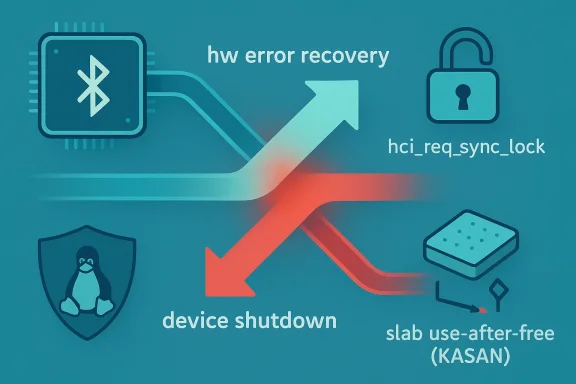
The latest Linux Bluetooth security issue to hit public tracking is CVE-2026-31500, a kernel bug in the Intel Bluetooth driver path that can race during hardware-error recovery and device shutdown. According to the published record, the problem is that
Lin been one of those subsystems that looks ordinary until a race condition turns it into a reliability problem. The Intel Bluetooth driver sits on top of the kernel’s HCI core, where state changes, command submission, and device teardown all have to be carefully serialized. In practice, that means a lot of seemingly small locking decisions carry a lot of weight, because the code is running in the middle of error recovery, suspend/resume, and device-close paths that may overlap in unpleasant ways.
CVE-2026-31500 is a classic kernel concurrency bug: not a malformed packet flaw, but a lifetime and synchronization problem. The upstream description says
That pattern matters because it is not just a crash bug in the abstract. The record includes both a data-race report and a KASAN slab-use-after-free trace, which means the bug was observed as real memory corruption behavior, not merely a theoretical race window. Kernel Bluetooth bugs often hide in exactly these seams: the ror recovery meets device shutdown, or where a driver assumes it owns the command path but another thread has already entered teardown.
The broader context is also worth noting. Linux kernel CVEs are frequently assigned after a fix lands in a supported tree, and the kernel project explicitly treats many such bugfixes as security-relevant even when exploitation is not obvious at first glance. That helps explain why a synchronization bug in Bluetooth recovery becomes a tracked vulnerability instead of being filed away as a generic stability issue.
The detail that matters most is not the specific Intel exception-info command, but the fact that the entire recovery sequence was missing the same serialization used elsewhere in the synchronous HCI stack. In other words, this was not a new lock design problem. It was a gap in consistency: one path was allowed to opt out of the rule every other synchronous command issuer already followed.
The practical consequence is straightforward:ash or hang during Bluetooth error recovery
That kind of fix usually signals strong maintainability. Kernel developers generally prefer the smallest change that closes the race without disturbing adjacent code paths. In this case, the new lock placement should be easier to audit and easier to backport than a wider refactor would be.
Because neither side fully respected the same synchronization boundary, they could both reach into the same response object at the same time. One path then frees the skb, and the other path, still running, trips over the memory that has already been returned to the slab allocator. That is how a race becomes a use-after-free.
It is also notable that the issue arises during recovery rather than normal Bluetooth operation. That means the trigger may be less common on healthy systems, but recovery paths are exactly where long-lived bugs hide. If a laptop or workstation only hits Bluetooth hardware recovery occasionally, the flaw can evade testing for a long time.
The Intel Bluetooth path here appears to have relied on a local assumption that
The kernel community has long emphasized that fixes should land in supported stable trees when they address real bugs or security issues, and this one fits that pattern neatly. A serialization bug in a widely deployed driver is the kind of thing maintainers tend to backport quickly.
The report also shows that the read happened in a worker context while the write/free came from an ioctl-driven close path. That matters because it tells us the vulnerable condition does e thread doing something absurd. It depends on ordinary control flows overlapping in just the wrong way.
It also means that an incident might be misdiagnosed. A Bluetooth close-time crash can look like a flaky adapter, a firmware problem, or a suspend/resume quirk long before someone notices the memory-safety trace. That is one reason kernel CVEs with race conditions deserve prompt attention even when the immediate user impact seems narrow.
The common lesson is that Bluetooth drivers are full of state transitions that happen under stress. Controller errors, device disconnects, and recovery logic all involve code paths that are harder to test than ordinary data transfer. In that sense, CVE-2026-31500 fits a larger pattern of synchronization-sensitive Bluetooth issues.
It is also notable that the fix is entirely internal. No protocol redesign, no new UAPI, no feature removal. The patch simply restores the proper lock discipline around the recovery sequence. That usually indicates the maintainers believed the existing architecture was sound, but one path had drifted outside the intended rules.
If the affected Intel driver path exists on a managed endpoint, the crash could interfere with device-close operations, post-error recovery, or system shutdown. In environments where drivers are part of a standardized build image, one bad kernel can affect thousands of identical machines. That is why “low-frequency” does not mean “low priority.”
A consumer might encounter symptoms such as Bluetooth instability after a device error, a close-time crash, or a system hang during shutdown or wake-cycle management. That said, it is not the sort of issue that usually presents as an obvious security compromise to the user. It is more likely to appear as an unexplained crash, a kernel warning, or a device that refuses to behave after a transient fault.
That is worth stressing because some readers still assume a CVE must imply a catastrophic exploit. In Linux kernel practice, CVE assignment often reflects a broader security-maintenance judgment: memory safety, availability, and cross-context races all matter. A bug does not need to be remotely weaponized to deserve a CVE.
It also means the patch likely deserves normal patch-management treatment rather than special-case triage. If you run affected Intel Bluetooth hardware, this is not a “wait and see” item. It is the sort of bug that should be folded into routine kernel maintenance as soon as your vendor ships the fix.
The broader opportunity is to use this CVE as a reminder to audit similar recovery paths across other drivers. The Bluetooth stack is full of helpers that issue synchronous commands, and any helper that bypasses common serialization deserves a closer look.
There is also the usual downstream risk: vendor kernels may lag upstream fixes, and managed fleets can stay exposed longer than expected. A second problem is observability; a Bluetooth close-time crash might be blamed on hardware, firmware, or suspend/resume behavior before anyone connects it to a kernel race.
The second thing to watch is whether adjacent Bluetooth recovery paths receive similar review. Once one driver helper is found to bypass the expected synchronous command lock, it is reasonable to ask whether other helpers are doing the same thing. Security work in the kernel often advances by pattern recognition, not by isolated bug hunting.
The third thing to watch is fleet behavior after patching. If the issue was previously being masked as an intermittent crash, the fix may reduce symptoms that operators had already grown used to treating as “just Bluetooth weirdness.” That can be a useful diagnostic signal on its own.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
btintel_hw_error issues synchronous HCI commands without holding hci_req_sync_lock, which allows it to collide with btintel_shutdown_combined and trigger a slab-use-after-free when both paths manipulate the same request state at once bility guide mirrors the upstream description and points to the same kernel.org fix references, confirming that the issue was recently published and is now part of the NVD dataset.
 Background
Background
Lin been one of those subsystems that looks ordinary until a race condition turns it into a reliability problem. The Intel Bluetooth driver sits on top of the kernel’s HCI core, where state changes, command submission, and device teardown all have to be carefully serialized. In practice, that means a lot of seemingly small locking decisions carry a lot of weight, because the code is running in the middle of error recovery, suspend/resume, and device-close paths that may overlap in unpleasant ways.CVE-2026-31500 is a classic kernel concurrency bug: not a malformed packet flaw, but a lifetime and synchronization problem. The upstream description says
btintel_hw_error sends two synchronous commands—reset and Intel exception-info retrieval—without taking the same lock that other synchronous HCI command issuers already rely on. That makes the path vulnerable to a racesethroughbtintel_shutdown_combined, which also uses__hci_cmd_syncunderhci_req_sync_lock`. When both paths run together, the request response skb can be freed on one side while the other side is still using it.That pattern matters because it is not just a crash bug in the abstract. The record includes both a data-race report and a KASAN slab-use-after-free trace, which means the bug was observed as real memory corruption behavior, not merely a theoretical race window. Kernel Bluetooth bugs often hide in exactly these seams: the ror recovery meets device shutdown, or where a driver assumes it owns the command path but another thread has already entered teardown.
The broader context is also worth noting. Linux kernel CVEs are frequently assigned after a fix lands in a supported tree, and the kernel project explicitly treats many such bugfixes as security-relevant even when exploitation is not obvious at first glance. That helps explain why a synchronization bug in Bluetooth recovery becomes a tracked vulnerability instead of being filed away as a generic stability issue.
What CVE-2026-31500 actually breaks
At the center of the bug ishdev->req_rsp, the response skb associated with synchronous HCI command handling. The published trace shows concurrent access from btintel_hw_error and btintel_shutdown_combined, with one path reading and the other writing or freeing the same state. In kernel terms, that is can turn a valid pointer into a use-after-free before the function call chain has even unwound.The detail that matters most is not the specific Intel exception-info command, but the fact that the entire recovery sequence was missing the same serialization used elsewhere in the synchronous HCI stack. In other words, this was not a new lock design problem. It was a gap in consistency: one path was allowed to opt out of the rule every other synchronous command issuer already followed.
Why the race is dangerous
A use-after-free in a skb path is especially nasty because skb lifetimes are central to networking correctness. Once the close path frees the response buffer, the error path can still think it owns that object and proceed to touch it or free it again. That is why the trace points intokfree_skb and sk_skb_reason_drop in the KASAN output.The practical consequence is straightforward:ash or hang during Bluetooth error recovery
- teardown can become unstable when triggered at the wrong time
- repeated close/open cycles can amplify the chance of hitting the race
- driver-state corruption may surface as unpredictable Bluetooth failures
Why the fix is so compact
The upstream remedy is elegantly narrow: wrap the whole recovery sequence inhci_req_sync_lock and hci_req_sync_unlock so btintel_hw_error is serialized with every other synchronous HCI command issuer. That is the right shape of fix for a race like this because it doeser. It simply restores a contract that already existed elsewhere in the subsystem.That kind of fix usually signals strong maintainability. Kernel developers generally prefer the smallest change that closes the race without disturbing adjacent code paths. In this case, the new lock placement should be easier to audit and easier to backport than a wider refactor would be.
The race condition in plain English
Think of the bug as two cleanup crews showing up at the same machine room with one spare key and one trash bag. One team is the hardware-error recovery path, trying to reset and query exception state. The other is the shutdown path, trying to close the device and dispose of whatever request state still exists.Because neither side fully respected the same synchronization boundary, they could both reach into the same response object at the same time. One path then frees the skb, and the other path, still running, trips over the memory that has already been returned to the slab allocator. That is how a race becomes a use-after-free.
The evidence in the report
The record is unusually direct about the failure mode. It includes:- a data-race warning involving
__hci_cmd_sync_sk - a close-path write/free in
btintel_shutdown_combined - a KASAN slab-use-after-free in
sk_skb_reason_drop - the culprit call chain inside
btintel_hw_error
It is also notable that the issue arises during recovery rather than normal Bluetooth operation. That means the trigger may be less common on healthy systems, but recovery paths are exactly where long-lived bugs hide. If a laptop or workstation only hits Bluetooth hardware recovery occasionally, the flaw can evade testing for a long time.
Why locking in kernel drivers is never optional
Kernel locking often looks boring, and that is the point. Correctly serialized state transitions are the difference between a stable subsystem and a race condition that only shows up under load, teardown, or fault injection. In Bluetooth, this is especially important because device state is not static; it changes during pairing, suspend/resume, controller reset, and close.The Intel Bluetooth path here appears to have relied on a local assumption that
btintel_hw_error could run its recovery commands without colliding with other synchronous issuers. The bug demonstrates why that assumption was unsafe. If the core HCI command path already has a lock for command serialization, bypassing it in one helper creates an exception that the rest of the system is not prepared to handle.Why this kind of bug keeps happening
There are a few reasons:- recovery code is less frequently exercised than hot-path code
- teardown often runs concurrently with error handling
- subsystem-specific helpers can drift from shared locking rules
- memory ownership in skb-based code is easy to get wrong
- race windows are small, so tests may miss them
The kernel community has long emphasized that fixes should land in supported stable trees when they address real bugs or security issues, and this one fits that pattern neatly. A serialization bug in a widely deployed driver is the kind of thing maintainers tend to backport quickly.
What the KASAN report tells us
KASAN is especially useful because it turns timing bugs into visible memory errors. In this case, the reported slab-use-after-free insk_skb_reason_drop suggests the response skb was still being handled after it had already been released elsewhere. That gives defenders more confidence that ly a benign race, but a genuine memory lifetime violation.The report also shows that the read happened in a worker context while the write/free came from an ioctl-driven close path. That matters because it tells us the vulnerable condition does e thread doing something absurd. It depends on ordinary control flows overlapping in just the wrong way.
Why that matters operationally
For enterprise operators, this raises a familiar concern: the bug may be rare in steady state, but a crash during shutdown or recovery can still have outsized impact. In fleet environments, even “nonpersistent” bugs matter because they can interrupt rolling updates, automated restarts, or endpoint management workflows.It also means that an incident might be misdiagnosed. A Bluetooth close-time crash can look like a flaky adapter, a firmware problem, or a suspend/resume quirk long before someone notices the memory-safety trace. That is one reason kernel CVEs with race conditions deserve prompt attention even when the immediate user impact seems narrow.
How this compares with other recent kernel Bluetooth bugs
Bluetooth has had a busy run of security issues across multiple drivers and layers, which is not surprising given the complexity of the subsystem. Nearby published issues have included btusb alternate-setting handling and other Bluetooth stack flaws, showing that the Bluetooth family as a whole remains a rich source of small-but-serious kernel defects. Those bugs are not identical, but they rhyme: each one exposes a place where the kernel trusted state too much.The common lesson is that Bluetooth drivers are full of state transitions that happen under stress. Controller errors, device disconnects, and recovery logic all involve code paths that are harder to test than ordinary data transfer. In that sense, CVE-2026-31500 fits a larger pattern of synchronization-sensitive Bluetooth issues.
What makes this one distinct
Unlike some Bluetooth flaws that involve validation or bounds checks, this issue is squarely about concurrency and object lifetime. That means the exploitability story is different. It is less about malformed input and more about forcing the driver into a recovery/shutdown overlap. That may reduce the number of real-world triggers, but it does not make the bug trivial.It is also notable that the fix is entirely internal. No protocol redesign, no new UAPI, no feature removal. The patch simply restores the proper lock discipline around the recovery sequence. That usually indicates the maintainers believed the existing architecture was sound, but one path had drifted outside the intended rules.
Why enterprise admins should care
Enterprise fleets rarely fail because of one dramatic bug; they fail because enough small bugs line up in the wrong context. Bluetooth may not be the centerpiece of most datacenter architecture, but it is common in laptops, workstations, docking setups, and managed endpoints. That makes a kernel-level Bluetooth crash relevant to fleet stability even if it is not a headline remote-code-execution event.If the affected Intel driver path exists on a managed endpoint, the crash could interfere with device-close operations, post-error recovery, or system shutdown. In environments where drivers are part of a standardized build image, one bad kernel can affect thousands of identical machines. That is why “low-frequency” does not mean “low priority.”
Enterprise impact points
- managed laptops using Intel Bluetooth hardware
- desktop fleets with frequent suspend/resume cycles
- environments that rely on remote management and reboot orchestration
- kiosk or endpoint systems that auto-recover from hardware faults
- systems with aggressive device lifecycle management
Consumer impact: usually limited, but not zero
For most consumers, the practical risk is probably narrower than for enterprise fleets. Many users will never trigger the exact recovery and shutdown overlap required for the bug to surface. Still, the affected code sits in a broadly deployed subsystem, and laptops are the most obvious class of hardware where Intel Bluetooth is common.A consumer might encounter symptoms such as Bluetooth instability after a device error, a close-time crash, or a system hang during shutdown or wake-cycle management. That said, it is not the sort of issue that usually presents as an obvious security compromise to the user. It is more likely to appear as an unexplained crash, a kernel warning, or a device that refuses to behave after a transient fault.
For consumers, the practical advice is simple
- Install kernel updates from your distribution as soon as they are available.
- Reboot after updates if your platform requires it.
- Watch for Bluetooth-related crash logs after suspend or shutdown.
- If you rely on Bluetooth peripherals, avoid delaying security maintenance.
- Treat recurring Bluetooth instability as a sign to update the kernel, not just the firmware.
Why the CVE was published so quickly
The Linux kernel’s CVE process is intentionally tied to fixes that have already landed in a stable tree, which helps explain why public records often appear shortly after remediation work is available. In this case, the publication timing suggests the kernel community considered the bug important enough to track formally once the lock-serialization fix existed.That is worth stressing because some readers still assume a CVE must imply a catastrophic exploit. In Linux kernel practice, CVE assignment often reflects a broader security-maintenance judgment: memory safety, availability, and cross-context races all matter. A bug does not need to be remotely weaponized to deserve a CVE.
What the publication tells defenders
The record’s presence in NVD and Microsoft’s vulnerability guide means downstream visibility is already spreading. For mixed-platform organizations, that matters because Linux kernel issues can nondows and Azure security data in the same enterprise tooling. That is increasingly normal, especially in environments that use Microsoft security workflows for fleet tracking.It also means the patch likely deserves normal patch-management treatment rather than special-case triage. If you run affected Intel Bluetooth hardware, this is not a “wait and see” item. It is the sort of bug that should be folded into routine kernel maintenance as soon as your vendor ships the fix.
Strengths and Opportunities
The upside of this fix is that it is narrow, understandable, and low-risk from a code-change perspective. It restores an existing locking discipline instead of inventing a new one, which reduces regression risk and makes backporting easier. It also closes a real memory-safety gap, not just a cosmetic bug.The broader opportunity is to use this CVE as a reminder to audit similar recovery paths across other drivers. The Bluetooth stack is full of helpers that issue synchronous commands, and any helper that bypasses common serialization deserves a closer look.
- The fix is small and surgical
- It aligns
btintel_hw_errorwith established lock discipline - It addresses a real use-after-free condition
- It should be relatively straightforward to backport
- It improves shutdown and recovery stability
- It gives vendors a clean basis for stable releases
- It highlights a reusable lesson for other driver error paths
Risks and Concerns
The main concern is that this bug lives in a privileged, timing-sensitive path that may not be exercised often enough in testing. That makes it easy to underestimate until a system hits the wrong combination of Bluetooth error recovery and shutdown. Rare bugs are still real bugs, especially when they involve kernel memory lifetime.There is also the usual downstream risk: vendor kernels may lag upstream fixes, and managed fleets can stay exposed longer than expected. A second problem is observability; a Bluetooth close-time crash might be blamed on hardware, firmware, or suspend/resume behavior before anyone connects it to a kernel race.
- Race windows are small, so they can evade testing
- Downstream kernels may lag the upstream fix
- The bug may be mistaken for a generic Bluetooth instability
- Recovery paths are harder to exercise than normal operation
- Enterprise automation can re-trigger close/reopen cycles
- Memory-safety bugs in the kernel can have unexpected side effects
- Mixed fleets may not know which devices use the affected Intel path
Looking Ahead
The next thing to watch is how quickly major Linux distributors and OEM-supported kernels absorb the lock-serialization change. Because the fix is tight and localized, it should not be controversial, but kernel backports can still take time to roll through long-term-support branches. That is especially true on devices whose support cadence is tied to OEM certification rather than upstream release timing.The second thing to watch is whether adjacent Bluetooth recovery paths receive similar review. Once one driver helper is found to bypass the expected synchronous command lock, it is reasonable to ask whether other helpers are doing the same thing. Security work in the kernel often advances by pattern recognition, not by isolated bug hunting.
The third thing to watch is fleet behavior after patching. If the issue was previously being masked as an intermittent crash, the fix may reduce symptoms that operators had already grown used to treating as “just Bluetooth weirdness.” That can be a useful diagnostic signal on its own.
- Confirm whether your kernel build includes the hci_req_sync_lock serialization fix
- Review Intel Bluetooth systems for close-time or recovery-path instability
- Check vendor backports in distro and OEM kernels, not just upstream commits
- Watch for similar synchronization issues in adjacent HCI helpers
- Prioritize devices that use Bluetooth heavily in suspend/resume workflows
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center