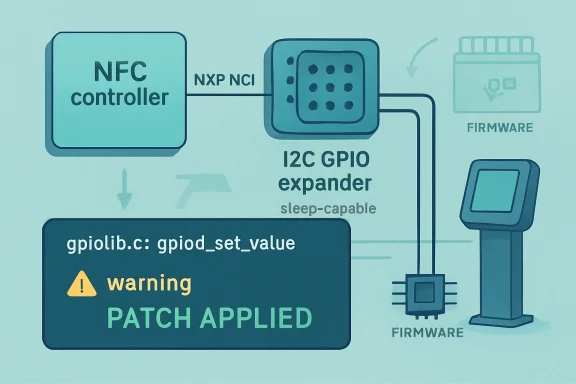
CVE-2026-31545 is a medium-severity Linux kernel flaw disclosed by kernel.org on April 24, 2026, affecting the NXP NCI NFC driver when firmware and enable GPIO lines are driven through sleep-capable controllers such as I2C GPIO expanders and fixed through stable kernel patches. The bug is not a remote-code-execution barnburner, and it is unlikely to trouble most desktop Windows users directly. But it is a useful reminder that modern platform security increasingly lives in the unglamorous borderlands between firmware, buses, power management, and driver assumptions. The interesting story is not that an NFC driver emitted a kernel warning; it is that the warning became a CVE because availability failures in small hardware paths now matter at scale.
The Linux kernel description of CVE-2026-31545 is almost comically terse: the NXP NCI NFC driver needed to “allow the firmware and enable GPIOs to sleep.” In practical terms, the driver was using a GPIO operation that assumes the line can be changed immediately, even though some GPIO providers sit behind buses such as I2C where setting a value may sleep.
That distinction is second nature to kernel developers and deeply obscure to almost everyone else. A memory-mapped GPIO on a system-on-chip can often be toggled in atomic contexts. A GPIO expander hanging off I2C cannot; the kernel may need to schedule, wait on the bus, and return later. Use the wrong GPIO API in the wrong place, and the kernel complains loudly.
The warning cited in the CVE lands in
That score is the right shape for the bug, but it is also a blunt instrument. For a laptop with no exposed NXP NFC controller, the issue is academic. For an embedded medical, payment, access-control, or industrial device that actually wires an NFC controller through a sleepy GPIO expander, it can be operationally relevant.
That does not make it irrelevant. Availability bugs in kernel drivers can be serious when the device is a fixed-function appliance and the affected peripheral participates in a business process. NFC is not decorative in systems that use it for identity badges, tap-to-authenticate workflows, reader modules, diagnostics, or provisioning.
The NXP NCI family also points the story away from commodity desktop drama and toward embedded Linux. NCI is the NFC Controller Interface, and NXP NFC controllers are common enough in phones, tablets, point-of-sale equipment, and custom hardware designs that a driver bug can travel through many products without ever becoming a household name.
The uncomfortable part for defenders is that hardware-shaped vulnerabilities rarely map cleanly to inventory systems. A vulnerability scanner can say “Linux kernel version in affected range.” It may not know whether the box has the relevant driver built, whether the device tree or ACPI tables expose that NFC controller, or whether the GPIO line is behind an expander that can sleep. This is where the CPE list becomes a starting point rather than an answer.
This is why the “Are we missing a CPE?” prompt on NVD pages is both useful and misleading. The CPEs for upstream Linux are not a product-by-product exploitability verdict. They are a coarse representation of affected kernel versions, not a definitive statement that every system running those versions can trigger the flaw.
For WindowsForum readers, the Microsoft Security Response Center link adds another layer of possible confusion. MSRC’s Security Update Guide includes CVEs assigned by industry partners and advisories beyond classic Windows Patch Tuesday items. The appearance of a Linux kernel CVE in a Microsoft-facing vulnerability portal does not automatically mean Windows itself is vulnerable.
The nuance matters for WSL users, Azure fleet operators, appliance vendors, and anyone maintaining Linux-based infrastructure under a Microsoft-heavy management umbrella. A Windows desktop with WSL installed is not the same thing as an embedded Linux board with an NXP NFC controller. A Linux VM in Azure is not inherently affected unless its kernel, configuration, and hardware exposure line up with the flaw.
This is the kernel doing what the kernel is supposed to do. It has separate APIs because not all GPIO providers are equal. The bug is not that an I2C expander sleeps; the bug is that the driver treated the GPIO as though it could not.
There is a useful lesson here for people who only encounter vulnerabilities through dashboards. Not every CVE is a dramatic failure of cryptography, memory safety, or authentication. Some are the formal security label attached to a mundane driver fix because a mundane driver fix can prevent denial of service on real systems.
The public record shows several stable patch references, which is also what defenders should want to see. The fix was not merely tossed into a future development branch; it was propagated through supported stable lines. That is the practical difference between “interesting upstream commit” and “something vendors can actually consume.”
CVE-2026-31545 lives precisely in that choreography. The NFC controller needs firmware and enable GPIO lines. Those lines may be served by an expander. The expander may require I2C traffic. I2C traffic may sleep. A driver path that assumes immediate GPIO access collides with the platform’s actual electrical design.
For sysadmins used to servers, this can feel like a niche footnote. For product security teams, it is daily life. The same upstream kernel version can behave very differently across two boards because the device tree, ACPI description, peripheral mix, and vendor patches are different. Vulnerability management becomes less about matching version numbers and more about understanding product construction.
That is why kernel CVEs sometimes look overbroad and underexplained at the same time. The upstream project has to publish enough information for stable consumers to act, while avoiding a bespoke threat model for every board design on Earth. The result is a CVE entry that names a driver and a warning, leaving downstream vendors to decide whether their product is actually exposed.
Imagine an access-control kiosk that intermittently loses NFC functionality after a suspend-resume sequence. Imagine a field device that logs kernel warnings until watchdog policy intervenes. Imagine a medical cart or industrial handheld where NFC is part of identity, configuration, or workflow. The attacker model may be local, but the business disruption can be real.
The key is not to inflate the vulnerability. There is no public basis for calling this a remote compromise or a privilege-escalation bug from the description alone. The key is to resist the opposite mistake: dismissing it because it lacks headline-grade impact categories.
Availability is often where hardware bugs announce themselves first. A kernel warning may be the visible symptom; the real cost is a device that cannot reliably perform the job it was sold to do. For enterprise defenders, that means the triage question should be “Do we run affected kernels on devices with this NFC path?” rather than “Is this scary enough to make the front page?”
Windows admins manage Linux servers in Azure, Linux appliances behind Windows clients, WSL images on developer workstations, and fleets of edge devices monitored through Microsoft tooling. They also read the MSRC guide, where industry CVEs can appear beside Microsoft product vulnerabilities. That creates a real risk of overreaction or misclassification.
The right posture is disciplined separation. If you are responsible for Windows endpoints only, CVE-2026-31545 is probably noise unless those endpoints depend on a Linux subsystem or appliance you also own. If you operate Linux devices, especially embedded systems with NFC hardware, it belongs in the normal kernel patch queue.
For WSL specifically, the public description does not suggest a meaningful path unless the environment exposes the affected kernel driver and relevant hardware arrangement, which is not how ordinary WSL deployments work. Treating this as a WSL emergency would confuse the asset model. Treating it as irrelevant across all Microsoft-managed estates would be just as lazy.
This is where mature organizations have an advantage. A good hardware bill of materials, kernel configuration archive, and device-tree inventory can turn an ambiguous kernel CVE into a quick decision. A poor inventory turns it into a week of Slack archaeology and vendor emails.
The affected ranges published by NVD are useful for initial filtering. Systems outside the affected kernel series can fall out of scope. Systems inside them require a second question: does the
Most enterprise scanners cannot answer all three alone. They can identify kernels and sometimes packages. They usually cannot infer board-level electrical design. That gap is why firmware teams, platform engineers, and security operations need a shared process rather than a ticket handoff.
SUSE has already surfaced the fix in a kernel security update context, which is typical for distribution-scale patch flow. Other vendors will handle it according to their kernel cadence and support model. The practical advice is to follow the vendor kernel stream you actually run, not to cherry-pick upstream commits blindly into production unless that is already your engineering practice.
For appliance owners, the hard part is that vendor firmware often hides the Linux kernel behind a branded interface. You may not know whether an NFC reader, badge terminal, kiosk, or industrial device is running one of the affected kernels until the vendor publishes an advisory. That is not an argument for panic; it is an argument for asking better supplier questions.
The best supplier answer is not “we monitor CVEs.” It is “this product uses or does not use the affected NXP NCI path, and this firmware release contains the relevant stable fix.” Anything less leaves customers doing inference from incomplete public data.
The signal is imperfect, but it is not useless. The entry tells us the affected subsystem, the failure mode, the warning site, the broad version ranges, the CVSS shape, and the stable commits. That is enough for a capable Linux platform team to triage.
What it does not provide is product-level certainty. It does not say whether your badge reader is affected, whether your laptop has the hardware, or whether your vendor’s downstream kernel already carried the change under another commit ID. That missing context is not a database failure so much as a structural limitation of global vulnerability enumeration.
The danger is treating CVE feeds as either gospel or garbage. They are neither. They are a routing layer. They tell you where to look, not what conclusion to reach before understanding your environment.
But “not an emergency” is not the same as “ignore.” Kernel patching is cumulative, and small driver fixes ride alongside more serious changes. If you maintain kernels in the affected ranges, the rational move is to adopt the stable updates through your normal distribution or vendor channel.
For embedded products, the more careful move is to test the patched kernel against suspend, resume, NFC initialization, and any workflows that manipulate the NXP controller. A two-line driver fix can still change timing. The purpose of validation is not to second-guess upstream; it is to make sure your board’s power sequence still behaves under real conditions.
For security teams, the message to leadership should be concise: this is a medium Linux kernel availability issue affecting NXP NCI NFC configurations, not a known remote compromise of Windows systems. Patch through normal channels, prioritize devices with NFC hardware, and ask vendors for product-specific exposure statements where inventory is incomplete.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Small NFC Bug Exposes a Bigger Kernel Reality
A Small NFC Bug Exposes a Bigger Kernel Reality
The Linux kernel description of CVE-2026-31545 is almost comically terse: the NXP NCI NFC driver needed to “allow the firmware and enable GPIOs to sleep.” In practical terms, the driver was using a GPIO operation that assumes the line can be changed immediately, even though some GPIO providers sit behind buses such as I2C where setting a value may sleep.That distinction is second nature to kernel developers and deeply obscure to almost everyone else. A memory-mapped GPIO on a system-on-chip can often be toggled in atomic contexts. A GPIO expander hanging off I2C cannot; the kernel may need to schedule, wait on the bus, and return later. Use the wrong GPIO API in the wrong place, and the kernel complains loudly.
The warning cited in the CVE lands in
gpiolib.c at gpiod_set_value, a clue that this is not a traditional attacker-sends-packet-and-owns-the-box story. It is a driver correctness problem that can degrade availability when a specific hardware arrangement is present. The National Vulnerability Database scored it 5.5 under CVSS 3.1, with local attack vector, low complexity, low privileges, no user interaction, unchanged scope, and high availability impact.That score is the right shape for the bug, but it is also a blunt instrument. For a laptop with no exposed NXP NFC controller, the issue is academic. For an embedded medical, payment, access-control, or industrial device that actually wires an NFC controller through a sleepy GPIO expander, it can be operationally relevant.
The Vulnerability Is Local, but the Blast Radius Is Hardware-Shaped
The most important word in the CVSS vector is local. CVE-2026-31545 does not describe a network-reachable weakness, and nothing in the public description suggests a confidentiality or integrity compromise. The assigned impact is availability, which fits a kernel warning or driver failure path much better than a data-theft narrative.That does not make it irrelevant. Availability bugs in kernel drivers can be serious when the device is a fixed-function appliance and the affected peripheral participates in a business process. NFC is not decorative in systems that use it for identity badges, tap-to-authenticate workflows, reader modules, diagnostics, or provisioning.
The NXP NCI family also points the story away from commodity desktop drama and toward embedded Linux. NCI is the NFC Controller Interface, and NXP NFC controllers are common enough in phones, tablets, point-of-sale equipment, and custom hardware designs that a driver bug can travel through many products without ever becoming a household name.
The uncomfortable part for defenders is that hardware-shaped vulnerabilities rarely map cleanly to inventory systems. A vulnerability scanner can say “Linux kernel version in affected range.” It may not know whether the box has the relevant driver built, whether the device tree or ACPI tables expose that NFC controller, or whether the GPIO line is behind an expander that can sleep. This is where the CPE list becomes a starting point rather than an answer.
The CPE List Is Broad Because Kernel CVEs Are Broad by Design
The NVD enrichment for CVE-2026-31545 lists multiple Linux kernel ranges, including stable-series spans from 5.4, 5.11, 5.16, 6.2, 6.7, 6.13, and 6.19, plus 7.0 release candidates. On paper, that looks alarmingly wide. In reality, it reflects how kernel fixes are backported across maintained branches and how CVE automation tends to express “this source tree contained the vulnerable code before the fix landed.”This is why the “Are we missing a CPE?” prompt on NVD pages is both useful and misleading. The CPEs for upstream Linux are not a product-by-product exploitability verdict. They are a coarse representation of affected kernel versions, not a definitive statement that every system running those versions can trigger the flaw.
For WindowsForum readers, the Microsoft Security Response Center link adds another layer of possible confusion. MSRC’s Security Update Guide includes CVEs assigned by industry partners and advisories beyond classic Windows Patch Tuesday items. The appearance of a Linux kernel CVE in a Microsoft-facing vulnerability portal does not automatically mean Windows itself is vulnerable.
The nuance matters for WSL users, Azure fleet operators, appliance vendors, and anyone maintaining Linux-based infrastructure under a Microsoft-heavy management umbrella. A Windows desktop with WSL installed is not the same thing as an embedded Linux board with an NXP NFC controller. A Linux VM in Azure is not inherently affected unless its kernel, configuration, and hardware exposure line up with the flaw.
The Fix Is Boring in the Best Possible Way
The patch behind CVE-2026-31545 is small: allow the firmware and enable GPIOs to sleep. That likely means replacing non-sleeping GPIO value calls with the sleep-capable variants, the kind of change kernel maintainers prefer because it addresses the bug at the abstraction boundary rather than papering over symptoms.This is the kernel doing what the kernel is supposed to do. It has separate APIs because not all GPIO providers are equal. The bug is not that an I2C expander sleeps; the bug is that the driver treated the GPIO as though it could not.
There is a useful lesson here for people who only encounter vulnerabilities through dashboards. Not every CVE is a dramatic failure of cryptography, memory safety, or authentication. Some are the formal security label attached to a mundane driver fix because a mundane driver fix can prevent denial of service on real systems.
The public record shows several stable patch references, which is also what defenders should want to see. The fix was not merely tossed into a future development branch; it was propagated through supported stable lines. That is the practical difference between “interesting upstream commit” and “something vendors can actually consume.”
Embedded Linux Turns Driver Correctness Into Security Posture
Embedded Linux has spent years absorbing functions once handled by smaller RTOSes, firmware blobs, or dedicated controllers. That has made Linux wildly capable, but it has also put the kernel in charge of awkward hardware choreography: regulators, reset lines, wake pins, GPIO expanders, power domains, runtime suspend, and bus ordering.CVE-2026-31545 lives precisely in that choreography. The NFC controller needs firmware and enable GPIO lines. Those lines may be served by an expander. The expander may require I2C traffic. I2C traffic may sleep. A driver path that assumes immediate GPIO access collides with the platform’s actual electrical design.
For sysadmins used to servers, this can feel like a niche footnote. For product security teams, it is daily life. The same upstream kernel version can behave very differently across two boards because the device tree, ACPI description, peripheral mix, and vendor patches are different. Vulnerability management becomes less about matching version numbers and more about understanding product construction.
That is why kernel CVEs sometimes look overbroad and underexplained at the same time. The upstream project has to publish enough information for stable consumers to act, while avoiding a bespoke threat model for every board design on Earth. The result is a CVE entry that names a driver and a warning, leaving downstream vendors to decide whether their product is actually exposed.
The “Medium” Label Can Hide Operational Pain
CVSS 5.5 medium severity will not set off the same alarms as a 9.8 remote exploit. It should not. But medium-severity availability flaws can still produce miserable incident tickets when they affect hardware that people expect to behave like infrastructure.Imagine an access-control kiosk that intermittently loses NFC functionality after a suspend-resume sequence. Imagine a field device that logs kernel warnings until watchdog policy intervenes. Imagine a medical cart or industrial handheld where NFC is part of identity, configuration, or workflow. The attacker model may be local, but the business disruption can be real.
The key is not to inflate the vulnerability. There is no public basis for calling this a remote compromise or a privilege-escalation bug from the description alone. The key is to resist the opposite mistake: dismissing it because it lacks headline-grade impact categories.
Availability is often where hardware bugs announce themselves first. A kernel warning may be the visible symptom; the real cost is a device that cannot reliably perform the job it was sold to do. For enterprise defenders, that means the triage question should be “Do we run affected kernels on devices with this NFC path?” rather than “Is this scary enough to make the front page?”
Why Windows People Should Still Pay Attention
At first glance, this is not a Windows story. It is a Linux kernel NFC driver issue, assigned by kernel.org, enriched by NVD, and fixed through upstream stable patches. But WindowsForum’s audience increasingly lives in hybrid environments where “Windows shop” no longer means “Windows-only estate.”Windows admins manage Linux servers in Azure, Linux appliances behind Windows clients, WSL images on developer workstations, and fleets of edge devices monitored through Microsoft tooling. They also read the MSRC guide, where industry CVEs can appear beside Microsoft product vulnerabilities. That creates a real risk of overreaction or misclassification.
The right posture is disciplined separation. If you are responsible for Windows endpoints only, CVE-2026-31545 is probably noise unless those endpoints depend on a Linux subsystem or appliance you also own. If you operate Linux devices, especially embedded systems with NFC hardware, it belongs in the normal kernel patch queue.
For WSL specifically, the public description does not suggest a meaningful path unless the environment exposes the affected kernel driver and relevant hardware arrangement, which is not how ordinary WSL deployments work. Treating this as a WSL emergency would confuse the asset model. Treating it as irrelevant across all Microsoft-managed estates would be just as lazy.
Patch Management Needs a Hardware Column
The natural instinct is to answer every CVE with a version comparison: vulnerable before this, fixed after that. CVE-2026-31545 resists that tidy workflow because exploitability depends heavily on configuration. Kernel version matters, but so do driver enablement, hardware presence, board wiring, and whether GPIO lines are backed by a sleep-capable provider.This is where mature organizations have an advantage. A good hardware bill of materials, kernel configuration archive, and device-tree inventory can turn an ambiguous kernel CVE into a quick decision. A poor inventory turns it into a week of Slack archaeology and vendor emails.
The affected ranges published by NVD are useful for initial filtering. Systems outside the affected kernel series can fall out of scope. Systems inside them require a second question: does the
nxp-nci NFC driver exist and participate in the product? A third question follows: are the relevant GPIOs provided in a way that triggers the sleeping-GPIO path?Most enterprise scanners cannot answer all three alone. They can identify kernels and sometimes packages. They usually cannot infer board-level electrical design. That gap is why firmware teams, platform engineers, and security operations need a shared process rather than a ticket handoff.
Vendors Will Decide How Real This Is for Their Products
For downstream Linux distributions, the fix is straightforward: carry the stable patch when updating affected kernel branches. For hardware vendors, the decision tree is more specific. If their product does not enable the driver or lacks the NFC hardware path, the advisory may be documentation-only. If it does, they need to ship a patched kernel or provide clear mitigation guidance.SUSE has already surfaced the fix in a kernel security update context, which is typical for distribution-scale patch flow. Other vendors will handle it according to their kernel cadence and support model. The practical advice is to follow the vendor kernel stream you actually run, not to cherry-pick upstream commits blindly into production unless that is already your engineering practice.
For appliance owners, the hard part is that vendor firmware often hides the Linux kernel behind a branded interface. You may not know whether an NFC reader, badge terminal, kiosk, or industrial device is running one of the affected kernels until the vendor publishes an advisory. That is not an argument for panic; it is an argument for asking better supplier questions.
The best supplier answer is not “we monitor CVEs.” It is “this product uses or does not use the affected NXP NCI path, and this firmware release contains the relevant stable fix.” Anything less leaves customers doing inference from incomplete public data.
The CVE Machine Is Working, Even When It Looks Messy
Kernel CVEs have become more numerous and more mechanical in recent years, and that has annoyed many administrators. They see a flood of medium and low issues, sparse descriptions, and long CPE ranges, then conclude that the signal has collapsed. CVE-2026-31545 shows a more complicated truth.The signal is imperfect, but it is not useless. The entry tells us the affected subsystem, the failure mode, the warning site, the broad version ranges, the CVSS shape, and the stable commits. That is enough for a capable Linux platform team to triage.
What it does not provide is product-level certainty. It does not say whether your badge reader is affected, whether your laptop has the hardware, or whether your vendor’s downstream kernel already carried the change under another commit ID. That missing context is not a database failure so much as a structural limitation of global vulnerability enumeration.
The danger is treating CVE feeds as either gospel or garbage. They are neither. They are a routing layer. They tell you where to look, not what conclusion to reach before understanding your environment.
The Practical Response Is Narrow, Not Dramatic
Organizations should resist turning CVE-2026-31545 into a broad Linux emergency. The facts do not support that. The vulnerability is local, availability-focused, and tied to a specific NFC driver behavior around sleep-capable GPIOs.But “not an emergency” is not the same as “ignore.” Kernel patching is cumulative, and small driver fixes ride alongside more serious changes. If you maintain kernels in the affected ranges, the rational move is to adopt the stable updates through your normal distribution or vendor channel.
For embedded products, the more careful move is to test the patched kernel against suspend, resume, NFC initialization, and any workflows that manipulate the NXP controller. A two-line driver fix can still change timing. The purpose of validation is not to second-guess upstream; it is to make sure your board’s power sequence still behaves under real conditions.
For security teams, the message to leadership should be concise: this is a medium Linux kernel availability issue affecting NXP NCI NFC configurations, not a known remote compromise of Windows systems. Patch through normal channels, prioritize devices with NFC hardware, and ask vendors for product-specific exposure statements where inventory is incomplete.
The Signal Hidden in the GPIO Warning
There are a few concrete conclusions worth carrying forward from this otherwise small CVE.- CVE-2026-31545 affects the Linux kernel’s NXP NCI NFC driver path, not Microsoft Windows itself.
- The public severity is medium, with a local attack vector and high availability impact under CVSS 3.1.
- The practical exposure depends on hardware and configuration, especially whether the affected NFC driver uses GPIOs that can sleep through providers such as I2C expanders.
- The fix is available through upstream stable kernel patches and should be consumed through normal distribution, vendor, or product firmware update channels.
- Asset owners should prioritize embedded Linux devices, NFC-enabled appliances, and vendor-managed hardware over ordinary Windows desktops or generic WSL deployments.
- The presence of the CVE in Microsoft’s Security Update Guide should be read as vulnerability visibility, not proof of a Windows product flaw.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center