CVE-2026-31546 is a medium-severity Linux kernel denial-of-service flaw, published by NVD on April 24, 2026 and modified on April 28, that lets a local privileged user crash affected systems through the bonding driver’s debugfs RLB hash display path. The bug is small enough to fit in a code-review margin: one debug routine trusted a pointer that other bonding code already knew could legitimately be NULL. That is precisely why it matters. Modern infrastructure does not fail only because of baroque exploit chains; it also fails when an observability hook forgets the rules of the subsystem it is observing.
The vulnerability sits in the Linux bonding driver, specifically the receive load balancing machinery used by adaptive load balancing mode. When a slave interface is removed and no replacement is available, the bonding code can intentionally leave an RLB hash-table entry on the used list with its
The crash happens because
That distinction matters because debugfs often feels less “real” than a network packet parser or filesystem write path. It is not part of the glossy application surface. But debugfs is still kernel code, and when it touches live subsystem state, it inherits the same obligation as the fast path: validate what you are about to use.
That makes CVE-2026-31546 a different class of problem from the usual “send malicious traffic, trigger kernel bug” networking vulnerability. The vulnerable function is an introspection path, the sort of thing administrators, monitoring agents, diagnostics scripts, or test harnesses may touch while investigating a bonded interface. It is local, it requires privileges, and it is not a remote unauthenticated compromise.
NVD’s CVSS 3.1 vector reflects that: local attack vector, low complexity, low privileges required, no user interaction, unchanged scope, no confidentiality or integrity impact, and high availability impact. The resulting 5.5 medium score is not glamorous. But in the kernel, availability impact is not academic. A NULL pointer dereference in kernel space is often the difference between an annoying bug and a reboot.
The uncomfortable part is that the vulnerable code was not doing something exotic. It was displaying state. The table already allowed entries with no slave; other bonding iterators handled that state correctly. The debugfs routine simply lagged behind the subsystem’s own invariants.
CVE-2026-31546 is tied to the bonding driver’s ALB/RLB behavior. RLB, or receive load balancing, tracks clients and assigned slave devices so inbound traffic can be distributed more intelligently. When the bond changes shape, the driver must reconcile existing client entries with available interfaces. Sometimes that means keeping a hash entry while acknowledging there is no current slave to associate with it.
That is the crux of the bug.
This is the sort of internal contract drift that accumulates in mature kernel subsystems. The fast-path code evolves to handle more edge cases. The maintenance path evolves later, or not at all. Then a debug display function becomes the least-tested consumer of a complicated state machine.
For WindowsForum readers, that is the real reason to care. The modern Windows administrator is often also a Linux-adjacent administrator, whether by choice or by procurement accident. A vulnerability in the Linux bonding driver may sound far away from a Windows desktop, but it can matter in Hyper-V labs, Azure infrastructure, security appliances, NAS boxes, CI runners, and WSL-adjacent workflows depending on the kernel and configuration in use.
That does not mean every Windows user is exposed. A typical Windows 11 laptop is not suddenly vulnerable because MSRC lists a Linux CVE. Nor does this imply that WSL users should panic; exposure depends on the kernel build, whether the affected bonding code is present, whether the vulnerable path is reachable, and whether the relevant debugfs interface is mounted and accessible.
The better read is that Microsoft’s security ecosystem now has to track Linux with the same seriousness it tracks Exchange, Office, and Windows Server. That is healthy. It also makes triage noisier, because “Microsoft-listed” no longer means “Microsoft-authored code.”
That spread tells administrators something important: do not triage this solely by reading the upstream version number. Distribution kernels are patched, backported, configured differently, and shipped with vendor-specific ABI policies. A machine running an older-looking enterprise kernel may already include the fix. A machine running a fresher custom kernel may not.
The presence of multiple stable-tree patch references also reflects the Linux kernel’s normal backport process. The same logical fix is carried into several supported branches, because the stable kernel ecosystem is not one line but a family tree. Security scanners that flatten that family tree into a single vulnerable/not-vulnerable version comparison can be wrong in both directions.
For IT teams, the sane workflow is familiar: check the vendor advisory for the distribution or appliance, confirm the installed kernel package, and verify whether the bonding fix has landed in that vendor’s update stream. If you manage self-built kernels, the answer is less comfortable: you own the backport or the upgrade.
The privilege requirement lowers the severity, but it does not erase the operational risk. Local privileged access is not rare in real environments. Monitoring agents run with elevated permissions. Break-glass troubleshooting sessions happen during outages. Container hosts, hypervisors, and network appliances often carry dense layers of automation around privileged interfaces. If a read of a diagnostic file can crash the host, the problem belongs in the patch queue.
There is also an incident-response angle. Debug paths are most likely to be touched when something else is already going wrong. If a bonded interface is misbehaving and an administrator reads the wrong diagnostic file, CVE-2026-31546 can turn a network troubleshooting session into a system availability event. That is the kind of bug that rarely makes exploit headlines but still ruins a maintenance window.
Kernel developers have long wrestled with this tradeoff. Debugfs is invaluable because it exposes implementation detail without forcing every internal knob into a stable ABI. The cost is that those implementation details must still be kept safe enough not to crash the machine when inspected.
But risk is not just score multiplied by panic. A medium-severity kernel denial-of-service in a feature used on high-availability hosts can outrank a more dramatic vulnerability in a component you do not run. Bonded interfaces are common in servers precisely because administrators want resilience. A crash in that layer has an irony sharp enough to draw blood.
The other triage wrinkle is exploitability in the everyday sense. This does not require winning a race in a speculative execution side channel or chaining half a dozen primitives. The vulnerable path is conceptually simple: reach a state with an RLB entry whose slave is NULL, then read the debugfs representation that dereferences it. The barrier is configuration and privilege, not complexity.
That is why the practical response should be measured but not dismissive. Patch during the next appropriate kernel update cycle, sooner for systems using bonding with ALB/RLB and exposed debugfs access. Restrict debugfs on production systems where possible. Treat local privileged crash bugs as reliability defects with security labels, because that is how they tend to show up in the real world.
The lesson is larger than the diff. Kernel subsystems increasingly expose rich internal state to observability tooling, and the quality of that tooling matters. A diagnostic path that assumes away edge cases can become a denial-of-service path. A helper written for humans can still be reached by machines at scale.
This also illustrates why the kernel’s CVE process now produces a steady stream of small, specific vulnerability records. Some administrators complain that the flood of kernel CVEs makes prioritization harder, and they are not wrong. But the alternative is worse: hiding reliability-impacting kernel bugs until they are rediscovered in production, stripped of context and harder to map to fixes.
CVE-2026-31546 is therefore not a headline-grabbing Linux crisis. It is a tidy case study in how mature infrastructure fails: through an overlooked invariant, in a maintenance path, under a configuration that many people assume is boring.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A One-Line Fix Exposes a Bigger Kernel Habit
A One-Line Fix Exposes a Bigger Kernel Habit
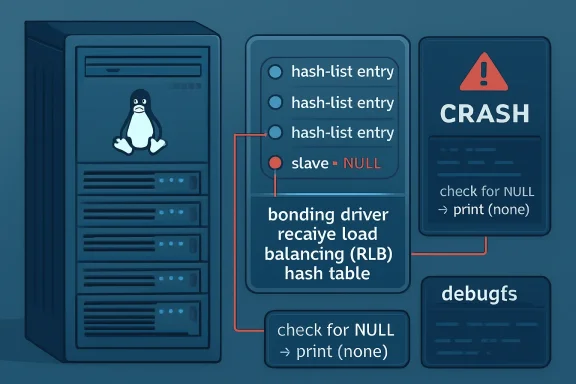
The vulnerability sits in the Linux bonding driver, specifically the receive load balancing machinery used by adaptive load balancing mode. When a slave interface is removed and no replacement is available, the bonding code can intentionally leave an RLB hash-table entry on the used list with its slave pointer set to NULL. That is not corruption. It is an expected internal state.The crash happens because
bond_debug_rlb_hash_show, the debugfs display function for that table, walked the same structure and dereferenced client_info->slave without first checking whether a slave existed. The kernel fix adds the missing guard and prints (none) for entries without an assigned slave. In security terms, this is CWE-476, a NULL pointer dereference. In operational terms, it is a kernel panic waiting behind a diagnostics file.That distinction matters because debugfs often feels less “real” than a network packet parser or filesystem write path. It is not part of the glossy application surface. But debugfs is still kernel code, and when it touches live subsystem state, it inherits the same obligation as the fast path: validate what you are about to use.
The Crash Path Runs Through the Tooling, Not the Wire
The reported crash trace lands inbond_debug_rlb_hash_show, then flows through seq_read_iter, seq_read, full_proxy_read, vfs_read, and the normal syscall path. In plain English, the system crashes when the kernel tries to render the bonding driver’s RLB hash table for a reader. The packet network is not the direct trigger; the act of inspection is.That makes CVE-2026-31546 a different class of problem from the usual “send malicious traffic, trigger kernel bug” networking vulnerability. The vulnerable function is an introspection path, the sort of thing administrators, monitoring agents, diagnostics scripts, or test harnesses may touch while investigating a bonded interface. It is local, it requires privileges, and it is not a remote unauthenticated compromise.
NVD’s CVSS 3.1 vector reflects that: local attack vector, low complexity, low privileges required, no user interaction, unchanged scope, no confidentiality or integrity impact, and high availability impact. The resulting 5.5 medium score is not glamorous. But in the kernel, availability impact is not academic. A NULL pointer dereference in kernel space is often the difference between an annoying bug and a reboot.
The uncomfortable part is that the vulnerable code was not doing something exotic. It was displaying state. The table already allowed entries with no slave; other bonding iterators handled that state correctly. The debugfs routine simply lagged behind the subsystem’s own invariants.
Bonding Is Boring Until It Becomes the Blast Radius
Linux bonding is one of those features that disappears into the plumbing when it works. It aggregates physical interfaces, provides redundancy, and underpins countless server, storage, virtualization, and lab environments. Adaptive load balancing is not the default choice in every shop, but bonding itself is widespread enough that kernel fixes in this area deserve attention from more than network-driver specialists.CVE-2026-31546 is tied to the bonding driver’s ALB/RLB behavior. RLB, or receive load balancing, tracks clients and assigned slave devices so inbound traffic can be distributed more intelligently. When the bond changes shape, the driver must reconcile existing client entries with available interfaces. Sometimes that means keeping a hash entry while acknowledging there is no current slave to associate with it.
That is the crux of the bug.
rlb_clear_slave deliberately leaves used-list entries behind with slave set to NULL when no replacement is available. Other code paths knew this and avoided dereferencing the missing slave. The debugfs renderer did not.This is the sort of internal contract drift that accumulates in mature kernel subsystems. The fast-path code evolves to handle more edge cases. The maintenance path evolves later, or not at all. Then a debug display function becomes the least-tested consumer of a complicated state machine.
Microsoft’s Name on the Page Is a Reminder, Not a Windows Bug
The user-facing source here comes through Microsoft’s Security Update Guide, but the vulnerability is not a Windows kernel issue. It is a Linux kernel CVE assigned by kernel.org and tracked by NVD, with the affected product listed as the Linux kernel. Microsoft’s inclusion is still notable because Linux is now part of the practical Microsoft estate: WSL, Azure-hosted Linux, Linux-based appliances, container hosts, AKS nodes, and partner images all blur the old platform boundaries.For WindowsForum readers, that is the real reason to care. The modern Windows administrator is often also a Linux-adjacent administrator, whether by choice or by procurement accident. A vulnerability in the Linux bonding driver may sound far away from a Windows desktop, but it can matter in Hyper-V labs, Azure infrastructure, security appliances, NAS boxes, CI runners, and WSL-adjacent workflows depending on the kernel and configuration in use.
That does not mean every Windows user is exposed. A typical Windows 11 laptop is not suddenly vulnerable because MSRC lists a Linux CVE. Nor does this imply that WSL users should panic; exposure depends on the kernel build, whether the affected bonding code is present, whether the vulnerable path is reachable, and whether the relevant debugfs interface is mounted and accessible.
The better read is that Microsoft’s security ecosystem now has to track Linux with the same seriousness it tracks Exchange, Office, and Windows Server. That is healthy. It also makes triage noisier, because “Microsoft-listed” no longer means “Microsoft-authored code.”
The Affected-Version Story Is Messier Than the Bug
NVD’s affected CPE data, as of the April 28 update, paints a broad picture. It lists vulnerable Linux kernel ranges beginning with 2.6.38.1 up to fixed long-term releases including 5.10.253, 5.15.203, 6.1.167, 6.6.130, 6.12.78, 6.18.20, and 6.19.10, along with 7.0 release candidates before rc5. Ubuntu’s tracker, meanwhile, marks several Ubuntu kernel packages as needing evaluation or not in release and identifies the mainline fix associated with 7.0-rc5.That spread tells administrators something important: do not triage this solely by reading the upstream version number. Distribution kernels are patched, backported, configured differently, and shipped with vendor-specific ABI policies. A machine running an older-looking enterprise kernel may already include the fix. A machine running a fresher custom kernel may not.
The presence of multiple stable-tree patch references also reflects the Linux kernel’s normal backport process. The same logical fix is carried into several supported branches, because the stable kernel ecosystem is not one line but a family tree. Security scanners that flatten that family tree into a single vulnerable/not-vulnerable version comparison can be wrong in both directions.
For IT teams, the sane workflow is familiar: check the vendor advisory for the distribution or appliance, confirm the installed kernel package, and verify whether the bonding fix has landed in that vendor’s update stream. If you manage self-built kernels, the answer is less comfortable: you own the backport or the upgrade.
Debugfs Is Not a Security Boundary, But It Is Still a Risk Surface
There is a temptation to wave away debugfs-triggered issues because debugfs is meant for debugging and is often restricted to privileged users. That instinct is partly right and partly dangerous. Debugfs should not be treated as a hardened user API, and many production systems avoid mounting it broadly. But code reachable through debugfs still executes in kernel context.The privilege requirement lowers the severity, but it does not erase the operational risk. Local privileged access is not rare in real environments. Monitoring agents run with elevated permissions. Break-glass troubleshooting sessions happen during outages. Container hosts, hypervisors, and network appliances often carry dense layers of automation around privileged interfaces. If a read of a diagnostic file can crash the host, the problem belongs in the patch queue.
There is also an incident-response angle. Debug paths are most likely to be touched when something else is already going wrong. If a bonded interface is misbehaving and an administrator reads the wrong diagnostic file, CVE-2026-31546 can turn a network troubleshooting session into a system availability event. That is the kind of bug that rarely makes exploit headlines but still ruins a maintenance window.
Kernel developers have long wrestled with this tradeoff. Debugfs is invaluable because it exposes implementation detail without forcing every internal knob into a stable ABI. The cost is that those implementation details must still be kept safe enough not to crash the machine when inspected.
The CVSS Score Is Correct, But It Is Not the Whole Triage
A 5.5 medium score is reasonable. There is no disclosed confidentiality impact, no integrity impact, no remote path in the NVD vector, and no need to pretend this is a wormable catastrophe. The bug is a local availability issue in a specific kernel subsystem.But risk is not just score multiplied by panic. A medium-severity kernel denial-of-service in a feature used on high-availability hosts can outrank a more dramatic vulnerability in a component you do not run. Bonded interfaces are common in servers precisely because administrators want resilience. A crash in that layer has an irony sharp enough to draw blood.
The other triage wrinkle is exploitability in the everyday sense. This does not require winning a race in a speculative execution side channel or chaining half a dozen primitives. The vulnerable path is conceptually simple: reach a state with an RLB entry whose slave is NULL, then read the debugfs representation that dereferences it. The barrier is configuration and privilege, not complexity.
That is why the practical response should be measured but not dismissive. Patch during the next appropriate kernel update cycle, sooner for systems using bonding with ALB/RLB and exposed debugfs access. Restrict debugfs on production systems where possible. Treat local privileged crash bugs as reliability defects with security labels, because that is how they tend to show up in the real world.
The Fix Is Small Because the Lesson Is Not
The patch’s behavior is almost boring: check whether the slave pointer exists, and if it does not, print(none). That is the right fix because it aligns the debug output with the driver’s intended state model. The absence of a slave is not an exceptional condition at that point; it is a value that needs representation.The lesson is larger than the diff. Kernel subsystems increasingly expose rich internal state to observability tooling, and the quality of that tooling matters. A diagnostic path that assumes away edge cases can become a denial-of-service path. A helper written for humans can still be reached by machines at scale.
This also illustrates why the kernel’s CVE process now produces a steady stream of small, specific vulnerability records. Some administrators complain that the flood of kernel CVEs makes prioritization harder, and they are not wrong. But the alternative is worse: hiding reliability-impacting kernel bugs until they are rediscovered in production, stripped of context and harder to map to fixes.
CVE-2026-31546 is therefore not a headline-grabbing Linux crisis. It is a tidy case study in how mature infrastructure fails: through an overlooked invariant, in a maintenance path, under a configuration that many people assume is boring.
The Bonding Bug That Belongs in the Next Kernel Window
This is not a drop-everything emergency for most WindowsForum readers, but it is exactly the kind of vulnerability that should survive the first triage pass instead of being buried under higher-scoring noise.- CVE-2026-31546 affects the Linux kernel bonding driver and can cause a local denial of service through a NULL pointer dereference in
bond_debug_rlb_hash_show. - The bug is triggered through a debugfs read path after RLB state contains an entry with no assigned slave, which the driver otherwise treats as valid.
- NVD rates the vulnerability as CVSS 3.1 5.5 medium, with local access, low complexity, low privileges, no user interaction, and high availability impact.
- Fixed kernel lines include stable updates such as 5.10.253, 5.15.203, 6.1.167, 6.6.130, 6.12.78, 6.18.20, 6.19.10, and the 7.0-rc5 mainline candidate.
- Administrators should rely on their distribution or appliance vendor’s kernel advisory rather than upstream version strings alone, because backports can change the real exposure.
- Production systems using Linux bonding, especially with debugfs mounted or monitored, deserve faster review than generic desktops or systems without the bonding driver in use.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center