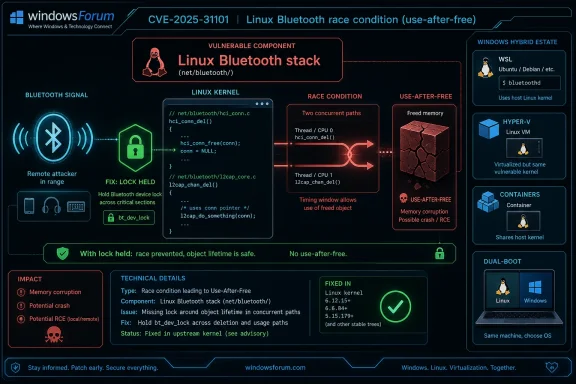
CVE-2026-43019 is a high-severity Linux kernel Bluetooth vulnerability, published by NVD on May 1, 2026 and modified on May 8, involving a potential use-after-free in set_cig_params_sync when hci_conn access is not properly protected by the Bluetooth device lock during configuration. It is not a Windows kernel bug, despite appearing in a Microsoft-adjacent security workflow for some readers. The practical story is broader: modern Windows environments increasingly depend on Linux kernels through WSL, appliances, containers, edge devices, and dual-boot developer machines. A small Bluetooth locking fix is therefore a useful reminder that “not Windows” no longer means “not in the estate.”
The bug itself is not hard to summarize, but it is easy to misfile. In the Linux Bluetooth stack, code handling Connected Isochronous Group parameters could look up and access an
That is the classic shape of a use-after-free flaw. The kernel.org CNA scored it 7.8, high severity, with local attack vector, low complexity, low privileges required, no user interaction, and high confidentiality, integrity, and availability impact. NVD had not yet provided its own CVSS score at the time of the May 8 enrichment, but it did add CWE-416 and affected Linux kernel CPE ranges.
The important word in that vector is local. This is not a drive-by Bluetooth worm in the facts currently available. It is a kernel memory-safety bug in a local code path, and exploiting such bugs usually requires the attacker to already have some foothold or ability to exercise the vulnerable subsystem.
That distinction should lower panic, not priority. Local kernel flaws are exactly the sort of issues attackers chain after phishing, credential theft, container escape attempts, or developer-workstation compromise. The danger is not that every Bluetooth adapter has become a remote doorway; it is that an already-running local actor may find a sharper knife.
That last word matters. This was not just about stopping a dangling pointer. It was also about ensuring the configuration being applied was coherent, not assembled from fields that could change under the code’s feet.
In kernel work, the difference between “probably still there” and “locked against mutation” is the difference between a clever optimization and a security boundary. Bluetooth’s modern feature set has grown far beyond pairing a mouse or headset. Low Energy audio, isochronous channels, and increasingly complex controller interactions make the subsystem a concurrency minefield.
The public fix appears in multiple stable branches, which is how kernel security maintenance is supposed to work. Administrators should not be looking for one magic commit in isolation; they should be looking for distribution kernels that have absorbed the relevant stable backport.
Linux distributions do not ship upstream kernels in a clean, linear way. Enterprise distros backport fixes, cloud images carry vendor patches, embedded systems freeze older branches, and enthusiast distributions move quickly enough that a vulnerable upstream number may be less useful than the package changelog. A scanner that only compares
For WindowsForum readers, this is where the Windows angle becomes practical. A Windows admin may not think they own many Linux kernels, yet their environment may include WSL developer systems, Hyper-V Linux guests, Kubernetes nodes, storage appliances, security sensors, Android-based handhelds, IoT gateways, and bootable recovery environments. Some of those have Bluetooth disabled or absent. Some quietly ship kernel branches nobody has reviewed in months.
The right first question is not “Do we run Linux?” It is “Where do we run a Linux kernel that can expose Bluetooth or load Bluetooth modules?”
That can create category confusion. A CVE appearing in a Microsoft security workflow is not automatically a Windows vulnerability. In this case, the vulnerable component is the Linux kernel Bluetooth subsystem, not Windows Bluetooth or the NT kernel.
Still, Microsoft’s presence around these issues is not cosmetic. The company now sits at the intersection of Windows endpoints, Linux development environments, Azure-hosted Linux workloads, and security tooling that inventories both. A vulnerability like CVE-2026-43019 may be “Linux” in origin while landing on the desk of a Windows administrator because the estate is hybrid by default.
This is the new normal for patch triage. Vendor boundaries are no longer the same as operational boundaries. The person responsible for the Windows fleet may also be responsible for the developer laptops running WSL, the Hyper-V lab with Linux guests, and the Defender portal flagging vulnerable kernels.
Kernel developers cannot afford that simplification. Bluetooth code runs in privileged contexts, parses controller state, handles asynchronous events, and coordinates with userspace daemons. The implementation is a stack of timing-sensitive interactions with hardware, firmware, drivers, and application-level configuration.
A local use-after-free in this area is not automatically easy to exploit. Kernel heap layout, mitigations, privilege boundaries, and hardware availability all matter. But dismissing the bug because it is “just Bluetooth” misses the point: optional subsystems are still kernel subsystems, and kernel subsystems are part of the trusted computing base when loaded.
The most conservative mitigation is boring. If a system does not need Bluetooth, disable it at firmware, kernel module, or operating-system policy level. If it does need Bluetooth, update the kernel from the distribution or vendor channel rather than trying to hand-apply upstream patches.
Developer workstations are the obvious example. They run experimental packages, local containers, WSL instances, test kernels, USB and Bluetooth accessories, and privileged tooling. They also tend to hold source code, credentials, signing material, and cloud tokens. A local kernel escalation on that class of machine can be more valuable than a remote bug on a locked-down kiosk.
Edge systems are the second concern. Linux-based gateways, industrial tablets, medical carts, conference-room controllers, and retail devices often include Bluetooth hardware whether or not anyone remembers why. Their patch cycles are slower, their management channels are uneven, and their inventories are frequently incomplete.
The uncomfortable lesson is that “local” and “Bluetooth” are not synonyms for “low risk.” They are context multipliers. On a server with no Bluetooth stack loaded, exposure may be negligible. On a developer laptop with untrusted local workloads and active Bluetooth hardware, the same CVE deserves faster attention.
The CPE list also has limits. NVD’s own interface asks whether a CPE is missing, and for good reason. CPEs are a rough map of affected software, not a complete statement of every vendor package, appliance firmware, or cloud image carrying the code.
This is where vulnerability management can go wrong. A team may chase every kernel string that resembles the NVD range while ignoring whether Bluetooth is enabled, whether the vendor has backported the fix, or whether the system is reachable by the kind of local actor needed to exploit the bug. Conversely, a team may suppress the finding because it is “not Windows” while leaving Linux-based endpoint components unmanaged.
The better workflow is to reconcile three facts: the running kernel package, the vendor advisory or changelog, and the actual exposure of the Bluetooth subsystem. That takes longer than reading a CVSS score, but it produces a decision instead of a dashboard color.
For Windows-heavy shops, the hidden work is discovery. Check whether Linux kernels appear in WSL distributions, Hyper-V guests, CI runners, dual-boot systems, security appliances, and container hosts. WSL itself is not a generic Bluetooth exposure story in the same way a bare-metal Linux laptop is, but it is part of the broader inventory problem: if Linux kernels exist in the environment, they need an owner.
The most useful near-term controls are mundane. Keep kernel packages current. Remove or blacklist Bluetooth modules where the hardware is unused. Watch for vendor advisories from distributions rather than relying only on upstream version strings. Treat developer endpoints as high-value systems, not disposable sandboxes.
None of that is glamorous. It is also exactly how most kernel CVEs are neutralized in real environments.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Bluetooth Race Becomes an Asset-Inventory Test
A Bluetooth Race Becomes an Asset-Inventory Test
The bug itself is not hard to summarize, but it is easy to misfile. In the Linux Bluetooth stack, code handling Connected Isochronous Group parameters could look up and access an hci_conn object without holding the correct device lock. If another path freed or modified that connection at the same time, the kernel could touch memory that no longer belonged to the object it thought it was using.That is the classic shape of a use-after-free flaw. The kernel.org CNA scored it 7.8, high severity, with local attack vector, low complexity, low privileges required, no user interaction, and high confidentiality, integrity, and availability impact. NVD had not yet provided its own CVSS score at the time of the May 8 enrichment, but it did add CWE-416 and affected Linux kernel CPE ranges.
The important word in that vector is local. This is not a drive-by Bluetooth worm in the facts currently available. It is a kernel memory-safety bug in a local code path, and exploiting such bugs usually requires the attacker to already have some foothold or ability to exercise the vulnerable subsystem.
That distinction should lower panic, not priority. Local kernel flaws are exactly the sort of issues attackers chain after phishing, credential theft, container escape attempts, or developer-workstation compromise. The danger is not that every Bluetooth adapter has become a remote doorway; it is that an already-running local actor may find a sharper knife.
The Fix Says More Than the Score
The patch rationale is plain: thehci_conn lookup and field access must be covered by the Bluetooth device lock, because RCU alone is not enough. RCU can help readers see consistent object lifetime in some contexts, but the kernel developers noted that this path also needed protection against concurrent deletion, modification, and configuration “tearing.”That last word matters. This was not just about stopping a dangling pointer. It was also about ensuring the configuration being applied was coherent, not assembled from fields that could change under the code’s feet.
In kernel work, the difference between “probably still there” and “locked against mutation” is the difference between a clever optimization and a security boundary. Bluetooth’s modern feature set has grown far beyond pairing a mouse or headset. Low Energy audio, isochronous channels, and increasingly complex controller interactions make the subsystem a concurrency minefield.
The public fix appears in multiple stable branches, which is how kernel security maintenance is supposed to work. Administrators should not be looking for one magic commit in isolation; they should be looking for distribution kernels that have absorbed the relevant stable backport.
The Affected-Version List Is a Warning Against Naive Version Checks
NVD’s initial analysis listed Linux kernel 7.0 release candidates and several version ranges: 6.6 before 6.12.81, 6.13 before 6.18.22, and 6.19 before 6.19.12, along with specific 6.4.16 and 6.5.3 entries. That range pattern is messy, and messy is normal for kernel CVEs.Linux distributions do not ship upstream kernels in a clean, linear way. Enterprise distros backport fixes, cloud images carry vendor patches, embedded systems freeze older branches, and enthusiast distributions move quickly enough that a vulnerable upstream number may be less useful than the package changelog. A scanner that only compares
uname -r against an upstream range can be both too loud and too quiet.For WindowsForum readers, this is where the Windows angle becomes practical. A Windows admin may not think they own many Linux kernels, yet their environment may include WSL developer systems, Hyper-V Linux guests, Kubernetes nodes, storage appliances, security sensors, Android-based handhelds, IoT gateways, and bootable recovery environments. Some of those have Bluetooth disabled or absent. Some quietly ship kernel branches nobody has reviewed in months.
The right first question is not “Do we run Linux?” It is “Where do we run a Linux kernel that can expose Bluetooth or load Bluetooth modules?”
Microsoft’s Shadow in the Story Is Mostly About Operations
The submitted material points to an MSRC Update Guide page, but the underlying CVE is sourced to kernel.org and the public technical detail sits in Linux and NVD channels. That is not unusual. Microsoft’s security ecosystem often surfaces third-party CVEs because Microsoft customers consume third-party software through Azure, Defender, GitHub, container images, WSL, and partner products.That can create category confusion. A CVE appearing in a Microsoft security workflow is not automatically a Windows vulnerability. In this case, the vulnerable component is the Linux kernel Bluetooth subsystem, not Windows Bluetooth or the NT kernel.
Still, Microsoft’s presence around these issues is not cosmetic. The company now sits at the intersection of Windows endpoints, Linux development environments, Azure-hosted Linux workloads, and security tooling that inventories both. A vulnerability like CVE-2026-43019 may be “Linux” in origin while landing on the desk of a Windows administrator because the estate is hybrid by default.
This is the new normal for patch triage. Vendor boundaries are no longer the same as operational boundaries. The person responsible for the Windows fleet may also be responsible for the developer laptops running WSL, the Hyper-V lab with Linux guests, and the Defender portal flagging vulnerable kernels.
Bluetooth Is Easy to Ignore Until It Becomes Kernel Attack Surface
Bluetooth has a reputation problem in enterprise IT. It is treated as peripheral convenience, not core infrastructure. That attitude made sense when the biggest policy debate was whether users could pair earbuds at work.Kernel developers cannot afford that simplification. Bluetooth code runs in privileged contexts, parses controller state, handles asynchronous events, and coordinates with userspace daemons. The implementation is a stack of timing-sensitive interactions with hardware, firmware, drivers, and application-level configuration.
A local use-after-free in this area is not automatically easy to exploit. Kernel heap layout, mitigations, privilege boundaries, and hardware availability all matter. But dismissing the bug because it is “just Bluetooth” misses the point: optional subsystems are still kernel subsystems, and kernel subsystems are part of the trusted computing base when loaded.
The most conservative mitigation is boring. If a system does not need Bluetooth, disable it at firmware, kernel module, or operating-system policy level. If it does need Bluetooth, update the kernel from the distribution or vendor channel rather than trying to hand-apply upstream patches.
The Real Risk Lives on Developer Machines and Edge Systems
CVE-2026-43019 is unlikely to be the vulnerability that wakes every CIO at 3 a.m. The more plausible risk is concentrated in places where local code execution is easier to obtain and kernel patch discipline is weaker.Developer workstations are the obvious example. They run experimental packages, local containers, WSL instances, test kernels, USB and Bluetooth accessories, and privileged tooling. They also tend to hold source code, credentials, signing material, and cloud tokens. A local kernel escalation on that class of machine can be more valuable than a remote bug on a locked-down kiosk.
Edge systems are the second concern. Linux-based gateways, industrial tablets, medical carts, conference-room controllers, and retail devices often include Bluetooth hardware whether or not anyone remembers why. Their patch cycles are slower, their management channels are uneven, and their inventories are frequently incomplete.
The uncomfortable lesson is that “local” and “Bluetooth” are not synonyms for “low risk.” They are context multipliers. On a server with no Bluetooth stack loaded, exposure may be negligible. On a developer laptop with untrusted local workloads and active Bluetooth hardware, the same CVE deserves faster attention.
Scanner Output Will Be Noisier Than the Vulnerability
Security teams should expect disagreement among tools. NVD shows the kernel.org score, some commercial databases may estimate differently, and distro trackers may mark packages as fixed even when the upstream version number appears vulnerable. That is not necessarily a contradiction; it is how backporting works.The CPE list also has limits. NVD’s own interface asks whether a CPE is missing, and for good reason. CPEs are a rough map of affected software, not a complete statement of every vendor package, appliance firmware, or cloud image carrying the code.
This is where vulnerability management can go wrong. A team may chase every kernel string that resembles the NVD range while ignoring whether Bluetooth is enabled, whether the vendor has backported the fix, or whether the system is reachable by the kind of local actor needed to exploit the bug. Conversely, a team may suppress the finding because it is “not Windows” while leaving Linux-based endpoint components unmanaged.
The better workflow is to reconcile three facts: the running kernel package, the vendor advisory or changelog, and the actual exposure of the Bluetooth subsystem. That takes longer than reading a CVSS score, but it produces a decision instead of a dashboard color.
Patch Management Has to Follow the Kernel, Not the Brand
For Linux distributions, the action is straightforward: install the kernel update that includes the stable fix for the maintained branch. For appliances and embedded products, the answer is less satisfying: wait for the vendor firmware or disable Bluetooth if the product allows it.For Windows-heavy shops, the hidden work is discovery. Check whether Linux kernels appear in WSL distributions, Hyper-V guests, CI runners, dual-boot systems, security appliances, and container hosts. WSL itself is not a generic Bluetooth exposure story in the same way a bare-metal Linux laptop is, but it is part of the broader inventory problem: if Linux kernels exist in the environment, they need an owner.
The most useful near-term controls are mundane. Keep kernel packages current. Remove or blacklist Bluetooth modules where the hardware is unused. Watch for vendor advisories from distributions rather than relying only on upstream version strings. Treat developer endpoints as high-value systems, not disposable sandboxes.
None of that is glamorous. It is also exactly how most kernel CVEs are neutralized in real environments.
The Small Locking Bug That Exposes a Bigger Blind Spot
CVE-2026-43019 should be read as a high-severity Linux kernel Bluetooth flaw with local exploitation characteristics, not as a Windows emergency or a remote Bluetooth apocalypse. The details are specific, but the operational lesson is general: hybrid environments make third-party kernel bugs relevant to Windows administrators whether or not the Windows kernel is involved.- CVE-2026-43019 concerns the Linux kernel Bluetooth stack, specifically unsafe
hci_connaccess inset_cig_params_sync. - The kernel.org CNA scored the issue 7.8 high under CVSS 3.1, while NVD had not yet assigned its own score in the supplied May 8 record.
- The flaw is categorized as CWE-416, use-after-free, and the fix is to hold the Bluetooth device lock around lookup and field access.
- The local attack vector makes broad remote panic inappropriate, but local kernel bugs remain important on developer machines, edge devices, and systems running untrusted workloads.
- Administrators should verify vendor kernel updates and actual Bluetooth exposure rather than relying only on upstream version comparisons.
- Windows-centric teams should still inventory Linux kernels in WSL-adjacent workflows, Hyper-V guests, appliances, containers, and dual-boot systems.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center