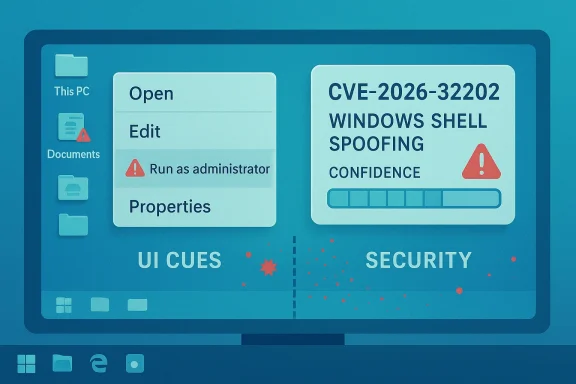
The Microsoft Security Response Center’s entry for CVE-2026-32202 points to a Windows Shell spoofing vulnerability, but the public-facing description is doing something just as important as naming the flaw: it is signaling how much confidence Microsoft has in the issue and how much technical detail is currently available to attackers. In Microsoft’s vulnerability taxonomy, that confidence level matters because a confirmed vulnerability generally implies a clearer exploit path, stronger attacker interest, and a higher likelihood that defenders should treat it as a real deployment priority. What makes this disclosure notable is not only the Windows Shell brand name, but the fact that spoofing bugs in shell-related components tend to sit in the awkward middle ground between “annoying UI issue” and “serious trust boundary problem.” That is exactly the kind of ambiguity security teams hate, because it can be easy to underestimate.
Windows Shell vulnerabilities have a long history of looking deceptively small from the outside while carrying outsize implications once an attacker understands the interaction model. The shell is not just a launcher for files and folders; it is one of the deepest trust surfaces in Windows, touching icons, file associations, context menus, previews, shortcuts, and user-facing prompts. A spoofing flaw in this area can matter because users often rely on shell presentation to decide whether they are opening a trusted object or interacting with a legitimate system element.
Microsoft’s use of the phrase “spoofing vulnerability” is especially important. Spoofing bugs are often about deception rather than direct code execution, which means the immediate effect may be convincing a user or system into believing something false. That can be enough to bypass human judgment, trick an admin into approving the wrong action, or make a malicious object look like a benign one. In enterprise environments, those failures can cascade far beyond one endpoint.
The confidence metric described in the update guide is also a clue about the stage of the vulnerability’s lifecycle. Microsoft is essentially saying that the flaw exists with some degree of certainty, but the public may not yet have a full exploit narrative, deep root-cause disclosure, or independent proof-of-concept. That is a useful distinction for defenders because confirmed but sparse is usually more urgent than speculative but noisy. It is also a reminder that attackers often learn from the same breadcrumbs defenders see.
Historically, Windows Shell issues have been dangerous because users tend to trust visible system cues, and attackers know that. A visually convincing file, shortcut, icon, dialog box, or folder can alter behavior without ever needing kernel-level compromise. The result is that even when the underlying issue seems “only” like spoofing, the practical outcome can be credential theft, malicious execution, or social engineering that is far harder to detect after the fact.
There is also a subtle enterprise dimension here. Security controls often assume that employees can visually identify safe versus unsafe content, yet shell spoofing attacks directly target that assumption. In other words, these bugs do not merely abuse software; they abuse confidence in software.
The Windows Shell has historically been a recurring attack surface because it bridges files, UI, and user intent. Many past Windows issues have relied on misleading icons, deceptive filenames, manipulated shortcuts, or crafted objects that exploit the way Windows renders or interprets content. Those techniques do not always need a complex exploit chain. Sometimes the goal is simply to create enough confusion that a user behaves as the attacker wants.
This matters in 2026 because modern endpoint defense is better than it used to be, but the human layer remains stubbornly exploitable. Phishing, attachment abuse, shortcut abuse, and lookalike content all work best when they can attach themselves to familiar system behavior. A shell spoofing vulnerability fits neatly into that pattern, because the shell is where users decide what something is before they interact with it.
Microsoft’s confidence metric, as described in the vulnerability entry, exists to help customers prioritize. A confirmed vulnerability with limited public detail often means defenders should prepare for additional disclosures, patch guidance, or security research to follow. The immediate technical specifics may be sparse, but the operational significance is already real: if Microsoft has assigned a CVE and labeled it as a shell spoofing issue, security teams should treat it as a live trust-boundary concern rather than a theoretical edge case.
A high-confidence entry can still be quiet in the wild, but it deserves attention because it may become weaponized quickly once enough technical details emerge. The history of Windows security shows that attackers are very good at turning vague but real findings into practical chains.
This is why shell spoofing bugs are not trivial cosmetic problems. They can serve as an entry point for malware delivery, privilege escalation social engineering, or hidden file execution pathways. The software need not crash to be dangerous.
It is also why attackers prefer attacks that align with routine workflows. The less unusual the action appears, the more likely the user is to accept it. The appearance of normality is the whole point.
For defenders, that distinction changes triage. A confirmed issue should move faster through patch review, risk assessment, and endpoint validation than a vague rumor. The absence of public exploit details is not the same as the absence of risk.
This is one reason vendors sometimes keep details sparse until patches are broadly available. The less the initial disclosure reveals, the less useful it is to opportunistic actors in the short term. Still, even a minimal label can be enough for determined researchers to start connecting dots.
Security operations teams should also consider the detection problem. Spoofing events may look like ordinary user activity until later stages of compromise appear. That lag is where attackers win time.
The threat is especially acute where people rely on visual confirmation rather than policy enforcement. If a malicious object can imitate a trusted one, then training alone may not be enough. Organizations need layered controls that reduce dependence on human interpretation.
That historical pattern is why shell spoofing should never be dismissed as cosmetic. A convincing lookalike can be enough to set up a later compromise path. Visual fidelity is not harmless when it is weaponized.
This is also one reason Microsoft’s vulnerability management has evolved toward richer contextual guidance. The company knows that a one-line description often underestimates how much a user-facing issue can matter in practice. CVE-2026-32202 fits into that tradition.
A useful response posture includes validation of file origin, inspection of object metadata, and careful review of recent shell-handling events. In many cases, the earliest indicator will be a user complaint that something looked normal but behaved differently. That kind of report should not be dismissed.
A strong response plan should include quick communication to users. When interface deception is the threat, awareness matters. People cannot report what they have been taught to ignore.
The flip side is that sparse disclosure can frustrate defenders who need more context for risk modeling. Security teams may want to know whether the vulnerability requires local access, user interaction, or special conditions. Without that detail, they must make assumptions, and assumptions create either overreaction or delay.
This is especially relevant as enterprises consolidate identities and workflows across cloud services, desktop environments, and web apps. The more integrated the user experience becomes, the more valuable a credible-looking spoof becomes to an attacker. That is a market problem as much as a technical one.
Enterprises should watch for signals that indicate the attack surface is broader than first described. That includes changes to the advisory, updated guidance from Microsoft, and any signs that security vendors are adding detections or mitigations. The most important thing is not to wait for proof of widespread abuse before taking the issue seriously. By then, the advantage is usually gone.
If Microsoft’s confidence level is any indication, CVE-2026-32202 is not a curiosity to file away for later. It is a reminder that the boundary between interface and security is still one of the most strategically important lines in Windows. Once that boundary can be bent, the attacker’s job becomes much easier, and the defender’s margin for error becomes much smaller.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Windows Shell vulnerabilities have a long history of looking deceptively small from the outside while carrying outsize implications once an attacker understands the interaction model. The shell is not just a launcher for files and folders; it is one of the deepest trust surfaces in Windows, touching icons, file associations, context menus, previews, shortcuts, and user-facing prompts. A spoofing flaw in this area can matter because users often rely on shell presentation to decide whether they are opening a trusted object or interacting with a legitimate system element.Microsoft’s use of the phrase “spoofing vulnerability” is especially important. Spoofing bugs are often about deception rather than direct code execution, which means the immediate effect may be convincing a user or system into believing something false. That can be enough to bypass human judgment, trick an admin into approving the wrong action, or make a malicious object look like a benign one. In enterprise environments, those failures can cascade far beyond one endpoint.
The confidence metric described in the update guide is also a clue about the stage of the vulnerability’s lifecycle. Microsoft is essentially saying that the flaw exists with some degree of certainty, but the public may not yet have a full exploit narrative, deep root-cause disclosure, or independent proof-of-concept. That is a useful distinction for defenders because confirmed but sparse is usually more urgent than speculative but noisy. It is also a reminder that attackers often learn from the same breadcrumbs defenders see.
Historically, Windows Shell issues have been dangerous because users tend to trust visible system cues, and attackers know that. A visually convincing file, shortcut, icon, dialog box, or folder can alter behavior without ever needing kernel-level compromise. The result is that even when the underlying issue seems “only” like spoofing, the practical outcome can be credential theft, malicious execution, or social engineering that is far harder to detect after the fact.
Why shell spoofing matters
The shell is one of the few Windows components that nearly every user touches daily. That ubiquity makes it valuable to attackers because it gives them a broad audience and a familiar context in which to hide. A flaw that changes what users believe they are seeing can be more exploitable than a technically deeper issue that affects only specialists.There is also a subtle enterprise dimension here. Security controls often assume that employees can visually identify safe versus unsafe content, yet shell spoofing attacks directly target that assumption. In other words, these bugs do not merely abuse software; they abuse confidence in software.
- Windows Shell sits in a high-trust, high-frequency user path.
- Spoofing can be enough to redirect judgment without obvious malware behavior.
- User interface deception is often an effective precondition for larger compromise.
- Enterprise users are especially vulnerable when they act on trusted-looking prompts.
- Security telemetry may miss the earliest stage if no code execution occurs.
Background
Microsoft publishes vulnerability entries for a reason beyond compliance: each record helps set expectations around certainty, severity, and response urgency. The description attached to CVE-2026-32202 is less about dramatic exploitation details and more about confidence in the finding. That makes the advisory framework itself part of the story, because Microsoft is signaling that something meaningful has been identified even if the public details remain thin.The Windows Shell has historically been a recurring attack surface because it bridges files, UI, and user intent. Many past Windows issues have relied on misleading icons, deceptive filenames, manipulated shortcuts, or crafted objects that exploit the way Windows renders or interprets content. Those techniques do not always need a complex exploit chain. Sometimes the goal is simply to create enough confusion that a user behaves as the attacker wants.
This matters in 2026 because modern endpoint defense is better than it used to be, but the human layer remains stubbornly exploitable. Phishing, attachment abuse, shortcut abuse, and lookalike content all work best when they can attach themselves to familiar system behavior. A shell spoofing vulnerability fits neatly into that pattern, because the shell is where users decide what something is before they interact with it.
Microsoft’s confidence metric, as described in the vulnerability entry, exists to help customers prioritize. A confirmed vulnerability with limited public detail often means defenders should prepare for additional disclosures, patch guidance, or security research to follow. The immediate technical specifics may be sparse, but the operational significance is already real: if Microsoft has assigned a CVE and labeled it as a shell spoofing issue, security teams should treat it as a live trust-boundary concern rather than a theoretical edge case.
Confidence versus exploitability
The existence of a CVE does not automatically mean there is a public exploit. It does, however, mean the issue has crossed a threshold where Microsoft believes it is credible enough to track, communicate, and remediate. That distinction matters because defenders often confuse confirmed vulnerability with active exploitation, when the two are not the same.A high-confidence entry can still be quiet in the wild, but it deserves attention because it may become weaponized quickly once enough technical details emerge. The history of Windows security shows that attackers are very good at turning vague but real findings into practical chains.
- Confirmed vulnerabilities can be more urgent than speculative reports.
- Spoofing flaws often sit at the intersection of UI trust and user action.
- Shell abuse remains relevant because it is deeply embedded in daily workflow.
- Public detail scarcity should not be mistaken for low risk.
- Patch prioritization should account for trust-boundary impact, not only exploit code.
How Spoofing Attacks Work in the Shell Layer
At a basic level, a spoofing flaw is about causing the system or the user to perceive something differently from what it really is. In the shell, that can mean one object appearing to be another, one file type masquerading as another, or one action looking safer than it truly is. The user response is often the exploit’s real payload.Presentation is part of the attack surface
Windows presents icons, thumbnails, filenames, metadata, context menu options, and shell overlays as part of normal operation. That presentation is useful, but it is also exploitable because users tend to trust it. If malicious content can shape what the shell displays, then the UI itself becomes a channel for deception.This is why shell spoofing bugs are not trivial cosmetic problems. They can serve as an entry point for malware delivery, privilege escalation social engineering, or hidden file execution pathways. The software need not crash to be dangerous.
The hidden power of trust cues
Users often judge objects based on what they think the shell is telling them. If the shell implies that something is a folder, a document, or a benign installer, people may act on that assumption without second-guessing the underlying object. That makes a spoofing issue especially effective against rushed users and administrators who move quickly.It is also why attackers prefer attacks that align with routine workflows. The less unusual the action appears, the more likely the user is to accept it. The appearance of normality is the whole point.
- Icons and thumbnails can create false confidence.
- File associations can hide the real behavior of content.
- Context menus can make malicious actions look routine.
- User speed increases exploit success when cues are misleading.
- Administrative users are not immune, because they often trust system visuals.
Why Microsoft’s Confidence Metric Matters
Microsoft’s vulnerability language is often more informative than casual readers realize. The confidence metric described for CVE-2026-32202 is not merely bureaucratic wording; it helps defenders estimate how solid the underlying evidence is and how much technical knowledge an attacker might already have. That is especially useful when public details are incomplete.What “confidence” implies
A vulnerability with high confidence usually means Microsoft has enough internal evidence to believe the issue is real and reproducible, even if the company has not published all of the technical background. That can come from internal analysis, partner reports, coordinated disclosure, or corroborating research. The key point is that Microsoft is not presenting a mere hypothesis.For defenders, that distinction changes triage. A confirmed issue should move faster through patch review, risk assessment, and endpoint validation than a vague rumor. The absence of public exploit details is not the same as the absence of risk.
Why attackers care about the same signal
Attackers watch these entries too, especially when the public description is broad enough to hint at an attack class. A shell spoofing issue tells a sophisticated adversary that there may be a user-interface deception path to explore, even if the exact primitive is not disclosed. That can inspire probing, fuzzing, or user-targeted lures.This is one reason vendors sometimes keep details sparse until patches are broadly available. The less the initial disclosure reveals, the less useful it is to opportunistic actors in the short term. Still, even a minimal label can be enough for determined researchers to start connecting dots.
- Confidence helps distinguish confirmed issues from speculation.
- Sparse details still carry operational meaning.
- Attackers infer likely exploit paths from vulnerability class alone.
- Defenders should prioritize based on certainty and trust impact.
- Patch timing often matters more than full public reverse-engineering.
Enterprise Impact
For enterprises, a shell spoofing vulnerability is dangerous because it targets the exact environment where users are trained to move fast and trust familiar interfaces. In large organizations, employees routinely approve prompts, open files, inspect folders, and react to dialog boxes without deep scrutiny. A deceptive shell presentation can exploit that pace.Endpoint and identity implications
If a spoofing flaw convinces a user to launch the wrong object or trust the wrong prompt, the result may be credential exposure, malware execution, or improper administrative action. Those outcomes can ripple into identity systems, network shares, and sensitive repositories. In a managed fleet, one misleading interface can become the first step in a broader intrusion.Security operations teams should also consider the detection problem. Spoofing events may look like ordinary user activity until later stages of compromise appear. That lag is where attackers win time.
Administrative workflow risk
Administrators are not only users; they are high-value users. A shell spoofing attack that persuades a helpdesk technician, system admin, or delegated operator to take a legitimate-looking action can have outsized consequences. In some environments, that single action can expose credentials, authorize a deployment, or open a privileged channel.The threat is especially acute where people rely on visual confirmation rather than policy enforcement. If a malicious object can imitate a trusted one, then training alone may not be enough. Organizations need layered controls that reduce dependence on human interpretation.
- Helpdesk staff can be prime targets because they act quickly and broadly.
- Admins may trust system cues more than they should.
- Managed fleets can spread one user mistake into many systems.
- Detection latency can let attackers persist longer.
- Least privilege becomes even more important when the UI can mislead.
Consumer impact
For home users, the main risk is simpler but still serious: a spoofed object can trick someone into opening the wrong file, trusting the wrong prompt, or following a malicious workflow. Consumers are less likely to have layered monitoring, and they may rely heavily on visual cues. That makes shell spoofing a useful delivery mechanism for scams and payloads.Historical Context: Windows Shell as a Repeat Target
Windows Shell issues have repeatedly drawn attention over the years because the shell is deeply intertwined with how Windows feels to use. Attackers favor components that shape user trust, not just those that execute code. That has made the shell a recurring focus for security researchers.Lessons from past UI deception
Historically, attackers have abused file icons, extensions, shortcut behaviors, and rendered metadata to blur the line between safe and unsafe content. These attacks are effective because they exploit assumptions rather than raw logic flaws. In many cases, the system technically behaves as designed, but the design itself enables deception.That historical pattern is why shell spoofing should never be dismissed as cosmetic. A convincing lookalike can be enough to set up a later compromise path. Visual fidelity is not harmless when it is weaponized.
Why this class persists
The shell is difficult to fully harden because it must remain flexible, user-friendly, and backward compatible. Windows supports decades of file types, third-party integrations, and legacy behaviors, and that creates a vast attack surface. Every new convenience feature risks becoming a new trust boundary.This is also one reason Microsoft’s vulnerability management has evolved toward richer contextual guidance. The company knows that a one-line description often underestimates how much a user-facing issue can matter in practice. CVE-2026-32202 fits into that tradition.
- Backward compatibility keeps older behaviors alive.
- User convenience often increases attack surface.
- UI trust is harder to defend than memory safety.
- Legacy integrations create edge cases that attackers love.
- Repeated targeting shows the shell remains strategically valuable.
Detection, Telemetry, and Response
One challenge with spoofing vulnerabilities is that they do not always generate the obvious crash traces or exploit artifacts defenders are used to seeing. If the issue manipulates appearance rather than memory, traditional exploit detection can be less useful. Security teams need to think more broadly about user behavior and object lineage.What defenders should look for
Investigators should pay attention to unusual file names, strange shortcut behavior, unexpected icon rendering, and suspicious execution sequences that begin with routine shell interactions. They should also correlate user-reported anomalies with endpoint telemetry, because spoofing may first surface as “this looked wrong” rather than “the device was compromised.”A useful response posture includes validation of file origin, inspection of object metadata, and careful review of recent shell-handling events. In many cases, the earliest indicator will be a user complaint that something looked normal but behaved differently. That kind of report should not be dismissed.
Operational response priorities
Enterprises should be ready to move on patching once Microsoft publishes remediation details, but they should also consider mitigations that reduce trust in shell-rendered cues. Application control, macro restrictions, attachment policies, and least-privilege enforcement all help narrow the space in which spoofing can succeed.A strong response plan should include quick communication to users. When interface deception is the threat, awareness matters. People cannot report what they have been taught to ignore.
- Inventory systems that rely heavily on interactive shell workflows.
- Patch affected Windows versions as soon as remediation is available.
- Review endpoint logs for suspicious file and shortcut activity.
- Reinforce user training on deceptive file and prompt behavior.
- Tighten application and attachment controls where possible.
- Telemetry gaps are common when the flaw is visual rather than memory-based.
- User reports may be the first sign of a problem.
- Patch speed matters, but so do complementary mitigations.
- Object provenance should be examined carefully.
- Behavioral correlation is often more useful than single-event alerts.
Competitive and Market Implications
Microsoft’s handling of a shell spoofing issue also has a market dimension. Security buyers compare vendors not only on raw patch volume but on transparency, timeliness, and the quality of mitigation guidance. A clearly framed advisory can reassure customers that the vendor is tracking the issue seriously, even if technical detail remains limited.Confidence as a trust signal
When Microsoft labels a vulnerability and explains its confidence level, it is making a trust claim to administrators. The company is saying, in effect, that the issue is real enough to matter and specific enough to track, even if the public cannot yet see the full internals. That can help enterprises prioritize more rationally.The flip side is that sparse disclosure can frustrate defenders who need more context for risk modeling. Security teams may want to know whether the vulnerability requires local access, user interaction, or special conditions. Without that detail, they must make assumptions, and assumptions create either overreaction or delay.
Broader industry lesson
Competing endpoint vendors will watch issues like this because user-interface spoofing is not unique to Windows. Any platform with rich shell semantics, file previews, link handling, and visual trust cues faces similar risks. The broader lesson is that modern security is as much about preventing deception as blocking execution.This is especially relevant as enterprises consolidate identities and workflows across cloud services, desktop environments, and web apps. The more integrated the user experience becomes, the more valuable a credible-looking spoof becomes to an attacker. That is a market problem as much as a technical one.
- Transparency affects how customers judge vendor credibility.
- Guidance quality can be as important as the patch itself.
- User-interface trust is a cross-platform security challenge.
- Consolidated workflows increase the value of deception.
- Security buyers increasingly weigh response clarity, not just CVSS scores.
Strengths and Opportunities
The good news is that Microsoft’s structured disclosure model gives defenders a real chance to prepare before a vulnerability is widely abused. Even when the technical detail is limited, a named CVE and an identified category provide a starting point for operational response. That is valuable in a world where many exploit chains become public only after they have already spread.- Clear classification helps security teams triage faster.
- Early awareness allows patch planning before exploitation escalates.
- Enterprise hardening can reduce the attack surface around shell interactions.
- User training can be refreshed with concrete examples of deception.
- Least privilege limits the blast radius of successful spoofing.
- Application controls can reduce exposure to malicious objects.
- Telemetry review can uncover suspicious file-handling patterns.
Risks and Concerns
The main concern is that shell spoofing is often underestimated because it may not look dramatic to casual observers. That creates a dangerous mismatch between technical severity and human intuition. If users and even some defenders treat the issue as merely cosmetic, response time can suffer.- Underestimation is a major risk because spoofing sounds mild.
- Human trust can be exploited more easily than software logic.
- Sparse public details make it harder to model the full attack path.
- Delayed patching increases exposure once proof-of-concept material appears.
- High-value users may be targeted selectively with tailored lures.
- Detection tooling may miss the earliest stages of misuse.
- Legacy compatibility can preserve weak behaviors longer than ideal.
What to Watch Next
The next phase will likely hinge on whether Microsoft expands the advisory with remediation details, whether researchers publish more technical analysis, and whether the issue begins to show up in real-world attack reporting. If this CVE follows the pattern of other user-interface or shell-related issues, the story may evolve quickly once defenders start testing edge cases. The real-world impact will depend on whether the flaw is easy to trigger and whether it can be chained with social engineering or another weakness.Enterprises should watch for signals that indicate the attack surface is broader than first described. That includes changes to the advisory, updated guidance from Microsoft, and any signs that security vendors are adding detections or mitigations. The most important thing is not to wait for proof of widespread abuse before taking the issue seriously. By then, the advantage is usually gone.
- Microsoft follow-up guidance and any expanded technical explanation.
- Research publications that clarify the attack mechanism.
- Patch availability across supported Windows versions.
- Detection updates from endpoint security vendors.
- Reports of in-the-wild abuse or targeted exploitation.
If Microsoft’s confidence level is any indication, CVE-2026-32202 is not a curiosity to file away for later. It is a reminder that the boundary between interface and security is still one of the most strategically important lines in Windows. Once that boundary can be bent, the attacker’s job becomes much easier, and the defender’s margin for error becomes much smaller.
Source: MSRC Security Update Guide - Microsoft Security Response Center