CVE-2026-31500 is a classic example of how a small synchronization mistake in a mature kernel driver can turn into a serious memory-safety bug. The flaw sits in the Linux Bluetooth Intel path, where
Bluetooth support in the Linux kernel is built on top of a fairly intricate command-and-response framework. Intel’s Bluetooth transport code is especially sensitive because it has to coordinate controller resets, firmware recovery, shutdown, and exception reporting while the hardware may already be in an unstable state. That means the code is not just moving packets; it is orchestrating state transitions under pressure, where ordering matters as much as correctness.
The vulnerable path is in
The result is not merely a theoretical race. The published trace shows a data-race warning in
The broader context also matters. Bluetooth drivers often sit at the edge of user experience and low-level hardware control, which makes their failure modes frustratingly ambiguous. A Bluetooth error path may look like a routine recovery helper, but if it shares state with device teardown, it can become a crash trigger during what appears to be normal disconnect or shutdown activity. That is why this CVE belongs in the same class of “small lock, big consequence” kernel issues that can remain hidden until timing aligns just badly enough.
The vulnerability description makes the failure mode clear. While
Why
The kernel’s synchronous HCI command helpers are not standalone utility calls. They depend on shared request bookkeeping, and that bookkeeping must not be manipulated concurrently. By wrapping the whole recovery sequence in
This is exactly the kind of fix that kernel maintainers prefer for concurrency bugs: tighten the critical section, do not redesign the subsystem. It is smaller, easier to audit, and less likely to break unrelated Bluetooth behavior. It also aligns the hardware-error path with the rest of the synchronous HCI command issuers, which is the real consistency gap at the heart of the issue.
Key technical points:
Because both paths mutate the same request/response state, the race can unfold in a narrow but lethal window. One thread may publish a response buffer and expect it to remain valid until its synchronous exchange completes. Another may tear the device down, free the response skb, and invalidate the memory underneath the still-running error handler. That is the textbook shape of a use-after-free in a heavily concurrent kernel subsystem.
In this case, the shutdown path is not just ending the lifecycle of the adapter; it is also participating in synchronous command exchange. That means it must obey the same serialization rules as any other synchronous HCI issuer. If it does not, it can invalidate shared request state while another path is mid-flight.
The practical implications are easy to miss:
The KASAN report is even more concrete. It points to a slab-use-after-free in
In practical terms, this kind of bug can be hard for users to reproduce manually. The race depends on timing, device state, and the precise overlap between hardware error handling and device close. But once discovered, the fix is usually straightforward because the kernel’s locking architecture already describes the intended serialization boundary.
The immediate impact is stability first and security second, at least in the published record. A slab-use-after-free can crash the kernel or trigger unpredictable behavior, and in some cases memory corruption bugs can later be chained into more serious exploitation paths. The CVE entry does not assign a CVSS score yet, but the absence of a score should not be mistaken for a lack of urgency; it usually means the record is still being enriched
For enterprises, the story is more serious because the same laptop or endpoint may be part of a managed fleet where sudden reboots, device instability, and support incidents all have operational cost. Bluetooth is often treated as peripheral, but in modern managed environments it can be tied to headsets, peripherals, conferencing, and docking workflows. Peripheral does not mean unimportant when a bug can take down the kernel.
Important operational consequences:
That kind of patch is often a good sign. Broad refactors in kernel drivers can introduce as many problems as they solve, especially in timing-sensitive code. By contrast, a focused lock fix is easier to reason about and easier to backport across supported kernel lines. It also indicates that maintainers understood the issue as a coordination failure rather than a deeper protocol mismatch.
That consistency matters more than it might sound. Kernel subsystems tend to accumulate invisible contracts over time. Once one path starts bypassing a lock, future maintainers may infer the wrong concurrency model and build on unstable assumptions. Restoring the lock closes that door.
The fix also hints at a broader maintenance principle:
That scrutiny is healthy. Bluetooth combines hardware quirks, asynchronous events, and driver-specific recovery behavior in a way that naturally breeds concurrency bugs. A driver may be perfectly correct under steady-state use and still fail under suspend/resume, disconnect, or firmware-recovery timing. That is why Bluetooth issues often look minor in isolation but collectively indicate a broad attack surface.
Some practical takeaways:
The most practical response is to inventory Intel Bluetooth hardware, check the running kernel lineage, and review vendor advisories for backported fixes. Because this is a concurrency bug, ordinary usage testing may not reveal it. Administrators should prioritize systems that rely on Bluetooth for peripherals, mobile workflows, or enterprise endpoint management, especially if those systems also see frequent sleep, wake, or device disconnect cycles.
The broader opportunity is that this CVE reinforces good maintenance habits around teardown serialization and skb lifetime management. Kernel teams can use it as a reminder to audit other recovery paths that touch shared request state.
There is also the usual operational risk that endpoint teams will underestimate a Bluetooth bug because it sounds peripheral. In practice, kernel instability on mobile systems and managed laptops can become a support burden very quickly. Small-sounding driver bugs often have an outsized effect when they occur across a fleet.
It will also be worth watching whether additional Bluetooth-related kernel reports surface in the same Intel code family. When one driver path shows a synchronization flaw, maintainers often review adjacent paths for similar assumptions. That can produce a small wave of follow-up hardening, which is often a healthy sign that the subsystem is being cleaned up rather than merely patched.
What to monitor next:
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
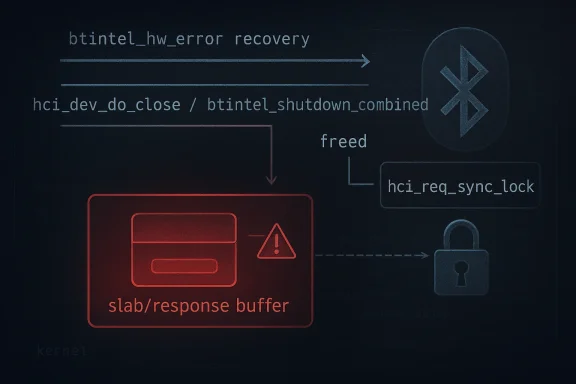
btintel_hw_error() can race with device shutdown logic and end up touching a response buffer after it has already been freed. The fix is straightforward in concept but important in practice: serialize the recovery path with hci_req_sync_lock() so that synchronous HCI command issuers cannot collide. The vulnerability was published on April 22, 2026, and the upstream record describes both a data race and a KASAN-detected slab use-after-free in the affected recovery sequence
 Background
Background
Bluetooth support in the Linux kernel is built on top of a fairly intricate command-and-response framework. Intel’s Bluetooth transport code is especially sensitive because it has to coordinate controller resets, firmware recovery, shutdown, and exception reporting while the hardware may already be in an unstable state. That means the code is not just moving packets; it is orchestrating state transitions under pressure, where ordering matters as much as correctness.The vulnerable path is in
btintel_hw_error(), which issues two synchronous HCI commands: a reset and an Intel exception-information retrieval step. According to the CVE record, those calls were made without holding hci_req_sync_lock(), even though the shutdown path hci_dev_do_close() -> btintel_shutdown_combined() also performs synchronous HCI work under that same lock. In kernel terms, that creates a dangerous overlap in ownership and lifetime management for hdev->req_status and hdev->req_rspThe result is not merely a theoretical race. The published trace shows a data-race warning in
__hci_cmd_sync_sk and then a KASAN report for a slab-use-after-free in sk_skb_reason_drop() while the hardware-error worker is still running. That combination is a strong signal that the bug is rooted in a response skb being freed on one path while another path still believes it is valid. In kernel debugging, that is the kind of evidence that usually moves a bug from “maybe unstable” to “definitely memory unsafe”The broader context also matters. Bluetooth drivers often sit at the edge of user experience and low-level hardware control, which makes their failure modes frustratingly ambiguous. A Bluetooth error path may look like a routine recovery helper, but if it shares state with device teardown, it can become a crash trigger during what appears to be normal disconnect or shutdown activity. That is why this CVE belongs in the same class of “small lock, big consequence” kernel issues that can remain hidden until timing aligns just badly enough.
What the Bug Actually Is
At a technical level, CVE-2026-31500 is a synchronization defect, not a parsing bug or a bounds check failure. The core problem is thatbtintel_hw_error() runs a recovery sequence involving synchronous HCI commands without first acquiring the lock that serializes those commands across the rest of the Bluetooth stack. That leaves it exposed to a race with close/shutdown code that uses the same machinery and assumes exclusive access to the request response state.The vulnerability description makes the failure mode clear. While
btintel_hw_error() is still in progress, btintel_shutdown_combined() may free the response skb first. Once that happens, the ongoing hardware-error path can hit a slab use-after-free in kfree_skb(). In other words, the bug is not that the driver frees the same object twice deliberately; it is that the object’s lifetime is no longer protected by the locking discipline that the surrounding code expectsWhy hci_req_sync_lock() matters
The kernel’s synchronous HCI command helpers are not standalone utility calls. They depend on shared request bookkeeping, and that bookkeeping must not be manipulated concurrently. By wrapping the whole recovery sequence in hci_req_sync_lock() and hci_req_sync_unlock(), the fix restores a single-file queueing model for the command path, preventing the error handler from racing with shutdown logic.This is exactly the kind of fix that kernel maintainers prefer for concurrency bugs: tighten the critical section, do not redesign the subsystem. It is smaller, easier to audit, and less likely to break unrelated Bluetooth behavior. It also aligns the hardware-error path with the rest of the synchronous HCI command issuers, which is the real consistency gap at the heart of the issue.
Key technical points:
- The bug is a race condition in a shared command path.
- The affected objects are
hdev->req_statusandhdev->req_rsp. - The visible crash is a slab-use-after-free rather than a simple null dereference.
- The shutdown and error-recovery paths both rely on the same HCI synchronization primitives.
- The fix is to serialize the entire recovery sequence with the existing lock.
How the Race Happens
The CVE record includes a fairly precise race narrative, and that is unusual enough to be worth unpacking.btintel_hw_error() starts a recovery flow that includes __hci_cmd_sync() calls. At the same time, the shutdown path can be entered through hci_dev_do_close(), which eventually reaches btintel_shutdown_combined() and also uses __hci_cmd_sync() under the synchronization lock. The problem is not that one path is “right” and the other is “wrong”; the problem is that one path assumed serialized access, and the other did not honor that assumption.Because both paths mutate the same request/response state, the race can unfold in a narrow but lethal window. One thread may publish a response buffer and expect it to remain valid until its synchronous exchange completes. Another may tear the device down, free the response skb, and invalidate the memory underneath the still-running error handler. That is the textbook shape of a use-after-free in a heavily concurrent kernel subsystem.
Why the shutdown path is especially risky
Shutdown code is often overlooked in security reviews because it feels “non-user-facing.” In practice, teardown is one of the most dangerous places to leave loose ends, because cleanup often assumes no other actor is still using the same state. If the cleanup path and the recovery path can both be entered during device instability, then teardown becomes part of the attack surface.In this case, the shutdown path is not just ending the lifecycle of the adapter; it is also participating in synchronous command exchange. That means it must obey the same serialization rules as any other synchronous HCI issuer. If it does not, it can invalidate shared request state while another path is mid-flight.
The practical implications are easy to miss:
- Error recovery may overlap with device close events.
- Shared skb-based request responses can be freed early.
- The use-after-free may only appear under rare timing.
- The crash can show up in unrelated code such as skb drop helpers.
- Automated testing may miss it unless teardown and error handling overlap.
Evidence From the Crash Reports
The published CVE text includes both a data-race report and a KASAN report, and those are the kinds of signals kernel engineers take very seriously. The data-race warning shows concurrent access tohdev->req_rsp in __hci_cmd_sync_sk, with btintel_hw_error() on one side and btintel_shutdown_combined() on the other. That tells us the race is not speculative; it was observed in live kernel instrumentationThe KASAN report is even more concrete. It points to a slab-use-after-free in
sk_skb_reason_drop() with a read from a freed address while __hci_cmd_sync_sk() and btintel_hw_error() are still executing. KASAN does not invent these issues; it reports real memory misuse in a controlled debugging environment. When paired with the data-race trace, the diagnosis becomes hard to dispute.Why the trace is persuasive
Kernel bugs are often debated when the evidence is indirect. Here, the evidence is unusually direct:- A synchronous HCI command path is reading shared request state.
- A shutdown path is writing and freeing that same state.
- The race is caught by a data-race detector.
- The misuse then manifests as a use-after-free.
- The failure occurs in packet cleanup code, where freed skb access is fatal.
In practical terms, this kind of bug can be hard for users to reproduce manually. The race depends on timing, device state, and the precise overlap between hardware error handling and device close. But once discovered, the fix is usually straightforward because the kernel’s locking architecture already describes the intended serialization boundary.
Impact on Linux Systems
For most systems, CVE-2026-31500 is not an everyday desktop annoyance. It is a kernel memory-safety bug in a specific Bluetooth Intel path, so exposure depends on hardware, driver usage, and whether the affected recovery code is actually exercised. That said, Bluetooth drivers are present on a huge number of laptops, small-form-factor machines, and enterprise endpoints, which means the reachable population is far from trivial.The immediate impact is stability first and security second, at least in the published record. A slab-use-after-free can crash the kernel or trigger unpredictable behavior, and in some cases memory corruption bugs can later be chained into more serious exploitation paths. The CVE entry does not assign a CVSS score yet, but the absence of a score should not be mistaken for a lack of urgency; it usually means the record is still being enriched
Consumer versus enterprise exposure
For consumers, the main question is whether the device uses Intel Bluetooth hardware and whether the hardware error and shutdown overlap can happen in normal use. If the answer is yes, then the bug may surface as a sporadic crash, a Bluetooth stack instability, or a system hang under device teardown stress. Many home users will never notice it, but those who do will probably see it as “Bluetooth got flaky” rather than “there is a kernel race.”For enterprises, the story is more serious because the same laptop or endpoint may be part of a managed fleet where sudden reboots, device instability, and support incidents all have operational cost. Bluetooth is often treated as peripheral, but in modern managed environments it can be tied to headsets, peripherals, conferencing, and docking workflows. Peripheral does not mean unimportant when a bug can take down the kernel.
Important operational consequences:
- Endpoint instability can look like random Bluetooth failure.
- Fleet support teams may misdiagnose the problem as hardware drift.
- Error handling bugs are hard to reproduce in help-desk conditions.
- Shutdown paths are common during sleep, suspend, and power transitions.
- Intel Bluetooth hardware is widely deployed in mobile systems.
Why the Fix Is Narrow but Correct
The remedy for CVE-2026-31500 does not redesign Bluetooth recovery. It simply surrounds the recovery sequence inbtintel_hw_error() with hci_req_sync_lock() and hci_req_sync_unlock(). That choice is significant because it shows the underlying problem was not with the recovery logic itself, but with its access discipline. The code already had a serialization model; the bug was that one path bypassed it.That kind of patch is often a good sign. Broad refactors in kernel drivers can introduce as many problems as they solve, especially in timing-sensitive code. By contrast, a focused lock fix is easier to reason about and easier to backport across supported kernel lines. It also indicates that maintainers understood the issue as a coordination failure rather than a deeper protocol mismatch.
What serialization buys you
Serialization does three important things here. First, it prevents two synchronous HCI command issuers from mutating the same request state concurrently. Second, it preserves the lifetime guarantees around the response skb. Third, it makes the hardware error path behave like every other command issuer in the subsystem, which reduces the chance of future regressions from inconsistent locking assumptions.That consistency matters more than it might sound. Kernel subsystems tend to accumulate invisible contracts over time. Once one path starts bypassing a lock, future maintainers may infer the wrong concurrency model and build on unstable assumptions. Restoring the lock closes that door.
The fix also hints at a broader maintenance principle:
- Prefer existing synchronization primitives over ad hoc protection.
- Keep critical sections aligned with shared ownership boundaries.
- Match error-recovery paths to the same rules as normal command paths.
- Avoid special-casing teardown unless there is a compelling reason.
- Treat skb lifetime as part of the concurrency design, not a detail.
Relationship to Other Bluetooth Bugs
Bluetooth is having an unusually busy security period, and CVE-2026-31500 fits that pattern. In the same general area of the kernel, the Bluetooth USB path has also seen security attention, which reinforces a familiar truth: the Bluetooth stack is a large, stateful subsystem with multiple opportunities for lifetime and boundary mistakes. The fact that several Bluetooth bugs are being reported close together does not necessarily mean they are related, but it does suggest the subsystem is under active scrutiny.That scrutiny is healthy. Bluetooth combines hardware quirks, asynchronous events, and driver-specific recovery behavior in a way that naturally breeds concurrency bugs. A driver may be perfectly correct under steady-state use and still fail under suspend/resume, disconnect, or firmware-recovery timing. That is why Bluetooth issues often look minor in isolation but collectively indicate a broad attack surface.
What this says about subsystem complexity
The Intel Bluetooth path is a good example of the challenge. The driver has to speak to a controller, recover from failure, report diagnostic information, and shut down cleanly across multiple execution contexts. Every one of those tasks can overlap with another if the timing is unfortunate enough. When a subsystem depends on both normal operation and emergency recovery, lock coverage becomes a first-order security property.Some practical takeaways:
- Bluetooth recovery paths should be reviewed as carefully as normal send paths.
- Shutdown behavior deserves the same locking discipline as runtime commands.
- Driver-specific exception handling can create hidden concurrency edges.
- Vendor hardware support often introduces bespoke recovery logic.
- Kernel Bluetooth code is a recurring source of timing-sensitive bugs.
What System Administrators Should Do
Administrators do not need to panic over CVE-2026-31500, but they should treat it as a real kernel maintenance issue. The fix is upstream, and the vulnerability record already links to stable Git references, which is usually a good sign that backports are in motion. The remaining work is to determine whether a given kernel build includes the serialized recovery path and whether the affected Intel Bluetooth code is present on the hardware in questionThe most practical response is to inventory Intel Bluetooth hardware, check the running kernel lineage, and review vendor advisories for backported fixes. Because this is a concurrency bug, ordinary usage testing may not reveal it. Administrators should prioritize systems that rely on Bluetooth for peripherals, mobile workflows, or enterprise endpoint management, especially if those systems also see frequent sleep, wake, or device disconnect cycles.
A sensible response plan
- Identify endpoints and laptops with Intel Bluetooth controllers.
- Confirm whether the enterprise kernel build contains the fix.
- Check vendor backport notes rather than relying on upstream version numbers alone.
- Watch for crash reports tied to Bluetooth teardown or hardware-error events.
- Treat repeated Bluetooth instability as a possible kernel issue, not just a device problem.
Strengths and Opportunities
The good news is that the bug is well understood, the fix is small, and the failure mode is specific enough to backport safely. That makes mitigation more straightforward than in many kernel security stories. It also gives downstream vendors a clear target for their stable branches.The broader opportunity is that this CVE reinforces good maintenance habits around teardown serialization and skb lifetime management. Kernel teams can use it as a reminder to audit other recovery paths that touch shared request state.
- The fix is surgical and low-risk.
- The crash evidence is clear and reproducible in instrumentation.
- The bug is confined to a recognizable Intel Bluetooth recovery path.
- Backporting should be relatively mechanical for stable trees.
- The issue highlights the value of consistent lock coverage.
- It creates a useful audit precedent for similar error-recovery paths.
- It may improve long-term subsystem robustness beyond the immediate CVE.
Risks and Concerns
The main concern is that concurrency bugs are rarely isolated. Even when one specific path is fixed, other code paths may still make similar assumptions about request ownership or teardown timing. That means this CVE could be a symptom of a broader class of Bluetooth synchronization problems rather than a single one-off defect.There is also the usual operational risk that endpoint teams will underestimate a Bluetooth bug because it sounds peripheral. In practice, kernel instability on mobile systems and managed laptops can become a support burden very quickly. Small-sounding driver bugs often have an outsized effect when they occur across a fleet.
- The race may point to similar locking gaps elsewhere.
- The use-after-free may be hard to reproduce in the field.
- Users may misattribute symptoms to hardware failure.
- Vendor backport status may be uneven across kernels.
- Shutdown paths are often less tested than hot paths.
- Bluetooth issues can be masked by unrelated sleep/wake behavior.
- The lack of a final CVSS score leaves some teams without a numerical triage anchor.
Looking Ahead
The next thing to watch is how quickly downstream kernel vendors and distribution maintainers backport the fix into supported releases. Because the upstream change is narrowly focused, it should translate cleanly, but the real-world rollout will depend on how each vendor handles Bluetooth driver updates in long-term kernel branches. In enterprise environments, that distinction can mean the difference between a prompt fix and a lingering exposure window.It will also be worth watching whether additional Bluetooth-related kernel reports surface in the same Intel code family. When one driver path shows a synchronization flaw, maintainers often review adjacent paths for similar assumptions. That can produce a small wave of follow-up hardening, which is often a healthy sign that the subsystem is being cleaned up rather than merely patched.
What to monitor next:
- Stable kernel backports landing across major distributions.
- OEM firmware and vendor-kernel update notes for Intel Bluetooth hardware.
- Any follow-on fixes in
btintelor adjacent Bluetooth error-recovery code. - Reports of sleep, wake, or shutdown instability on affected laptops.
- Additional CVEs that reveal related synchronization assumptions.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center