resume constantly. That is exactly the kind of pattern modern kernel maintenance tries to catch before it becomes a support headache.
The CVE record itself shows the fix was cherry-picked from commit 52024a94e7111366141cfc5d888b2ef011f879e5, with stable references published through kernel.org. The public description is concise, but it is enough to tell the stect ownership, the trigger is a connected sink during resume, and the remediation is to release the old EDID before updating the connector state.
At its core, CVE-2026-31461 is a memory leak in the AMDGPU display manager. The affected logic updates
The public wording in the CVE record is unusually clear: the sink-connected path overwrote the connector’s EDID pointer without freeing the old allocation, and the fix simply frees the previous object before updating the pointer. That narrowness is btructive. It means the bug is likely limited in scope, but it also highlights how much of kernel correctness depends on exact ownership discipline.
A memory leak does not always produce a visible failure right away. Instead, it can show up as degradation: slower resume behavior, increased memory pressure, instability on constrained systems, or symptoms that appear unrelated to the real cause. That makes it harder for administrators to diagnose and easier to dismiss as “just a flaky driver,” which is why even a modest-seeming CVE can be worth tracking.
That is why display bugs often read like housekeeping failures but behave like infrastructure problems. A connector is not just a port; it is a live state machine with a memory footprint. Small mistakes in the state machine may not crash the system immediately, but they can still affect reliability in ways that enterprise users notice.
A leak in display code also has a special kind of invisibility. Users can see bad visuals or a failed wake, but they generally cannot see the leaked object count. That makes detection dependent on profiling, logs, or someone noticing that a repeated action slowly changes the machine’s behavior. In other words, quiet bugs can still be expensive bugs.
This also matters because display code has a tendency to attract “fix one thing, break three others” patches. The narrower the change, the easier it is to backport into stable branches and the lower the chance of regression in a path that already has enough moving parts. AMD’s own documentation shows how much of the stack is validated around suspend/resume, hotplugging, and display topology changes, which is exactly whx is preferable here.
The absence of a CVSS score at publication time should not be read as absence of importance. cord is new enough that NVD has not finished scoring it. In practice, the operational question is not whether this is a dramatic exploit; it is whether the affected kernels can leak memory in a common path. The answer, based on the record, is yes.
The upside is that this is not a remotely triggerable network issue, and nothing in the public description suggests arbitrary code execution. That means it belongs in the “patch promptly, but don’t panic” category. Still, users who see resume-related weirdness on AMD hardware should not ignore it just because it does not sound as severe as a memory corruption CVE.
Administrators should also remember that display issues are often misclassified. A bug like this may be logged internally as a “graphics annoyance,” even though it is really a kernel resource management problem. That gap between symptoms and root cause is one reason why display driver updates deserve the same version control discipline as storage or networking fixes.
It also suggests a broader lesson for kernel maintainers: even when the display stack is being heavily exercised, certain combinations of resume, connector state, and object replacement can slip through ordinary validation. That is not a failure of engineering discipline so much as evidence that stateful systems create edge cases faster than test matrices can fully enumerate them.
The broader implication is that the Linux graphics stack still benefits enormously from conservative maintenance. Small fixes, especially those involving allocation ownership, are where long-term stability is won. If anything, CVE-2026-31461 is a reminder that well-maintained code still needs careful backporting because correctnesse themselves loudly in advance.
The more mature enterprise response is to map the advisory to your asset inventory rather than to a general severity label. If the affected systems sleep, resume, and hotplug monitors frequently, the bug is more relevant than a generic “low-severity leak” classification might suggest. That is exactly why kernel CVEs need context, not just a score.
It is also worth watching whether similarr in adjacent AMD display paths. The graphics stack is full of connector, stream, and EDID-handling objects, and bugs in one object lifecycle often reveal review targets in neighboring code. That does not mean another flaw is guaranteed, but it does mean maintainers may use this case as a cue to auflows more aggressively.
For defenders, the next practical checkpoint is simple: verify that the kernel you run contains the corrected behavior, test suspend/resume on AMD systems, and treat graphics stability regressions as security-relevant until proven otherwise. That is the best way to turn a small CVE into a broader improvement in fleet hygiene rather than just another line item in an advisory feed.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
aconnector->drm_edid without freeing the previous allocation first, slowly wasting memory each time the path was exercised. The published record says the fix is straightforward: free the old EDID object before assigning the new one, and the CVE is already flowing through the Linux stable pipeline and Microsoft’s Security Update Guide ecosystem. inux graphics stack is a layered system, and amdgpu_dm sits in the middle of a particularly important one. AMD’s Display Core architecture splits responsibilities between the OS-agnostic Display Core (DC) and the OS-dependent Display Manager (DM), with DM acting as the bridge between DRM and the hardware-facing display core. The kernel documentation describes that arrangement explicitly, and it is the reason a bug in the connector-handling path can have consequences well beyond a single code branch.That architecture also helps explain why lifecycle bugs in display code are so common. The driver is constantly juggling hotplug events, resume operations, EDID parsing, atomic state updates, and multiple layers of helper infrastructure. AMD’s own documentation emphasizes how heavily the display stack is validated, including suspend/resume testing and extensive IGT coverage, which is a good sign—but also a reminder that even well-tested code can still miss a subtle ownership error.
EDID handling is especially sensitive because it is tied to display discovery and mode setting. The Linux DRM KMS documentation makes clear that connector state includes EDID-related data and that these fields are managed through specific helper families rather than casual direct mutation. That makes the bug in CVE-2026-31461 look small on the surface, but it also shows why the fix is important: if a connector’s EDID pointer is replaced during resume without releasing the previous object, the leak repeats each time the path is hit.
This kind of issue is not the kind of defect that makes a dramatic exploit demo. It is quieter than that, but in many fleets quiet bugs are the ones that create the most operational friction. A leak in a resume path may not be visible during a normal desktop session, yet it can still matter on laptops, docks, workstation systems, and fleet images that suspend and resume constantly. That is exactly the kind of pattern modern kernel maintenance tries to catch before it becomes a support headache.
The CVE record itself shows the fix was cherry-picked from commit 52024a94e7111366141cfc5d888b2ef011f879e5, with stable references published through kernel.org. The public description is concise, but it is enough to tell the stect ownership, the trigger is a connected sink during resume, and the remediation is to release the old EDID before updating the connector state.
 What the Vulnerability Actually Is
What the Vulnerability Actually Is
At its core, CVE-2026-31461 is a memory leak in the AMDGPU display manager. The affected logic updates aconnector->drm_edid when a sink is connected, but the previous drm_edid allocation was not freed first. Over time, repeated resume e lost allocations, which is the classic footprint of a resource lifecycle bug rather than a structural memory safety flaw.Why this matters
A leak sounds harmless until you look at the path it lives in. Resume handling is not an edge case for mobile systems; it is a routine operation. If a driver leaks on every reconnect or resume, the bug can become a persistent slow burn, especially on laptops, docking stations, and multi-monitor systems that regularly cycle through display detection.The public wording in the CVE record is unusually clear: the sink-connected path overwrote the connector’s EDID pointer without freeing the old allocation, and the fix simply frees the previous object before updating the pointer. That narrowness is btructive. It means the bug is likely limited in scope, but it also highlights how much of kernel correctness depends on exact ownership discipline.
A memory leak does not always produce a visible failure right away. Instead, it can show up as degradation: slower resume behavior, increased memory pressure, instability on constrained systems, or symptoms that appear unrelated to the real cause. That makes it harder for administrators to diagnose and easier to dismiss as “just a flaky driver,” which is why even a modest-seeming CVE can be worth tracking.
The resume path angle
The most interesting part of this bug is that it is tied to resume. Suspend/resume paths are often the most fragile code in graphics drivers because they have to restore hardware state while also re-validating display topology. That means the bug is not about one-time initialization; it is about the repeated transition between power states, where stale objects and replacement logic tend to collide.- The fl sink is connected.
- The connector’s EDID pointer is overwritten.
- The previous allocation is not released first.
- Repeated resumes can accumulate leaked memory.
- The fix is to free the old EDID before assignment.
Why EDID Handling Is So Sensitive
EDID is the data that tells the GPU what a monitor can do: resolution ranges, refresh rates, color capabilities, and other display characteristics. In kernel terms, it is part of the connector’s state, and the DRM subsystem treats connector bookkeeping carefully for a reason. The documentation around DRM connector state and EDID handling makes clear that this is not something drivers are supposed to manipulate casually or inconsistently.Ownership rules matter
The bug is a textbook example of what happens when ownership rules get blurred. Once the driver has an allocated EDID object, it must either transfer, reuse, or free it deliberately. Overwriting the pointer without freeing the old allocation breaks that contract, and the fact that the bug was found in resume logic suggests a second layer of complexity: the object likely survives long enough to matter during power transitions, then gets replaced during the next detection pass.That is why display bugs often read like housekeeping failures but behave like infrastructure problems. A connector is not just a port; it is a live state machine with a memory footprint. Small mistakes in the state machine may not crash the system immediately, but they can still affect reliability in ways that enterprise users notice.
The practical impact
For consumer devices, the most likely effect is gradual annoyance rather than instant failure. A system may resume more slowly, show instability after repeated dock undock cycles, or exhibit memory growth that only becomes noticeable after many power-state changes. For enterprise fleets, that turns into a support issue because the same bug can be multiplied across hundreds or thousands of endpoints.A leak in display code also has a special kind of invisibility. Users can see bad visuals or a failed wake, but they generally cannot see the leaked object count. That makes detection dependent on profiling, logs, or someone noticing that a repeated action slowly changes the machine’s behavior. In other words, quiet bugs can still be expensive bugs.
- EDID is central to monitor discovery and capability reporting.
- Connector state is part of DRM’s structured lifecycle.
- Resume paths are high-risk because they rehydrate live hardware state.
- Leaks can look like generic instability instead of a discrete flaw. ([kernel.org](https://www.kernel.org/doc/html/v6.9/gpu/drm-kms.he Fix Changes
drm_edid before updating the connector’s EDID pointer. That is the kind of fix kernel maintainers like because it resolves the immediate ownership defect without changing the wider display flow. The CVE entry says the patch was cherry-picked from commit `52024a94e7111366141cfc5d888b2ef011f87eferences confirm it has already been folded into kernel maintenance history.Surgical fixes are usually best
The strongest kernel fixes are often the ones that solve a single invariant violation cleanly. Here, the invariant is simple: if a connector replaces its EDID object, the old object must not be abandoned. That is a good example of correctness through disciplined ownership, not a wider redesign of how display discovery works.This also matters because display code has a tendency to attract “fix one thing, break three others” patches. The narrower the change, the easier it is to backport into stable branches and the lower the chance of regression in a path that already has enough moving parts. AMD’s own documentation shows how much of the stack is validated around suspend/resume, hotplugging, and display topology changes, which is exactly whx is preferable here.
Why this is a stable-kernel style fix
The public record shows the issue was handled in the same way many Linux kernel CVEs are handled: identify the bad lifecycle pattern, patch the ownership bug, and push the change into stable branches. That is a sign the maint as concrete and low-risk to fix, which is generally what operators want to hear.The absence of a CVSS score at publication time should not be read as absence of importance. cord is new enough that NVD has not finished scoring it. In practice, the operational question is not whether this is a dramatic exploit; it is whether the affected kernels can leak memory in a common path. The answer, based on the record, is yes.
- The fix is narrow and targeted.
- It preserves the existing display flow.
- It is suited to stable backporting.
- It reduces regression risk compared with a larger redesign.
Who Is Most Affected
The obvious affected group is anyone running Linux systems with AMDGPU display support. But the practical exposure is not uniform. Systems that suspend and resume frequently, use external monitors, or rely on docking stations are more likely to exercise the vulnerable path than fixed appliances or headless machines.Consumer systems
For consumers, the risk is mostly about reliability. A laptop connected to a monitor, a home workstation that sleeps and wakes repeatedly, or a desktop that is frequently hotplugged will hit the EDID refresh path more often. That makes the bug more likely to pry pressure or mysterious display oddities over time.The upside is that this is not a remotely triggerable network issue, and nothing in the public description suggests arbitrary code execution. That means it belongs in the “patch promptly, but don’t panic” category. Still, users who see resume-related weirdness on AMD hardware should not ignore it just because it does not sound as severe as a memory corruption CVE.
Enterprise systems
For enterprise fleets, the bigger issue is scale. A memory leak that costs a little on a single workstation becomes more meaningful when it affects a standard image deployed across many laptops or workstations. That is especially true in environments where end users routinely dock and undock devices, or where suspend/resume is part of daily mobility workflows.Administrators should also remember that display issues are often misclassified. A bug like this may be logged internally as a “graphics annoyance,” even though it is really a kernel resource management problem. That gap between symptoms and root cause is one reason why display driver updates deserve the same version control discipline as storage or networking fixes.
- Mobile workers on AMD laptops are the most likely to notice it.
- Docking-station environments are prime repeat-trigger scenarios.
- Desktop fleets may see it only after prolonged use.
- Headless servers are less likely to be impacted directly.
How This Fits the Bigger AMDGPU Picture
AMD’s display stack is documented as a shared, multi-layered system that receives continuous validation across hardware types and OS integration points. That matters because a bug like CVE-2026-31461 is not a sign that the display subsystem is unusually broken; it is a sign that mature kernel code still depends on exact lifetime management, especially around state refreshes and suspend/resume.The testing story
The documentation notes that AMD’s display code is validated with manual and automated tests, including suspend/resume, hotplugging, and multiple-display scenarios. That is important context because it shows the fix belongs to the class of issues test teams actively try to catch. The fact that it still made it to a CVE tells you how tricky lifecycle bugs can be in a real-world driver.It also suggests a broader lesson for kernel maintainers: even when the display stack is being heavily exercised, certain combinations of resume, connector state, and object replacement can slip through ordinary validation. That is not a failure of engineering discipline so much as evidence that stateful systems create edge cases faster than test matrices can fully enumerate them.
Why this is not unusual
Kernel graphics drivers are often fued caches, refcounts, helper objects, and state snapshots. EDID data fits right into that pattern. A bug like this is therefore not unusual in nature, only in timing; it happens where the driver is switching between hardware-presence detection and software-managed connector state, which is exactly where lifetime mistakes are easiest to make.The broader implication is that the Linux graphics stack still benefits enormously from conservative maintenance. Small fixes, especially those involving allocation ownership, are where long-term stability is won. If anything, CVE-2026-31461 is a reminder that well-maintained code still needs careful backporting because correctnesse themselves loudly in advance.
What operators should infer
- Testing helps, but it cannot eliminate every edge case.
- Suspend/resume remains a high-value validation target.
- EDID and connector state are not “just metadata.”
- Backports matter because the production kernel is what counts.
Enterprise Patch Priorities
Organizations should treat this as a **stability-and-correctny tracking attached. The lack of a published CVSS score does not reduce the need to patch; it only means the public scoring pipeline has not finished assigning a severity value yet. In practice, the right response is to identify AMDGPU-equipped endpoints, confirm the kernel build in use, and verify whether the stable fix is present.Operationally, what to check
If your fleet contains AMD mobile workstations, developer laptops, or dock-heavy desktop setups, this should be on the patch watchlist. The relevant question is not whether the machine ever displayed a symptom, but whether it runs a kernel branch that still contains the pre-fix amdgpu_dm logic. Because the published fix ae references, downstream distributions should eventually carry it if they have not already.The more mature enterprise response is to map the advisory to your asset inventory rather than to a general severity label. If the affected systems sleep, resume, and hotplug monitors frequently, the bug is more relevant than a generic “low-severity leak” classification might suggest. That is exactly why kernel CVEs need context, not just a score.
Practical remediation sequence
- Identify AMDGPU systems in your fleet.
- Checkkernel includes the stable fix.
- Prioritize mobile and docked endpoints first.
- Validate resume and multi-monitor behavior after patching.
- Watch for vendor backports in your distribution stream.
Why version verification matters
One of the most common mistakes in Linux security operations is assuming that a CVE announcement means a fix is already present on the box. That is not always true, especially when vendors backport chls. Here, the only reliable answer is to confirm the shipped kernel contains the corrected EDID lifetime handling.- Inventory AMDGPU usage first.
- Confirm the kernel branch, not just the distro name.
- Validate post-patch resume behavior.
- Do not rely on CVE publication alone as proof of remediation.
Strengths and Opportunitieat CVE-2026-31461 is the kind of bug that kernel maintainers can fix cleanly and operators can reason about quickly. The vulnerability description is precise, the remediation is simple, and the affected path is a standard lifecycle transition that most modern patch programs already test. That makes it a good candidate for rapid backporting and low-friction operational remediation.
- The bug is narrowly defined and easy to understand.
- The fix is small and low-risk to backport.
- Resume-path issues are straightforward to validate after patching.
- The record already points to stable kernel references.
- The issue reinforces better object lifetime discipline.
- AMD’s documentation shows the path is already heavily tested.
- Enterprises can map exposure directly to AMDGPU-equipped devices.
Risks and Concerns
The biggest risk is underestimating a leak because itmatic as a memory corruption flaw. That would be a mistake. In a kernel display stack, repeated leaks can slowly erode reliability, and because the symptom may appear only after many suspend/resume cycles, the real cause can be easy to miss.- Resume-heavy laptops may accumulate lea- Users may blame the driver generally instead of the specific bug.
- Vendor backports may land on different schedules across distros.
- Symptoms may look like flaky graphics rather than a kernel defect.
- Fleet-wide impact becomes more meaningful when multiplied across devices.
- Missing CVSS scoring can delay prioritization if teams rely on it too heavily.
- Mixed kernel branches can create a false sense of uniform protection.
Looking Ahead
The immediate thing to watch is how quickly downstream Linux distributions and OEM kernels absorb the stable fix. In most real deployments, the upstream commit matters less than the version actually shipped by the vendor, so the operational story will depend on backport timing and package rollout rather than publication date alone.It is also worth watching whether similarr in adjacent AMD display paths. The graphics stack is full of connector, stream, and EDID-handling objects, and bugs in one object lifecycle often reveal review targets in neighboring code. That does not mean another flaw is guaranteed, but it does mean maintainers may use this case as a cue to auflows more aggressively.
For defenders, the next practical checkpoint is simple: verify that the kernel you run contains the corrected behavior, test suspend/resume on AMD systems, and treat graphics stability regressions as security-relevant until proven otherwise. That is the best way to turn a small CVE into a broader improvement in fleet hygiene rather than just another line item in an advisory feed.
- Watch for distro advisories that mention the stable backport.
- Confirm whether mobile endpoints already received the fix.
- Test dock/undock and suspend/resume after updates.
- Keep an eye on related amdgpu_dm lifecycle patches.
- Track whether NVD assigns a CVSS score and CWE classification.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center