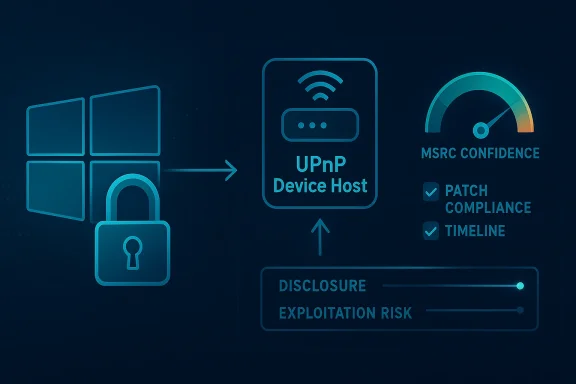
Microsoft’s handling of CVE-2026-32075 is a reminder that, in Windows security, metadata can be as important as exploit detail. The vulnerability is identified as a Windows UPnP Device Host Elevation of Privilege Vulnerability, and the MSRC confidence metric is specifically designed to indicate how certain Microsoft is that the bug exists and how credible the technical details are. Even when public technical notes are sparse, that confidence signal changes the operational meaning of the advisory: defenders are no longer dealing with a vague hypothesis, but with a vendor-tracked issue that Microsoft considers real enough to publish and prioritize.
The UPnP Device Host is one of those Windows components most users never think about until it matters. It supports device discovery and control workflows that make local networking and peripheral integration feel seamless, which is exactly why a flaw there is security-sensitive: convenience features often sit close to trust boundaries. When Microsoft labels an issue in this area as an elevation-of-privilege bug, it usually means a local attacker may be able to turn limited access into a higher-privileged context, often on the same host.
That distinction matters because elevation-of-privilege vulnerabilities are not always flashy, but they are foundational to real-world compromise chains. An attacker who already has some foothold — through phishing, a malicious script, a dropped payload, or another initial-access path — can use a local EoP bug to cross the last major barrier before full system control. In other words, these bugs frequently serve as the second stage of an intrusion rather than the first.
Microsoft has been signaling more clearly in recent years that confidence and disclosure quality are part of the patching story. Its Security Update Guide and related MSRC publications increasingly emphasize the difference between a confirmed vulnerability, a suspected issue, and a technical lead that still needs validation. That is a useful evolution for defenders, because it helps them separate patch-now items from issues that deserve monitoring but not blind assumptions.
CVE-2026-32075 fits that pattern. The public label tells us the affected subsystem, the class of impact, and the vendor’s confidence framework, but not much else about the root cause. That may frustrate reverse engineers and threat hunters, but it should not slow administrators; a confirmed Microsoft CVE affecting a privileged Windows service deserves the same basic response discipline regardless of how much exploit detail is publicly available.
Microsoft’s modern vulnerability workflow has become more transparent in the way it communicates risk. Rather than limiting defenders to a CVE name and a severity label, MSRC often provides context around confirmation status, exploitability, and the confidence level associated with the report. That matters because not every published vulnerability is equally mature; some are crisp, independently verifiable bugs, while others are vendor-confirmed but still technically under-described. The confidence metric is meant to help customers understand that difference.
In practice, that metric is especially useful for local privilege-escalation issues. Attackers who can already run code as a standard user do not need a remote exploit chain to benefit; they need reliability, stealth, and a way to pivot to SYSTEM or another elevated context. For that reason, even a minimally described EoP in a Windows subsystem can be highly valuable to both criminal operators and post-exploitation frameworks. Microsoft’s own framing helps defenders infer how much trust to place in the public details, even when the underlying flaw remains opaque.
The historical lesson here is that Windows EoP bugs tend to be underestimated by casual observers and overvalued by attackers. They are often not the headline vulnerability that gets the initial breach, but they are frequently the mechanism that determines whether an intrusion stays noisy and constrained or becomes complete system compromise. That makes them central to enterprise risk management, especially on endpoints where local access is easier to obtain than many teams would like to admit.
The challenge for defenders is that the window between disclosure and weaponization can be very short. Once a local EoP lands in the public tracking system, it becomes available for validation, research, and chaining. Even without exploit code, threat actors can often reconstruct enough of the attack surface from the affected component name, the OS build, and patch behavior to begin experimenting. That is why confirmed-but-sparse advisories should still be treated as actionable intelligence.
This is one reason the MSRC confidence metric has become operationally meaningful. It helps separate three different states of public vulnerability intelligence: hypothesis, credible report, and confirmed issue. In a world where scanners, SIEMs, and patch dashboards can all overwhelm analysts, that distinction is not academic. It tells defenders whether they should budget time for validation or move directly to remediation.
That matters because defenders often mistake silence for safety. A thin advisory can look less urgent than a rich one, but in vulnerability management that can be misleading. If Microsoft has assigned a CVE, identified a specific component, and framed the issue as elevation of privilege, the absence of more prose should be treated as a disclosure choice, not a sign of low importance.
That is why privilege-escalation bugs in services are so persistent across Windows releases. The surface area is not just the code that runs the service, but the way the service interacts with the operating system, COM objects, IPC mechanisms, and device-related trust decisions. A flaw in one of those layers can cascade into a much larger problem.
For enterprises, the consequences are broader. A local privilege-escalation issue can help an attacker move from a low-privileged domain context to a host-admin position, which then opens the door to credential theft, defensive evasion, and lateral movement. Once SYSTEM-level access is achieved, the endpoint becomes a staging ground for broader compromise.
That is also why it is useful to map this kind of issue against prior Windows EoP patterns. Microsoft has repeatedly had to patch privilege bugs in services, brokers, and kernel-facing components because those are the structures attackers most want to corrupt after the initial breach. The pattern is old, but the operational consequences are still current.
This kind of escalation can unlock:
This is particularly true on managed endpoints where users have local software installations, cached credentials, or access to data that is valuable even without full admin rights. An EoP in a Windows service can be the bridge that converts that limited foothold into durable control. That bridge is what defenders should fear, not just the first foothold.
The practical response is straightforward: inventory affected systems, confirm update levels, and reduce the number of endpoints where a local attacker can remain long enough to benefit from a privilege bug. That is a standard response, but in a case like CVE-2026-32075 it is also the right one.
This is especially important in the UPnP and device-hosting space, where public exploit detail can help attackers validate the bug rapidly. Vendors often walk a line between transparency and risk reduction, and the public advisory format is part of that balancing act. For defenders, the best reading is pragmatic: assume the bug is real, assume the patch is meaningful, and assume timing matters.
This is why Microsoft’s confidence metric deserves more attention than it often gets. It offers a shorthand for how hard defenders should lean into remediation before the rest of the ecosystem catches up. In a monthly patch cycle with dozens of issues, that shorthand is useful because it helps triage. It is not perfect, but it is better than guessing.
That also means defenders should use their own telemetry aggressively. Look for unexpected local privilege escalation patterns, suspicious service interactions, and post-exploitation behavior that might indicate abuse of a Windows broker or device-hosting service. Even in the absence of known exploit signatures, behavior-based detection can reduce dwell time.
Historically, privilege-escalation fixes in Windows often reveal the same themes:
That is why administrators should not read a component name and conclude that the threat is niche. A long-lived feature can be embedded deeply enough that remediation is tied to operating system servicing rather than optional software updates. That makes patching less flexible but also more important, because you cannot simply remove the service without risking regressions.
A sensible response sequence looks like this:
Endpoint detection and response tools can help, but only if they are tuned to identify escalation patterns. The key is not just detecting malware, but detecting the moment a lesser-privileged process becomes something more dangerous. That moment is often the true exploit event.
Home users are also less likely to notice subtle signs of escalation. A system may seem stable while the attacker uses elevated access to harvest data, tamper with settings, or disable protections. By the time the damage is visible, the exploitation path may have been active for days.
Security teams should also pay attention to whether this CVE appears in exploit kits, threat-intel feeds, or coordinated intrusion reports over the coming patch cycles. That will tell the industry whether the issue remains a cleanly handled advisory or becomes part of a live exploitation pattern. Even without public exploit code today, local privilege-escalation bugs have a habit of showing up in post-compromise tradecraft once attackers have time to study them.
In the end, the value of Microsoft’s confidence metric is not that it replaces technical detail, but that it helps defenders act when detail is still limited. CVE-2026-32075 is a textbook example of why that matters: a privileged Windows service, a local escalation path, and enough vendor certainty to justify immediate attention. In modern Windows security, that combination is rarely harmless, and it should not be treated that way here.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The UPnP Device Host is one of those Windows components most users never think about until it matters. It supports device discovery and control workflows that make local networking and peripheral integration feel seamless, which is exactly why a flaw there is security-sensitive: convenience features often sit close to trust boundaries. When Microsoft labels an issue in this area as an elevation-of-privilege bug, it usually means a local attacker may be able to turn limited access into a higher-privileged context, often on the same host.That distinction matters because elevation-of-privilege vulnerabilities are not always flashy, but they are foundational to real-world compromise chains. An attacker who already has some foothold — through phishing, a malicious script, a dropped payload, or another initial-access path — can use a local EoP bug to cross the last major barrier before full system control. In other words, these bugs frequently serve as the second stage of an intrusion rather than the first.
Microsoft has been signaling more clearly in recent years that confidence and disclosure quality are part of the patching story. Its Security Update Guide and related MSRC publications increasingly emphasize the difference between a confirmed vulnerability, a suspected issue, and a technical lead that still needs validation. That is a useful evolution for defenders, because it helps them separate patch-now items from issues that deserve monitoring but not blind assumptions.
CVE-2026-32075 fits that pattern. The public label tells us the affected subsystem, the class of impact, and the vendor’s confidence framework, but not much else about the root cause. That may frustrate reverse engineers and threat hunters, but it should not slow administrators; a confirmed Microsoft CVE affecting a privileged Windows service deserves the same basic response discipline regardless of how much exploit detail is publicly available.
Background
Windows has a long history of privilege-escalation issues in components that mediate services, brokers, device plumbing, or shell integration. The pattern is familiar: a feature that exists to make the platform easier to use also creates a rich attack surface, because it often handles structured input, IPC, or trust decisions on behalf of less-privileged callers. UPnP Device Host belongs to that broader category of Windows infrastructure that is highly useful for connectivity and device awareness, but also attractive to attackers looking for an internal path to escalation.Microsoft’s modern vulnerability workflow has become more transparent in the way it communicates risk. Rather than limiting defenders to a CVE name and a severity label, MSRC often provides context around confirmation status, exploitability, and the confidence level associated with the report. That matters because not every published vulnerability is equally mature; some are crisp, independently verifiable bugs, while others are vendor-confirmed but still technically under-described. The confidence metric is meant to help customers understand that difference.
In practice, that metric is especially useful for local privilege-escalation issues. Attackers who can already run code as a standard user do not need a remote exploit chain to benefit; they need reliability, stealth, and a way to pivot to SYSTEM or another elevated context. For that reason, even a minimally described EoP in a Windows subsystem can be highly valuable to both criminal operators and post-exploitation frameworks. Microsoft’s own framing helps defenders infer how much trust to place in the public details, even when the underlying flaw remains opaque.
The historical lesson here is that Windows EoP bugs tend to be underestimated by casual observers and overvalued by attackers. They are often not the headline vulnerability that gets the initial breach, but they are frequently the mechanism that determines whether an intrusion stays noisy and constrained or becomes complete system compromise. That makes them central to enterprise risk management, especially on endpoints where local access is easier to obtain than many teams would like to admit.
The challenge for defenders is that the window between disclosure and weaponization can be very short. Once a local EoP lands in the public tracking system, it becomes available for validation, research, and chaining. Even without exploit code, threat actors can often reconstruct enough of the attack surface from the affected component name, the OS build, and patch behavior to begin experimenting. That is why confirmed-but-sparse advisories should still be treated as actionable intelligence.
Why the MSRC confidence metric matters
The core detail in this case is not only the CVE itself, but the fact that Microsoft attaches a confidence signal to the advisory. In Microsoft’s own terminology, that signal measures how certain the company is that the vulnerability exists and how credible the known technical details are. That is a subtle but important distinction, because it gives defenders a way to prioritize without over-reading the limited public narrative.Confidence is not severity, but it influences urgency
A high-confidence advisory does not automatically mean a bug is remotely exploitable or widely weaponized. It means Microsoft has enough evidence to believe the issue is real and that the technical framing is dependable. For security teams, that is often enough to justify immediate patch planning, especially when the component is part of the Windows trust boundary and the issue is an EoP rather than a low-impact glitch.This is one reason the MSRC confidence metric has become operationally meaningful. It helps separate three different states of public vulnerability intelligence: hypothesis, credible report, and confirmed issue. In a world where scanners, SIEMs, and patch dashboards can all overwhelm analysts, that distinction is not academic. It tells defenders whether they should budget time for validation or move directly to remediation.
- High confidence generally means the bug is real enough to plan around.
- Lower confidence may warrant watchlisting and confirmation.
- Confidence plus vendor patch is the most actionable combination.
What confidence does and does not tell you
It does not tell you whether exploitation is easy. It does not tell you whether the bug is remotely reachable, or whether a weaponized chain already exists in the wild. What it does tell you is that Microsoft is confident enough in the existence and characterization of the flaw to publish it as a live security issue rather than an unresolved rumor.That matters because defenders often mistake silence for safety. A thin advisory can look less urgent than a rich one, but in vulnerability management that can be misleading. If Microsoft has assigned a CVE, identified a specific component, and framed the issue as elevation of privilege, the absence of more prose should be treated as a disclosure choice, not a sign of low importance.
- Treat the confidence signal as a trust indicator, not a threat score.
- Use it to separate confirmed issues from tentative research leads.
- Assume exploitability may still evolve after publication.
- Consider the component’s privilege boundary as the real risk amplifier.
The UPnP Device Host attack surface
UPnP Device Host sits in a category of Windows components that are easy to ignore and dangerous to over-trust. Its purpose is to support device discovery and interoperability, which creates a broad interface between local software, network-adjacent functionality, and privileged system behavior. That kind of component tends to have a complicated history because it must balance usability with strict security boundaries.Why device-hosting services are attractive targets
Any service that brokers requests on behalf of other processes is inherently sensitive. It may receive input from untrusted callers, transform that input, and then perform operations under a more privileged security context. If the authorization logic, memory handling, or object lifetime management is flawed, a local attacker may be able to trigger behavior that was never intended for their privilege level.That is why privilege-escalation bugs in services are so persistent across Windows releases. The surface area is not just the code that runs the service, but the way the service interacts with the operating system, COM objects, IPC mechanisms, and device-related trust decisions. A flaw in one of those layers can cascade into a much larger problem.
Enterprise and consumer exposure are not identical
For consumers, the immediate concern is often a single compromised workstation or a home PC with local malware. In that environment, an EoP in UPnP Device Host can be the difference between nuisance malware and full machine takeover. The user may not notice the bug directly, but an attacker who lands a foothold can use it to deepen persistence and disable defenses.For enterprises, the consequences are broader. A local privilege-escalation issue can help an attacker move from a low-privileged domain context to a host-admin position, which then opens the door to credential theft, defensive evasion, and lateral movement. Once SYSTEM-level access is achieved, the endpoint becomes a staging ground for broader compromise.
- Consumer risk is often about device takeover and persistence.
- Enterprise risk is often about lateral movement and escalation chains.
- Both scenarios are amplified when endpoints are poorly segmented.
- Local does not mean low consequence.
Why the name alone matters
Even without exploit specifics, the component name provides meaningful context. Windows services that manage devices or discovery frequently operate with a mix of local privileges and system-level access, which makes them a natural target for attackers who can manipulate parameters, messages, or state transitions. The public label therefore tells defenders enough to recognize the class of risk even when technical proof is not public.That is also why it is useful to map this kind of issue against prior Windows EoP patterns. Microsoft has repeatedly had to patch privilege bugs in services, brokers, and kernel-facing components because those are the structures attackers most want to corrupt after the initial breach. The pattern is old, but the operational consequences are still current.
How local privilege escalation changes the attack chain
A local privilege-escalation flaw rarely exists in isolation. It usually becomes useful after an attacker has already found a way onto the machine, and at that point the bug becomes a multiplier. That is what makes EoP vulnerabilities so important in incident response: they often explain how a modest intrusion became a full compromise.From foothold to SYSTEM
Once malware lands as a standard user, the attacker’s next challenge is to escape that limited context. If CVE-2026-32075 can be exploited locally by an authenticated user, then it potentially gives the attacker the ability to elevate into a more powerful security context, bypassing endpoint restrictions and gaining access to assets protected by the OS. In many post-exploitation playbooks, that is the step that unlocks privilege-sensitive operations.This kind of escalation can unlock:
- Credential dumping attempts,
- Service manipulation,
- Security product tampering,
- Scheduled task or startup abuse,
- Host-level persistence.
Why local bugs are still a major concern
Security teams sometimes underestimate local EoPs because they are not directly exposed over the network. That is a mistake. Initial access is frequently achieved through phishing, malicious attachments, stolen credentials, drive-by downloads, or abused remote management tooling. Once the attacker is inside, the difference between low privilege and high privilege is enormous.This is particularly true on managed endpoints where users have local software installations, cached credentials, or access to data that is valuable even without full admin rights. An EoP in a Windows service can be the bridge that converts that limited foothold into durable control. That bridge is what defenders should fear, not just the first foothold.
- Initial access is often easier than complete compromise.
- EoP closes the gap between a user shell and system control.
- Attackers value reliability more than elegance.
- A quiet escalation path is often more dangerous than a noisy exploit.
Why patch cadence matters here
Because local EoP bugs are so useful in the post-compromise phase, attackers can move quickly to integrate them into tooling. Once that happens, the patch window narrows dramatically. Even if public exploit code is not available on day one, security teams should assume that validation work starts immediately and that opportunistic use may follow.The practical response is straightforward: inventory affected systems, confirm update levels, and reduce the number of endpoints where a local attacker can remain long enough to benefit from a privilege bug. That is a standard response, but in a case like CVE-2026-32075 it is also the right one.
Microsoft’s disclosure style and what it means for defenders
Microsoft’s Security Update Guide has evolved into more than a list of patches. It is increasingly a risk-communication channel, where naming, scoring, confidence signals, and classification all matter. That makes advisories like CVE-2026-32075 useful not only for patching, but for understanding how Microsoft wants customers to interpret incomplete public detail.Sparse detail is not the same as low risk
A short description may reflect a deliberate choice to avoid publishing unnecessary technical breadcrumbs before customers have patched. It may also reflect the reality that Microsoft has enough confidence to publish the issue but not enough public detail to explain the precise root cause without compromising defensive value. In either case, the operational message is the same: act on the advisory, not on the absence of prose.This is especially important in the UPnP and device-hosting space, where public exploit detail can help attackers validate the bug rapidly. Vendors often walk a line between transparency and risk reduction, and the public advisory format is part of that balancing act. For defenders, the best reading is pragmatic: assume the bug is real, assume the patch is meaningful, and assume timing matters.
Vendor confirmation carries weight
When Microsoft assigns and publishes a CVE, it is effectively acknowledging that the vulnerability is tracked enough to be part of the company’s security maintenance process. That does not mean every detail is publicly confirmed to the same degree, but it does mean the issue has crossed the threshold from rumor to actionable advisory. In the context of enterprise patching, that threshold is the one that matters.This is why Microsoft’s confidence metric deserves more attention than it often gets. It offers a shorthand for how hard defenders should lean into remediation before the rest of the ecosystem catches up. In a monthly patch cycle with dozens of issues, that shorthand is useful because it helps triage. It is not perfect, but it is better than guessing.
- Vendor confirmation makes the issue operationally real.
- Confidence helps rank response urgency.
- Sparse detail should not be confused with uncertainty.
- Patch cadence should follow vendor confirmation, not rumor velocity.
How this affects security operations
For SOC and vulnerability-management teams, the main implication is simple: do not wait for someone else to explain the bug in blog-post form before beginning response work. Microsoft’s own framing provides enough to justify immediate prioritization, endpoint verification, and exposure mapping. If the issue affects a core Windows service, then patch verification should be treated as part of the incident-prevention baseline.That also means defenders should use their own telemetry aggressively. Look for unexpected local privilege escalation patterns, suspicious service interactions, and post-exploitation behavior that might indicate abuse of a Windows broker or device-hosting service. Even in the absence of known exploit signatures, behavior-based detection can reduce dwell time.
Why UPnP and device services keep reappearing in Windows advisories
UPnP-related components and device-broker services tend to recur in security discussions because they sit at a complicated intersection of convenience, compatibility, and trust. Windows has to support a huge range of devices, workflows, and legacy behaviors, and that breadth of support inevitably creates attack surface. CVE-2026-32075 is another reminder that those components are not background noise; they are part of the security core.Historical patterns in Windows service bugs
Microsoft has spent years tightening service hardening, privilege separation, and broker behavior, yet EoP issues keep surfacing in services that mediate user actions. That is not necessarily a sign of failure so much as a sign of complexity. When a platform must support both modern security expectations and decades of compatibility, some components will always be under pressure.Historically, privilege-escalation fixes in Windows often reveal the same themes:
- improper access control,
- unsafe object handling,
- race conditions,
- confused-deputy behavior,
- insufficient boundary enforcement.
Why “legacy” does not mean “safe”
UPnP, in particular, is one of those technologies that feels older than the modern security conversation, yet it continues to matter because systems still need interoperability. Legacy support is not a security defense. If anything, long-lived compatibility surfaces can become more dangerous over time because they accumulate assumptions, glue code, and exceptions that attackers can exploit.That is why administrators should not read a component name and conclude that the threat is niche. A long-lived feature can be embedded deeply enough that remediation is tied to operating system servicing rather than optional software updates. That makes patching less flexible but also more important, because you cannot simply remove the service without risking regressions.
- Legacy components may have broad compatibility needs.
- Broad compatibility tends to widen attack surface.
- Security debt accumulates in long-lived brokers.
- The oldest surfaces are often the hardest to retire.
Enterprise response priorities
Enterprise defenders should treat CVE-2026-32075 as a patch-management and exposure-management problem, not merely a software bulletin. The challenge is to determine where the relevant Windows service is present, whether the affected builds exist in the fleet, and how quickly patches can be safely validated and deployed. On managed systems, the difference between “published” and “remediated” is where risk lives.Immediate actions for administrators
The first step is to map the advisory to your Windows estate and ensure the vulnerable hosts are identified. Then verify whether endpoint-management tools have actually deployed the corresponding security update rather than just queued it. In large environments, update compliance often lags behind reporting, and local privilege bugs exploit exactly that gap.A sensible response sequence looks like this:
- Identify all impacted Windows builds and SKUs.
- Confirm the security update is installed, not just offered.
- Prioritize systems with higher user exposure or weaker segmentation.
- Monitor for signs of local exploitation or privilege abuse.
- Recheck vulnerable hosts after maintenance windows and reboots.
Monitoring and detection opportunities
The hardest part of local EoP defense is that it often looks like normal administrative behavior until it does not. That means defenders should correlate suspicious process trees, service interactions, and privilege transitions with the timing of the advisory. If a standard user suddenly triggers unusual service activity or if a low-privileged process is followed by SYSTEM-level actions, that is worth investigating.Endpoint detection and response tools can help, but only if they are tuned to identify escalation patterns. The key is not just detecting malware, but detecting the moment a lesser-privileged process becomes something more dangerous. That moment is often the true exploit event.
- Look for unusual service spawning behavior.
- Watch for unexpected token changes.
- Correlate local privilege escalation attempts with new persistence.
- Investigate post-patch exploitation attempts as well as pre-patch ones.
Consumer impact and the home user perspective
For home users, a Windows UPnP Device Host EoP may sound abstract, but the implications are practical. If malware lands on a machine through a download, fake update, or phishing lure, the exploit can help it cross from user-level access to deeper control. That can lead to browsers being hijacked, security settings changed, and personal files exposed or encrypted.Why home users should care
Most consumer systems are not protected by the same layered controls found in enterprise environments. Local administrator habits, minimal segmentation, and shared family-use patterns can make a privilege bug much more dangerous. Even a single compromised account can be enough for the attacker to stage a broader takeover if the local service can be abused.Home users are also less likely to notice subtle signs of escalation. A system may seem stable while the attacker uses elevated access to harvest data, tamper with settings, or disable protections. By the time the damage is visible, the exploitation path may have been active for days.
What practical defense looks like
For consumers, the best defense is plain but effective: install updates promptly, keep Windows security features enabled, and avoid creating unnecessary local admin exposure. If a machine is used for work, banking, or identity-sensitive tasks, it should be kept current and treated with the same seriousness as a business endpoint. Delay is the attacker’s ally.- Keep Windows updates current.
- Use standard user accounts when possible.
- Avoid disabling built-in protections.
- Back up important files before patch windows.
- Treat unexpected prompts or service behavior as suspicious.
Strengths and Opportunities
Microsoft’s publication of CVE-2026-32075 demonstrates a mature disclosure model, and that creates real value for defenders who know how to use it. The advisory gives enough information to act, even if it does not reveal every technical detail, and the confidence framing helps teams prioritize with more nuance than a bare CVE entry would allow. In that sense, the system is working the way it should: warning first, explanation later.- Clear component identification helps teams map exposure quickly.
- Elevation-of-privilege classification makes the risk easy to operationalize.
- Confidence metadata improves prioritization across crowded patch cycles.
- Vendor confirmation reduces ambiguity about whether the issue is real.
- Patchable framing gives defenders a concrete remediation path.
- Service-level context helps hunt for suspicious behavior after deployment.
- Enterprise tooling can use this signal to drive faster compliance checks.
Risks and Concerns
The obvious risk is that a local privilege-escalation flaw can be underestimated because it is not remote. That is a mistake defenders make repeatedly, especially when the public advisory is short and the component name sounds like background plumbing. In practice, local EoPs are often the pivot that turns a low-value compromise into a serious incident.- Sparse public detail may slow technical understanding for some teams.
- Local attack requirements can create false confidence in risk assessments.
- Attack chaining can make the flaw much more dangerous than it appears.
- Delayed patch verification leaves a gap for post-exploitation abuse.
- Telemetry blind spots may let privilege escalation go unnoticed.
- Legacy compatibility pressure can complicate remediation in some environments.
Looking Ahead
The most important next step is not more speculation about the root cause; it is execution. Administrators should confirm exactly which Windows builds are affected, validate update deployment, and watch for behavior that suggests privilege abuse on machines that have not yet been remediated. If Microsoft publishes additional detail later, that can refine hunting and root-cause analysis, but it should not delay response now.Security teams should also pay attention to whether this CVE appears in exploit kits, threat-intel feeds, or coordinated intrusion reports over the coming patch cycles. That will tell the industry whether the issue remains a cleanly handled advisory or becomes part of a live exploitation pattern. Even without public exploit code today, local privilege-escalation bugs have a habit of showing up in post-compromise tradecraft once attackers have time to study them.
- Confirm patch presence across all Windows endpoints.
- Review any delayed maintenance windows or offline systems.
- Watch for suspicious service interactions and token changes.
- Reassess the advisory if Microsoft adds more technical guidance.
- Correlate with threat intelligence for signs of chaining.
In the end, the value of Microsoft’s confidence metric is not that it replaces technical detail, but that it helps defenders act when detail is still limited. CVE-2026-32075 is a textbook example of why that matters: a privileged Windows service, a local escalation path, and enough vendor certainty to justify immediate attention. In modern Windows security, that combination is rarely harmless, and it should not be treated that way here.
Source: MSRC Security Update Guide - Microsoft Security Response Center