CVE-2026-31548 is the kind of Linux kernel flaw that looks narrow at first glance but carries broad operational meaning for anyone managing Wi-Fi-enabled Linux systems, embedded devices, lab workstations, or Linux workloads tied into Windows-heavy environments. The bug sits in cfg80211, the kernel’s wireless configuration layer, and involves a race between an asynchronous cleanup task and interface teardown. Kernel.org rates the issue High under CVSS 3.1 with a 7.8 score, reflecting the uncomfortable reality that a local, low-complexity trigger can end in undefined driver behavior, crashes, and potentially deeper compromise if paired with other weaknesses.
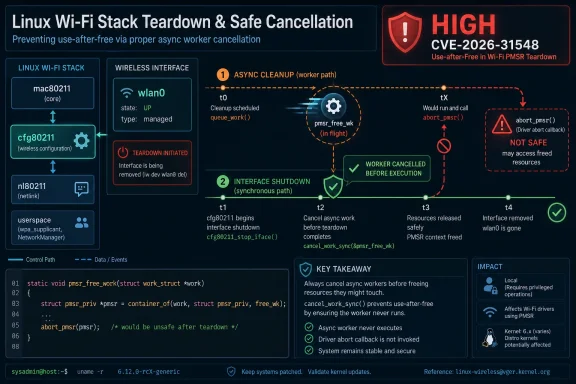
The vulnerability centers on PMSR, or peer measurement service request handling, a Wi-Fi subsystem feature used for measurement-oriented operations such as positioning and radio diagnostics. In this case, the problem emerges when the nl80211 socket that originated a PMSR request closes while the wireless interface is also being torn down. One path schedules cleanup work asynchronously, while another directly processes an abort during device shutdown.
That overlap creates the race. The scheduled work item, pmsr_free_wk, can remain pending even after cfg80211_pmsr_wdev_down() has begun interface teardown and called the abort processing path directly. If the delayed work later executes, it may call into a driver’s abort_pmsr callback after the relevant interface has already been removed.
The fix is conceptually small but technically important: cancel the pending work synchronously before proceeding with abort handling during interface shutdown. In kernel engineering terms, this is classic lifetime management: no callback should operate on an object whose ownership, registration state, or backing driver context has already disappeared. That small ordering guarantee is the difference between controlled teardown and post-removal driver execution.
CVE-2026-31548 was published by NVD on April 24, 2026, modified on April 27, 2026, and sourced from kernel.org as the assigning authority. NVD’s own enrichment remains incomplete in places, while the kernel.org CNA score currently lists the vulnerability as CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, making this a local but serious kernel-level issue.
The severity comes from where the bug lives: inside the Linux kernel, at the boundary between generic wireless infrastructure and hardware-specific drivers. If a local user or process can trigger the right sequence of PMSR request closure and interface teardown, the driver may receive an abort callback after the wireless device context is already gone. That is exactly the kind of use-after-teardown pattern that can produce kernel crashes and, in worse cases, memory corruption.
Key reasons this issue deserves attention include:
That is normal kernel design. Work queues allow cleanup to happen outside a hot path or lock-sensitive context. The trouble starts when the wireless interface is concurrently torn down before the scheduled work item actually runs.
This is not just a programming neatness issue. Wireless drivers often maintain state tied to firmware, PCIe or USB devices, netdev objects, and power-management transitions. Calling back into that code after teardown may expose stale pointers, invalid locks, unregistered objects, or hardware state that no longer matches software assumptions.
That breadth is not unusual for kernel CVEs. A bug introduced in a shared subsystem can travel through long-term support, stable, and development series for years. The wireless stack is especially sensitive because the same cfg80211 layer supports many drivers and distributions.
Administrators should verify:
The most visible impact is availability: a kernel crash can take down the system. But CVSS allows for broader impact when a flaw may lead to memory corruption or unsafe driver callbacks in privileged kernel context. The score is not proof of a polished privilege-escalation exploit, but it signals that defenders should not dismiss the bug as a mere nuisance.
For defenders, that means policy should not rely on a single field. A vulnerability scanner may show “NVD score unavailable” even while the assigning authority has already marked the issue as high severity. Conversely, early CPE data can be noisy, broad, or missing downstream backport nuance.
Practical interpretation should consider:
Even Microsoft-heavy environments depend on Linux in practical ways. Azure hosts Linux virtual machines, network appliances, Kubernetes nodes, and container images. On the desktop side, Windows users may run Linux through WSL, though typical WSL configurations do not expose raw Wi-Fi driver control in the same way a native Linux kernel does.
Enterprise risk is more nuanced:
Still, power users should not ignore it. Linux laptops frequently depend on Wi-Fi, sleep and resume, NetworkManager transitions, driver reloads, and rapid interface resets. Bugs in these paths can surface as intermittent crashes that are hard to diagnose, especially if a system is already running experimental kernels or release candidates.
Desktop users should consider:
Synchronous cancellation matters because merely marking work as canceled is not enough if the work is already running on another CPU. The kernel needs to ensure that pending or in-progress execution has fully drained. Otherwise, the teardown path could still race with code that believes the interface remains valid.
That separation demands strong lifetime rules:
The Debian security tracker, for example, shows different status across releases, with newer development branches moving ahead faster than stable releases. Red Hat’s Bugzilla entry tracks the issue as a security response item and mirrors the upstream description. These public trackers help, but administrators should still treat the distribution’s own fixed package advisory as the authoritative operational answer.
Scanner teams should also beware of false positives and false negatives. A raw CPE match may flag a kernel that is actually patched through backporting, while a custom vendor kernel may escape detection despite carrying the vulnerable code. For appliances, the vendor’s firmware advisory often matters more than the upstream kernel line.
This is especially relevant to Wi-Fi because wireless stacks are event-heavy. Interfaces appear and disappear, firmware restarts, devices sleep and resume, regulatory changes arrive, scans overlap with connection attempts, and user-space network managers constantly open and close control sockets. Every one of those transitions is a chance for a race.
The recurring risk factors include:
For Microsoft, this advisory’s appearance in security guidance reflects the company’s broader role in a mixed operating-system world. Windows is still the desktop center for many organizations, but Microsoft’s cloud, developer, and security products increasingly inventory and manage Linux assets. The boundary between Windows security and Linux security is now operational, not philosophical.
The ecosystem impact includes:
However, operational signs may still appear. Kernel oops messages, Wi-Fi driver crashes, sudden reboots, or logs mentioning cfg80211, nl80211, PMSR, or driver abort paths could warrant investigation. Such evidence is not proof of exploitation, but it may help identify unstable systems or failed attempts to exercise the race.
Recommended actions include:
For WindowsForum readers, the larger story is the continued convergence of Windows, Linux, cloud, and endpoint security operations. A Linux Wi-Fi CVE can appear in Microsoft security tooling, affect developer laptops that authenticate into Windows domains, and matter to Azure-connected inventory systems. That does not make it a Windows flaw, but it does make it part of the same security conversation.
Watch these items over the coming days and weeks:
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The vulnerability centers on PMSR, or peer measurement service request handling, a Wi-Fi subsystem feature used for measurement-oriented operations such as positioning and radio diagnostics. In this case, the problem emerges when the nl80211 socket that originated a PMSR request closes while the wireless interface is also being torn down. One path schedules cleanup work asynchronously, while another directly processes an abort during device shutdown.That overlap creates the race. The scheduled work item, pmsr_free_wk, can remain pending even after cfg80211_pmsr_wdev_down() has begun interface teardown and called the abort processing path directly. If the delayed work later executes, it may call into a driver’s abort_pmsr callback after the relevant interface has already been removed.
The fix is conceptually small but technically important: cancel the pending work synchronously before proceeding with abort handling during interface shutdown. In kernel engineering terms, this is classic lifetime management: no callback should operate on an object whose ownership, registration state, or backing driver context has already disappeared. That small ordering guarantee is the difference between controlled teardown and post-removal driver execution.
CVE-2026-31548 was published by NVD on April 24, 2026, modified on April 27, 2026, and sourced from kernel.org as the assigning authority. NVD’s own enrichment remains incomplete in places, while the kernel.org CNA score currently lists the vulnerability as CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, making this a local but serious kernel-level issue.
Why This Wi-Fi Kernel Bug Matters
At one level, CVE-2026-31548 is not a remote wormable Wi-Fi flaw. It does not describe a nearby attacker breaking into a laptop over the air without credentials. That distinction matters, because administrators should avoid treating every wireless CVE as an over-the-air catastrophe.The severity comes from where the bug lives: inside the Linux kernel, at the boundary between generic wireless infrastructure and hardware-specific drivers. If a local user or process can trigger the right sequence of PMSR request closure and interface teardown, the driver may receive an abort callback after the wireless device context is already gone. That is exactly the kind of use-after-teardown pattern that can produce kernel crashes and, in worse cases, memory corruption.
Local Does Not Mean Low Priority
Local privilege requirements often lead teams to delay fixes, especially when no public exploit is circulating. That can be a mistake for kernel vulnerabilities because local access is not rare on developer systems, shared lab machines, containers with expanded device access, or kiosks with limited user shells.Key reasons this issue deserves attention include:
- Kernel-space execution raises the stakes beyond ordinary application crashes.
- Low attack complexity means exploitation does not require an elaborate timing environment in principle.
- No user interaction is required once a capable local process is running.
- Wi-Fi subsystem availability may be critical for laptops, tablets, point-of-sale devices, and field systems.
- Driver diversity means behavior may vary across chipsets and distributions.
Technical Root Cause: Asynchronous Work Meets Teardown
The core failure pattern is a race between deferred cleanup and immediate device shutdown. When the originating nl80211 socket closes, cfg80211_release_pmsr() marks the PMSR request as no longer associated with that socket by setting its port ID to zero. It then schedules pmsr_free_wk to handle the abort asynchronously.That is normal kernel design. Work queues allow cleanup to happen outside a hot path or lock-sensitive context. The trouble starts when the wireless interface is concurrently torn down before the scheduled work item actually runs.
The Dangerous Sequence
The vulnerable timeline can be described in five steps:- A local process initiates a PMSR request through nl80211.
- The originating nl80211 socket closes, triggering asynchronous PMSR cleanup.
- The kernel schedules pmsr_free_wk, but the work does not run immediately.
- The wireless interface goes down, and cfg80211_pmsr_wdev_down() directly calls the abort processor.
- The already scheduled work later runs and may invoke the driver callback after the interface is removed.
This is not just a programming neatness issue. Wireless drivers often maintain state tied to firmware, PCIe or USB devices, netdev objects, and power-management transitions. Calling back into that code after teardown may expose stale pointers, invalid locks, unregistered objects, or hardware state that no longer matches software assumptions.
Affected Kernel Lines and Patch Scope
The NVD change history lists affected Linux kernel ranges spanning multiple supported and development branches. The vulnerable ranges include kernels from 5.0.1 up to before 6.1.167, 6.2 up to before 6.6.130, 6.7 up to before 6.12.78, 6.13 up to before 6.18.20, and 6.19 up to before 6.19.10. It also identifies several 7.0 release candidates as affected, from rc1 through rc7.That breadth is not unusual for kernel CVEs. A bug introduced in a shared subsystem can travel through long-term support, stable, and development series for years. The wireless stack is especially sensitive because the same cfg80211 layer supports many drivers and distributions.
What Administrators Should Check
The most important question is not whether a kernel version string appears in a generic CPE list. The real question is whether your distribution has shipped the relevant backport. Enterprise distributions often carry fixes without moving to the exact upstream minor version listed in a public database.Administrators should verify:
- Running kernel version, not just installed kernel packages.
- Distribution security advisories, especially for enterprise and LTS channels.
- Vendor backport notes, because patched kernels may retain older upstream numbering.
- Wi-Fi hardware exposure, including laptops, embedded systems, and test rigs.
- Privileged local access paths, including users who can manipulate wireless interfaces.
- WSL or virtualization assumptions, because not every Linux kernel context exposes Wi-Fi device control.
Severity: Reading the CVSS Signal Correctly
Kernel.org’s CVSS 3.1 vector assigns CVE-2026-31548 a 7.8 High rating. The vector says exploitation is local, requires low privileges, has low attack complexity, requires no user interaction, and can affect confidentiality, integrity, and availability at high impact. That is an aggressive but understandable scoring profile for a kernel-space race with undefined behavior.The most visible impact is availability: a kernel crash can take down the system. But CVSS allows for broader impact when a flaw may lead to memory corruption or unsafe driver callbacks in privileged kernel context. The score is not proof of a polished privilege-escalation exploit, but it signals that defenders should not dismiss the bug as a mere nuisance.
Why NVD and CNA Details May Differ
The NVD entry indicates that NIST enrichment was still incomplete or not fully assessed in parts of the record, while the CNA-provided kernel.org score is available. This split is increasingly common in modern vulnerability management. CNA records may arrive quickly, while NVD enrichment, CPE mapping, CWE classification, and scoring can lag or change.For defenders, that means policy should not rely on a single field. A vulnerability scanner may show “NVD score unavailable” even while the assigning authority has already marked the issue as high severity. Conversely, early CPE data can be noisy, broad, or missing downstream backport nuance.
Practical interpretation should consider:
- CNA severity as the first authoritative signal.
- Distribution advisories as the operational patch truth.
- NVD CPE ranges as useful but not definitive inventory hints.
- Exploitability context based on local access, Wi-Fi exposure, and driver availability.
- Business criticality of systems that rely on wireless networking.
Enterprise Impact: Linux in a Windows-Centric World
For many WindowsForum readers, the immediate reaction may be: why care about a Linux Wi-Fi CVE? The answer is that Windows-centric organizations rarely run only Windows anymore. Developer laptops dual-boot Linux, security teams use Linux-based tooling, edge appliances run embedded kernels, and cloud estates often include substantial Linux footprints.Even Microsoft-heavy environments depend on Linux in practical ways. Azure hosts Linux virtual machines, network appliances, Kubernetes nodes, and container images. On the desktop side, Windows users may run Linux through WSL, though typical WSL configurations do not expose raw Wi-Fi driver control in the same way a native Linux kernel does.
Where Exposure Is Most Plausible
The highest practical concern is for systems where untrusted or semi-trusted users can run local code and interact with network management features. That includes university labs, developer workstations, shared engineering benches, kiosks, and testing devices with Wi-Fi hardware enabled.Enterprise risk is more nuanced:
- Cloud VMs are usually not directly affected by Wi-Fi driver paths.
- Native Linux laptops may be affected if they run vulnerable kernels and supported wireless hardware.
- Embedded Linux devices may be affected if they include cfg80211 and expose PMSR-capable workflows.
- Build farms are lower risk unless they attach wireless devices or test Wi-Fi drivers.
- Security research systems may be higher risk because they intentionally expose low-level networking controls.
Consumer and Power User Impact
For ordinary Linux desktop users, CVE-2026-31548 is unlikely to be the most urgent security event of the month. The bug requires local code execution and a specific race involving wireless PMSR cleanup and interface teardown. A home user who keeps their distribution updated will likely receive the fix through normal kernel updates.Still, power users should not ignore it. Linux laptops frequently depend on Wi-Fi, sleep and resume, NetworkManager transitions, driver reloads, and rapid interface resets. Bugs in these paths can surface as intermittent crashes that are hard to diagnose, especially if a system is already running experimental kernels or release candidates.
Practical Steps for Desktop Users
The right response is straightforward: update the kernel from your distribution, reboot, and confirm the new kernel is running. Installing an update without rebooting does not remove exposure from the active kernel. That point is basic but routinely overlooked.Desktop users should consider:
- Applying kernel updates promptly when offered by the distribution.
- Rebooting after installation to load the patched kernel.
- Avoiding unnecessary 7.0 release candidates on daily-driver machines.
- Checking vendor forums if Wi-Fi becomes unstable after an update.
- Keeping fallback kernels installed in case a driver regression appears.
- Avoiding random out-of-tree Wi-Fi driver builds unless absolutely necessary.
Patch Mechanics: A Small Fix With Big Lifetime Guarantees
The fix for CVE-2026-31548 is a textbook example of defensive kernel teardown ordering. By adding a synchronous cancellation of pmsr_free_wk before abort processing in cfg80211_pmsr_wdev_down(), the kernel prevents delayed work from re-entering a driver after the interface lifecycle has moved on. This is the kind of change that may look trivial in a diff but is significant in a concurrent kernel.Synchronous cancellation matters because merely marking work as canceled is not enough if the work is already running on another CPU. The kernel needs to ensure that pending or in-progress execution has fully drained. Otherwise, the teardown path could still race with code that believes the interface remains valid.
Why Work Queues Are Both Powerful and Dangerous
Work queues are essential to Linux scalability. They let subsystems defer expensive or context-sensitive tasks, avoid doing too much inside socket release paths, and coordinate operations outside strict locking zones. But deferred execution also separates the decision to perform work from the moment that work actually runs.That separation demands strong lifetime rules:
- Objects must remain valid until all users and callbacks are finished.
- Teardown paths must drain pending work before unregistering driver-visible state.
- Callbacks must not assume hardware availability after interface-down transitions.
- Reference counts must cover asynchronous users, not only synchronous call stacks.
- Abort paths must be idempotent or explicitly serialized.
- Testing must include teardown races, not just normal request completion.
Distribution Response and Backport Reality
Linux vulnerability management is complicated by the difference between upstream version numbers and distribution-maintained kernels. A Debian, Ubuntu, Red Hat, SUSE, Fedora, Arch, or embedded vendor kernel may include thousands of backported patches while retaining an older-looking version string. That means version comparison alone can mislead both humans and scanners.The Debian security tracker, for example, shows different status across releases, with newer development branches moving ahead faster than stable releases. Red Hat’s Bugzilla entry tracks the issue as a security response item and mirrors the upstream description. These public trackers help, but administrators should still treat the distribution’s own fixed package advisory as the authoritative operational answer.
How to Validate Your Environment
A defensible validation workflow looks like this:- Identify all Linux systems with Wi-Fi hardware or wireless testing roles.
- Record the running kernel using standard system tools.
- Check your distribution’s security tracker for CVE-2026-31548.
- Confirm whether the fix was backported into your package stream.
- Deploy the update through normal change-control channels.
- Reboot affected systems and verify the patched kernel is active.
- Monitor crash logs, wireless stability, and driver regressions after deployment.
Scanner teams should also beware of false positives and false negatives. A raw CPE match may flag a kernel that is actually patched through backporting, while a custom vendor kernel may escape detection despite carrying the vulnerable code. For appliances, the vendor’s firmware advisory often matters more than the upstream kernel line.
Security Lessons Beyond This CVE
CVE-2026-31548 reinforces a broader lesson: many modern kernel vulnerabilities are not dramatic parser bugs or obvious bounds-check failures. They are lifecycle mistakes. An object is valid in one path, invalid in another, and accessed after the handoff between the two paths becomes ambiguous under concurrency.This is especially relevant to Wi-Fi because wireless stacks are event-heavy. Interfaces appear and disappear, firmware restarts, devices sleep and resume, regulatory changes arrive, scans overlap with connection attempts, and user-space network managers constantly open and close control sockets. Every one of those transitions is a chance for a race.
Why Wi-Fi Is a Persistent Kernel Risk Area
Wireless code combines hardware complexity, driver variation, and user-space control. It is not unusual for the same subsystem to serve laptops, phones, routers, industrial devices, and test equipment. That breadth makes generic kernel layers like cfg80211 both valuable and risky.The recurring risk factors include:
- Many hardware vendors implementing callbacks beneath common kernel APIs.
- Frequent power-state transitions on mobile devices.
- Asynchronous firmware behavior that does not always align with kernel state.
- Multiple user-space managers interacting through netlink interfaces.
- Complex teardown paths during suspend, device removal, or driver reload.
- Security-sensitive local interfaces exposed to privileged or semi-privileged tools.
Competitive and Ecosystem Implications
Linux’s openness cuts both ways in vulnerability response. On the positive side, the patch is visible, the affected code can be reviewed, and downstream vendors can backport quickly. On the negative side, public commits can also help attackers understand the failure mode before every distribution has shipped and every user has rebooted.For Microsoft, this advisory’s appearance in security guidance reflects the company’s broader role in a mixed operating-system world. Windows is still the desktop center for many organizations, but Microsoft’s cloud, developer, and security products increasingly inventory and manage Linux assets. The boundary between Windows security and Linux security is now operational, not philosophical.
Market and Platform Effects
The competitive implications are subtle rather than sensational. Linux vendors must continue proving that fast upstream fixes translate into reliable downstream updates. Microsoft, meanwhile, benefits when its security tooling can surface Linux risks accurately without confusing administrators into thinking every Linux CVE affects Windows endpoints.The ecosystem impact includes:
- Security platforms needing better kernel backport intelligence.
- Cloud providers distinguishing virtual Linux exposure from physical Wi-Fi exposure.
- Endpoint managers improving Linux laptop patch visibility.
- Distribution vendors communicating fixed package status clearly.
- Hardware vendors testing driver callbacks under teardown races.
- Enterprise buyers demanding clearer SBOM and kernel provenance data for appliances.
Detection, Mitigation, and Operational Playbook
There is no indication from the public description that defenders can reliably detect exploitation from a simple network signature. The trigger is local and kernel-internal, involving nl80211 PMSR request handling and interface teardown. That makes prevention through patching more valuable than after-the-fact detection.However, operational signs may still appear. Kernel oops messages, Wi-Fi driver crashes, sudden reboots, or logs mentioning cfg80211, nl80211, PMSR, or driver abort paths could warrant investigation. Such evidence is not proof of exploitation, but it may help identify unstable systems or failed attempts to exercise the race.
Recommended Mitigations
The primary mitigation is to install a kernel containing the upstream fix or a vendor backport. Where immediate patching is not possible, reduce local attack surface and restrict access to wireless device control. Those compensating controls are imperfect, but they can buy time.Recommended actions include:
- Patch and reboot affected Linux systems as the top priority.
- Restrict local shell access on Wi-Fi-enabled Linux hosts.
- Limit network-management privileges to trusted users and services.
- Disable unused Wi-Fi hardware on servers, kiosks, and appliances.
- Avoid running untrusted code on systems with vulnerable kernels.
- Monitor kernel crash logs for cfg80211 or wireless-driver failures.
- Validate embedded firmware updates with the device vendor.
Strengths and Opportunities
The response to CVE-2026-31548 shows several strengths in the modern Linux security process, especially around fast identification, upstream correction, and downstream tracking. It also gives enterprises a chance to improve how they handle kernel CVEs that do not fit neat remote-exploit categories.- The root cause is clearly documented, making it easier for maintainers and defenders to understand the race.
- The patch is narrowly targeted, reducing the likelihood of broad behavioral disruption.
- Multiple stable branches received fixes, supporting organizations that cannot jump to the newest kernel.
- Public tracking across vendor ecosystems helps security teams correlate status beyond one database.
- The CVSS vector highlights local kernel risk, avoiding the common underreaction to local-only bugs.
- The case improves teardown testing awareness, especially for asynchronous work and driver callbacks.
- Mixed-fleet visibility gets stronger when Microsoft, Linux vendors, and vulnerability databases surface the same CVE.
Risks and Concerns
The main concern is not that CVE-2026-31548 will instantly become a mass internet attack. The bigger risk is inconsistent remediation across the long tail of Linux kernels, appliances, developer machines, and embedded devices that quietly depend on wireless subsystems.- Backport ambiguity can confuse scanners and patch teams.
- Local exploit chains may combine this bug with sandbox escapes or weak user isolation.
- Embedded devices may receive delayed or no firmware updates.
- Out-of-tree Wi-Fi drivers may complicate stability testing after kernel updates.
- Release-candidate users may underestimate the risk of running development kernels.
- Kernel crash evidence may be misdiagnosed as ordinary Wi-Fi instability.
- NVD enrichment delays may cause some dashboards to under-prioritize the issue.
Looking Ahead
The next step is distribution follow-through. Administrators should watch for fixed kernel packages in stable enterprise channels, not just upstream commits. Security teams should also verify that vulnerability scanners correctly distinguish affected upstream versions from vendor-patched kernels with backported fixes.For WindowsForum readers, the larger story is the continued convergence of Windows, Linux, cloud, and endpoint security operations. A Linux Wi-Fi CVE can appear in Microsoft security tooling, affect developer laptops that authenticate into Windows domains, and matter to Azure-connected inventory systems. That does not make it a Windows flaw, but it does make it part of the same security conversation.
Watch these items over the coming days and weeks:
- Distribution advisories for fixed package availability across stable releases.
- Scanner updates that refine CPE matching and backport detection.
- Vendor firmware bulletins for embedded and appliance products using affected kernels.
- Reports of practical exploitation or proof-of-concept code, if any emerges.
- Regression reports from users with Intel, Qualcomm, Broadcom, Realtek, or other Wi-Fi chipsets.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center