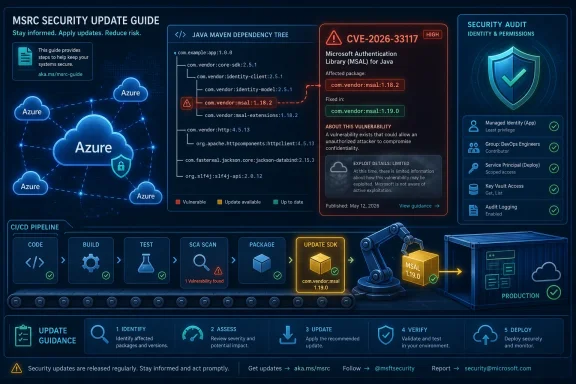
Microsoft has assigned CVE-2026-33117 to a security feature bypass vulnerability in the Azure SDK for Java, with the advisory published through the Microsoft Security Response Center’s Security Update Guide on May 12, 2026. The public record is thin, but that is itself the story: this is a cloud-development dependency issue where the important work starts before exploit details are plentiful. For WindowsForum readers, the practical question is not whether this looks like a classic Windows patch emergency. It is whether your Java applications, build pipelines, and Azure-facing services are actually consuming a fixed SDK version.
Security feature bypass bugs rarely arrive with the drama of remote code execution, but they often live in places defenders trust too much. CVE-2026-33117 is attached not to a desktop component or a kernel driver, but to the Azure SDK for Java — the library layer that thousands of applications use to talk to Azure services from production code, automation jobs, integration services, and internal platforms.
That makes the vulnerability easy to underread. A library flaw does not necessarily expose a server port or light up a Windows Update dashboard. It can sit inside a Maven dependency tree, inherited through a client library, pinned months ago by a cautious engineering team, and then forgotten because “the app still builds.”
The Azure SDK for Java is not a single monolithic “SDK” in the old Windows sense. It is a constellation of service-specific packages, common core libraries, identity components, transport abstractions, management clients, and data-plane clients. That structure is good engineering, but it complicates incident response: a security fix may be one version bump away, but knowing which version is actually deployed is the hard part.
Microsoft’s advisory title gives us the broad class: security feature bypass. It does not, at least from the public summary, hand defenders a comfortable root-cause narrative. That means administrators and developers should resist two bad instincts: panic because the word “Azure” appears, or dismissal because the word “bypass” sounds less severe than “RCE.”
That distinction matters because a CVE record is not the same thing as a full exploit write-up. Vendors often publish advisories before giving the world the exact failure mode, especially when the affected component is a widely used client library. The absence of a public proof of concept is not the same as the absence of risk.
In CVSS terms, a confirmed issue means there are detailed reports, a reproducible condition, source-level confirmation, or vendor acknowledgement. Microsoft’s publication through MSRC is a strong signal that the company accepts the vulnerability as real. What the public may not yet have is the sort of code-path detail that turns a patching task into an exploit tutorial.
That is the awkward middle ground where many enterprise teams live. The bug is credible enough to demand action, but not described enough to make environment-specific risk scoring easy. In those moments, defenders should prioritize exposure mapping over speculation.
In an SDK, that distinction becomes especially important. Developers generally do not read every line of a cloud client library; they rely on it to serialize requests correctly, validate inputs correctly, authenticate correctly, handle redirects correctly, respect endpoints correctly, and preserve security assumptions between application code and service APIs.
A bypass in that layer can undermine assumptions far above it. An application may believe it has enabled a protective mode because the code uses the right builder option. A service integration may assume a token, endpoint, or request policy is being constrained as documented. A pipeline may pass tests because the SDK still returns successful responses, even while a security guarantee has been weakened.
That is why the category should not be treated as cosmetic. “Bypass” sounds smaller than “compromise,” but in security engineering the bypass is often the opening move.
If an internal application uses Azure Blob Storage, Key Vault, Service Bus, Event Hubs, Cosmos DB, Identity, Resource Manager, or any number of Azure service clients from Java, the relevant patch may arrive through Maven rather than Windows Update. That means the operational center of gravity moves from endpoint compliance to build reproducibility.
The Azure SDK for Java commonly enters projects through Maven coordinates under the
The worst-case enterprise pattern is familiar: a team pins a working SDK version to avoid regressions, another team copies the same internal starter template, and two years later a vulnerability report reveals that dozens of services inherited the same stale dependency. That is not negligence so much as entropy. But attackers do not care whether entropy or recklessness created the opening.
Large Java estates often contain a mix of Maven, Gradle, shaded JARs, internal mirrors, private artifact repositories, container images, and old CI pipelines. Some projects import the BOM and then override individual versions. Some depend on frameworks that pull Azure packages transitively. Some package dependencies into fat JARs where runtime inspection becomes harder than source inspection.
That is why the first response to CVE-2026-33117 should be inventory, not heroics. Security teams need to know which applications include Azure SDK for Java packages, which versions are built into deployable artifacts, and which running services actually use those artifacts. A dependency listed in source control is not always the dependency running in production.
For Windows-heavy shops, this may require crossing organizational seams. The team that manages Azure subscriptions may not own the Java code. The team that owns the code may not own the runtime platform. The team that owns the runtime platform may not have access to the software composition analysis results. CVE-2026-33117 is exactly the kind of advisory that exposes whether those seams are documented or merely assumed.
An SDK vulnerability has a different lifecycle. The vendor publishes a fixed package. Developers update dependency manifests. CI builds new artifacts. Test suites run. Containers or app packages are rebuilt. Deployment rings roll forward. Old images are retired. Long-lived services are restarted. Only then is the vulnerability meaningfully remediated in production.
That chain has more failure points than a conventional cumulative update. A source repository can be patched while a production container still runs the old image. A base image can be rebuilt while an application artifact still embeds the stale library. A dependency scanner can flag the issue while the engineering backlog treats it as “medium priority” because the app is not internet-facing.
This is where sysadmins and developers need a shared vocabulary. The administrator asks, “Is the system patched?” The developer answers, “The dependency is updated in main.” Those are not the same statement. The security team needs the third sentence: “The fixed artifact is deployed everywhere the vulnerable artifact was running.”
The client side still matters. SDKs shape requests before they leave the application. They handle credentials, retries, redirects, serialization, deserialization, logging, tracing, encryption helpers, and policy pipelines. When those behaviors contain a security flaw, the customer’s application may remain exposed even if the Azure service itself is healthy.
This is especially relevant for hybrid Windows estates. Many organizations run Java services on Windows Server, deploy build agents on Windows, authenticate with Microsoft Entra ID, and integrate with Azure services from both cloud-hosted and on-premises workloads. The vulnerable component may be a Java library, but the operational footprint is often thoroughly Microsoft-shaped.
The security boundary is not “cloud versus local.” It is the trust relationship between application code, SDK behavior, credentials, and Azure APIs. A bypass in that chain deserves attention precisely because it is easy to miss in asset inventories built around machines rather than software components.
That means a high-confidence report should raise the floor of urgency, not end the conversation. Once Microsoft acknowledges a vulnerability in a widely used SDK, defenders should assume that enough technical truth exists to justify remediation. The remaining question is how quickly the fix can move through engineering and operations without breaking production systems.
This is also where CVSS can be both helpful and misleading. CVSS gives the industry a common language for technical severity, but it cannot know whether your affected Java service handles billing events, identity automation, customer data, backup orchestration, or a weekend prototype. Environmental context still belongs to the organization.
A security feature bypass in a dormant internal tool is one kind of risk. The same class of bug in a privileged automation service that manages Azure resources is another. Teams that treat those cases identically are not being rigorous; they are outsourcing judgment to a score.
This is why dependency response should be paired with credential and permission review. If an affected Java application uses service principals, managed identities, workload identity federation, or certificate-based authentication, teams should verify that permissions are still least-privilege and that credentials are not overbroad relics from initial deployment.
The broader lesson is not unique to this CVE. Cloud client libraries concentrate trust. They are installed by developers, invoked by applications, authorized by identity platforms, and monitored by security teams that may not know the code path exists. When a flaw appears in that layer, patching is necessary but not sufficient.
A mature response asks whether the vulnerable component had access to anything it did not truly need. If the answer is yes, CVE-2026-33117 becomes more than a patch ticket. It becomes an audit prompt.
Java packages from Maven Central, Node packages from npm, Python wheels, container base images, GitHub Actions, Terraform providers, and Azure SDKs all sit adjacent to the Windows estate. They may be developed by Microsoft, hosted by Microsoft, or used to control Microsoft cloud resources, but they are not serviced like Windows.
That mismatch creates a governance gap. An organization can be beautifully compliant on Windows cumulative updates and still run vulnerable Azure SDK packages in production. Conversely, a development team can patch dependencies quickly but leave operations unaware that an important security exposure was closed.
The answer is not to force every dependency into a Windows-style patch calendar. The answer is to make software composition visible to the same risk process that already tracks endpoints and servers. If the CMDB knows about the VM but not the application dependencies inside it, it is only telling half the story.
The sensible move is to patch before the advisory ecosystem fills in the blanks. Once a vendor publishes an update, researchers and adversaries often compare versions, inspect commits, and infer the vulnerable code path. In open-source or source-available ecosystems, the fix can become the map.
That is not an argument for secrecy as a permanent policy. Transparency matters, especially for customers trying to assess risk. But in the early window after publication, defenders should assume that technical detail will only increase, not decrease.
The speed advantage belongs to teams that already know where their dependencies are. If the first day of a CVE response is spent arguing about who owns the inventory, the organization has already lost the easiest part of the race.
That does not justify delay-by-default. It means teams should have a safe fast path for dependency security releases. Automated dependency PRs, software composition analysis, integration tests against Azure resources, staged rollouts, and rollback plans are not luxuries. They are the machinery that lets an organization patch quickly without guessing.
The Azure SDK BOM can reduce version drift, but the team still needs to read release notes for the specific packages in use. A storage-heavy service, an identity-heavy service, and a resource-management automation tool may all use Azure SDK for Java, but they may exercise very different parts of the library stack.
Good engineering response is boring and disciplined. Identify affected packages, move to the fixed versions, rebuild artifacts, test meaningful Azure operations, deploy in rings, and confirm runtime state. The boring path is the one that survives contact with production.
The strongest proof includes dependency manifests, lockfiles where applicable, software bill of materials output, CI build records, artifact hashes, container image digests, deployment timestamps, and runtime verification. For Java services, teams should be able to show not only that source control references a fixed version, but that the deployed JAR or image no longer contains the vulnerable package.
This is where SBOM work becomes practical rather than bureaucratic. An SBOM that is generated once and filed away is paperwork. An SBOM that can answer “where are we using this package today?” is operational security.
The same applies to vulnerability scanners. A scanner finding is useful only if the organization can route it to the team that can rebuild and redeploy the affected artifact. Otherwise, CVE-2026-33117 becomes another noisy ticket in a queue full of technically true but operationally orphaned findings.
This is the paradox of mature platforms. The more developers rely on a shared library to do the right thing, the more valuable that library becomes as a place to find subtle flaws. A mistake in bespoke application code hurts one application. A mistake in a widely used SDK can ripple through entire classes of services.
That does not mean organizations should avoid SDKs and hand-roll REST calls. Quite the opposite. Vendor SDKs are usually safer, better maintained, and more consistent than ad hoc integrations. But they must be treated as active dependencies, not plumbing poured into the foundation and forgotten.
The old enterprise habit of “if it works, don’t touch it” is increasingly incompatible with cloud software. In 2026, a dependency that keeps working may still be a dependency that needs to move.
For Windows professionals, this is another sign that Microsoft security response no longer fits neatly into the Windows Update frame. Azure, developer tooling, identity, SDKs, and open-source package ecosystems now sit inside the same risk envelope as servers and endpoints. The forum crowd that once tracked KB numbers now also needs to care about Maven coordinates.
The forward-looking answer is not panic-driven dependency churn. It is an operating model where software inventory, build automation, Azure identity governance, and patch management are treated as one system. CVE-2026-33117 will eventually fade into the archive, but the organizations that handle it well will be the ones that can prove, quickly and calmly, where their cloud-facing code comes from, what it depends on, and how fast they can replace it when trust in that dependency changes.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s Quiet Advisory Lands in the Loudest Part of the Stack
Microsoft’s Quiet Advisory Lands in the Loudest Part of the Stack
Security feature bypass bugs rarely arrive with the drama of remote code execution, but they often live in places defenders trust too much. CVE-2026-33117 is attached not to a desktop component or a kernel driver, but to the Azure SDK for Java — the library layer that thousands of applications use to talk to Azure services from production code, automation jobs, integration services, and internal platforms.That makes the vulnerability easy to underread. A library flaw does not necessarily expose a server port or light up a Windows Update dashboard. It can sit inside a Maven dependency tree, inherited through a client library, pinned months ago by a cautious engineering team, and then forgotten because “the app still builds.”
The Azure SDK for Java is not a single monolithic “SDK” in the old Windows sense. It is a constellation of service-specific packages, common core libraries, identity components, transport abstractions, management clients, and data-plane clients. That structure is good engineering, but it complicates incident response: a security fix may be one version bump away, but knowing which version is actually deployed is the hard part.
Microsoft’s advisory title gives us the broad class: security feature bypass. It does not, at least from the public summary, hand defenders a comfortable root-cause narrative. That means administrators and developers should resist two bad instincts: panic because the word “Azure” appears, or dismissal because the word “bypass” sounds less severe than “RCE.”
The Vulnerability Is Confirmed, but the Details Are Deliberately Scarce
The user-provided MSRC text focuses on the CVSS Report Confidence metric, and that is a useful lens here. Report Confidence measures how much trust evaluators have in the existence of the vulnerability and the credibility of the technical details. In plain English: do we know this is real, do we know why it happens, and do attackers know enough to reproduce it?That distinction matters because a CVE record is not the same thing as a full exploit write-up. Vendors often publish advisories before giving the world the exact failure mode, especially when the affected component is a widely used client library. The absence of a public proof of concept is not the same as the absence of risk.
In CVSS terms, a confirmed issue means there are detailed reports, a reproducible condition, source-level confirmation, or vendor acknowledgement. Microsoft’s publication through MSRC is a strong signal that the company accepts the vulnerability as real. What the public may not yet have is the sort of code-path detail that turns a patching task into an exploit tutorial.
That is the awkward middle ground where many enterprise teams live. The bug is credible enough to demand action, but not described enough to make environment-specific risk scoring easy. In those moments, defenders should prioritize exposure mapping over speculation.
“Security Feature Bypass” Is Not a Soft Category
A security feature bypass vulnerability is often misunderstood because it describes what fails rather than what the attacker ultimately achieves. The feature being bypassed might be a validation step, a boundary check, an authentication-related guardrail, a cryptographic protection, or a policy enforcement mechanism. The impact depends on where that protection sits in the call chain.In an SDK, that distinction becomes especially important. Developers generally do not read every line of a cloud client library; they rely on it to serialize requests correctly, validate inputs correctly, authenticate correctly, handle redirects correctly, respect endpoints correctly, and preserve security assumptions between application code and service APIs.
A bypass in that layer can undermine assumptions far above it. An application may believe it has enabled a protective mode because the code uses the right builder option. A service integration may assume a token, endpoint, or request policy is being constrained as documented. A pipeline may pass tests because the SDK still returns successful responses, even while a security guarantee has been weakened.
That is why the category should not be treated as cosmetic. “Bypass” sounds smaller than “compromise,” but in security engineering the bypass is often the opening move.
Java Dependency Hygiene Is Now Azure Security Hygiene
For Windows administrators who spend their days in Intune, Defender, WSUS, Autopatch, Group Policy, or PowerShell, Java dependency management can feel like someone else’s problem. CVE-2026-33117 is a reminder that Azure estates increasingly depend on software supply-chain discipline that sits outside the traditional Windows patch loop.If an internal application uses Azure Blob Storage, Key Vault, Service Bus, Event Hubs, Cosmos DB, Identity, Resource Manager, or any number of Azure service clients from Java, the relevant patch may arrive through Maven rather than Windows Update. That means the operational center of gravity moves from endpoint compliance to build reproducibility.
The Azure SDK for Java commonly enters projects through Maven coordinates under the
com.azure group, with versions controlled either directly in application dependency files or indirectly through the Azure SDK BOM. The BOM approach is useful because it aligns generally available Azure SDK package versions, but it does not absolve teams from checking whether their projects are actually using it, overriding it, or depending on libraries outside it.The worst-case enterprise pattern is familiar: a team pins a working SDK version to avoid regressions, another team copies the same internal starter template, and two years later a vulnerability report reveals that dozens of services inherited the same stale dependency. That is not negligence so much as entropy. But attackers do not care whether entropy or recklessness created the opening.
The BOM Helps Only If the Build System Is Telling the Truth
Microsoft’s Java guidance encourages use of the Azure SDK Bill of Materials to keep compatible client package versions aligned. In theory, that gives developers a clean way to update a fleet of Azure client libraries without manually curating every transitive dependency. In practice, BOMs are only as trustworthy as the build graph around them.Large Java estates often contain a mix of Maven, Gradle, shaded JARs, internal mirrors, private artifact repositories, container images, and old CI pipelines. Some projects import the BOM and then override individual versions. Some depend on frameworks that pull Azure packages transitively. Some package dependencies into fat JARs where runtime inspection becomes harder than source inspection.
That is why the first response to CVE-2026-33117 should be inventory, not heroics. Security teams need to know which applications include Azure SDK for Java packages, which versions are built into deployable artifacts, and which running services actually use those artifacts. A dependency listed in source control is not always the dependency running in production.
For Windows-heavy shops, this may require crossing organizational seams. The team that manages Azure subscriptions may not own the Java code. The team that owns the code may not own the runtime platform. The team that owns the runtime platform may not have access to the software composition analysis results. CVE-2026-33117 is exactly the kind of advisory that exposes whether those seams are documented or merely assumed.
Patch Tuesday Thinking Does Not Map Cleanly to SDK Vulnerabilities
Microsoft advisories often trigger a familiar mental model: identify affected Windows versions, approve KBs, monitor deployment, deal with reboots, and watch for known issues. That model is useful for operating systems and Microsoft applications. It is less useful for developer libraries.An SDK vulnerability has a different lifecycle. The vendor publishes a fixed package. Developers update dependency manifests. CI builds new artifacts. Test suites run. Containers or app packages are rebuilt. Deployment rings roll forward. Old images are retired. Long-lived services are restarted. Only then is the vulnerability meaningfully remediated in production.
That chain has more failure points than a conventional cumulative update. A source repository can be patched while a production container still runs the old image. A base image can be rebuilt while an application artifact still embeds the stale library. A dependency scanner can flag the issue while the engineering backlog treats it as “medium priority” because the app is not internet-facing.
This is where sysadmins and developers need a shared vocabulary. The administrator asks, “Is the system patched?” The developer answers, “The dependency is updated in main.” Those are not the same statement. The security team needs the third sentence: “The fixed artifact is deployed everywhere the vulnerable artifact was running.”
The Cloud Does Not Remove the Client-Side Attack Surface
It is tempting to assume that because Azure services are operated by Microsoft, SDK vulnerabilities are somehow absorbed by the cloud. That is only partly true. Microsoft can patch service-side components, rotate infrastructure, and change backend behavior. It cannot automatically rebuild every customer application that compiled an affected Java library into its deployment artifact.The client side still matters. SDKs shape requests before they leave the application. They handle credentials, retries, redirects, serialization, deserialization, logging, tracing, encryption helpers, and policy pipelines. When those behaviors contain a security flaw, the customer’s application may remain exposed even if the Azure service itself is healthy.
This is especially relevant for hybrid Windows estates. Many organizations run Java services on Windows Server, deploy build agents on Windows, authenticate with Microsoft Entra ID, and integrate with Azure services from both cloud-hosted and on-premises workloads. The vulnerable component may be a Java library, but the operational footprint is often thoroughly Microsoft-shaped.
The security boundary is not “cloud versus local.” It is the trust relationship between application code, SDK behavior, credentials, and Azure APIs. A bypass in that chain deserves attention precisely because it is easy to miss in asset inventories built around machines rather than software components.
Report Confidence Is a Signal, Not a Substitute for Triage
The quoted CVSS language gives defenders a useful way to think about uncertainty. Report Confidence asks how credible the vulnerability report is. It does not tell you how important the affected application is, whether your configuration is exposed, whether exploit code is circulating privately, or whether a compensating control exists in your environment.That means a high-confidence report should raise the floor of urgency, not end the conversation. Once Microsoft acknowledges a vulnerability in a widely used SDK, defenders should assume that enough technical truth exists to justify remediation. The remaining question is how quickly the fix can move through engineering and operations without breaking production systems.
This is also where CVSS can be both helpful and misleading. CVSS gives the industry a common language for technical severity, but it cannot know whether your affected Java service handles billing events, identity automation, customer data, backup orchestration, or a weekend prototype. Environmental context still belongs to the organization.
A security feature bypass in a dormant internal tool is one kind of risk. The same class of bug in a privileged automation service that manages Azure resources is another. Teams that treat those cases identically are not being rigorous; they are outsourcing judgment to a score.
The Enterprise Blast Radius Depends on Identity and Privilege
For Azure SDK issues, the blast radius often follows identity. A vulnerable application using a low-privilege managed identity against a narrow storage container presents a different risk profile than a deployment orchestrator using broad rights across subscriptions. The SDK is the path; the identity is often the prize.This is why dependency response should be paired with credential and permission review. If an affected Java application uses service principals, managed identities, workload identity federation, or certificate-based authentication, teams should verify that permissions are still least-privilege and that credentials are not overbroad relics from initial deployment.
The broader lesson is not unique to this CVE. Cloud client libraries concentrate trust. They are installed by developers, invoked by applications, authorized by identity platforms, and monitored by security teams that may not know the code path exists. When a flaw appears in that layer, patching is necessary but not sufficient.
A mature response asks whether the vulnerable component had access to anything it did not truly need. If the answer is yes, CVE-2026-33117 becomes more than a patch ticket. It becomes an audit prompt.
Windows Shops Need Better Visibility Into Non-Windows Patches
WindowsForum readers know the ritual of monthly Microsoft updates. The industry has built dashboards, compliance reports, servicing channels, and emergency processes around them. But modern Microsoft environments now include dependencies that do not flow through that machinery.Java packages from Maven Central, Node packages from npm, Python wheels, container base images, GitHub Actions, Terraform providers, and Azure SDKs all sit adjacent to the Windows estate. They may be developed by Microsoft, hosted by Microsoft, or used to control Microsoft cloud resources, but they are not serviced like Windows.
That mismatch creates a governance gap. An organization can be beautifully compliant on Windows cumulative updates and still run vulnerable Azure SDK packages in production. Conversely, a development team can patch dependencies quickly but leave operations unaware that an important security exposure was closed.
The answer is not to force every dependency into a Windows-style patch calendar. The answer is to make software composition visible to the same risk process that already tracks endpoints and servers. If the CMDB knows about the VM but not the application dependencies inside it, it is only telling half the story.
The Absence of Public Exploit Code Is Not a Comfort Blanket
At the time of writing, public information around CVE-2026-33117 appears limited compared with heavily analyzed zero-days. That should reduce panic, not urgency. Limited details can mean attackers have less to work with, but it can also mean defenders have less ability to construct precise compensating controls.The sensible move is to patch before the advisory ecosystem fills in the blanks. Once a vendor publishes an update, researchers and adversaries often compare versions, inspect commits, and infer the vulnerable code path. In open-source or source-available ecosystems, the fix can become the map.
That is not an argument for secrecy as a permanent policy. Transparency matters, especially for customers trying to assess risk. But in the early window after publication, defenders should assume that technical detail will only increase, not decrease.
The speed advantage belongs to teams that already know where their dependencies are. If the first day of a CVE response is spent arguing about who owns the inventory, the organization has already lost the easiest part of the race.
Developers Should Treat the Fix as a Release, Not a Line Edit
Updating an SDK version looks simple in a pull request. In production systems, it is a release. Azure SDK packages can bring dependency updates, behavior changes, serialization tweaks, retry-policy changes, transport differences, and deprecation effects. Even security-driven updates need testing.That does not justify delay-by-default. It means teams should have a safe fast path for dependency security releases. Automated dependency PRs, software composition analysis, integration tests against Azure resources, staged rollouts, and rollback plans are not luxuries. They are the machinery that lets an organization patch quickly without guessing.
The Azure SDK BOM can reduce version drift, but the team still needs to read release notes for the specific packages in use. A storage-heavy service, an identity-heavy service, and a resource-management automation tool may all use Azure SDK for Java, but they may exercise very different parts of the library stack.
Good engineering response is boring and disciplined. Identify affected packages, move to the fixed versions, rebuild artifacts, test meaningful Azure operations, deploy in rings, and confirm runtime state. The boring path is the one that survives contact with production.
Security Teams Should Ask for Evidence, Not Assurances
When a vulnerability like CVE-2026-33117 appears, “we updated the dependency” is a start, not an endpoint. Security teams should ask for evidence that connects the advisory to running systems. That evidence does not need to be theatrical, but it should be concrete.The strongest proof includes dependency manifests, lockfiles where applicable, software bill of materials output, CI build records, artifact hashes, container image digests, deployment timestamps, and runtime verification. For Java services, teams should be able to show not only that source control references a fixed version, but that the deployed JAR or image no longer contains the vulnerable package.
This is where SBOM work becomes practical rather than bureaucratic. An SBOM that is generated once and filed away is paperwork. An SBOM that can answer “where are we using this package today?” is operational security.
The same applies to vulnerability scanners. A scanner finding is useful only if the organization can route it to the team that can rebuild and redeploy the affected artifact. Otherwise, CVE-2026-33117 becomes another noisy ticket in a queue full of technically true but operationally orphaned findings.
The Azure SDK’s Strength Is Also Its Weakness
The Azure SDK for Java exists to make cloud development predictable. It gives developers consistent builders, authentication patterns, retry handling, transport abstractions, and service-specific clients. That consistency is exactly why a security issue in the SDK matters: common abstractions create common exposure.This is the paradox of mature platforms. The more developers rely on a shared library to do the right thing, the more valuable that library becomes as a place to find subtle flaws. A mistake in bespoke application code hurts one application. A mistake in a widely used SDK can ripple through entire classes of services.
That does not mean organizations should avoid SDKs and hand-roll REST calls. Quite the opposite. Vendor SDKs are usually safer, better maintained, and more consistent than ad hoc integrations. But they must be treated as active dependencies, not plumbing poured into the foundation and forgotten.
The old enterprise habit of “if it works, don’t touch it” is increasingly incompatible with cloud software. In 2026, a dependency that keeps working may still be a dependency that needs to move.
What CVE-2026-33117 Should Trigger Inside the Windows-Azure Shop
The practical response to this advisory is not glamorous, but it is clear. Teams should use the CVE as a forcing function to check whether they can answer basic questions about Java applications that connect to Azure.- Organizations should identify every Java application, service, job, and internal tool that uses Azure SDK packages, including transitive dependencies brought in through frameworks or shared libraries.
- Development teams should update affected Azure SDK for Java packages to Microsoft’s fixed versions, preferably through the Azure SDK BOM where that fits the project’s dependency model.
- Build and platform teams should rebuild deployable artifacts, container images, and packaged services rather than assuming a source-level dependency change has reached production.
- Security teams should verify runtime exposure with SBOMs, dependency scans, artifact inspection, or equivalent evidence that the vulnerable package is no longer present.
- Azure administrators should review the identities used by affected applications and reduce excessive permissions that would magnify the impact of any SDK-layer bypass.
- Incident-response teams should document who owns future SDK advisories, because the next one will not wait for an org chart debate.
The Real Patch Is the Process Around the Package
CVE-2026-33117 is a modestly described advisory with a large operational lesson. Microsoft can publish the CVE, fix the package, and update the guidance, but customers still have to close the loop inside their own build systems and deployments. That is the part of cloud security that still looks stubbornly like old-fashioned IT work.For Windows professionals, this is another sign that Microsoft security response no longer fits neatly into the Windows Update frame. Azure, developer tooling, identity, SDKs, and open-source package ecosystems now sit inside the same risk envelope as servers and endpoints. The forum crowd that once tracked KB numbers now also needs to care about Maven coordinates.
The forward-looking answer is not panic-driven dependency churn. It is an operating model where software inventory, build automation, Azure identity governance, and patch management are treated as one system. CVE-2026-33117 will eventually fade into the archive, but the organizations that handle it well will be the ones that can prove, quickly and calmly, where their cloud-facing code comes from, what it depends on, and how fast they can replace it when trust in that dependency changes.
Source: MSRC Security Update Guide - Microsoft Security Response Center