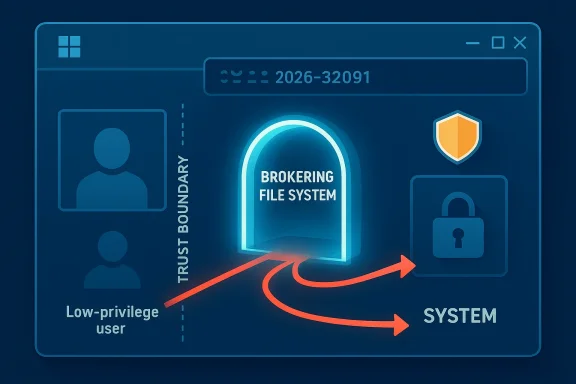
Microsoft has published a new Windows vulnerability entry for CVE-2026-32091, describing it as a Microsoft Brokering File System Elevation of Privilege Vulnerability. The title alone signals a local privilege-escalation issue in a Windows component that historically sits close to the file system and can therefore have outsized impact when security boundaries fail. Microsoft’s own severity language around this class of bug usually implies that an attacker may need prior access to the device, but could then move from a low-privilege account to much more powerful control.
The most important detail here is that the description emphasizes confidence in the vulnerability’s existence and the credibility of the technical details, rather than a root-cause narrative. In other words, this is the sort of advisory that tells defenders the issue is real and materially relevant, even if the public record does not yet spell out the full exploit chain. That distinction matters, because enterprise teams often have to decide whether to prioritize a patch on certainty alone.
The Microsoft Brokering File System has become a recurring source of elevation-of-privilege issues over the past several Windows release cycles. That alone is a useful clue: repeated bug class clustering is rarely random, and it usually points to a privileged service or subsystem that brokers file access between less trusted callers and highly trusted system contexts. Once a component like that is exposed to attacker-controlled input, even small mistakes can become powerful escalation paths.
Microsoft’s modern Security Update Guide is designed to surface these issues quickly, with the public CVE page serving as the canonical advisory entry. The company has spent years moving toward more machine-readable and transparent vulnerability reporting, including its Security Update Guide, CVRF APIs, and newer CSAF publishing efforts. That makes the public entry itself a first-class artifact, not merely a placeholder until a more detailed post appears later.
Historically, Brokering File System bugs have tended to be local privilege escalation problems affecting newer Windows platforms and server builds. That pattern is important because local EoP flaws are often underestimated by consumers but highly valued by attackers once they already have a foothold. A low-privilege account on a desktop, jump box, or server can be the difference between a contained incident and full system compromise.
Microsoft has also been increasingly explicit that file-system-based EoP issues often depend on interactions with privileged processes, junctions, path handling, or race conditions. Its later work on filesystem mitigations such as RedirectionGuard shows how seriously the company treats these classes of attacks, especially where privileged code touches attacker-influenced paths. That context suggests the Brokering File System family sits in a genuinely sensitive part of the Windows security model.
For defenders, the practical takeaway is straightforward: when Microsoft flags a Brokering File System flaw, it is rarely cosmetic. These bugs can provide the final step in a multi-stage compromise, allowing an attacker to pivot from ordinary user access to broader control. That makes even a seemingly narrow vulnerability strategically significant.
That matters because the confidence metric is more than a paperwork detail. High confidence implies that the vulnerability is real, reproducible, and likely exploitable under the right conditions. It also hints that attackers would not need to reverse-engineer an imaginary flaw from vague symptoms; they would have enough technical substance to build on.
In operational terms, that changes how security teams should read the advisory. A low-confidence item can be triaged as a watch-list issue, but a high-confidence local EoP in a trusted Windows subsystem deserves immediate attention. Especially in enterprise estates with shared workstations, developer laptops, or servers where standard users can obtain interactive access, the risk calculus becomes much more urgent.
This is why file-system EoP issues are often more consequential than their labels suggest. They do not necessarily allow remote code execution on their own, but they frequently become the reliable bridge from user-level foothold to admin-level persistence. For ransomware operators and hands-on keyboard intruders, that bridge is extremely valuable.
Microsoft’s own RedirectionGuard guidance underscores the importance of defending against unsafe junction traversal and filesystem redirection attacks. The company explains that an attacker who can influence privileged filesystem operations may be able to redirect operations into protected locations, tamper with files, or induce code execution in a privileged context. That is a powerful reminder that the filesystem is often a security boundary, not just a storage layer.
Earlier disclosures such as CVE-2024-28907, CVE-2024-26213, and CVE-2025-49694 all reinforced the same basic lesson: local privilege escalation in filesystem brokers is not a theoretical concern. Each new CVE adds to the evidence that attackers have found a productive seam in the Windows security model. It is an uncomfortable but useful signal for defenders that a subsystem may require more scrutiny than the public headline alone implies.
That history also tells us something about Microsoft’s patching posture. The company has not ignored the problem, which is good, but repeated issues in the same family suggest that remediation can be incremental rather than structural. In security engineering terms, that usually means patches close individual bugs, while the surrounding design continues to attract fresh research.
The Brokering File System family has historically been associated with conditions that are easier for a local attacker to manipulate than for a remote one. That usually means the attacker already has some form of authenticated access, but the value of the exploit is high because the prize is elevated control. In ransomware incidents, that can mean disabling protections, spreading to adjacent systems, or tampering with backup agents.
What is not known publicly yet matters less than what is known operationally: Microsoft has identified this as a real elevation-of-privilege issue in a privileged Windows component. That alone is enough to warrant patch validation and host-level hardening. You do not need a public proof-of-concept to take the risk seriously.
The impact is amplified in environments with shared systems, VDI pools, jump servers, and developer workstations. Those systems often have many users, elevated tooling, or complex trust relationships, making local escalation more valuable. A vulnerability like CVE-2026-32091 can therefore be a force multiplier for an intrusion that looked modest at first.
Windows Server environments deserve separate attention. Even if the flaw is “local,” server administrators sometimes assume servers are protected because only a small number of people log on interactively. But service accounts, remote administration, automation tooling, and scheduled tasks all expand the real attack surface. That assumption can be dangerously optimistic.
Consumers also tend to underestimate the significance of privilege escalation because they focus on visible symptoms. A system that seems to “just work” may still be operating under silent compromise, and an elevated attacker can hide more effectively, install persistence, or modify browser and security settings. That makes timely patching important even for home devices that are not part of a corporate network.
The broader consumer issue is trust. Windows users expect the operating system to enforce boundaries between ordinary apps and protected system functions. When a brokered subsystem fails, that trust boundary weakens, and the user may not notice until the damage is already done. By then, recovery is often much harder than prevention.
For this class of flaw, patch management should focus on the systems most likely to be reachable by an attacker with user-level access. That includes endpoints with frequent browsing, document handling, software development, and remote access. The more opportunities a threat actor has to gain an initial foothold, the more important the EoP becomes.
Monitoring also matters. If the flaw is being actively explored in the wild, defenders should look for suspicious privilege transitions, anomalous service behavior, and unexpected filesystem changes around the time of patch deployment. A quiet local exploit can leave surprisingly noisy side effects if you know where to look.
That matters because a repeated vulnerability class often pushes vendors toward platform-level defenses rather than one-off fixes. If Microsoft can reduce the exploitability of an entire class of path or broker abuse, it gains leverage across many future CVEs. That is a better outcome than shipping successive point patches that only address individual bugs.
The hard part is that platform fixes often take time to mature. Meanwhile, attackers continue to search for the next variant. That tension is why CVE-2026-32091 should be seen both as an immediate patching issue and as part of a longer engineering story.
The larger opportunity is to use this CVE as a forcing function for better local-privilege hygiene and endpoint hardening. A single advisory can justify stronger standard-user policies, tighter control over admin access, and more aggressive patch verification. It can also help security teams revisit whether their current telemetry is good enough to catch privilege escalation in progress.
The less obvious risk is patch lag. Organizations often move slower than they think, especially on endpoints that are offline, intermittently connected, or tied to delicate application dependencies. If exploitation research emerges quickly, those lagging devices can become easy targets.
Watch how Microsoft layers future mitigations around brokered filesystem access. A single patch often solves the immediate bug, but repeated issues in the same subsystem usually produce broader hardening later. That may include more guardrails, tighter validation, or changes that reduce how much privileged code trusts caller-controlled path state.
Security teams should keep an eye on whether the broader Brokering File System family continues to generate CVEs in 2026. If it does, that would reinforce the argument that this remains a structurally sensitive area of Windows. If it does not, the current advisory may represent another step in a long-running hardening process that is finally paying off.
CVE-2026-32091 reinforces a durable truth in Windows security: local does not mean minor, and a brokered trust failure can be every bit as dangerous as a remote bug once the wrong user lands on the machine. The organizations that respond fastest, reduce standing privilege, and watch for escalation patterns will be best positioned to absorb the risk. The ones that wait for exploit proof may discover too late that the proof was already built into the compromise chain.
Source: MSRC Security Update Guide - Microsoft Security Response Center
The most important detail here is that the description emphasizes confidence in the vulnerability’s existence and the credibility of the technical details, rather than a root-cause narrative. In other words, this is the sort of advisory that tells defenders the issue is real and materially relevant, even if the public record does not yet spell out the full exploit chain. That distinction matters, because enterprise teams often have to decide whether to prioritize a patch on certainty alone.
 Background
Background
The Microsoft Brokering File System has become a recurring source of elevation-of-privilege issues over the past several Windows release cycles. That alone is a useful clue: repeated bug class clustering is rarely random, and it usually points to a privileged service or subsystem that brokers file access between less trusted callers and highly trusted system contexts. Once a component like that is exposed to attacker-controlled input, even small mistakes can become powerful escalation paths.Microsoft’s modern Security Update Guide is designed to surface these issues quickly, with the public CVE page serving as the canonical advisory entry. The company has spent years moving toward more machine-readable and transparent vulnerability reporting, including its Security Update Guide, CVRF APIs, and newer CSAF publishing efforts. That makes the public entry itself a first-class artifact, not merely a placeholder until a more detailed post appears later.
Historically, Brokering File System bugs have tended to be local privilege escalation problems affecting newer Windows platforms and server builds. That pattern is important because local EoP flaws are often underestimated by consumers but highly valued by attackers once they already have a foothold. A low-privilege account on a desktop, jump box, or server can be the difference between a contained incident and full system compromise.
Microsoft has also been increasingly explicit that file-system-based EoP issues often depend on interactions with privileged processes, junctions, path handling, or race conditions. Its later work on filesystem mitigations such as RedirectionGuard shows how seriously the company treats these classes of attacks, especially where privileged code touches attacker-influenced paths. That context suggests the Brokering File System family sits in a genuinely sensitive part of the Windows security model.
For defenders, the practical takeaway is straightforward: when Microsoft flags a Brokering File System flaw, it is rarely cosmetic. These bugs can provide the final step in a multi-stage compromise, allowing an attacker to pivot from ordinary user access to broader control. That makes even a seemingly narrow vulnerability strategically significant.
What Microsoft Is Signaling
The public wording around CVE-2026-32091 focuses on the existence and credibility of the vulnerability, which is a notable clue in itself. Microsoft is effectively telling customers that this is not speculative research, but a confirmed issue serious enough to warrant a distinct CVE. When a vendor uses that framing, it often means the core security boundary failure is sufficiently understood for remediation to proceed, even if the public disclosure remains sparse.That matters because the confidence metric is more than a paperwork detail. High confidence implies that the vulnerability is real, reproducible, and likely exploitable under the right conditions. It also hints that attackers would not need to reverse-engineer an imaginary flaw from vague symptoms; they would have enough technical substance to build on.
In operational terms, that changes how security teams should read the advisory. A low-confidence item can be triaged as a watch-list issue, but a high-confidence local EoP in a trusted Windows subsystem deserves immediate attention. Especially in enterprise estates with shared workstations, developer laptops, or servers where standard users can obtain interactive access, the risk calculus becomes much more urgent.
Why confidence matters
A vulnerability with a clear root cause is easier to weaponize. It also tends to be easier to validate in testing, which can accelerate exploitation after patch release. Defenders should assume that any confirmed EoP in a privileged broker is a plausible target for post-exploitation tooling and offensive research.- Confirmed vulnerabilities tend to be weaponized faster than vague or speculative issues.
- Local EoP bugs are especially dangerous after phishing, malware, or credential theft.
- Brokered file-system components often sit at a trust boundary attackers love to abuse.
- Public CVE entries can be enough for threat actors to begin targeting patched and unpatched systems differently.
Why Brokering File System Bugs Matter
The Brokering File System is not just another Windows service name; it sits in a class of components that mediate file access on behalf of other processes. That mediation is where the risk lives. When a privileged broker makes a bad decision about path handling, access checks, synchronization, or trust boundaries, the result can be system-level abuse.This is why file-system EoP issues are often more consequential than their labels suggest. They do not necessarily allow remote code execution on their own, but they frequently become the reliable bridge from user-level foothold to admin-level persistence. For ransomware operators and hands-on keyboard intruders, that bridge is extremely valuable.
Microsoft’s own RedirectionGuard guidance underscores the importance of defending against unsafe junction traversal and filesystem redirection attacks. The company explains that an attacker who can influence privileged filesystem operations may be able to redirect operations into protected locations, tamper with files, or induce code execution in a privileged context. That is a powerful reminder that the filesystem is often a security boundary, not just a storage layer.
The attacker’s path
A typical local EoP chain is often boring in outline and devastating in effect. The attacker starts with a standard user or a compromised low-privilege account, then uses a bug in a trusted service to cross into a privileged context. Once there, the attacker can write to protected locations, hijack execution, or plant persistence.- Initial access through phishing, stolen credentials, or a weak local account.
- Privileged broker interaction through a vulnerable file-system pathway.
- Escalation to SYSTEM or a comparable high-trust context.
- Persistence, defense evasion, or lateral movement after privilege gain.
Historical Context: A Familiar Pattern
CVE-2026-32091 arrives after a long series of Brokering File System disclosures in prior years. Microsoft and third-party vulnerability trackers have repeatedly listed BF-related elevation-of-privilege issues across recent Windows generations, including Windows 11 and Windows Server 2025-era builds. That history suggests the attack surface is both real and persistent, not an isolated one-off.Earlier disclosures such as CVE-2024-28907, CVE-2024-26213, and CVE-2025-49694 all reinforced the same basic lesson: local privilege escalation in filesystem brokers is not a theoretical concern. Each new CVE adds to the evidence that attackers have found a productive seam in the Windows security model. It is an uncomfortable but useful signal for defenders that a subsystem may require more scrutiny than the public headline alone implies.
That history also tells us something about Microsoft’s patching posture. The company has not ignored the problem, which is good, but repeated issues in the same family suggest that remediation can be incremental rather than structural. In security engineering terms, that usually means patches close individual bugs, while the surrounding design continues to attract fresh research.
What repeated CVEs imply
Repeated disclosures in the same subsystem usually indicate one or more of three things. Either the component is hard to secure because it must perform complex privileged mediation, or the attack surface is large enough to invite repeated errors, or both. In a Windows environment, those conditions are all plausible.- The broker may need to handle many edge cases and path types.
- Multiple product generations may share related code paths.
- Race conditions and trust confusion are notoriously hard to eliminate completely.
- Attackers only need one viable exploit path to make the flaw valuable.
Exploitability and Real-World Risk
A local elevation-of-privilege vulnerability can be deceptively dangerous because it often sits at the end of an intrusion chain rather than the start. Attackers do not always need it to enter the network; they need it to finish the job after initial access. That makes the issue especially relevant in environments where endpoint compromise is already a realistic threat.The Brokering File System family has historically been associated with conditions that are easier for a local attacker to manipulate than for a remote one. That usually means the attacker already has some form of authenticated access, but the value of the exploit is high because the prize is elevated control. In ransomware incidents, that can mean disabling protections, spreading to adjacent systems, or tampering with backup agents.
What is not known publicly yet matters less than what is known operationally: Microsoft has identified this as a real elevation-of-privilege issue in a privileged Windows component. That alone is enough to warrant patch validation and host-level hardening. You do not need a public proof-of-concept to take the risk seriously.
Likely attack scenarios
The exact chain for CVE-2026-32091 may remain undisclosed for a while, but the most likely scenarios are familiar. A compromised user session, a malicious insider account, or a low-privilege foothold from malware could all set the stage for exploitation. From there, a local broker flaw could give the attacker the SYSTEM-equivalent leverage they need to persist.- Malware drops a foothold under a standard user.
- The attacker probes the brokered filesystem path handling.
- Privilege is escalated through a trusted Windows code path.
- System services, security tools, or protected files are then targeted.
Enterprise Impact
For enterprises, the biggest concern is not a single machine compromise but the blast radius that comes after privilege escalation. Once an attacker reaches SYSTEM or a comparable privileged context, they can often tamper with software deployment tooling, disable endpoint security, access sensitive files, or prepare for lateral movement. That turns one endpoint into a foothold for broader compromise.The impact is amplified in environments with shared systems, VDI pools, jump servers, and developer workstations. Those systems often have many users, elevated tooling, or complex trust relationships, making local escalation more valuable. A vulnerability like CVE-2026-32091 can therefore be a force multiplier for an intrusion that looked modest at first.
Windows Server environments deserve separate attention. Even if the flaw is “local,” server administrators sometimes assume servers are protected because only a small number of people log on interactively. But service accounts, remote administration, automation tooling, and scheduled tasks all expand the real attack surface. That assumption can be dangerously optimistic.
Enterprise priorities
A mature enterprise response is not just “patch it.” It is also asset identification, exposure mapping, and exploit-path reduction. Security teams should care about which systems are most likely to host low-privilege interactive users and which systems expose the most powerful post-escalation opportunities.- Prioritize systems with many standard-user logons.
- Review endpoints that allow lateral movement from user sessions.
- Pay special attention to developer, admin, and shared-use devices.
- Validate patch deployment on Windows builds that match the advisory scope.
- Watch for privilege escalation indicators after suspicious logons.
Consumer Impact
For consumers, a vulnerability like this is more about the integrity of the device than about enterprise-style lateral movement. A personal Windows PC is still at risk if malware, a malicious script, or a compromised app gains standard-user execution. Once that happens, a local EoP can convert a nuisance infection into something much harder to remove.Consumers also tend to underestimate the significance of privilege escalation because they focus on visible symptoms. A system that seems to “just work” may still be operating under silent compromise, and an elevated attacker can hide more effectively, install persistence, or modify browser and security settings. That makes timely patching important even for home devices that are not part of a corporate network.
The broader consumer issue is trust. Windows users expect the operating system to enforce boundaries between ordinary apps and protected system functions. When a brokered subsystem fails, that trust boundary weakens, and the user may not notice until the damage is already done. By then, recovery is often much harder than prevention.
What home users should do
Home users do not need to become security analysts, but they do need disciplined update hygiene. The safest course is to install Microsoft’s cumulative updates promptly, especially on systems that are already exposed to the internet, used for work, or shared among family members. Consumers should also keep an eye on security software alerts and suspicious behavior after logins or downloads.- Install Windows updates as soon as they are available and validated.
- Reboot fully so the patch actually takes effect.
- Avoid running untrusted installers or scripts.
- Keep antivirus and browser protections current.
- Treat unusual prompts for elevated permissions as suspicious.
Patch Management and Defensive Response
The first response to a confirmed Windows EoP should be routine but urgent: inventory, patch, validate, and monitor. That sounds basic because it is. Yet many incidents become expensive because organizations underestimate the time needed to get from vendor disclosure to full fleet coverage.For this class of flaw, patch management should focus on the systems most likely to be reachable by an attacker with user-level access. That includes endpoints with frequent browsing, document handling, software development, and remote access. The more opportunities a threat actor has to gain an initial foothold, the more important the EoP becomes.
Monitoring also matters. If the flaw is being actively explored in the wild, defenders should look for suspicious privilege transitions, anomalous service behavior, and unexpected filesystem changes around the time of patch deployment. A quiet local exploit can leave surprisingly noisy side effects if you know where to look.
Operational checklist
A practical response plan should be clear, fast, and reproducible. Security teams that already have monthly patch playbooks can fold this advisory into the highest-priority queue if the affected builds are present. If not, they should at least classify the issue as a standing escalation item for the next maintenance window.- Confirm which Windows versions and builds are in scope.
- Prioritize internet-facing and user-rich endpoints first.
- Deploy Microsoft’s cumulative security update.
- Reboot and verify the installed build level.
- Watch for post-patch instability or exploitation indicators.
How This Fits Microsoft’s Broader Security Direction
Microsoft has been steadily refining how it communicates and mitigates vulnerability classes tied to file system redirection and trusted brokers. That effort includes modern advisory publication, machine-readable advisory formats, and explicit mitigations like RedirectionGuard for certain path-traversal risks. The company is clearly treating filesystem trust boundaries as a strategic area, not just an implementation detail.That matters because a repeated vulnerability class often pushes vendors toward platform-level defenses rather than one-off fixes. If Microsoft can reduce the exploitability of an entire class of path or broker abuse, it gains leverage across many future CVEs. That is a better outcome than shipping successive point patches that only address individual bugs.
The hard part is that platform fixes often take time to mature. Meanwhile, attackers continue to search for the next variant. That tension is why CVE-2026-32091 should be seen both as an immediate patching issue and as part of a longer engineering story.
Security architecture lessons
There are broader lessons here for Windows security design. Systems that broker privileged file access need extremely careful boundary validation, and they need to assume attackers will manipulate paths, timing, and object lifetimes. If not, the broker itself becomes the trust failure.- Privileged brokers should validate untrusted input aggressively.
- Race-prone code needs defensive synchronization and review.
- Path handling should assume attacker-controlled edge cases.
- Mitigations should reduce the impact of failures, not just the frequency.
Strengths and Opportunities
Microsoft’s public handling of CVE-2026-32091 has a few notable strengths. The advisory naming is direct, the issue class is clear, and the confidence framing helps defenders prioritize without waiting for a lengthy proof-of-concept narrative. That kind of clarity is valuable because it helps organizations act before attackers do.The larger opportunity is to use this CVE as a forcing function for better local-privilege hygiene and endpoint hardening. A single advisory can justify stronger standard-user policies, tighter control over admin access, and more aggressive patch verification. It can also help security teams revisit whether their current telemetry is good enough to catch privilege escalation in progress.
- Clear vendor identification of the affected subsystem.
- High-priority signal for patch triage and risk-based scheduling.
- Opportunity to reduce standing local admin exposure.
- Chance to improve telemetry around privilege transitions.
- Motivation to review hardening on shared and developer systems.
- Useful reminder that local bugs can have enterprise-scale consequences.
Risks and Concerns
The obvious risk is that a confirmed local EoP in a brokered file system component gives attackers a high-value post-exploitation path. Even if initial access is rare, the payoff from successful escalation is substantial. That makes the bug attractive both to opportunistic malware authors and to more targeted intruders.The less obvious risk is patch lag. Organizations often move slower than they think, especially on endpoints that are offline, intermittently connected, or tied to delicate application dependencies. If exploitation research emerges quickly, those lagging devices can become easy targets.
- Potential for rapid weaponization after public disclosure.
- Strong value as a post-exploitation step in multi-stage intrusions.
- Patch delays on edge devices and laptops.
- Hidden exposure in server automation and service accounts.
- Possible operational disruption during update rollout.
- Risk that defenders underestimate a “local” issue.
Looking Ahead
The next few weeks will likely determine how serious this CVE becomes in practice. If Microsoft’s patch is stable and no exploit activity appears, the issue may remain an important but manageable local EoP. If researchers or threat actors publish reliable details, however, it could quickly become part of routine post-compromise tradecraft.Watch how Microsoft layers future mitigations around brokered filesystem access. A single patch often solves the immediate bug, but repeated issues in the same subsystem usually produce broader hardening later. That may include more guardrails, tighter validation, or changes that reduce how much privileged code trusts caller-controlled path state.
Security teams should keep an eye on whether the broader Brokering File System family continues to generate CVEs in 2026. If it does, that would reinforce the argument that this remains a structurally sensitive area of Windows. If it does not, the current advisory may represent another step in a long-running hardening process that is finally paying off.
- Confirm which Windows builds are affected and updated.
- Track whether exploitation telemetry starts to emerge.
- Reassess local admin exposure on high-value endpoints.
- Monitor for follow-on Microsoft hardening updates.
- Review whether related filesystem-broker CVEs appear later in the year.
CVE-2026-32091 reinforces a durable truth in Windows security: local does not mean minor, and a brokered trust failure can be every bit as dangerous as a remote bug once the wrong user lands on the machine. The organizations that respond fastest, reduce standing privilege, and watch for escalation patterns will be best positioned to absorb the risk. The ones that wait for exploit proof may discover too late that the proof was already built into the compromise chain.
Source: MSRC Security Update Guide - Microsoft Security Response Center