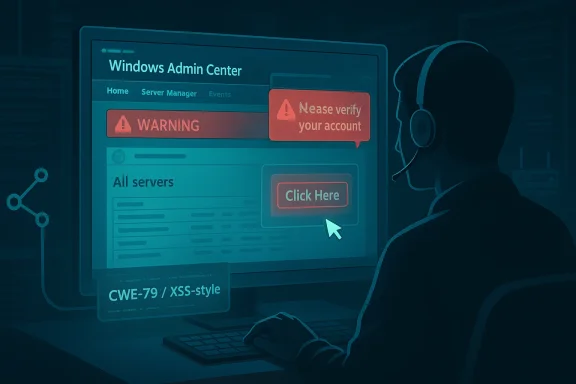
CVE-2026-32196 is a useful reminder that not every Windows security flaw arrives as a dramatic remote code execution headline. In this case, Microsoft’s Security Update Guide entry for Windows Admin Center Spoofing Vulnerability appears to place the issue in the broad, deceptively practical category of trust-manipulation bugs: the kind that can reshape what an administrator sees, believes, or clicks in a management console. Third-party tracking currently describes the flaw as a CWE-79/XSS-style issue with a CVSS 3.1 base score of 6.1, and the public description frames it as spoofing over a network with user interaction required. (cvefeed.io)
Windows Admin Center has long occupied an awkward but important place in Microsoft’s management stack. It is the modern, web-based tool administrators use to manage Windows servers and related infrastructure, which means it sits directly in the path of privileged operational decisions. That makes even a “medium” severity spoofing issue worth more attention than the label alone might suggest, because management interfaces are not ordinary user-facing websites; they are trusted control planes.
The broader significance of CVE-2026-32196 comes from the combination of three traits: it is tied to a management surface, it is categorized as spoofing, and the public technical description suggests a web-page-generation weakness. In practical terms, those conditions imply that an attacker’s goal is not necessarily to crash a service or dump memory, but to manipulate the interface or content that an operator relies on. That is often enough to create downstream compromise if the victim is persuaded to trust the wrong action, page, or context. (cvefeed.io)
Microsoft’s own vulnerability taxonomy has long treated spoofing as a distinct class of security problem, separate from pure code execution or privilege escalation. The distinction matters because spoofing bugs are frequently underappreciated: they can facilitate phishing, session confusion, UI deception, or trust boundary violations without looking catastrophic at first glance. In an administrative console, that can still be highly consequential.
There is also a timing angle worth noting. The record currently visible on the public tracker shows CVE-2026-32196 being added on April 14, 2026, with a concise description and a limited amount of exploit detail. That pattern fits a modern disclosure model in which vendors confirm the existence of a flaw but intentionally keep enough low-level detail back to reduce abuse. For defenders, the existence of the advisory itself is already a signal that the issue has crossed from theory into tracked reality. (cvefeed.io)
The second signal is that the issue is not presented as a remote exploit with no interaction at all. The public CVSS vector shown by cvefeed indicates network attack vector, low attack complexity, no privileges required, and user interaction required, with a changed scope. That combination usually points to an exploit that still needs a human to load, view, or trigger something, but can cross a boundary once successful. (cvefeed.io)
That is exactly why spoofing is so dangerous in enterprise tooling. Even if the technical root cause is “only” cross-site scripting or input handling during page generation, the security consequence can still be trust poisoning. An attacker who can influence what the admin sees may not need to fully own the host immediately; they only need to alter the next action the admin takes. That is often enough to begin a compromise chain. (cvefeed.io)
Windows Admin Center also lives in the same ecosystem as Azure integration, server management, and other high-value workflows. Microsoft’s own documentation on known issues shows that the product is used in environments where browser behavior, popups, Azure sign-in, and gateway configuration all matter. That makes the product a dense intersection of authentication, UI, and management logic, which is exactly where spoofing weaknesses tend to become operationally important.
That also means defenders should avoid overreading the “medium” score as harmless. A low-to-moderate score can still be dangerous if it lands in the right place, and admin tooling is one of the places where moderate scores can translate into high real-world consequence. Risk is contextual, not just numerical. (cvefeed.io)
Microsoft’s modern vulnerability guidance has also become more explicit about communicating confidence and exploitability. That is a practical improvement for defenders because it helps separate confirmed issues from placeholder advisories and distinguish technical uncertainty from business urgency. In security operations, that distinction saves time.
A sensible response sequence would look like this:
For Microsoft, the strategic challenge is preserving the appeal of Windows Admin Center while proving that the product can be hardened at the same pace as the rest of the platform. That is important because administrators increasingly expect management tools to behave like secure cloud services, not old intranet dashboards. Security is now part of the product’s value proposition.
We should also watch for whether independent researchers validate the advisory with additional analysis. If the issue proves to be a straightforward XSS-like rendering bug, defenders will likely focus on patching and access control. If it turns out to be part of a broader trust-boundary weakness in the admin workflow, the response may expand to browser policy, session handling, and gateway design. That distinction could change how enterprises prioritize remediation. (cvefeed.io)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Windows Admin Center has long occupied an awkward but important place in Microsoft’s management stack. It is the modern, web-based tool administrators use to manage Windows servers and related infrastructure, which means it sits directly in the path of privileged operational decisions. That makes even a “medium” severity spoofing issue worth more attention than the label alone might suggest, because management interfaces are not ordinary user-facing websites; they are trusted control planes.The broader significance of CVE-2026-32196 comes from the combination of three traits: it is tied to a management surface, it is categorized as spoofing, and the public technical description suggests a web-page-generation weakness. In practical terms, those conditions imply that an attacker’s goal is not necessarily to crash a service or dump memory, but to manipulate the interface or content that an operator relies on. That is often enough to create downstream compromise if the victim is persuaded to trust the wrong action, page, or context. (cvefeed.io)
Microsoft’s own vulnerability taxonomy has long treated spoofing as a distinct class of security problem, separate from pure code execution or privilege escalation. The distinction matters because spoofing bugs are frequently underappreciated: they can facilitate phishing, session confusion, UI deception, or trust boundary violations without looking catastrophic at first glance. In an administrative console, that can still be highly consequential.
There is also a timing angle worth noting. The record currently visible on the public tracker shows CVE-2026-32196 being added on April 14, 2026, with a concise description and a limited amount of exploit detail. That pattern fits a modern disclosure model in which vendors confirm the existence of a flaw but intentionally keep enough low-level detail back to reduce abuse. For defenders, the existence of the advisory itself is already a signal that the issue has crossed from theory into tracked reality. (cvefeed.io)
What Microsoft Appears to Be Signaling
The first signal is certainty. Microsoft’s update-guide process is built not just to label a weakness, but to communicate that the weakness is real enough to document and monitor. The wording here is spare, but the entry’s presence itself suggests that Microsoft considers the issue credible and actionable. That matters more than the exact amount of technical detail on day one.Confidence Is Part of the Message
Microsoft has previously explained that the Security Update Guide is meant to help customers understand vulnerability severity and context, not merely serve as a catalog of CVE identifiers. In practice, that means a short advisory can still carry a strong operational message: patch, assess exposure, and assume the issue is real unless later guidance proves otherwise. That is especially true for administrative products where trust and authentication are part of the attack surface.The second signal is that the issue is not presented as a remote exploit with no interaction at all. The public CVSS vector shown by cvefeed indicates network attack vector, low attack complexity, no privileges required, and user interaction required, with a changed scope. That combination usually points to an exploit that still needs a human to load, view, or trigger something, but can cross a boundary once successful. (cvefeed.io)
- Confidence matters because Microsoft is distinguishing confirmed issues from speculative ones.
- User interaction means the vulnerability may hinge on a click, navigation event, or rendered content.
- Changed scope suggests the impact may extend beyond the component that first processes the input.
- Low attack complexity means the barrier to abuse may not be especially high once a target is identified. (cvefeed.io)
Why the Score Is Not the Whole Story
A 6.1 score is not trivial, but it is also not the kind of number that typically forces emergency shutdowns across every enterprise. What it does mean is that administrators should read the vulnerability in context: a weakness in Windows Admin Center can be more valuable than a higher-scoring bug in a lower-trust peripheral component because it targets the control layer. The blast radius of an admin-plane flaw can be disproportionately large. (cvefeed.io)How Spoofing Changes the Risk Profile
Spoofing vulnerabilities deserve a special kind of attention because they often attack judgment rather than memory safety. If an attacker can make a legitimate admin interface appear to say something it does not, or render attacker-controlled content inside a trusted context, the end result can be misconfiguration, credential exposure, or unauthorized action. That is why spoofing bugs in admin tools are rarely “just UX issues.”The Admin Trust Problem
Windows Admin Center is designed for administrators who are already operating under pressure. They are switching among servers, settings, alerts, and remediations, often with elevated rights and limited time. In that environment, the smallest interface deception can have outsized effect because the user is primed to trust the console as part of the management workflow.That is exactly why spoofing is so dangerous in enterprise tooling. Even if the technical root cause is “only” cross-site scripting or input handling during page generation, the security consequence can still be trust poisoning. An attacker who can influence what the admin sees may not need to fully own the host immediately; they only need to alter the next action the admin takes. That is often enough to begin a compromise chain. (cvefeed.io)
The XSS Connection
The cvefeed tracking page maps CVE-2026-32196 to CWE-79, which is the canonical weakness class for improper neutralization of input during web page generation, commonly associated with cross-site scripting. That does not automatically mean a textbook browser exploit with flashy payloads; in an administrative app, XSS-like behavior can also manifest as interface manipulation, session-context abuse, or malicious data echoed into privileged pages. (cvefeed.io)- XSS in admin tools is often more dangerous than in ordinary websites.
- Trusted context amplifies the impact of attacker-controlled output.
- Session handling can become part of the attack path if a console is already authenticated.
- Content rendering flaws are especially sensitive in web-based management dashboards. (cvefeed.io)
Why Windows Admin Center Matters So Much
Windows Admin Center is not a consumer-facing product where a spoofed page might simply annoy a user. It is part of the operational backbone for many Windows environments, bridging local and remote management tasks and often acting as a front door into server administration. A vulnerability in that surface can therefore influence multiple systems, not just one console session.A Control Plane, Not Just a Web App
That distinction changes the threat model. A web application used for admin work is effectively a control plane, and control planes are valuable precisely because they concentrate privilege. When spoofing hits a control plane, the issue is no longer merely “can someone impersonate a page?” but “can someone redirect an operator’s trust in a way that changes infrastructure state?”Windows Admin Center also lives in the same ecosystem as Azure integration, server management, and other high-value workflows. Microsoft’s own documentation on known issues shows that the product is used in environments where browser behavior, popups, Azure sign-in, and gateway configuration all matter. That makes the product a dense intersection of authentication, UI, and management logic, which is exactly where spoofing weaknesses tend to become operationally important.
Enterprise vs Consumer Impact
For enterprises, the concern is not just a single compromised workstation. It is whether an attacker can use a spoofing flaw to manipulate privileged admins, seed malicious configuration, or misdirect remediation efforts. For consumers, Windows Admin Center is generally not the same everyday touchpoint, so the practical exposure is narrower. But in a data center or hybrid cloud environment, this can be a serious enterprise-class trust flaw.What the Public Technical Data Suggests
The public record is still limited, but limited data can still be meaningful. The description on the cvefeed page says the issue is “improper neutralization of input during web page generation” in Windows Admin Center, allowing an unauthorized attacker to perform spoofing over a network. That language strongly implies the root problem is not authentication logic alone, but how untrusted input reaches rendered content. (cvefeed.io)Reading the Vector Carefully
The CVSS vector attached to the entry is particularly instructive: AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N. In plain English, that suggests a network-reachable issue with low complexity, no privileges required, user interaction required, changed scope, and limited confidentiality and integrity impact rather than broad system destruction. That profile is consistent with a vulnerability that aims to deceive or manipulate, not necessarily to fully weaponize the host immediately. (cvefeed.io)That also means defenders should avoid overreading the “medium” score as harmless. A low-to-moderate score can still be dangerous if it lands in the right place, and admin tooling is one of the places where moderate scores can translate into high real-world consequence. Risk is contextual, not just numerical. (cvefeed.io)
What We Can and Cannot Conclude
What we can conclude is that Microsoft has acknowledged a spoofing weakness in Windows Admin Center, and that third-party aggregators currently map it to XSS-style input handling. What we cannot conclude, from the public data alone, is exactly which page, parameter, or workflow is affected, or whether there are practical exploit chains in the wild. Until Microsoft publishes more detail, caution is the right default. (cvefeed.io)- Confirmed: a spoofing flaw exists in Windows Admin Center.
- Likely: the issue involves improper output handling or echoed input.
- Unclear: the exact attack path and any real-world exploitation.
- Actionable: administrators should treat the advisory as real and relevant. (cvefeed.io)
Historical Context: Why This Kind of Bug Keeps Reappearing
If this advisory feels familiar, that is because spoofing and web-rendering issues have a long history across Microsoft products. Microsoft has repeatedly published security bulletins and advisories for spoofing vulnerabilities in browsers, RPC services, TLS-related trust flows, and administrative interfaces. The recurring theme is not that Microsoft ignores the problem, but that systems built around trust are inherently hard to harden perfectly.The Pattern Behind the Pattern
The deeper lesson is that spoofing bugs often emerge where a product blends user interface, identity, and transport trust. Windows Admin Center does exactly that: it is a browser-based management app that must faithfully represent actions, session state, and remote system data. Any place where untrusted data can flow into that environment becomes a candidate for abuse.Microsoft’s modern vulnerability guidance has also become more explicit about communicating confidence and exploitability. That is a practical improvement for defenders because it helps separate confirmed issues from placeholder advisories and distinguish technical uncertainty from business urgency. In security operations, that distinction saves time.
A Familiar Enterprise Lesson
Enterprises often patch what looks catastrophic and delay what looks cosmetic. Spoofing flaws exploit exactly that bias because they are easy to underestimate. Yet many of the most effective enterprise compromises begin with user deception, not kernel-level privilege escalation. That is why a medium-severity spoofing advisory in an admin console deserves scrutiny alongside the flashier CVEs. (cvefeed.io)Defensive Priorities for Administrators
The immediate priority is to inventory Windows Admin Center deployments and assess whether they are exposed in a way that makes the spoofing issue relevant. Even if the exploit requires user interaction, any reachable admin portal is worth treating as sensitive until patched. In a management product, “reachable” often matters almost as much as “remote.” (cvefeed.io)What Admins Should Do First
Administrators should start with the basics: confirm the version in use, check Microsoft’s advisory entry, and verify whether the deployment is internet-facing, intranet-only, or restricted through a proxy or gateway model. They should also review whether multiple admins use the system, because shared administrative workflows can make spoofing more operationally dangerous. (cvefeed.io)A sensible response sequence would look like this:
- Identify every Windows Admin Center instance in the environment.
- Determine whether the instance is reachable from untrusted networks.
- Verify patch status against Microsoft’s advisory.
- Review browser and gateway configuration for trust assumptions.
- Communicate the risk to teams that perform routine server administration. (cvefeed.io)
Hardening the Surrounding Surface
Even before a patch is deployed, organizations can reduce risk by tightening access to the gateway, limiting exposure to trusted networks, and avoiding unnecessary privilege sprawl among admins. They should also be especially cautious about anything that could amplify a spoofing flaw, such as overly permissive browser behavior, stale sessions, or weak separation between administrative roles. Defense in depth still matters when the bug is “just” spoofing.- Restrict exposure of the management surface.
- Audit admin access and role distribution.
- Review browser trust assumptions around the console.
- Patch promptly once Microsoft’s fix is validated.
- Monitor for abnormal admin actions that may follow deceptive UI behavior. (cvefeed.io)
Competitive and Market Implications
Microsoft has spent years pushing Windows administration toward a more unified, browser-based model, and Windows Admin Center is part of that story. But as enterprises centralize management, they also concentrate risk. A spoofing flaw in the management plane becomes a reminder that the convenience of a web console comes with an attack surface that looks increasingly like a modern application stack.Why This Matters Beyond Microsoft
Rivals in the systems-management space face the same fundamental tradeoff: richer web UIs improve usability, but they also create more opportunities for injection, trust confusion, and browser-context abuse. CVE-2026-32196 therefore fits a broader industry pattern rather than a Microsoft-specific exception. Every vendor that ships an admin portal is in the same trust business, whether it wants to be or not. (cvefeed.io)For Microsoft, the strategic challenge is preserving the appeal of Windows Admin Center while proving that the product can be hardened at the same pace as the rest of the platform. That is important because administrators increasingly expect management tools to behave like secure cloud services, not old intranet dashboards. Security is now part of the product’s value proposition.
The Broader Trust Economy
Spoofing flaws also affect vendor credibility in subtle ways. If administrators begin to worry that a management UI may present manipulated content, trust in the entire control plane erodes, even if the flaw is quickly patched. That can slow adoption, encourage workarounds, and push enterprises to layer on more restrictive access controls than they otherwise would. (cvefeed.io)Strengths and Opportunities
The most encouraging aspect of this disclosure is that Microsoft has surfaced the issue through its normal vulnerability pipeline rather than leaving customers to discover it through incident response. That gives defenders a clear chance to act, and it gives Microsoft the opportunity to reinforce best practices around secure rendering and admin-session protection. The bug may be real, but so is the chance to improve the product. (cvefeed.io)- Clear vendor acknowledgment gives defenders a concrete response target.
- Moderate scoring suggests the issue is serious but still manageable with good process.
- User-interaction requirement may limit opportunistic mass abuse.
- Management-plane visibility means the flaw can be prioritized appropriately.
- Opportunity to harden rendering paths may produce lasting security gains.
- Better admin education can reduce the success rate of spoofing attempts.
- Improved trust in the product is possible if Microsoft ships a strong fix and guidance. (cvefeed.io)
Risks and Concerns
The biggest concern is that a spoofing flaw in Windows Admin Center can be dismissed as a UI issue when it is really a trust issue. If attackers can use the weakness to alter what an administrator believes, the downstream impact can extend well beyond the initial vulnerability class. In a privileged console, deception can be the first step in a much larger compromise. (cvefeed.io)- Admins may underestimate spoofing because it lacks the drama of RCE.
- Shared administrative workflows can magnify the value of a successful exploit.
- User interaction means phishing-like conditions may be enough for abuse.
- Changed scope raises concern about impact beyond the initial component.
- Insufficient public detail makes exact risk modeling harder for defenders.
- Delayed patching could leave exposed management portals vulnerable longer than necessary.
- Supply-chain and hybrid-cloud workflows can widen the operational blast radius. (cvefeed.io)
Looking Ahead
The next meaningful development will be Microsoft’s own follow-up guidance. If the company publishes more technical detail, administrators will get a better sense of the precise attack pattern, the affected workflows, and whether any special mitigations are needed beyond ordinary patching. Until then, the right posture is disciplined caution rather than speculation. (cvefeed.io)We should also watch for whether independent researchers validate the advisory with additional analysis. If the issue proves to be a straightforward XSS-like rendering bug, defenders will likely focus on patching and access control. If it turns out to be part of a broader trust-boundary weakness in the admin workflow, the response may expand to browser policy, session handling, and gateway design. That distinction could change how enterprises prioritize remediation. (cvefeed.io)
- Microsoft patch details for the affected Windows Admin Center versions.
- Independent technical analysis confirming exploit path and exposure.
- Any evidence of exploitation or proof-of-concept publication.
- Follow-up hardening guidance for gateway and browser trust settings.
- Enterprise advisories from security teams and national CERTs. (cvefeed.io)
Source: MSRC Security Update Guide - Microsoft Security Response Center