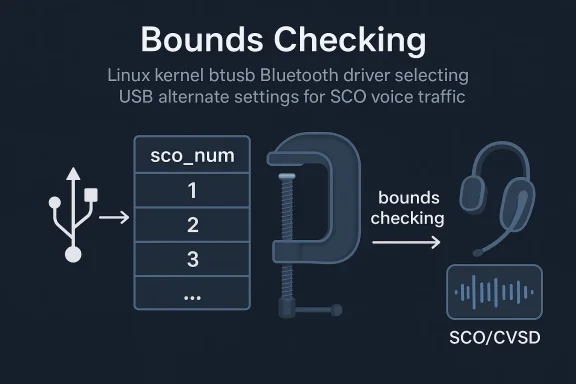
CVE-2026-31497 is a small Linux kernel Bluetooth bug with outsized meaning for maintainers and downstream vendors. The issue sits in the btusb driver, where the kernel maps the number of active SCO links to USB alternate settings through a fixed lookup table, but failed to clamp the index before use. In practical terms, the fix ensures the driver keeps selecting the highest supported alternate setting without reading past the end of the array, a classic defensive correction in a path that handles voice traffic and device state tooth vulnerabilities in the Linux kernel often look deceptively narrow because they are buried inside subsystem-specific logic rather than broad, user-facing features. That is part of what makes them easy to underestimate. The btusb driver is the USB transport layer for a wide range of Bluetooth hardware, and its job is to coordinate low-level device behavior with higher-level Bluetooth connection state. A bug in that layer may not splash across a desktop in an obvious way, but it can still matter to systems that rely on Bluetooth headsets, hands-free calling, embedded devices, and integrated radio modules.
The specific weakness here lives in the logic that handles SCO links, which are used for synchronous voice traffic. When CVSD voice settings are active in transparent mode, the driver chooses a USB alternate setting from a small table. The vulnerability arose because the code used
That kind of bug isngineering. It is not necessarily a dramatic memory corruption primitive, but it is still a trust-boundary error. Any time a dynamic runtime count is translated into a table lookup, there must be a guardrail. Without one, the code may read unintended memory, select an invalid configuration, or drift into undefined behavior. The kernel community tends to treat these mistakes seriously because they are exactly the sort of edge-case failures that can survive testing for a long time.
The CVE record itself reflects that ecosystem. Microsoft’s Security Update Guide entry mirrors the Linux kernel description and points back to multiple stable commit references on kernel.org, reinforcing that the issue is already in the upstream remediation pipeline rather than a speculative report with no fix attached. The Linux kernel documentation also explpically assigned after a fix is available and applied to a stable tree, which helps explain why these records often appear alongside backports rather than long before them
Not every kernel bug looks like an exploit. In practice, the Linux CVE process is intentionally broad because even “small” correctness failures can become security-relevant once they involve out-of-bounds access, undefined behavior, or state that influences external device handling. The kernel’s own documentation makes clear that many CVEs are issued for bug fixes once a security impact is recognized, even if the exploitability is not fully proven at the time
That matters because defenders sometimes assume a CVE must mean remote compromise or a headline-grabbing attack. In reality, kernel CVEs often capture narrower flaws that are still worth fixing quickly. A Bluetooth driver reading past the end of a lookup table is exactly the kind of issue that may be difficult to weaponize but still deserves prompt attention, especially in a core subsystem used across laptops, desktops, and embedded Linux systems.
This is the kind of issue that can sit unnoticed because it depends on a specific combination of hardware behavior and traffic mode. The advisory says the bug matters when CVSD traffic uses transparent voice settings, which narrows the exposure substantially. That means the vulnerability is not a universal Bluetooth failure; it is a constrained path inside a constrained path. Still, narrow bugs are often the ones that survive longest in production, because they are easy to miss in ordinary testing.
There is also an important operational dimension to the fix. By clamping the table index, the driver continues to choose the highest supported alternate setting when the active SCO count rises above three. In other words, the patch preserves the intended scaling behavior instead of introducing a new fallback rule or a disruptive reconfiguration. That is a hallmark of a good kernel fix: change as little as possible, but enough to restore safety.
Microsoft’s update guide currently shows no NVD-enriched CVSS score for the CVE, which is common early in the disclosure cycle. The record is still useful even without a finalized severity number because the code path and the correction are clear enough to guide triage. In kernel security, a precise bug description is often more actionable than an abstract score, especially when the underlying behavior is easy to reason about fromf
The btusb fix is the sort of patch that maintainers like because it is clearly correct, narrowly scoped, and compatible with stable backporting. The stable kernel rules emphasize that accepted patches should already exist in mainline, be obviously correct, and address a real bug or security issue. This patch fits that model well, which is one reason CVE records like this often propagate quickly into vendor branches
The patch changes the logic so the code clamps the value before indexing. That means once the connection count exceeds the last table entry, the driver simply reuses the highest supported alternate setting instead of trying to read beyond the available entries. In security engineering, that is a textbook example of converting implicit trust into explicit bounds checking.
This is not just about avoiding a crash. Out-of-bounds reads can expose adjacent memory, produce unpredictable behavior, or destabilize state machines in ways that are very hard to reproduce. Even if the practical risk here is limited by the specific driver path, the fix removes an unnecessary gamble from a code section that should never have depended on unchecked arithmetic.
In Bluetooth driver code, those mistakes can be particularly annoying because the visible symptom may be indirect. You might see flaky voice behavior, negotiation oddities, or device-specific inconsistencies rather than a neat kernel panic. That makes a small defensive fix like this more important than it first appears.
The three practical implications are straightforward:
Enterprise exposure is more nuanced. Managed Windows endpoints that use Linux-based components indirectly, embedded Linux products, thin clients, or devices with integrated Bluetooth stacks may all inherit the problem depending on their kernel line and backport status. In those environments, the question is not whether every machine is vulnerable, but whether any deployed image includes the affected Bluetooth driver version and usage pattern.
This is also a reminder that Bluetooth security is not just about pairing, authentication, or radio-layer attacks. Driver bugs can matter just as much because they sit below the user interface and often below the troubleshooting tools administrators rely on. When the kernel mismanages device state, the failure can look like a flaky peripheral, not a security issue.
The distinction matters because enterprise teams are often juggling drivers, firmware, OEM customization, and compliance timelines. A tiny kernel fix can be operationally significant if it prevents recurring service tickets or avoids a support escalation chain that masks the real root cause.
Linux kernel CVEs also require careful interpretation because the CVE assignment is tied to the existence of a fix and the stable kernel process, not to a universally exploitable attack scenario. The kernel documentation explicitly notes that applicability depends on how a system uses Linux and which portions of the tree are actually active on that machine. That is especially important here, because only systems using the affected Bluetooth path under the relevant voice settings are likely to care.
A sensible triage response should focus on whether the affected kernel branch is in use and whether the vendor has already backported the patch. In many Linux environments, the real answer will come from distribution advisories or vendor kernel changelogs, not from version numbers alone. Backport status matters more than headline version strings.
The reference list attached to the CVE shows multiple kernel.org stable commits, which suggestsbeen propagated through the normal upstream-to-stable path. In Linux land, that is often the most important clue for defenders: if the commit has already landed in a stable branch, your vendor may be close behind or may already have the fix in a downstream kernel package.
This also illustrates why kernel patch discipline matters. A tiny out-of-bounds read can be corrected cleanly because the underlying logic is simple and isolated. If the fix had required broad refactoring, stable backports would be slower and riskier. Instead, the narrow scope makes the patch easier to trust and easier to ship.
The practical benefits are obvious:
There is also a deeper lesson about voice-oriented code paths. SCO and CVSD handling often receive less attention than newer, flashier wireless features, but they remain core to hands-free audio and call quality. When those paths fail, the result may not be a dramatic exploit; it may be a subtle reliability degradation that erodes trust in the platform.
From a software assurance perspective, this CVE is another reminder that memory safety isn’t only about writes. Reads can be just as dangerous when they cross a boundary, because they can leak data, destabilize logic, or simply expose the fact that the code was making an assumption it could not actually justify. That is why out-of-bounds reads are still treated seriously in kernel maintenance.
The design principles are boring, but boring is good here:
The hardest part may be that Bluetooth issues are often managed indirectly. OEMs package kernel updates, distributions backport fixes on their own schedules, and embedded vendors sometimes ship heavily customized trees. That means two devices with the same nominal kernel version may not have the same underlying fix set. Version parity is not fix parity.
It is also smart to test voice workflows after updating. Even though the patch is small, Bluetooth audio paths are notoriously sensitive to change. A good rollout sequence will prove that the driver still behaves correctly under normal headsets, call audio, and any device classes that rely on SCO transport.
It will also be worth watching whether related Bluetooth code paths get similar scrutiny. Simple bounds bugs often reveal neighboring assumptions, especially in drivers that translate hardware state into arrays, alternate settings, or protocol negotiation decisions. One fix rarely ends the audit story; it often starts it.
In the near term, the most useful questions are practical ones:
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
The specific weakness here lives in the logic that handles SCO links, which are used for synchronous voice traffic. When CVSD voice settings are active in transparent mode, the driver chooses a USB alternate setting from a small table. The vulnerability arose because the code used
data->sco_num - 1 directly as an index, even though sco_num is derived from hci_conn_num and can exceed the number of table entries. The fix is simple: cap the index at the final valid table entry before dereferencing itThat kind of bug isngineering. It is not necessarily a dramatic memory corruption primitive, but it is still a trust-boundary error. Any time a dynamic runtime count is translated into a table lookup, there must be a guardrail. Without one, the code may read unintended memory, select an invalid configuration, or drift into undefined behavior. The kernel community tends to treat these mistakes seriously because they are exactly the sort of edge-case failures that can survive testing for a long time.
The CVE record itself reflects that ecosystem. Microsoft’s Security Update Guide entry mirrors the Linux kernel description and points back to multiple stable commit references on kernel.org, reinforcing that the issue is already in the upstream remediation pipeline rather than a speculative report with no fix attached. The Linux kernel documentation also explpically assigned after a fix is available and applied to a stable tree, which helps explain why these records often appear alongside backports rather than long before them
 Why this kind of bug gets a CVE
Why this kind of bug gets a CVE
Not every kernel bug looks like an exploit. In practice, the Linux CVE process is intentionally broad because even “small” correctness failures can become security-relevant once they involve out-of-bounds access, undefined behavior, or state that influences external device handling. The kernel’s own documentation makes clear that many CVEs are issued for bug fixes once a security impact is recognized, even if the exploitability is not fully proven at the timeThat matters because defenders sometimes assume a CVE must mean remote compromise or a headline-grabbing attack. In reality, kernel CVEs often capture narrower flaws that are still worth fixing quickly. A Bluetooth driver reading past the end of a lookup table is exactly the kind of issue that may be difficult to weaponize but still deserves prompt attention, especially in a core subsystem used across laptops, desktops, and embedded Linux systems.
Overview
The heart of the bug is arithmetic, not drama. The driver’s altsetting table has only three entries, but the selection logic could use a raw connection count that exceeds that range. The result is an out-of-bounds table access risk when SCO link counts grow beyond the assumptions baked into the code. The patch does not change the driver’s intended behavior; it simply forces the lookup to stop at the last supported entry so the driver degrades gracefuing off the table edgeThis is the kind of issue that can sit unnoticed because it depends on a specific combination of hardware behavior and traffic mode. The advisory says the bug matters when CVSD traffic uses transparent voice settings, which narrows the exposure substantially. That means the vulnerability is not a universal Bluetooth failure; it is a constrained path inside a constrained path. Still, narrow bugs are often the ones that survive longest in production, because they are easy to miss in ordinary testing.
There is also an important operational dimension to the fix. By clamping the table index, the driver continues to choose the highest supported alternate setting when the active SCO count rises above three. In other words, the patch preserves the intended scaling behavior instead of introducing a new fallback rule or a disruptive reconfiguration. That is a hallmark of a good kernel fix: change as little as possible, but enough to restore safety.
Microsoft’s update guide currently shows no NVD-enriched CVSS score for the CVE, which is common early in the disclosure cycle. The record is still useful even without a finalized severity number because the code path and the correction are clear enough to guide triage. In kernel security, a precise bug description is often more actionable than an abstract score, especially when the underlying behavior is easy to reason about fromf
The Linux kernel angle
Linux kernel Bluetooth code sits at an awkward intersection of hardware variability and user expectations. Different adapters expose different capabilities, device firmware may behave inconsistently, and the driver still has to synthesize all of that into stable behavior. That is why indexing bugs are common in low-level drivers: the software is constantly translating unstable external state into fixed internal assumptions.The btusb fix is the sort of patch that maintainers like because it is clearly correct, narrowly scoped, and compatible with stable backporting. The stable kernel rules emphasize that accepted patches should already exist in mainline, be obviously correct, and address a real bug or security issue. This patch fits that model well, which is one reason CVE records like this often propagate quickly into vendor branches
Technical Root Cause
The root cause is a mismatch between the number of active SCO links and the size of the alternate-setting table. The lookup useddata->sco_num - 1 directly, which assumes the active link count can never outgrow the table’s three supported entries. That assumption is fragile because data->sco_num com`, not from a hard-coded constant tied to the array lengthThe patch changes the logic so the code clamps the value before indexing. That means once the connection count exceeds the last table entry, the driver simply reuses the highest supported alternate setting instead of trying to read beyond the available entries. In security engineering, that is a textbook example of converting implicit trust into explicit bounds checking.
This is not just about avoiding a crash. Out-of-bounds reads can expose adjacent memory, produce unpredictable behavior, or destabilize state machines in ways that are very hard to reproduce. Even if the practical risk here is limited by the specific driver path, the fix removes an unnecessary gamble from a code section that should never have depended on unchecked arithmetic.
Why table clamping matters
A fixed lookup table is only safe when the input domain is strictly controlled. When the input comes from runtime state, the code must treat the table size as the authority. Anything else invites off-by-one errors, stale assumptions, and hard-to-debug edge cases.In Bluetooth driver code, those mistakes can be particularly annoying because the visible symptom may be indirect. You might see flaky voice behavior, negotiation oddities, or device-specific inconsistencies rather than a neat kernel panic. That makes a small defensive fix like this more important than it first appears.
The three practical implications are straightforward:
- The driver no longer trusts
sco_numto stay within the table’s bounds. - The code preserves the maximum supported behavior for higher SCO counts.
- The patch reduces the chance of undefined memory access in a voice-handling path.
Impact on Devices and Deployments
For most consumers, the practical impact is likely limited. Many desktop and laptop users will never notice the bug directly, especially if they are not using the affected voice path or their hardware never exercises the edge case. That said, limited consumer exposure does not mean no relevance; Bluetooth bugs can still affect audio reliability, headset behavior, and device-specific quirks that users blame on firmware or pairing issues.Enterprise exposure is more nuanced. Managed Windows endpoints that use Linux-based components indirectly, embedded Linux products, thin clients, or devices with integrated Bluetooth stacks may all inherit the problem depending on their kernel line and backport status. In those environments, the question is not whether every machine is vulnerable, but whether any deployed image includes the affected Bluetooth driver version and usage pattern.
This is also a reminder that Bluetooth security is not just about pairing, authentication, or radio-layer attacks. Driver bugs can matter just as much because they sit below the user interface and often below the troubleshooting tools administrators rely on. When the kernel mismanages device state, the failure can look like a flaky peripheral, not a security issue.
Consumer versus enterprise risk
Consumers usually experience Bluetooth issues as nuisance problems: a headset that drops audio, a call device that behaves oddly, or a connection that will not quite settle into the right mode. In a business fleet, the same underlying bug can create support noise, wasted troubleshooting time, and confidence loss in a device class that users expect to “just work.”The distinction matters because enterprise teams are often juggling drivers, firmware, OEM customization, and compliance timelines. A tiny kernel fix can be operationally significant if it prevents recurring service tickets or avoids a support escalation chain that masks the real root cause.
Severity and Triage Considerations
At the time reflected in the record, NVD had not yet published a formal CVSS score for the issue, and Microsoft’s guide likewise showed no finalized severity metadata. That does not make the vulnerability unimportant; it just means the scoyet caught up with the disclosure stream. For defenders, the absence of a score should never be read as the absence of a fixable bug.Linux kernel CVEs also require careful interpretation because the CVE assignment is tied to the existence of a fix and the stable kernel process, not to a universally exploitable attack scenario. The kernel documentation explicitly notes that applicability depends on how a system uses Linux and which portions of the tree are actually active on that machine. That is especially important here, because only systems using the affected Bluetooth path under the relevant voice settings are likely to care.
A sensible triage response should focus on whether the affected kernel branch is in use and whether the vendor has already backported the patch. In many Linux environments, the real answer will come from distribution advisories or vendor kernel changelogs, not from version numbers alone. Backport status matters more than headline version strings.
What administrators should verify
A practical verification sequence would look something like this:- Confirm whether the device actually uses the Linux btusb Bluetooth driver path.
- Check whether the system relies on SCO voice traffic and transparent CVSD settings.
- Determine whether the vendor kernel already includes the clamping fix.
- Validate that any Bluetooth-dependent voice workflows still behave normally after update.
- Treat unsupported or custom kernels as higher-risk until proven otherwise.
Upstream Fix and Backporting
The upstream fix is refreshingly straightforward: clamp the index to the final table entry before dereferencingalts. That kind of surgical correction is ideal for stable trees because it addresses the bug without redesigning the subsystem or altering user-visible policy. It is also a good sign when the patch can be expressed in a sentence aecting the highest supported alternate setting without reading past the array”*The reference list attached to the CVE shows multiple kernel.org stable commits, which suggestsbeen propagated through the normal upstream-to-stable path. In Linux land, that is often the most important clue for defenders: if the commit has already landed in a stable branch, your vendor may be close behind or may already have the fix in a downstream kernel package.
This also illustrates why kernel patch discipline matters. A tiny out-of-bounds read can be corrected cleanly because the underlying logic is simple and isolated. If the fix had required broad refactoring, stable backports would be slower and riskier. Instead, the narrow scope makes the patch easier to trust and easier to ship.
Why narrow fixes are preferred
Kernel maintainers usually prefer fixes that do one thing well. In this case, the driver still does what it was meant to do, but it now enforces the bounds of its own table. That is a better outcome than adding layers of workaround logic or changing the voice-selection algorithm more broadly.The practical benefits are obvious:
- Lower regression risk.
- Easier stable backporting.
- Minimal impact on supported hardware behavior.
- Clearer code intent for future maintainers.
- Less chance of hidden side effects in adjacent Bluetooth logic.
Broader Bluetooth Security Lessons
Bluetooth bugs have a tendency to live in the gray space between hardware, protocol stacks, and device-specific behavior. That makes them difficult to generalize about, which is precisely why simple guards like this are worth highlighting. If a driver accepts a count from the runtime environment, it should never trust that count to be safe for an array without checking the table size first.There is also a deeper lesson about voice-oriented code paths. SCO and CVSD handling often receive less attention than newer, flashier wireless features, but they remain core to hands-free audio and call quality. When those paths fail, the result may not be a dramatic exploit; it may be a subtle reliability degradation that erodes trust in the platform.
From a software assurance perspective, this CVE is another reminder that memory safety isn’t only about writes. Reads can be just as dangerous when they cross a boundary, because they can leak data, destabilize logic, or simply expose the fact that the code was making an assumption it could not actually justify. That is why out-of-bounds reads are still treated seriously in kernel maintenance.
Lessons for driver authors
Driver authors can take a few concrete lessons from this case. First, table sizes should be treated as hard constraints, not soft hints. Second, runtime counters should be capped before they influence memory access. Third, when a path depends on a device-specific feature like transparent voice settings, the safest code is the code that assumes the least.The design principles are boring, but boring is good here:
- Bound all dynamic indices.
- Prefer explicit minimum and maximum checks.
- Avoid letting hardware state drive unchecked array access.
- Keep fallback behavior predictable.
- Make the “safe” path the default path.
Operational Response for Fleet Owners
For fleet operators, the right response is not panic; it is inventory. Determine which systems actually run kernels that include the affected Bluetooth code and whether those systems use the voice mode implicated by the advisory. If the answer is no, the issue may be a non-event for that branch of the fleet. If the answer is yes, prioritize patch validation on the affected image line.The hardest part may be that Bluetooth issues are often managed indirectly. OEMs package kernel updates, distributions backport fixes on their own schedules, and embedded vendors sometimes ship heavily customized trees. That means two devices with the same nominal kernel version may not have the same underlying fix set. Version parity is not fix parity.
It is also smart to test voice workflows after updating. Even though the patch is small, Bluetooth audio paths are notoriously sensitive to change. A good rollout sequence will prove that the driver still behaves correctly under normal headsets, call audio, and any device classes that rely on SCO transport.
A practical rollout checklist
- Identify systems that actually use the affected Bluetooth stack.
- Verify vendor backports, not just upstream version numbers.
- Test hands-free audio and call workflows after patching.
- Keep an eye on regression reports from device users.
- Document which kernel build first included the fix.
Strengths and Opportunities
This CVE is a good example of a tight kernel fix that improves safety without changing the broader architecture. It is easy to understand, easy to backport, and likely easy to validate in controlled testing. More importantly, it reinforces a habit that every low-level driver should already be following: never let a runtime count outrun a table boundary.- The fix is narrowly scoped and low-risk.
- It preserves the driver’s intended top-end behavior.
- It reduces the chance of out-of-bounds reads.
- It should backport cleanly into stable kernels.
- It is easy for maintainers to audit.
- It improves robustness in a voice-handling path.
- It demonstrates good defensive kernel coding practice.
Risks and Concerns
The biggest risk here is not necessarily dramatic exploitation; it is complacency. Small Bluetooth CVEs can be dismissed as obscure, and that often leads to slow remediation in fleets that assume the issue will not affect them. Another risk is patch confusion, where administrators assume an upstream fix means their vendor kernel has already inherited it when that may not yet be true.- The bug may be underestimated because it is narrow.
- Vendor backports may lag behind upstream fixes.
- Fleet owners may not realize they use the affected path.
- Bluetooth regressions can be hard to diagnose after patching.
- Custom kernels may miss the stable fix entirely.
- Support teams may misattribute symptoms to hardware.
- Edge-case issues often remain latent until specific devices appear.
Looking Ahead
The main thing to watch now is downstream adoption. Because the fix is small and clean, it should move through distribution kernels and vendor trees relatively quickly, but quickly still means different things in different servicing ecosystems. Enterprise teams should verify the exact kernel build they are running rather than assuming the issue has vanished because a security bulletin exists.It will also be worth watching whether related Bluetooth code paths get similar scrutiny. Simple bounds bugs often reveal neighboring assumptions, especially in drivers that translate hardware state into arrays, alternate settings, or protocol negotiation decisions. One fix rarely ends the audit story; it often starts it.
In the near term, the most useful questions are practical ones:
- Has the vendor kernel already picked up the clamp fix?
- Are there any Bluetooth voice regressions after deployment?
- Do any custom or embedded builds still expose the old lookup behavior?
- Are similar table-based paths elsewhere in the Bluetooth stack being reviewed?
- Can patch validation be folded into existing Bluetooth QA routines?
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center