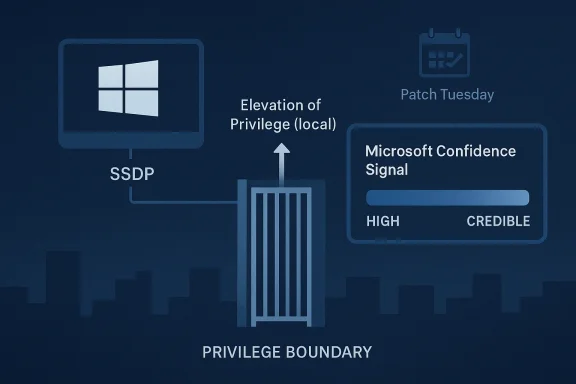
Microsoft’s handling of CVE-2026-32083 is a reminder that the most operationally important Windows security advisories are not always the ones with dramatic exploit narratives. In this case, the issue is framed as a Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability, and the real story is the confidence signal Microsoft attaches to the entry: a measure of how certain the company is that the vulnerability exists and how credible the known technical details are. That matters because defenders are not just deciding whether to patch; they are deciding how much weight to place on a vendor-acknowledged flaw when public technical detail is thin. The result is a vulnerability that sits at the intersection of exposure, trust, and patch urgency. s has long treated local privilege escalation as one of its most serious classes of bugs, even when the exploit path is not remotely reachable. That is partly because local bugs often become the final link in a compromise chain: a user-level foothold, a phished endpoint, or a lightly constrained service account can be turned into full system control. Microsoft’s own historical guidance has repeatedly described elevation-of-privilege flaws as issues that allow an attacker with existing access to run code in a higher privilege context, and that framing still applies here.
The SSDP service ii a class of Windows components that people often ignore until they fail. SSDP is tied to device discovery and network-adjacent plumbing, which means it can live for years as background infrastructure while quietly accumulating security debt. A service like that tends to matter far more in enterprise environments than in casual consumer discussions, because it can be present across fleets even when no one thinks of it as a “real” application.
Microsoft’s public update guidance has evolved toward richertal years, including standardized descriptions and advisory fields that help customers separate confirmed issues from tentative research leads. That evolution is important in this case because the confidence metric itself is part of the operational signal. The point is not merely that a CVE exists, but that Microsoft is telling defenders how much faith to place in the existence and technical explanation of the flaw.
There is also a broader pattern worth noting. In Windows security reporting, SSDP has been the kind ofrelevation-of-privilege advisories, often alongside other local bugs in kernel-adjacent or service-level components. That repetition suggests two things: the attack surface is persistent, and the defensive burden is cumulative. A single advisory may look routine, but over time these “routine” bugs become a meaningful part of the Windows patch-management load.
The user-facing description of Microsoft’s confidence metric is the most important part of the adveconfidence in the existence of the vulnerability and the credibility of the known technical details, which means it is really a quality signal for the advisory itself. That is different from exploitability, severity, or whether malware is already in circulation.
For administrators, that distinction is not academic. A confirmed vulnerability with minimal public detail still deserves priority if the component is widely deployed and the privilege boundary is meaningf a weak advisory; it is often a deliberately constrained one. Microsoft has historically published advisories with limited technical detail when disclosure is being managed carefully.
The operational implication is simple: when Microsoft signals confidence, defenders should treat the issue as real even if outside research has not yet filled in the technical blanks. Caution is warranted in interpreting root cause, but not in recognizing that the patch belongs in the urgerability teams need when they manage hundreds of entries per month.
This is why SSDP bugs have historically attracted attention even when they are “only” local elevation issues. Local privilege escalation can be the bridge between one compromised account and a full domain incident. In an enterprise setting, that means the difference between a user workstation event and a serious compromise of management tooling, credentials, or lateral-movht is the real multiplier
Consumer users may see SSDP as a background Windows service they never interact with. Enterprises, by contrast, see scale: thousands of endpoints, diverse configurations, patch windows, and local admin constraints. A vulnerability in a common system service becomes far more consequential when patch compliance is uneven and attackers can chain it with existing aclws security teams cannot treat this class of flaw as a niche issue. Even without public exploit detail, the combination of a Microsoft-confirmed CVE, a privilege boundary, and a service that sits close to system internals is enough to justify urgent review. That is especially true where hardening controls are inconsistent across endpoints.
This advisory fits that pattern neatly. It reinforces ttclosing weaknesses in deep system plumbing, and that defenders must think in terms of attack chain disruption, not just initial compromise prevention. The importance of the patch lies less in novelty than in how it blocks escalation after the first foothold.
A useful way to think about the cycle is this:
Consumers also benefit from the fact that Microsoft patches these bugs centrally. Unlike niche third-party software, Windows platform fixes usually ride along with the normal update channel. That said, the protection only exists after installation, and delayed updating still leaves the system exposed.
That is why the confidence metric is so useful for SOC and patch teams. It tells them the vulnerability is credible enough to act on even if exploit development details are still sparse. In a world of limited maintenance windows, credible is often good enough to patch first and investigate later. That iional stance.
The SSDP service’s placement in the operati this more than an abstract concern. When a flaw lives in a service that interacts with system-level plumbing or kernel-adjacent behavior, the practical outcome can be SYSTEM-level compromise. That is why Microsoft’s simple label “Elevation of Privilege” deserves serious treatment in incident planning.
That is also why the confidence metadata matters so much. It helps separate “interesting research” from “confirmed vendor issue,” which changes how quickly defenders should move. Even a sparse advisory can be operationally decisive.
The advisory also reinforces a healthy security practice: patching should be driven by trusted vendor confirmation, not by sensationalism. That creates an opportunity for teak-ranking models around Windows components that are old, common, and deeply embedded. The more transparent the metadata, the better the prioritization.
Another concern is that obscure services can slip through patch validation and asset inventory gaps. If teams do not know where SSDP is enabled, they may not know where to focus testing or validation. That creates a falseafter the patch is released.
More broadly, this advisory is another sign that Windows security in 2026 is increasingly about confidence management as much as vulnerability management. Security teams are no longer just asking, “Is there a patch?” They are asking, “How sure is the vendor, how likely is exploitation, and how quickly can we close the path before it becomes part of a chain?” That is a better question set, and Microsoft’s metadata is clearly designed to support it.
Source: MSRC Security Update Guide - Microsoft Security Response Center
The SSDP service ii a class of Windows components that people often ignore until they fail. SSDP is tied to device discovery and network-adjacent plumbing, which means it can live for years as background infrastructure while quietly accumulating security debt. A service like that tends to matter far more in enterprise environments than in casual consumer discussions, because it can be present across fleets even when no one thinks of it as a “real” application.
Microsoft’s public update guidance has evolved toward richertal years, including standardized descriptions and advisory fields that help customers separate confirmed issues from tentative research leads. That evolution is important in this case because the confidence metric itself is part of the operational signal. The point is not merely that a CVE exists, but that Microsoft is telling defenders how much faith to place in the existence and technical explanation of the flaw.
There is also a broader pattern worth noting. In Windows security reporting, SSDP has been the kind ofrelevation-of-privilege advisories, often alongside other local bugs in kernel-adjacent or service-level components. That repetition suggests two things: the attack surface is persistent, and the defensive burden is cumulative. A single advisory may look routine, but over time these “routine” bugs become a meaningful part of the Windows patch-management load.
 What the Confidence Metric Actually Means
What the Confidence Metric Actually Means
The user-facing description of Microsoft’s confidence metric is the most important part of the adveconfidence in the existence of the vulnerability and the credibility of the known technical details, which means it is really a quality signal for the advisory itself. That is different from exploitability, severity, or whether malware is already in circulation.Confidence is not the same as severity
A high-confidence advisory does not automatically mean the flaw is easy to exploit or broadly weaponized. It means Microsoft believes the bug iting technical information is solid enough to publish and track. In practice, that should increase defender urgency even when the write-up is sparse, because uncertainty around existence is one of the main reasons organizations delay patching.For administrators, that distinction is not academic. A confirmed vulnerability with minimal public detail still deserves priority if the component is widely deployed and the privilege boundary is meaningf a weak advisory; it is often a deliberately constrained one. Microsoft has historically published advisories with limited technical detail when disclosure is being managed carefully.
Why Microsoft uses this language
Microsoft’s Security Update Guide has progressively emphasized structured vulnerability descriptions, including CVSS-linked metadata and clearer advisory language. The company’s shift toward this style suggests eithout waiting for third-party analysis. That is especially useful for obscure Windows services where public proof-of-concept material may never arrive.The operational implication is simple: when Microsoft signals confidence, defenders should treat the issue as real even if outside research has not yet filled in the technical blanks. Caution is warranted in interpreting root cause, but not in recognizing that the patch belongs in the urgerability teams need when they manage hundreds of entries per month.
Why SSDP Still Matters
SSDP is one of those Windows components that feels old-fashioned until it becomes important. It is part of the networking and device-discovery ecosystem that helps Windows participate in local network environments, and that kind of subsystem tends to be exposed enough to matter but mundane enough to be ovelege escalation flaw shows up there, it raises immediate questions about code age, service hardening, and whether the issue reflects legacy design assumptions.Legacy components can be dangerous precisely because they are familiar
Enterprise defenders often focus on new products, cloud services, and visible attack surfaces because those are the areas generating headlines. Legacy services such as SSDP are different. They may be less glamorous, but they are embedded in the platform, often enabled by default, and frequently trusted by other components. That makes them an attractive target for attackers seeking quiet privilege gains rather than noisy remote compromise.This is why SSDP bugs have historically attracted attention even when they are “only” local elevation issues. Local privilege escalation can be the bridge between one compromised account and a full domain incident. In an enterprise setting, that means the difference between a user workstation event and a serious compromise of management tooling, credentials, or lateral-movht is the real multiplier
Consumer users may see SSDP as a background Windows service they never interact with. Enterprises, by contrast, see scale: thousands of endpoints, diverse configurations, patch windows, and local admin constraints. A vulnerability in a common system service becomes far more consequential when patch compliance is uneven and attackers can chain it with existing aclws security teams cannot treat this class of flaw as a niche issue. Even without public exploit detail, the combination of a Microsoft-confirmed CVE, a privilege boundary, and a service that sits close to system internals is enough to justify urgent review. That is especially true where hardening controls are inconsistent across endpoints.
How This Fits Microsoft’s 2026 Patch Cadence
CVE-2026-32083 does not appear i oft has been shipping large monthly rollups with numerous elevation-of-privilege fixes across kernel, service, and driver surfaces. That context matters because it shows how much of Windows security is now a game of continuous maintenance rather than one-off crises.March and April 2026 illustrate the pattern
Across the 2026 update cycle, Microsoft has repeatedly patcscalation issues in components like ProjFS, ATBroker, CDPSvc, and other system services. The public pattern is clear: many of the most important fixes are not remote code execution headlines, but local elevation bugs that become dangerous after an attacker already has limited access. That is the shape of modern Windows defensive work.This advisory fits that pattern neatly. It reinforces ttclosing weaknesses in deep system plumbing, and that defenders must think in terms of attack chain disruption, not just initial compromise prevention. The importance of the patch lies less in novelty than in how it blocks escalation after the first foothold.
Patch Tuesday is now a systems-level planning exercise
For IT teams, the challenge is not whether to patch, but how to sequence, test, and validate changes without breaking endpoints. Microsoft’s servicing guidance in 2026 has reflected increasing complexity, including update ordering and offline image servicing concerns in some packages. That broader servicing burden makes confidence signals more valuable, because they help teams prioritize among dozens of “important” items.A useful way to think about the cycle is this:
- Identify whether the affected component is enabled or installed in your estate.
- Determine whether the vulnerability is local-only or part of a chain.
- Prioritize the patch based on privilege boundary and deployment exposure.
- Verify remediation across all build branches and managed images.
- Reassess hardening to reduce the blast radius if exploitation occurs.
Enterprise Impact vs Consumer Impact
For home users, CVE-2026-32083 is mainly a reminder to install Windows updates promptly. The risk still matters, because local privilege escalation can turn a compromised standard account int one. But the likelihood of strategic exploitation is generally higher in managed environments where the attacker can move from a low-privilege foothold to broader access.Consumer systems: quiet but not irrelevant
Consumer devices often rely on default services and shared administrative habits that can still make local bugs useful. If an attacker gains execution through malware, phishing, or a malicious download, an EoP flaw can be the difference between cleanup and reinfection. That is why even “just local” vulnerabilities remain significant on endpoints.Consumers also benefit from the fact that Microsoft patches these bugs centrally. Unlike niche third-party software, Windows platform fixes usually ride along with the normal update channel. That said, the protection only exists after installation, and delayed updating still leaves the system exposed.
Enterprise systems: the real blast radius
In enterprise environments, SSDP-related privilege escalation deserves a different level of concern. Attackers with any authenticated foothold may be able to pivot into service-level or system-level control, and that can become an incident involving credential theft, persistence, or lateral movement. The consequence is not just endpoint compromise; it is the possibility of stepping stones into broader infrastructure.That is why the confidence metric is so useful for SOC and patch teams. It tells them the vulnerability is credible enough to act on even if exploit development details are still sparse. In a world of limited maintenance windows, credible is often good enough to patch first and investigate later. That iional stance.
The Security Meaning of a Local Elevation Bug
Local elevation vulnerabilities are often underestimated because they are not glamorous. They do not usually let an attacker click a link and instantly own a server. Instead, they reward persistence, patience, and a willingness to combine them with another initial access method. That makes them especially attractive to real-world attackers.Why attackers like them
A local privilege escalation flaw is valuable because it reduces the cost of turning a foothold into control. Malware operators and hands-on-keyboard intruders frequently use one bug to land, another to elevate, and a third to spread. Even if CVE-2026-32083 is not widely weaponized today, the class of vulnerability has a clear place in adversary tradecraft.The SSDP service’s placement in the operati this more than an abstract concern. When a flaw lives in a service that interacts with system-level plumbing or kernel-adjacent behavior, the practical outcome can be SYSTEM-level compromise. That is why Microsoft’s simple label “Elevation of Privilege” deserves serious treatment in incident planning.
Why attackers do not need public exploit code to care
One of the recurring misconceptions in vulnerability management is that a lack of public exploit details means low danger. In reality, a confirmed local EoP vulnerability may be exploitable by operators long before public proof-of-concept code appears. The patch window is therefore a race against both disclosure and experimentation.That is also why the confidence metadata matters so much. It helps separate “interesting research” from “confirmed vendor issue,” which changes how quickly defenders should move. Even a sparse advisory can be operationally decisive.
What Administrators Should Do Now
The safest response is straightforward: treat CVE-2026-32083 as a real, patchable Windows privilege escalation issue and verify remediation across all relevant systems. If your environment includes SSDP-dependent roles, older images, or endpoints with delayed servicing, this should be added to the immediate patch backlog. The guidance is not speculative; it is grounded in Microsoft’s own confidence framing for the advisory.Practical defensive steps
- Confirm whether SSDP-related services are enabled or present in your Windows baseline.
- Prioritize patching on systems that already have local footholds or shared admin access.
- Verify deployment across workstations, servers, and gold images rather than assuming one patch wave covers everything.
- Review local admin sprawl, because privilege escalation bugs become much more dangerous when users already have excessive rights.
- Check for delayed-update populatirk laptops and seldom-booted virtual machines.
- Watch for signs of chained compromise in telemetry, especially unusual service execution or privilege transitions.
- Treat the advisory as credible even if incomplete; do not wait for a fuller public reverse-engineering write-up.
Strengths and Opportunities
Microsoft’s approach to CVE-2026-32083 has one major strength: it gives defenders a confidence signal that can be used immediately for triage. That is erprises where patch queues are crowded and not every advisory deserves equal treatment. It also reflects the broader maturitye metadata, which increasingly helps security teams make faster decisions.The advisory also reinforces a healthy security practice: patching should be driven by trusted vendor confirmation, not by sensationalism. That creates an opportunity for teak-ranking models around Windows components that are old, common, and deeply embedded. The more transparent the metadata, the better the prioritization.
- Clear vendor confidence helps separate confirmed issues from uncertain research.
- **Local privilege escalatio map into real-world incident chains.
- SSDP is a reminder that legacy services still deserve active defense.
- Patch guidance can be prioritized more intelligently when public detail is sparse.
- Enterprise fleets benefit from stronger triage logic acrosies.
- Telemetry correlation can be tuned to watch for privilege boundary abuse.
- Security baselines can be tightened around services that are rarely needed.
Risks and Concerns
The biggest concern is that many organizations still underestimate local EoP bugs because they do not read like urgent remote exploits. That is dangerous, because a foothold plus a privilege escalation is often enough to turn an ordinary endpoint incident into a system-wide response. In other words, the risk is not just the bug; it is the combination of the bug with weak operational hygiene.Another concern is that obscure services can slip through patch validation and asset inventory gaps. If teams do not know where SSDP is enabled, they may not know where to focus testing or validation. That creates a falseafter the patch is released.
- Underestimation of local EoP flaws can delay remediation.
- Incomplete inventory can leave SSDP-enabled systems outside the patch plan.
- Delayed servicing on remote or rarely used endpoints can prolong exposure.
- Excessive local rights can make exploitation much easier.
- Limited public detail can create analyst uncertainty and slow response.
- Chained attacks can magnify the impact far beyond the original CVE.
- Legacy service exposure can persist even when the service is no longer obviously used.
Looking Ahead
The next question is whether Microsoft or independent researchers will publish more technical detail about CVE-2026-32083. That detail may never be extensive, and in many cases it does not need to be for defenders to act. What matters now is whether the patch is fully deployed and whether the underlying service exposure is actually necessary in each environment.More broadly, this advisory is another sign that Windows security in 2026 is increasingly about confidence management as much as vulnerability management. Security teams are no longer just asking, “Is there a patch?” They are asking, “How sure is the vendor, how likely is exploitation, and how quickly can we close the path before it becomes part of a chain?” That is a better question set, and Microsoft’s metadata is clearly designed to support it.
- Finalize deployment of the relevant Windows update across all rings.
- Verify SSDP exposure and disable the service where it is unnecessary.
- Re-check endpoint privilege assignments and local administrator scope.
- Look for correlated post-exploitation activity in endpoint and identity logs.
- Reassess patch prioritization rules to account for confidence-rated advisories.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: