CVE-2026-31771 is a high-severity Linux kernel Bluetooth flaw disclosed on May 1, 2026, in which malformed short HCI event frames could reach wake-reason address handling before per-event payload-length validation occurred. The bug is not a Windows vulnerability in the narrow sense, but it matters to WindowsForum readers because Microsoft’s security ecosystem increasingly surfaces Linux kernel CVEs through WSL, Azure, Defender, containers, appliances, and mixed-device fleets. Its lesson is larger than Bluetooth: modern platform security often fails in the small gap between “we parsed the packet” and “we proved the packet is long enough to trust.” For administrators, the practical question is not whether every laptop is instantly exposed, but where Linux Bluetooth stacks sit close enough to untrusted radios to turn a kernel bookkeeping mistake into a real operational risk.
The phrase “wake reason storage” sounds like a diagnostic footnote, the sort of subsystem plumbing that only kernel maintainers and power-management obsessives should ever need to think about. In practice, it sits at a surprisingly sensitive intersection: Bluetooth event processing, suspend and resume behavior, device identity, and kernel memory safety.
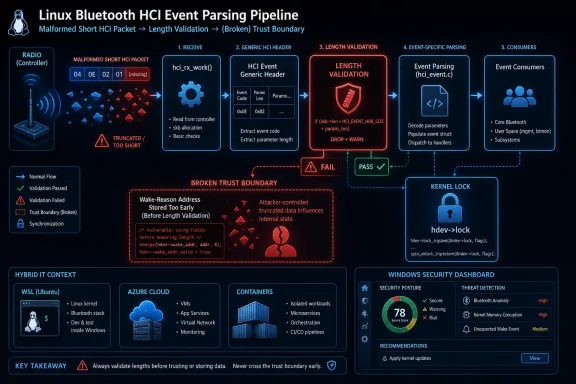
The vulnerable path lived in the Linux Bluetooth Host Controller Interface event handling code. HCI is the layer where the host operating system and the Bluetooth controller exchange commands and events. When a controller reports that something happened — a connection request, an advertising report, a connection completion, or another radio-side event — the kernel receives an HCI event packet and dispatches it to the appropriate handler.
CVE-2026-31771 turns on a simple ordering mistake. The kernel stripped the generic HCI event header and then called
That is the kind of bug that rarely looks dramatic in a changelog and often looks obvious in hindsight. The kernel already had a table of event handlers and minimum payload lengths. The missing defense was not a brand-new mitigation or a sweeping redesign; it was the discipline of ensuring that every consumer of event data sits behind the validation gate, not beside it.
Bluetooth is local by design. An attacker generally needs radio proximity, a reachable Bluetooth controller, and a vulnerable kernel path exposed through the right kind of HCI event behavior. That makes this a different species of risk from a wormable SMB or HTTP flaw. It is not automatically a data-center perimeter fire, and it is not a reason to rip Bluetooth radios out of every machine before lunch.
But “adjacent” is not the same as “academic.” Offices, airports, hotels, classrooms, warehouses, hospitals, retail floors, and shared labs are all adjacent-network environments in the Bluetooth sense. The security model of Bluetooth has always been complicated by the fact that the radio edge is physically fuzzy. A machine that is “not on the network” may still be listening to the room.
The more important point is that the vulnerability is in kernel code. Once malformed controller-originated or radio-influenced event data reaches a kernel parser incorrectly, the blast radius is qualitatively different from a userspace daemon bug. Kernel memory exposure and kernel availability failures are not inconveniences; they are foundational failures in the operating system’s trust model.
So why does it show up in Microsoft’s orbit at all? Because Microsoft is no longer just a Windows client vendor. It ships, hosts, scans, documents, and secures Linux in several forms: Azure virtual machines, Azure Kubernetes Service nodes, Linux-based appliances and agents, Defender-managed endpoints, GitHub-hosted supply chains, and Windows Subsystem for Linux environments that depend on Microsoft-distributed kernels or kernel-adjacent components.
That does not mean every Windows 11 PC is affected. It means Microsoft’s customers increasingly operate Windows and Linux as one security estate. A vulnerability in the Linux kernel may be operationally relevant to a Windows shop if that shop runs Linux containers on Windows developer workstations, Ubuntu images in Azure, IoT gateways, security appliances, or dual-boot and lab systems with active Bluetooth hardware.
This is the part of the modern Microsoft story that still catches some administrators off guard. The Security Update Guide is not merely a list of Windows patches anymore; it is a window into an ecosystem where Microsoft’s customers expect one vendor to tell them about risk across a hybrid stack. That makes the entry useful, but it also makes precise reading essential.
The description makes the relevant sequence clear.
That gap matters because a Bluetooth address copy routine such as
The fix is architecturally conservative. Instead of teaching
That is the right kind of repair. Security fixes are strongest when they remove a bad ordering assumption rather than scattering new conditional checks across a path that future maintainers may accidentally bypass. The change also narrows the helper’s responsibility: it stores an already-validated address while the caller holds the Bluetooth device lock.
That may sound like kernel-maintainer housekeeping, but it is the part that separates a local patch from a durable correction. The old problem involved a helper being called in a context where validation had not yet happened. The new helper is intentionally made smaller and more explicit: it does not decide whether event data is safe; it records a value that a validated caller provides while holding the right lock.
Kernel code ages through call sites. A helper that seems private and obvious today becomes tomorrow’s convenient shortcut. By making the locking contract visible to static analysis and runtime lock dependency checking, maintainers reduce the chance that a future patch reintroduces the same class of error through a new path.
This matters because Bluetooth event handling is full of state transitions. Connections are requested, completed, synchronized, reported, advertised, accepted, rejected, suspended, and resumed. The fix touches handlers including classic connection request and completion events, synchronous connection completion, LE connection completion, several LE advertising report paths, periodic advertising sync establishment, and periodic advertising sync transfer receipt. That breadth tells us the wake-reason path was not a one-off corner; it was a cross-cutting convenience threaded through many event types.
When a convenience function spans many event families, it becomes tempting to call it early and centrally. CVE-2026-31771 is the cost of that temptation. Centralized parsing feels clean until the central point lacks the event-specific facts needed to be safe.
Linux laptops, embedded devices, and IoT systems have a long history of Bluetooth-related suspend and resume weirdness. Users see machines waking from sleep, Bluetooth devices failing after resume, controllers timing out during suspend, or logs blaming an HCI device for unexpected activity. The wake-reason machinery exists because the kernel needs to explain what woke the system or at least record that a Bluetooth event was involved.
A security fix that simply deleted wake-address recording would reduce the vulnerable surface but degrade observability. That might be acceptable in an emergency, but it is not good engineering. The chosen fix keeps the behavior: when a specific validated event handler can identify a peer address, it records it; when no validated event handler does so, the fallback still records the wake event without inventing an address.
That is the subtle balance mature kernel maintenance has to strike. Security hardening must not turn every diagnostic into “unknown” unless there is no alternative. In enterprise environments, power-management telemetry can matter for battery life, fleet reliability, sleep-state debugging, and incident investigation.
For administrators, this creates a familiar timing problem. Your scanner may begin reporting CVE-2026-31771 before your distribution has published a clean advisory with affected-version tables, or after your distribution has already backported the fix without changing the upstream kernel version string in an obvious way. The result is noise, uncertainty, and sometimes false positives.
Linux distribution kernels do not map neatly to upstream version numbers. Red Hat, Ubuntu, Debian, SUSE, Amazon Linux, and others routinely backport individual fixes into long-term kernels. A system may report an older kernel base version while still containing the relevant patch. Conversely, a rolling or custom kernel may look modern but lack a vendor-specific backport cadence that your scanner understands.
That is why the operational answer is not simply “upgrade to the newest kernel” in every environment. The better answer is to check your vendor’s kernel changelog or security advisory, verify whether the fix for the Bluetooth HCI wake-reason path is included, and treat raw CVE-to-version matching as a starting point rather than a verdict.
Developer workstations are one candidate. Many Windows developers use WSL, containers, USB pass-through tools, dual-boot installations, or Linux virtual machines. WSL itself does not automatically mean the Linux guest has direct access to a Bluetooth controller in the same way a native Linux install does, but lab configurations can vary, and developer machines are often where policy exceptions accumulate.
Edge devices are another candidate. Industrial gateways, kiosks, point-of-sale devices, conference-room systems, signage controllers, and test benches often run Linux with Bluetooth enabled for provisioning, peripherals, diagnostics, or vendor maintenance. These devices may sit in physically exposed areas where an adjacent radio attacker is more plausible than a remote Internet attacker.
Cloud servers are usually less interesting for this CVE because they generally lack Bluetooth radios, but cloud images should not be dismissed wholesale. Some cloud security scanners will flag the kernel package regardless of whether the relevant hardware exists. That does not make the finding fake; it means risk prioritization must incorporate attack surface, not just package presence.
The place to be most careful is the messy middle: laptops used by administrators, Linux-based management appliances, and lab machines that bridge corporate credentials with physically accessible radio environments. A Bluetooth-adjacent kernel flaw on a throwaway test laptop is one thing. The same class of flaw on an admin workstation used for privileged access deserves a faster response.
Still, defenders should avoid the opposite mistake: treating the absence of exploit chatter as proof of safety. Bluetooth attack research has repeatedly shown that proximity-based bugs can be practical when the attacker can control timing, malformed frames, and the target’s radio environment. Even if exploitation beyond denial of service is difficult, a kernel crash triggered from nearby is a serious failure for mobile and edge systems.
The confidentiality impact in the CVSS vector is also worth parsing carefully. A short frame reaching a copy operation before bounds checking can create the conditions for an out-of-bounds read. Whether that yields meaningful kernel memory disclosure depends on implementation details, logging paths, data propagation, and mitigations. The score reflects potential impact, not a guarantee that every vulnerable system leaks secrets on demand.
Availability is easier to imagine. Kernel memory-safety violations in packet processing paths can become crashes, warnings, or controller failures. For a user laptop, that may mean an ugly local denial of service. For an embedded or operational device, availability failures can have outsized consequences if the machine is unattended, physically remote, or tied to business processes.
This is a recurring pattern across network stacks, file systems, image decoders, archive libraries, drivers, hypervisors, and protocol implementations. A shared helper is placed near the top of a dispatch path to avoid duplication. Later, someone realizes that the helper depends on data whose validity is not uniform across all event types. The code is elegant; the trust boundary is wrong.
The Linux fix is instructive because it accepts a small amount of repetition at the handler level in exchange for a clearer security model. Each event handler knows the shape of its event. Each event handler already has or sits behind the appropriate minimum-length check. Recording the wake address there may be less centralized, but it is more truthful.
That trade-off is often where secure systems differ from merely tidy systems. Centralization is not a virtue when it centralizes assumptions that are not globally true. The best place to process untrusted data is the place that can prove the data’s structure.
The hardest part is evidence. Security dashboards may list the CVE against a kernel package without knowing whether a Bluetooth controller is present. Endpoint management may know hardware inventory but not kernel patch state. Linux package tooling may report a vendor kernel version that looks vulnerable to a scanner trained on upstream versions. Each tool sees a slice of the truth.
Administrators should therefore correlate three facts: whether the kernel package includes the relevant stable backport, whether the Bluetooth stack is present and active, and whether the device operates in an environment where nearby attackers are plausible. That triage is more useful than simply sorting by CVSS score.
There is also a policy question. Many enterprises disable Bluetooth on servers and sensitive endpoints by default, but exceptions creep in through laptops, collaboration devices, lab systems, and vendor appliances. CVE-2026-31771 is a reminder that “we do not use Bluetooth” should be a verifiable control, not an assumption inherited from a spreadsheet.
The upstream kernel fix tells maintainers what changed. The CVE tells scanners what to track. Distribution advisories tell administrators whether their supported packages are affected and when fixed packages are available. Cloud and platform advisories may add another layer by declaring whether a managed image, appliance, or service is affected in that provider’s environment.
This layered reality is annoying, but it is also how Linux security actually works. A backported enterprise kernel can be secure without looking numerically current. A custom-built kernel can be vulnerable even if it has a shiny version banner. A container host can matter even when the container image itself has no Bluetooth stack, because the host kernel is where the vulnerable code lives.
For WindowsForum readers, the Windows analogy is useful but imperfect. On Windows, Patch Tuesday often gives a relatively centralized answer for supported client and server versions. In Linux fleets, especially hybrid ones, the answer is distributed across kernel branches, vendors, repositories, and local build practices. CVE-2026-31771 is a small Bluetooth bug that forces that larger operational truth back into view.
Here, the cause is not buried. A helper ran too early. A short HCI event frame could reach an address copy before bounds checks. The fix moved storage into validated handlers and made the lock contract explicit. That is enough for kernel engineers and security teams to reason about the flaw without waiting for exploit theater.
The downside is that this style pushes more interpretation onto downstream vendors and administrators. NVD enrichment may lag. CWE mappings may be missing or generic. CVSS may come from the CNA before NVD publishes its own assessment. Product applicability can remain unclear while scanners already treat the CVE as live.
This is not a failure of the CVE system so much as a mismatch between source-code security and enterprise vulnerability management. Kernel vulnerabilities are often born as patches, not bulletins. The industry then spends days or weeks translating a precise code change into asset impact, remediation guidance, and scanner logic.
The most concrete actions are straightforward, even if the inventory work is not.
That is the new normal. Windows administrators manage Linux. Linux administrators consume Microsoft guidance. Cloud teams inherit kernel exposure through images and hosts they may not compile. Security teams see CVEs before product owners understand whether the hardware path exists.
The best response is not panic and not complacency. Patch where Bluetooth is real, verify where scanners are vague, and use this CVE as another reminder that validation must happen before convenience code touches untrusted bytes. The next kernel flaw may arrive through Wi-Fi, USB, graphics, storage, or a virtual device, but the argument will be the same: in hybrid IT, the edges are everywhere, and the safest systems are the ones that treat every edge as a parser under pressure.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Bluetooth Wake Path Became a Kernel Trust Boundary
A Bluetooth Wake Path Became a Kernel Trust Boundary
The phrase “wake reason storage” sounds like a diagnostic footnote, the sort of subsystem plumbing that only kernel maintainers and power-management obsessives should ever need to think about. In practice, it sits at a surprisingly sensitive intersection: Bluetooth event processing, suspend and resume behavior, device identity, and kernel memory safety.The vulnerable path lived in the Linux Bluetooth Host Controller Interface event handling code. HCI is the layer where the host operating system and the Bluetooth controller exchange commands and events. When a controller reports that something happened — a connection request, an advertising report, a connection completion, or another radio-side event — the kernel receives an HCI event packet and dispatches it to the appropriate handler.
CVE-2026-31771 turns on a simple ordering mistake. The kernel stripped the generic HCI event header and then called
hci_store_wake_reason() before the event-specific handler enforced the minimum payload length for that particular event. That meant a short HCI event frame could arrive at code that copied a Bluetooth device address before the kernel had proved that the frame actually contained the bytes being copied.That is the kind of bug that rarely looks dramatic in a changelog and often looks obvious in hindsight. The kernel already had a table of event handlers and minimum payload lengths. The missing defense was not a brand-new mitigation or a sweeping redesign; it was the discipline of ensuring that every consumer of event data sits behind the validation gate, not beside it.
The Severity Score Says “High,” But the Attack Surface Says “Nearby”
The assigned CVSS 3.1 score from kernel.org is 8.1, with an adjacent-network attack vector, low attack complexity, no privileges required, no user interaction, high confidentiality impact, no integrity impact, and high availability impact. That combination is enough to make vulnerability scanners light up, but it should not be read as “anyone on the Internet can crash or read your Linux box.”Bluetooth is local by design. An attacker generally needs radio proximity, a reachable Bluetooth controller, and a vulnerable kernel path exposed through the right kind of HCI event behavior. That makes this a different species of risk from a wormable SMB or HTTP flaw. It is not automatically a data-center perimeter fire, and it is not a reason to rip Bluetooth radios out of every machine before lunch.
But “adjacent” is not the same as “academic.” Offices, airports, hotels, classrooms, warehouses, hospitals, retail floors, and shared labs are all adjacent-network environments in the Bluetooth sense. The security model of Bluetooth has always been complicated by the fact that the radio edge is physically fuzzy. A machine that is “not on the network” may still be listening to the room.
The more important point is that the vulnerability is in kernel code. Once malformed controller-originated or radio-influenced event data reaches a kernel parser incorrectly, the blast radius is qualitatively different from a userspace daemon bug. Kernel memory exposure and kernel availability failures are not inconveniences; they are foundational failures in the operating system’s trust model.
Microsoft’s Presence Is a Signal, Not a Windows Panic Button
The user-facing source here is Microsoft’s Security Update Guide entry, which can make the vulnerability look like a Microsoft bulletin at first glance. That framing is easy to misunderstand. CVE-2026-31771 is a Linux kernel vulnerability, and the fix lives in Linux kernel Bluetooth code, not in the Windows Bluetooth stack.So why does it show up in Microsoft’s orbit at all? Because Microsoft is no longer just a Windows client vendor. It ships, hosts, scans, documents, and secures Linux in several forms: Azure virtual machines, Azure Kubernetes Service nodes, Linux-based appliances and agents, Defender-managed endpoints, GitHub-hosted supply chains, and Windows Subsystem for Linux environments that depend on Microsoft-distributed kernels or kernel-adjacent components.
That does not mean every Windows 11 PC is affected. It means Microsoft’s customers increasingly operate Windows and Linux as one security estate. A vulnerability in the Linux kernel may be operationally relevant to a Windows shop if that shop runs Linux containers on Windows developer workstations, Ubuntu images in Azure, IoT gateways, security appliances, or dual-boot and lab systems with active Bluetooth hardware.
This is the part of the modern Microsoft story that still catches some administrators off guard. The Security Update Guide is not merely a list of Windows patches anymore; it is a window into an ecosystem where Microsoft’s customers expect one vendor to tell them about risk across a hybrid stack. That makes the entry useful, but it also makes precise reading essential.
The Bug Is About Validation Order, Not Bluetooth Pairing Magic
Many Bluetooth security stories revolve around pairing, encryption negotiation, device spoofing, or user consent prompts. CVE-2026-31771 is less theatrical. It is about when the kernel decides that a packet is structurally safe to inspect.The description makes the relevant sequence clear.
hci_event_packet() receives an HCI event, strips the general event header, and at that early point the older code could call hci_store_wake_reason(). Only afterward would hci_event_func() enforce the per-event minimum payload length listed in the HCI event table. The vulnerable moment was the gap between generic parsing and event-specific validation.That gap matters because a Bluetooth address copy routine such as
bacpy() assumes that its source points to a valid bdaddr structure. If the packet is shorter than the event type requires, code can read beyond the bytes that actually arrived. Depending on memory layout, compiler behavior, sanitizers, and the exact path, that kind of bug can become an information leak, a crash, or a primitive that defenders would rather not hand to an attacker at all.The fix is architecturally conservative. Instead of teaching
hci_store_wake_reason() to re-parse every possible HCI event and duplicate length checks, the patch moves wake-address storage into the individual event handlers that already validate their own payloads. In other words, the kernel now records the wake address only after the relevant handler has established that the event body is long enough to contain that address.That is the right kind of repair. Security fixes are strongest when they remove a bad ordering assumption rather than scattering new conditional checks across a path that future maintainers may accidentally bypass. The change also narrows the helper’s responsibility: it stores an already-validated address while the caller holds the Bluetooth device lock.
The Lock Annotation Tells Us Maintainers Were Fixing the Contract, Not Just the Crash
One of the most interesting details in the fix is not the address copy itself. It is the addition of explicit locking expectations around the helper: the helper is annotated with__must_hold(&hdev->lock) and guarded with lockdep_assert_held(&hdev->lock).That may sound like kernel-maintainer housekeeping, but it is the part that separates a local patch from a durable correction. The old problem involved a helper being called in a context where validation had not yet happened. The new helper is intentionally made smaller and more explicit: it does not decide whether event data is safe; it records a value that a validated caller provides while holding the right lock.
Kernel code ages through call sites. A helper that seems private and obvious today becomes tomorrow’s convenient shortcut. By making the locking contract visible to static analysis and runtime lock dependency checking, maintainers reduce the chance that a future patch reintroduces the same class of error through a new path.
This matters because Bluetooth event handling is full of state transitions. Connections are requested, completed, synchronized, reported, advertised, accepted, rejected, suspended, and resumed. The fix touches handlers including classic connection request and completion events, synchronous connection completion, LE connection completion, several LE advertising report paths, periodic advertising sync establishment, and periodic advertising sync transfer receipt. That breadth tells us the wake-reason path was not a one-off corner; it was a cross-cutting convenience threaded through many event types.
When a convenience function spans many event families, it becomes tempting to call it early and centrally. CVE-2026-31771 is the cost of that temptation. Centralized parsing feels clean until the central point lacks the event-specific facts needed to be safe.
The “Unexpected Wake” Fallback Shows Why Security Fixes Cannot Break Power Management
The patch also preserves existing fallback behavior for unexpected wake events by calling the helper with a null address after normal event dispatch when no validated handler records a wake address. That detail is not cosmetic. It shows the maintainer’s real constraint: fix the memory-safety problem without breaking diagnostics and power-management semantics that users and developers may rely on.Linux laptops, embedded devices, and IoT systems have a long history of Bluetooth-related suspend and resume weirdness. Users see machines waking from sleep, Bluetooth devices failing after resume, controllers timing out during suspend, or logs blaming an HCI device for unexpected activity. The wake-reason machinery exists because the kernel needs to explain what woke the system or at least record that a Bluetooth event was involved.
A security fix that simply deleted wake-address recording would reduce the vulnerable surface but degrade observability. That might be acceptable in an emergency, but it is not good engineering. The chosen fix keeps the behavior: when a specific validated event handler can identify a peer address, it records it; when no validated event handler does so, the fallback still records the wake event without inventing an address.
That is the subtle balance mature kernel maintenance has to strike. Security hardening must not turn every diagnostic into “unknown” unless there is no alternative. In enterprise environments, power-management telemetry can matter for battery life, fleet reliability, sleep-state debugging, and incident investigation.
The Patch Landed Before Most Users Knew the CVE Existed
The references associated with the CVE point to stable kernel commits, and public patch discussion appeared before the CVE record reached broad vulnerability feeds. That chronology is typical for many Linux kernel CVEs: the vulnerability is often represented first as a kernel patch with a technical subject line, then later as a CVE record ingested by scanners, vendor advisories, and security dashboards.For administrators, this creates a familiar timing problem. Your scanner may begin reporting CVE-2026-31771 before your distribution has published a clean advisory with affected-version tables, or after your distribution has already backported the fix without changing the upstream kernel version string in an obvious way. The result is noise, uncertainty, and sometimes false positives.
Linux distribution kernels do not map neatly to upstream version numbers. Red Hat, Ubuntu, Debian, SUSE, Amazon Linux, and others routinely backport individual fixes into long-term kernels. A system may report an older kernel base version while still containing the relevant patch. Conversely, a rolling or custom kernel may look modern but lack a vendor-specific backport cadence that your scanner understands.
That is why the operational answer is not simply “upgrade to the newest kernel” in every environment. The better answer is to check your vendor’s kernel changelog or security advisory, verify whether the fix for the Bluetooth HCI wake-reason path is included, and treat raw CVE-to-version matching as a starting point rather than a verdict.
Windows Shops Should Look for Linux Where Bluetooth Still Exists
The most obvious affected machines are Linux desktops and laptops with Bluetooth enabled. But in Windows-heavy organizations, those are not the only places to look. The more interesting inventory question is where Linux kernels run with Bluetooth hardware exposed or enabled.Developer workstations are one candidate. Many Windows developers use WSL, containers, USB pass-through tools, dual-boot installations, or Linux virtual machines. WSL itself does not automatically mean the Linux guest has direct access to a Bluetooth controller in the same way a native Linux install does, but lab configurations can vary, and developer machines are often where policy exceptions accumulate.
Edge devices are another candidate. Industrial gateways, kiosks, point-of-sale devices, conference-room systems, signage controllers, and test benches often run Linux with Bluetooth enabled for provisioning, peripherals, diagnostics, or vendor maintenance. These devices may sit in physically exposed areas where an adjacent radio attacker is more plausible than a remote Internet attacker.
Cloud servers are usually less interesting for this CVE because they generally lack Bluetooth radios, but cloud images should not be dismissed wholesale. Some cloud security scanners will flag the kernel package regardless of whether the relevant hardware exists. That does not make the finding fake; it means risk prioritization must incorporate attack surface, not just package presence.
The place to be most careful is the messy middle: laptops used by administrators, Linux-based management appliances, and lab machines that bridge corporate credentials with physically accessible radio environments. A Bluetooth-adjacent kernel flaw on a throwaway test laptop is one thing. The same class of flaw on an admin workstation used for privileged access deserves a faster response.
The Attack Story Is Plausible Enough to Patch, Not Clear Enough to Panic
The CVE description does not provide a public exploit chain, and the available public material frames the flaw through the resolved kernel patch rather than a weaponized proof of concept. That distinction matters. There is a difference between a memory-safety bug with a high theoretical impact and a widely exploited vulnerability with turnkey tooling.Still, defenders should avoid the opposite mistake: treating the absence of exploit chatter as proof of safety. Bluetooth attack research has repeatedly shown that proximity-based bugs can be practical when the attacker can control timing, malformed frames, and the target’s radio environment. Even if exploitation beyond denial of service is difficult, a kernel crash triggered from nearby is a serious failure for mobile and edge systems.
The confidentiality impact in the CVSS vector is also worth parsing carefully. A short frame reaching a copy operation before bounds checking can create the conditions for an out-of-bounds read. Whether that yields meaningful kernel memory disclosure depends on implementation details, logging paths, data propagation, and mitigations. The score reflects potential impact, not a guarantee that every vulnerable system leaks secrets on demand.
Availability is easier to imagine. Kernel memory-safety violations in packet processing paths can become crashes, warnings, or controller failures. For a user laptop, that may mean an ugly local denial of service. For an embedded or operational device, availability failures can have outsized consequences if the machine is unattended, physically remote, or tied to business processes.
The Real Lesson Is That Parsers Need One Door, Not Two
CVE-2026-31771 belongs to a broad and stubborn family of bugs: parser consumers that read fields before the parser’s validation contract has fully executed. These mistakes survive code review because they are often wrapped in sensible abstractions. A function that “stores the wake reason” sounds higher-level than a function that “reads untrusted bytes from a variable-length packet.” But if the wake reason includes a peer address extracted from the packet, the abstraction is only safe after validation.This is a recurring pattern across network stacks, file systems, image decoders, archive libraries, drivers, hypervisors, and protocol implementations. A shared helper is placed near the top of a dispatch path to avoid duplication. Later, someone realizes that the helper depends on data whose validity is not uniform across all event types. The code is elegant; the trust boundary is wrong.
The Linux fix is instructive because it accepts a small amount of repetition at the handler level in exchange for a clearer security model. Each event handler knows the shape of its event. Each event handler already has or sits behind the appropriate minimum-length check. Recording the wake address there may be less centralized, but it is more truthful.
That trade-off is often where secure systems differ from merely tidy systems. Centralization is not a virtue when it centralizes assumptions that are not globally true. The best place to process untrusted data is the place that can prove the data’s structure.
Patch Management Has to Understand Backports, Radios, and Reality
For IT teams, CVE-2026-31771 should enter the normal kernel-update pipeline with a risk modifier for Bluetooth exposure. If Bluetooth is enabled on Linux endpoints or edge devices, prioritize the fix. If Bluetooth is absent, disabled in firmware, blocked by policy, or unavailable to the running kernel, the practical exploitability is much lower, though package compliance may still require remediation.The hardest part is evidence. Security dashboards may list the CVE against a kernel package without knowing whether a Bluetooth controller is present. Endpoint management may know hardware inventory but not kernel patch state. Linux package tooling may report a vendor kernel version that looks vulnerable to a scanner trained on upstream versions. Each tool sees a slice of the truth.
Administrators should therefore correlate three facts: whether the kernel package includes the relevant stable backport, whether the Bluetooth stack is present and active, and whether the device operates in an environment where nearby attackers are plausible. That triage is more useful than simply sorting by CVSS score.
There is also a policy question. Many enterprises disable Bluetooth on servers and sensitive endpoints by default, but exceptions creep in through laptops, collaboration devices, lab systems, and vendor appliances. CVE-2026-31771 is a reminder that “we do not use Bluetooth” should be a verifiable control, not an assumption inherited from a spreadsheet.
The Scanner Finding Is the Start of the Investigation
When a vulnerability scanner reports CVE-2026-31771, the first reaction should be to identify the kernel vendor and update channel. A Microsoft security entry, an NVD record, a Red Hat bug, an Amazon Linux page, and an upstream kernel commit may all describe the same flaw, but they do not necessarily answer the same question for your machine.The upstream kernel fix tells maintainers what changed. The CVE tells scanners what to track. Distribution advisories tell administrators whether their supported packages are affected and when fixed packages are available. Cloud and platform advisories may add another layer by declaring whether a managed image, appliance, or service is affected in that provider’s environment.
This layered reality is annoying, but it is also how Linux security actually works. A backported enterprise kernel can be secure without looking numerically current. A custom-built kernel can be vulnerable even if it has a shiny version banner. A container host can matter even when the container image itself has no Bluetooth stack, because the host kernel is where the vulnerable code lives.
For WindowsForum readers, the Windows analogy is useful but imperfect. On Windows, Patch Tuesday often gives a relatively centralized answer for supported client and server versions. In Linux fleets, especially hybrid ones, the answer is distributed across kernel branches, vendors, repositories, and local build practices. CVE-2026-31771 is a small Bluetooth bug that forces that larger operational truth back into view.
Vendors Are Learning to Describe Kernel Bugs as Resolved Code, Not Exploit Drama
The wording of the CVE record is classic Linux-kernel security prose: “In the Linux kernel, the following vulnerability has been resolved.” It then describes the commit-level repair rather than a marketing-friendly exploit scenario. That style can frustrate defenders looking for crisp “affected/not affected” statements, but it has an advantage: it exposes the actual engineering cause.Here, the cause is not buried. A helper ran too early. A short HCI event frame could reach an address copy before bounds checks. The fix moved storage into validated handlers and made the lock contract explicit. That is enough for kernel engineers and security teams to reason about the flaw without waiting for exploit theater.
The downside is that this style pushes more interpretation onto downstream vendors and administrators. NVD enrichment may lag. CWE mappings may be missing or generic. CVSS may come from the CNA before NVD publishes its own assessment. Product applicability can remain unclear while scanners already treat the CVE as live.
This is not a failure of the CVE system so much as a mismatch between source-code security and enterprise vulnerability management. Kernel vulnerabilities are often born as patches, not bulletins. The industry then spends days or weeks translating a precise code change into asset impact, remediation guidance, and scanner logic.
The Bluetooth Footnote That Belongs in This Week’s Risk Meeting
CVE-2026-31771 is not the largest vulnerability of the year, and it is unlikely to be the only Linux kernel CVE in any serious dashboard this month. Its importance is that it draws a clean line from a small validation-order mistake to a high-severity kernel advisory in a radio-exposed subsystem. That makes it a useful test of whether an organization can separate headline severity from actual attack surface without dismissing either.The most concrete actions are straightforward, even if the inventory work is not.
- Organizations should verify whether their Linux kernel packages include the stable fix that moves Bluetooth wake-reason address storage behind event-specific validation.
- Linux laptops, workstations, edge devices, and appliances with Bluetooth enabled deserve higher priority than cloud servers or virtual machines with no Bluetooth hardware exposure.
- Windows-centric teams should still check WSL-adjacent, Azure, container-host, lab, and vendor-appliance environments because Microsoft-managed security views increasingly include Linux kernel risk.
- Scanner results should be reconciled against distribution backports rather than judged only by upstream kernel version numbers.
- Bluetooth disablement should be treated as a documented and auditable mitigation, especially on administrative systems and physically exposed devices.
- Teams should watch vendor advisories for affected-package determinations, because NVD enrichment and product applicability data can lag the initial CVE publication.
Small Kernel Bugs Keep Exposing the Shape of Hybrid IT
The uncomfortable part of CVE-2026-31771 is not that Bluetooth has another vulnerability. Anyone who has watched wireless stacks for long enough expects malformed frames, parser edge cases, and controller-host boundary mistakes to surface periodically. The uncomfortable part is how easily a Linux kernel Bluetooth detail becomes a Microsoft-tracked issue, a scanner finding in a Windows-led security program, and a triage problem for teams that thought they knew where their operating-system boundaries were.That is the new normal. Windows administrators manage Linux. Linux administrators consume Microsoft guidance. Cloud teams inherit kernel exposure through images and hosts they may not compile. Security teams see CVEs before product owners understand whether the hardware path exists.
The best response is not panic and not complacency. Patch where Bluetooth is real, verify where scanners are vague, and use this CVE as another reminder that validation must happen before convenience code touches untrusted bytes. The next kernel flaw may arrive through Wi-Fi, USB, graphics, storage, or a virtual device, but the argument will be the same: in hybrid IT, the edges are everywhere, and the safest systems are the ones that treat every edge as a parser under pressure.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center