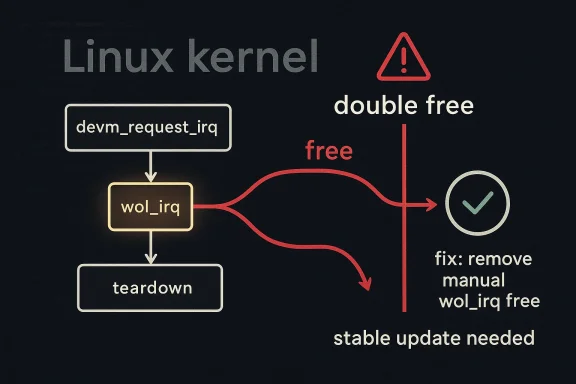
CVE-2026-31506 has landed in the Linux kernel security stream as another reminder that even small cleanup mistakes in driver error paths can matter. In this case, the issue is a double free in the bcmasp Ethernet driver’s Wake-on-LAN interrupt handling, where the code tried to free an IRQ that had already been handed to the managed resource framework. The fix is straightforward, but the lesson is broader: when kernel code mixes manual cleanup with devm_-managed allocation, the consequences of getting ownership wrong can range from noisy crashes to harder-to-diagnose system instability. The CVE was published on April 22, 2026, and NVD has not yet assigned a CVSS score.
The Linux kernel has a long history of treating memory-management mistakes as first-class security and reliability issues, and for good reason. A double free can corrupt allocator state, trigger a crash, or in some contexts open the door to code execution if an attacker can influence timing and memory layout. Even when a flaw is not obviously exploitable, kernel maintainers and CVE assignees frequently err on the side of publication because the kernel’s privilege level turns “just a bug” into something much more serious.
The upstream description for CVE-2026-31506 is concise: the Linux kernel’s net: bcmasp path contained a bug in the cleanup logic for the Wake-on-LAN IRQ, and the driver did not need to free
This kind of issue is especially common in driver code because IRQ registration, DMA buffers, and network device teardown paths often span multiple layers of abstraction. The Linux kernel provides managed resource helpers precisely to reduce teardown bugs, but those helpers only work when developers consistently follow the ownership model. If a codebase mixes manual lifetime management with managed lifetime management in the same path, the cleanup logic becomes fragile and harder to reason about.
The CVE entry currently carries no NVD severity assignment, which is typical for very recent disclosures. That does not mean the issue is unimportant; it means the scoring process has not yet been completed. For operators, the practical takeaway is to track the stable kernel branches that incorporate the fix and apply updates promptly once their distribution backports the patch.
That mismatch is exactly what makes the issue a double free. The first cleanup happens as part of the devm-managed lifecycle, and the second cleanup is triggered by driver logic that assumes it still owns the IRQ. The kernel usually does not tolerate that kind of duplication gracefully, because the resource may already have been released or repurposed by the time the second free occurs.
In this case, the bug was not in the interrupt itself but in the cleanup path around it. The driver apparently treated the IRQ like a manually allocated resource, which is a common enough mistake in large kernel subsystems where code evolves over time and ownership conventions differ from function to function. The fix reflects a broader kernel rule: if a resource is devm-managed, let devres own the release path.
The Linux kernel community has repeatedly emphasized that many bugs become security-relevant because of where they occur, not because they were originally written with malicious use in mind. That is why the kernel CVE process often assigns identifiers to fixes that look like reliability bugs on the surface. In practice, that cautious approach helps downstream vendors and cloud operators treat kernel stability issues with the seriousness they deserve.
It is also worth noting that a bug can be security-relevant even if a live exploit has not been publicly demonstrated. The Linux kernel CVE process explicitly notes that nearly any bug may be exploitable in principle, even when that possibility is not evident at the moment of fix. That philosophy explains why kernel.org frequently publishes CVEs for resolved defects before their real-world impact is fully characterized.
Networking drivers are especially prone to subtle lifetime bugs because they juggle interrupts, DMA mappings, packet queues, and power-management hooks. Wake-on-LAN adds another layer of complexity because the interface must preserve enough state to respond to a wake event while still cooperating with the device lifecycle. That combination creates exactly the sort of code path where a cleanup mistake can sit unnoticed until a rare sequence of operations hits it.
That is one reason kernel maintainers are so strict about matching acquisition and release patterns. Once an IRQ, buffer, or descriptor is registered in a managed framework, the cleanup rules change. The bcmasp fix is therefore more than a one-line correction; it is an acknowledgment that the driver was mixing ownership models in a way that the kernel could not safely tolerate.
The broader lesson is that kernel code is safest when the cleanup strategy is consistent from the moment a resource is created. If an IRQ, memory region, or hardware register block is registered using a devm helper, the corresponding release path should usually be implicit rather than explicit. Mixed semantics are where bugs like double free emerge.
The kernel’s generic IRQ documentation reinforces the broader idea that interrupts are first-class kernel objects with their own lifecycle semantics. Even without diving into the bcmasp code, it is easy to see how an IRQ that is both managed and manually released would be a red flag in a subsystem where interrupt ownership matters.
CVE-2026-31506 fits that pattern neatly. The record appeared in NVD shortly after the kernel-side issue was resolved, and the NVD entry notes that the CVE was received from kernel.org on April 22, 2026. That speed is useful for vendors and enterprise defenders because it gives them a stable identifier to track while they wait for distribution backports and patch advisories.
At the same time, the lack of an immediate CVSS score should not be misread as a sign of low priority. NVD may simply not have completed its enrichment work yet. In practice, kernel teams and downstream vendors frequently treat recent CVEs as actionable long before NVD finalizes metadata.
Systems that rely on wake-capable network hardware deserve special attention. Servers, remote appliances, and embedded devices often preserve Wake-on-LAN support for out-of-band management or power-saving policies, and those are exactly the environments where IRQ lifecycle bugs can become operationally visible. A defect in the teardown path can be particularly annoying because it may show up during maintenance windows, reboot sequences, or device replacement events rather than under constant load.
Enterprise teams should also think in terms of exposure windows. Even when a bug is “just” a double free, a long-lived unpatched fleet can turn a low-level defect into a broad availability issue if it is hit repeatedly across many devices. That is why kernel patching programs often bundle security and stability work together rather than treating them as separate disciplines.
Embedded devices are a different story. Home routers, media boxes, industrial controllers, and appliance-style systems often rely on narrow kernel configurations and may keep a driver in place for years. In that world, an IRQ cleanup bug can survive long after mainstream desktop kernels have moved on, especially if the vendor does not aggressively backport networking fixes.
That is why kernel CVEs are worth tracking even when the initial scoring is absent. The absence of a score is not the absence of risk; it is simply the absence of final metadata. For consumers, the practical advice is straightforward: keep the distribution kernel updated and do not ignore low-level networking fixes just because they sound obscure.
It also provides a teaching moment for driver authors and reviewers. Every place a resource is acquired should have a clearly corresponding release model, and every teardown path should be checked for duplicates. The broader ecosystem benefits when maintainers treat ownership conventions as part of the API contract rather than an implementation detail.
There is also the risk of patch lag. Even when the upstream fix is straightforward, downstream vendors may need time to cherry-pick, validate, and distribute it across supported branches. During that gap, users can be left with a known CVE and no immediately visible indicator of whether their exact build is protected.
There is a final concern, too: NVD enrichment is still pending. Until a final severity rating appears, some organizations may under-prioritize the issue because it lacks a score. That would be a mistake, since kernel CVEs often become actionable long before scoring is complete.
It is also worth watching whether the same ownership pattern turns up elsewhere in the networking stack. Kernel bugs of this kind often reveal coding habits rather than isolated mistakes, and that means review teams may find similar cleanup issues in other drivers that adopted managed APIs over time. If so, CVE-2026-31506 may end up being remembered less for its individual impact than for the audit it prompts across related code.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The Linux kernel has a long history of treating memory-management mistakes as first-class security and reliability issues, and for good reason. A double free can corrupt allocator state, trigger a crash, or in some contexts open the door to code execution if an attacker can influence timing and memory layout. Even when a flaw is not obviously exploitable, kernel maintainers and CVE assignees frequently err on the side of publication because the kernel’s privilege level turns “just a bug” into something much more serious.The upstream description for CVE-2026-31506 is concise: the Linux kernel’s net: bcmasp path contained a bug in the cleanup logic for the Wake-on-LAN IRQ, and the driver did not need to free
wol_irq because it was created with devm_request_irq. That matters because devres owns the lifecycle of resources acquired through the devm API family, which means cleanup is automatic when the device goes away. In other words, the explicit free call was not just redundant; it was wrong in a way that could lead to freeing the same object twice.This kind of issue is especially common in driver code because IRQ registration, DMA buffers, and network device teardown paths often span multiple layers of abstraction. The Linux kernel provides managed resource helpers precisely to reduce teardown bugs, but those helpers only work when developers consistently follow the ownership model. If a codebase mixes manual lifetime management with managed lifetime management in the same path, the cleanup logic becomes fragile and harder to reason about.
The CVE entry currently carries no NVD severity assignment, which is typical for very recent disclosures. That does not mean the issue is unimportant; it means the scoring process has not yet been completed. For operators, the practical takeaway is to track the stable kernel branches that incorporate the fix and apply updates promptly once their distribution backports the patch.
What the Vulnerability Is
At the center of CVE-2026-31506 is a simple ownership mistake. The bcmasp driver set up a Wake-on-LAN interrupt usingdevm_request_irq, which registers the interrupt through the device-managed resource system. The bug was that the driver later attempted to free that same IRQ explicitly, even though devres would already free it automatically during teardown.That mismatch is exactly what makes the issue a double free. The first cleanup happens as part of the devm-managed lifecycle, and the second cleanup is triggered by driver logic that assumes it still owns the IRQ. The kernel usually does not tolerate that kind of duplication gracefully, because the resource may already have been released or repurposed by the time the second free occurs.
Why managed IRQs matter
The Linux kernel’s managed resource model exists to make teardown safer and less error-prone. When a driver uses managed APIs, the kernel ties the resource to the device object and automatically reclaims it when the device is removed. That reduces boilerplate and removes a whole class of cleanup bugs, but it also means the driver author must not free the resource manually unless the API explicitly requires it.In this case, the bug was not in the interrupt itself but in the cleanup path around it. The driver apparently treated the IRQ like a manually allocated resource, which is a common enough mistake in large kernel subsystems where code evolves over time and ownership conventions differ from function to function. The fix reflects a broader kernel rule: if a resource is devm-managed, let devres own the release path.
- The bug is in teardown, not normal operation.
- The resource was acquired with a managed API.
- Manual cleanup duplicated the automatic release.
- The visible failure mode may be a crash, warning, or memory corruption.
- The actual exploitability depends on runtime conditions, which NVD has not yet assessed.
Why a Double Free Is Serious
A double free is one of those bugs that sounds mundane until you remember that kernel memory management is part of the trusted computing base. Double freeing a structure can destabilize allocator bookkeeping, cause use-after-free behavior, and in some circumstances create a path toward privilege escalation. The exact impact depends on the code path, the allocator, and whether an attacker can trigger the bug predictably.The Linux kernel community has repeatedly emphasized that many bugs become security-relevant because of where they occur, not because they were originally written with malicious use in mind. That is why the kernel CVE process often assigns identifiers to fixes that look like reliability bugs on the surface. In practice, that cautious approach helps downstream vendors and cloud operators treat kernel stability issues with the seriousness they deserve.
How this can show up operationally
For an administrator, the most likely symptom of a bug like this is not a dramatic “exploit” event. More often, it appears as a driver crash, an oops, a spurious warning during device teardown, or an unstable system after a network interface is brought down or reinitialized. Because Wake-on-LAN functionality is tied to device power states and shutdown behavior, failures can also emerge during suspend, resume, or module unload sequences.It is also worth noting that a bug can be security-relevant even if a live exploit has not been publicly demonstrated. The Linux kernel CVE process explicitly notes that nearly any bug may be exploitable in principle, even when that possibility is not evident at the moment of fix. That philosophy explains why kernel.org frequently publishes CVEs for resolved defects before their real-world impact is fully characterized.
- Crash risk rises when teardown paths run repeatedly.
- Driver unload and device removal are common trigger points.
- Wake-on-LAN logic often executes during power transitions.
- A double free can degrade into memory corruption.
- Public exploitability is not required for a CVE assignment.
The bcmasp Driver in Context
The bcmasp driver belongs to Broadcom’s ASP Ethernet support in the Linux kernel, a niche but important area of the networking stack. Drivers like this tend to live far from the spotlight until a bug turns up in an edge case such as suspend/resume, wake events, or teardown. When that happens, the problem can affect systems that depend on reliable low-level network behavior more than everyday desktop users.Networking drivers are especially prone to subtle lifetime bugs because they juggle interrupts, DMA mappings, packet queues, and power-management hooks. Wake-on-LAN adds another layer of complexity because the interface must preserve enough state to respond to a wake event while still cooperating with the device lifecycle. That combination creates exactly the sort of code path where a cleanup mistake can sit unnoticed until a rare sequence of operations hits it.
Why this driver class is fragile
The bcmasp case reflects a familiar kernel pattern: the more a driver tries to be efficient with resource management, the more carefully ownership boundaries must be documented. Managed APIs simplify routine cleanup, but they also create a split-brain situation if the codebase still contains older manual-release habits. The result is often not an immediate failure but a latent bug waiting for a maintenance path to uncover it.That is one reason kernel maintainers are so strict about matching acquisition and release patterns. Once an IRQ, buffer, or descriptor is registered in a managed framework, the cleanup rules change. The bcmasp fix is therefore more than a one-line correction; it is an acknowledgment that the driver was mixing ownership models in a way that the kernel could not safely tolerate.
- Broadcom network drivers often sit in embedded or specialized systems.
- Wake-on-LAN support increases teardown complexity.
- Power-state transitions are fertile ground for lifecycle bugs.
- Managed resources reduce boilerplate but demand discipline.
- Latent bugs often surface only during rare shutdown or suspend paths.
What the Fix Changes
The remediation is conceptually simple: stop freeing the Wake-on-LAN IRQ manually because the resource was allocated withdevm_request_irq and will be released automatically. That means the fix removes the redundant cleanup and lets the device-managed framework do what it was designed to do. It is the sort of patch that looks tiny in a changelog but carries a meaningful reliability payoff.The broader lesson is that kernel code is safest when the cleanup strategy is consistent from the moment a resource is created. If an IRQ, memory region, or hardware register block is registered using a devm helper, the corresponding release path should usually be implicit rather than explicit. Mixed semantics are where bugs like double free emerge.
Managed vs. manual cleanup
Managed cleanup is not a magic shield; it is a contract. Developers get simpler teardown code, but they must accept that the framework owns the resource lifetime. Manual cleanup is still appropriate for resources that are not devm-managed, but it must be used consistently and carefully. When the two approaches collide, the cleanup path becomes a source of instability rather than protection.The kernel’s generic IRQ documentation reinforces the broader idea that interrupts are first-class kernel objects with their own lifecycle semantics. Even without diving into the bcmasp code, it is easy to see how an IRQ that is both managed and manually released would be a red flag in a subsystem where interrupt ownership matters.
- Identify how the IRQ is acquired.
- Determine whether the acquisition is devm-managed.
- Remove any duplicate manual free path.
- Audit nearby teardown logic for related ownership assumptions.
- Test suspend, resume, unload, and device-removal scenarios.
Upstream Process and CVE Signaling
The Linux kernel’s CVE documentation makes clear that the project maintains its own approach to vulnerability assignment and announcement. CVEs are often reserved and published around fixes that are already in stable trees, which helps downstream maintainers correlate identifiers with real patches rather than speculative issue reports. That system is one reason the kernel’s CVE stream can be very active even when the underlying defects are narrow.CVE-2026-31506 fits that pattern neatly. The record appeared in NVD shortly after the kernel-side issue was resolved, and the NVD entry notes that the CVE was received from kernel.org on April 22, 2026. That speed is useful for vendors and enterprise defenders because it gives them a stable identifier to track while they wait for distribution backports and patch advisories.
Why publication timing matters
Security teams often need a CVE before they have all the contextual details about exploitability, severity, or real-world impact. That is especially true for kernel bugs, where vendor backports may arrive on different schedules and the same logical fix can appear in multiple branches. A published CVE gives operations teams a common language for triage, patch planning, and executive reporting.At the same time, the lack of an immediate CVSS score should not be misread as a sign of low priority. NVD may simply not have completed its enrichment work yet. In practice, kernel teams and downstream vendors frequently treat recent CVEs as actionable long before NVD finalizes metadata.
- Kernel CVEs are often tied to resolved fixes.
- Stable backports can lag behind the upstream disclosure.
- NVD enrichment is not always immediate.
- Operators should watch vendor advisories, not just NVD.
- Shared CVE IDs simplify cross-vendor tracking.
Enterprise Impact
For enterprise environments, the key question is not whether the bug exists upstream, but whether the affected code is present in the kernels actually deployed in production. Many organizations run vendor-modified or long-term-support kernels, which means the relevant fix may arrive through a distribution security update rather than a direct upstream version bump. That makes patch tracking a supply-chain problem as much as a technical one.Systems that rely on wake-capable network hardware deserve special attention. Servers, remote appliances, and embedded devices often preserve Wake-on-LAN support for out-of-band management or power-saving policies, and those are exactly the environments where IRQ lifecycle bugs can become operationally visible. A defect in the teardown path can be particularly annoying because it may show up during maintenance windows, reboot sequences, or device replacement events rather than under constant load.
What admins should prioritize
The right response is a controlled patching review, not panic. Administrators should determine whether their kernel line includes the bcmasp driver, check their vendor’s advisory feed, and verify whether the fix has been backported into the exact build they are running. If the system uses Broadcom-based networking and Wake-on-LAN is enabled, the priority should move higher.Enterprise teams should also think in terms of exposure windows. Even when a bug is “just” a double free, a long-lived unpatched fleet can turn a low-level defect into a broad availability issue if it is hit repeatedly across many devices. That is why kernel patching programs often bundle security and stability work together rather than treating them as separate disciplines.
- Inventory kernels and driver stacks by exact build.
- Verify whether the bcmasp driver is in use.
- Check whether Wake-on-LAN is enabled on affected hosts.
- Follow vendor backport status, not just upstream commit status.
- Schedule reboots or maintenance where the fix can be validated safely.
Consumer and Embedded Device Impact
For consumers, the direct risk is usually lower and less visible, but it is not zero. Desktop users who never touch Wake-on-LAN or who run hardware with different network drivers may never encounter the issue at all. Still, consumer-oriented Linux distributions often inherit kernel fixes quickly, and those updates can improve stability even if users never see the underlying CVE.Embedded devices are a different story. Home routers, media boxes, industrial controllers, and appliance-style systems often rely on narrow kernel configurations and may keep a driver in place for years. In that world, an IRQ cleanup bug can survive long after mainstream desktop kernels have moved on, especially if the vendor does not aggressively backport networking fixes.
Why small fixes can have outsized value
Even if the bug never becomes a high-profile exploit, it still matters because reliability defects accumulate. A device that crashes only during rare suspend or wake cycles can generate support calls, reboot loops, or unexplained downtime that users attribute to “hardware problems.” The reality is often a software lifecycle mismatch, and the cure is usually a maintenance update rather than a replacement.That is why kernel CVEs are worth tracking even when the initial scoring is absent. The absence of a score is not the absence of risk; it is simply the absence of final metadata. For consumers, the practical advice is straightforward: keep the distribution kernel updated and do not ignore low-level networking fixes just because they sound obscure.
- Consumer desktops may never notice the issue.
- Embedded products may retain the bug for a long time.
- Stability updates can matter as much as security updates.
- Vendor support cadence often determines real exposure.
- Rare edge cases are common in long-lived appliances.
Strengths and Opportunities
The good news is that this is the kind of kernel vulnerability that upstream development is structurally well equipped to catch and fix. Managed resource APIs, stable backports, and the kernel’s active CVE workflow all help shrink the window between bug discovery and remediation. That makes the issue a useful case study in how process can reduce risk even when the underlying mistake is small.It also provides a teaching moment for driver authors and reviewers. Every place a resource is acquired should have a clearly corresponding release model, and every teardown path should be checked for duplicates. The broader ecosystem benefits when maintainers treat ownership conventions as part of the API contract rather than an implementation detail.
- Managed cleanup reduces many classes of teardown bugs.
- Stable kernel backports can protect long-lived deployments.
- Wake-on-LAN testing can catch edge cases during validation.
- Driver audits often uncover nearby lifetime bugs.
- CVE publication improves visibility for enterprise patching.
- Upstream fixes tend to propagate quickly into vendor trees.
Risks and Concerns
The main concern is that bugs like this are easy to underestimate because they are small and localized. A single incorrect free in a teardown routine can sit unnoticed in a seldom-used code path while still representing a real risk to systems that rely on the driver. Kernel bugs do not have to be glamorous to be operationally meaningful.There is also the risk of patch lag. Even when the upstream fix is straightforward, downstream vendors may need time to cherry-pick, validate, and distribute it across supported branches. During that gap, users can be left with a known CVE and no immediately visible indicator of whether their exact build is protected.
The hidden cost of lifecycle mistakes
Lifecycle bugs are particularly troublesome because they often masquerade as benign refactoring errors. Once a driver has mixed devm-managed and manual cleanup patterns, reviewers may struggle to reconstruct ownership semantics from the code alone. That makes future maintenance harder and increases the chance of similar bugs in adjacent functions.There is a final concern, too: NVD enrichment is still pending. Until a final severity rating appears, some organizations may under-prioritize the issue because it lacks a score. That would be a mistake, since kernel CVEs often become actionable long before scoring is complete.
- Patch delays can leave affected systems exposed.
- Ownership confusion makes kernel code harder to audit.
- Low-scoring or unscored CVEs may be deprioritized incorrectly.
- Rare execution paths are often the most dangerous.
- Backport variability complicates fleet-wide verification.
- Adjacent bugs may exist in the same driver subsystem.
Looking Ahead
The next step is straightforward: watch for vendor advisories and stable-kernel releases that incorporate the fix, then verify that your deployed kernel includes the patched bcmasp logic. Because the issue is already public and tied to a specific commit family, the distribution of remediation should be measurable rather than mysterious. The practical question is simply how quickly each vendor turns that upstream fix into an update you can deploy.It is also worth watching whether the same ownership pattern turns up elsewhere in the networking stack. Kernel bugs of this kind often reveal coding habits rather than isolated mistakes, and that means review teams may find similar cleanup issues in other drivers that adopted managed APIs over time. If so, CVE-2026-31506 may end up being remembered less for its individual impact than for the audit it prompts across related code.
What to monitor
- Stable kernel release notes mentioning the bcmasp fix.
- Distribution security advisories for affected kernel packages.
- Whether your hardware actually uses the bcmasp driver.
- Any follow-on fixes in related network driver teardown paths.
- NVD’s eventual CVSS publication and enrichment updates.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center