A newly published Linux kernel CVE is drawing attention for a familiar but dangerous reason: a trusted control path accepted attacker-controlled data without enforcing a hard ceiling. In CVE-2026-31464, the
That is why this bukeeping flaw. The vulnerable path takes a server-supplied count, stores it, and later uses it as a loop bound. In kernel code, that pattern is always a warning sign because a count that is “just metadata” in one function becomes an address calculation in another. The patch changes one line, but the design lesson is bigger: counts derived from external responses must be normalized before they can influence array traversal.
The issue was publicly traced back to a January 2026 mailing-list patch that described the failure as an out-of-bounds read in
For administrators, the headline takeaway is straightforward: this is a narrow driin a privileged storage path and can expose memory from kernel space. That combination makes it worth treating as a real security issue even though the CVSS scoring had not yet been populated in NVD at the time the record surfaced. Microsoft’s advisory page and the NVD entry both show the CVE as newly published, with enrichment still catching up.
The root cause is a classic mismatch between an external length fieldcation size. The discover-targets response includes a
The security impact is also more subtle than a crash. The out-of-bounds bytes are not merely read and discarded; they are later incorporated into follow-up MAD traffic. That means the bug can leak kernel memory back to the VIO server in a structured way, making the disclosure meaningful even if the driver never panics. In other words, the bug crosses from memory safety into information exposure.
The important distinction is that the attacker does not need direct memory access to learn something useful. If a malicious or compromised VIO server can influence the count, it can potenl into echoing memory it should never have seen. That is why this is best understood as a leak vulnerability with a clear trust-boundary failure, not merely a bounds-check bug buried in a driver.
This is also a good example of least-surprise engineering. The driver already knows the maximum number of targets it can handle, and the patch does not ask the rest of the subsystem to tolerate something larger. That matters because security fixes that preserve the subsystem’s original assumptions are easier to backport, easier to verify, and less likely to cause regressions.
There is also a maintenance benefit. A one-line clamp is the sort of fix stable trees can absorb quickly, which matters when the vulnerable path is inside a storage driver used in enterprise Power environments. Narrow patches are usually the ones that travel fastest from upstream into vendo
This is especially concerning in environments where the VIO server is assumed to be trusted infrastructure. If that layer is compromised, the driver becomes an oracle for memory that should never leave the kernel. In practice, that can aid reconnaissance, exposure of pointers or metadata, or even chaining with other bugs that need just a little more knowledge of the memory rage-path bugs deserve extra attention
Storage is not just about availability. It is also about integrity and confidentiality, because storage drivers often move data on behalf of higher-value workloads. A bug in this class can therefore affect databases, virtual machines, and enterprise applications indirectly, even if the vulnerable code is “only” in a driver. That makes triage mo raw patch size might suggest.
The other reason defenders should care is that driver bugs tend to be underestimated by asset inventories. Operators often know what application they run, but not which transport stack or virtualization path the kernel uses underneath. That means a flaw in an adapter client driver can lurk in systems that were never explicitly categorized as storage-security targets.
Enterprise Exposure vs. General Consum is not likely to affect every Linux installation equally. The issue lives in
The operational risk is also amplified by the fvirtualization teams often separate duties. A platform team may assume the virtualization layer is trustworthy, while a security team focuses on the guest OS or application tier. This CVE sits in the seam between those responsibilities, which is where a lot of real-world exposure hides.
The practical consequence for consumers is more indirectily and distribution channels used in enterprise appliances can ship into less visible devices. So while the average laptop user may never touch
The patch also contains useful attribution: the issue was reported by two researchers, and the commit message gives a
For defenders, that means the safest response is not to wait for a final score. If your environment uses the affected driver, the right question is whether the relevant kernel branch includes the clamp. If not, the system should be treated as exposed until proven otherwise.
The broader pattern is that many kernel CVEs are not exotic logic puzzles. They are the result of assuming a field is already safe because it usually is. Over time, that habit creates a large attack surface in exactly the places where the kernel is least toler fields, loop bounds, array indexes, and protocol-derived counters.
It is also a reminder that “read” bugs can still be security bugs. The kernel does not have to overwrite memory to create harm; reading beyond a boundary and exporting the result is enough to expose confidential state. In a security review, that distinction matters a great deal.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
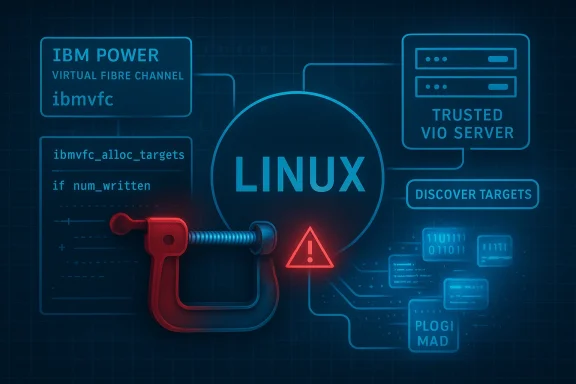
ibmvfc driver can take a num_written value from a VIO server’s discover-targets MAD response and store it in vhost->num_targets without validation, even when that value exceeds max_targets. The result is an out-of-bounds access in ibmvfc_alloc_targets(), and the leaked data can be echoed back to the VIO server in follow-on MADs, turning a bounds bug into a kernel memory disclosure. The upstream fix is simple and correct: clamp the count before storing it. bmvfc` driver sits in an unusual but important part of the Linux ecosystem: Power Systems virtual Fibre Channel. That matters because storage-path bugs are often treated as “just driver issues” until they are shown to cross a trust boundary. Here, the trust boundary is the VIO server, which the kernel expects to behave correctly but which may be malicious or compromised in the threat model described by the CVE record. When that server overstates how many targets were written, the driver does not merely miscount; it later walks beyond the bounds of a DMA-coherent buffer and uses whatever it finds there.That is why this bukeeping flaw. The vulnerable path takes a server-supplied count, stores it, and later uses it as a loop bound. In kernel code, that pattern is always a warning sign because a count that is “just metadata” in one function becomes an address calculation in another. The patch changes one line, but the design lesson is bigger: counts derived from external responses must be normalized before they can influence array traversal.
The issue was publicly traced back to a January 2026 mailing-list patch that described the failure as an out-of-bounds read in
discover_targets, with the fix proposed as clamping the response to the maximum buffer size. The later CVE wording sharpened the impact analysis by explaining that the out-of-bounds content can be embedded in Implicit Logout and PLOGI MADs sent back to the VIO server, which turns the bug into a kernel-memory leak rather than a simple crash candidate.For administrators, the headline takeaway is straightforward: this is a narrow driin a privileged storage path and can expose memory from kernel space. That combination makes it worth treating as a real security issue even though the CVSS scoring had not yet been populated in NVD at the time the record surfaced. Microsoft’s advisory page and the NVD entry both show the CVE as newly published, with enrichment still catching up.
 What Actually Went Wrong
What Actually Went Wrong
The root cause is a classic mismatch between an external length fieldcation size. The discover-targets response includes a num_written value, and the driver accepted it at face value. The code later uses vhost->num_targets as the number of entries to iterate over in ibmvfc_alloc_targets(), but the discovery buffer was only sized for max_targets. If num_written is larger than that limit, the loop steps off the end of the array and begins reading adjacent kernel memory.The data flow problem
This kind of bug is especially easy to miss because the failure is split across functions. One funt, another function trusts the count, and neither function on its own obviously “looks wrong” in a review. That split responsibility is exactly why kernel patches tend to clamp at the first trusted boundary rather than relying on later callers to behave responsibly. The patch in the mailing list does precisely that by replacing direct assignment withmin_t(u32, be32_to_cpu(rsp->num_written), max_targets).The security impact is also more subtle than a crash. The out-of-bounds bytes are not merely read and discarded; they are later incorporated into follow-up MAD traffic. That means the bug can leak kernel memory back to the VIO server in a structured way, making the disclosure meaningful even if the driver never panics. In other words, the bug crosses from memory safety into information exposure.
Why the DMA buffer matters
The discovery buffer is DMA-coherent, which means the kernel and device share an agreed-upon memory region for the exchange. That doessafe by itself; it just makes it accessible to both sides. Once the loop exceeds the number of allocated entries, the driver starts treating unrelated memory as though it were target metadata. This is one of those cases where the words “only a read” are misleading, because the read data is subsequently packaged into outbound protocol messages.The important distinction is that the attacker does not need direct memory access to learn something useful. If a malicious or compromised VIO server can influence the count, it can potenl into echoing memory it should never have seen. That is why this is best understood as a leak vulnerability with a clear trust-boundary failure, not merely a bounds-check bug buried in a driver.
The Patch Is Small, but the Fix Is Right
The upstream fix is minimal: clampnum_written to max_targets before the value is written into vhost->num_targets. In kernel security work, that kind oft kind because it attacks the bug at the point where unsafe data first becomes part of internal state. The patch does not change the protocol, invent a fallback path, or reinterpret the meaning of the response. It simply refuses to let a server claim more targets than the buffer can hold.Why clamping is better than compensating later
Once a bad count is stored, every later consumer has to remember to defend itself. That model is fragile. A single missed caller turns a defensive chain into a liability, and kernel code is full of call paths that evolve over time. By normalizing the count immediately, the patch restores a simple invariant:vhost->num_targets can never exceed the allocated table size.This is also a good example of least-surprise engineering. The driver already knows the maximum number of targets it can handle, and the patch does not ask the rest of the subsystem to tolerate something larger. That matters because security fixes that preserve the subsystem’s original assumptions are easier to backport, easier to verify, and less likely to cause regressions.
A familiar kernel-hardening pattern
The Linux kernel often resolves this class of bug by locking down the first point of trust, not by adding extra checks everywhere else. The CVE’s public description and the mailing-list patch both point to the same philosophy: make the invalid state impossible to retain. That is cleaner than allowing oversize counts into the data model and hoping later code notices.There is also a maintenance benefit. A one-line clamp is the sort of fix stable trees can absorb quickly, which matters when the vulnerable path is inside a storage driver used in enterprise Power environments. Narrow patches are usually the ones that travel fastest from upstream into vendo
Why the Leak Matters to Defenders
It is tempting to downplay a memory leak if there is no immediate code execution angle. That would be a mistake here. Kernel memory disclosures can still be valuable to attackers because they reveal allocator layout, adjacent object contents, or other sensitive state that can support follow-on exploitation. In a privileged storage path, even a modest leak is enough to undermine confidence in isolation.Information disclosure is not harmless
The CVE text specifically says the out-of-bounds data is embedded in Implicit Logout and PLOGI MADs sent back to the VIO server. That means the leak is not theoretical and not confined to local diagnostics; it can cross the virtualized storage boundary back to the peer that triggered the overlong count. For a lane component, that is exactly the kind of visibility an attacker wants.This is especially concerning in environments where the VIO server is assumed to be trusted infrastructure. If that layer is compromised, the driver becomes an oracle for memory that should never leave the kernel. In practice, that can aid reconnaissance, exposure of pointers or metadata, or even chaining with other bugs that need just a little more knowledge of the memory rage-path bugs deserve extra attention
Storage is not just about availability. It is also about integrity and confidentiality, because storage drivers often move data on behalf of higher-value workloads. A bug in this class can therefore affect databases, virtual machines, and enterprise applications indirectly, even if the vulnerable code is “only” in a driver. That makes triage mo raw patch size might suggest.
The other reason defenders should care is that driver bugs tend to be underestimated by asset inventories. Operators often know what application they run, but not which transport stack or virtualization path the kernel uses underneath. That means a flaw in an adapter client driver can lurk in systems that were never explicitly categorized as storage-security targets.
Enterprise Exposure vs. General Consum is not likely to affect every Linux installation equally. The issue lives in ibmvfc, which narrows the practical exposure to systems using the IBM Power virtual Fibre Channel stack. That immediately makes this a specialized enterprise problem rather than a universal desktop issue. But specialized does not mean unimportant.
Enterprise impact
Enterprises runniucture, virtualization layers, and storage-connected workloads should care most. Those environments are exactly where a VIO server is part of the control plane and where a storage-path leak can have outsized consequences. If the VIO server is compromised or misbehaving, the kernel bug becomes a disclosure primitive inside a highly trusted channel.The operational risk is also amplified by the fvirtualization teams often separate duties. A platform team may assume the virtualization layer is trustworthy, while a security team focuses on the guest OS or application tier. This CVE sits in the seam between those responsibilities, which is where a lot of real-world exposure hides.
Consumer impact
For most consumer Linux users, the direct risk is likely low because they are not running this specifiific configuration. That said, “consumer” is not the same thing as “safe,” especially in environments where Linux underpins small appliances or niche infrastructure. The broader lesson is that kernel CVEs can matter far beyond their apparent footprint when they land in shared or embedded platforms.The practical consequence for consumers is more indirectily and distribution channels used in enterprise appliances can ship into less visible devices. So while the average laptop user may never touch
ibmvfc, the patch still matters in the broader ecosystem of vendor kernels, appliance firmware, and managed infrastructure.What the Mailing-List Patch Tells Us
The mailing-list discussion is useful because it shows the issue was recognized before the CVE record appeared. That often meanon a stable-tracking path and has a clearer paper trail than many disclosures do. Here, the patch explicitly describes the bug as an out-of-bounds read indiscover_targets, notes that num_written > max_targets is the trigger, and states that clamping to the maximum buffer size is the proper correction.The reviewer-friendly part
Kernel m that are easy to reason about, and this one qualifies. It preserves the original logic, does not create a new policy layer, and keeps the patch tiny. That is important because stable-tree acceptance often depends on whether the change is clearly safer than the buggy behavior without introducing new ambiguities.The patch also contains useful attribution: the issue was reported by two researchers, and the commit message gives a
Fixes tag pointing back to the original ibmvfc driver introduction. That is the sort of detail that improves downstream traceability and helps distributions decide whether their backports line up with upstream intent.Why the commit trail matters
A strong commit trail matters because not all CVE pages are equally useful on day one. NVD had not yet assigned a full score when the record was published, so the most concrete technical guidance came from the kernel patch itself. That is a common pattern with newly disclosed Linux issues: the upstream fix tells you what the bug is, while the CVE record catches up on scoring and normalization later.For defenders, that means the safest response is not to wait for a final score. If your environment uses the affected driver, the right question is whether the relevant kernel branch includes the clamp. If not, the system should be treated as exposed until proven otherwise.
Historical Context: Why This Kind of Bug Keeps Happening
Count-handling bugs are a recurring theme in kernel security because the kernel constantly translates external messages into internal data structures. Every time a device, server, or peer reports how many items it produced, the kernel has to decide whether that number is trustworthy,ent with the memory already allocated. When any of those checks are missing, a bad count can become a memory safety problem.The trust-boundary lesson
This is especially true in virtualized and paravirtualized environments, where the kernel is often talking to another privileged component ra hardware device. The VIO server is not just another input source; it is part of the control fabric. That makes oversize responses more dangerous, because the kernel’s assumptions about honesty are often stronger than they should be.The broader pattern is that many kernel CVEs are not exotic logic puzzles. They are the result of assuming a field is already safe because it usually is. Over time, that habit creates a large attack surface in exactly the places where the kernel is least toler fields, loop bounds, array indexes, and protocol-derived counters.
Why this one is a good example
CVE-2026-31464 is a clean illustration because the fix is proportionate to the bug. It does not overcorrect, and it does not change the subsystem’s meaning. It just restores the missing invariant that the count must never exceed the array size. That is the kind of defect kernel developers want to catch early and reviewersurgically.It is also a reminder that “read” bugs can still be security bugs. The kernel does not have to overwrite memory to create harm; reading beyond a boundary and exporting the result is enough to expose confidential state. In a security review, that distinction matters a great deal.
Strengths and Opportunities
The good news is that this is a well-scoped issue with a well-scoped fix. That makes it easier for vendors to backport, easier for administrators to validate, and easier for security teams to explain without overstating the problem. It also provides a useful reminder that storage and virtualization paths deserve the same scrutiny as more obviously exposed network services.- The fix is small and surgical, which lowers regression risk.
- The vulnerable state is easy to understand: an oversize count becomes a loop bound.
- The patch restores a clean invariant by capping
num_targetsatmax_targets. - The issue is narrow in scope, so organizations can target remediation precisely.
- The leak path is visible in thich helps defenders reason about impact.
- The upstream mailing-list history suggests the bug was understood before publication, which helps stable backporting.
- The fix reinforces a broader best practice: never let externally supplied counts reach internal loops unbounded.
Risks and Concerns
The main concern is that this looks like a small driver bug but behaves like a real confidentiality issue. If the VIO server is malicious or compromised, the kernel can be induced to leak memory that should have remained private. That means the bug is not just about correctness; it is about trust in a contromised VIO server can influence the bug directly, so the trust boundary is already crossed.- Out-of-bounds reads may expose data that is later packaged into outbound MADs.
- The issue affeage path, which can amplify operational impact.
- Vendor backports may lag behind upstream pubxposure.
- Asset inventories may miss the affected path if teams do not track Power virtualization dependencies closely enough.
- A “no CVSS yet” status can cause under-prioritization if teams wait for scoring instead of reviewing the code path.
- Small leaks are easy to dismiss, but they can still support follow-on exploitation or reconnaissance.
Looking Ahead
The immediate question is how quickly the fix propagates into supported kernel streams and vendor-maintained branches. Upstream code now shows the clamp, but most organizations do not run raw upstream trees; they run distribution kernels, applianc backports. In practice, that means exposure lasts until the patch lands in the build your environment second thing to watch is whether vendors issue clear advisories mapping their packatched kernel commits. That matters because a kernel CVE can be easy to misunderstand em exists across multiple flavors of Power and enterprise Linux packaging. Administrators need version-to-fix clarity, not just a CVE number and a commit hash.- Confirm whether your kernel includes the clamp for `nuwhether your environment uses IBM Power virtual Fibre Channel paths.
- Validate vendor backports rather than assuming equals remediation.
- Review whether VIO server trust assumptions are documented and enforced.
- Prioritiage traffic crosses a privileged virtualization boundary.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center