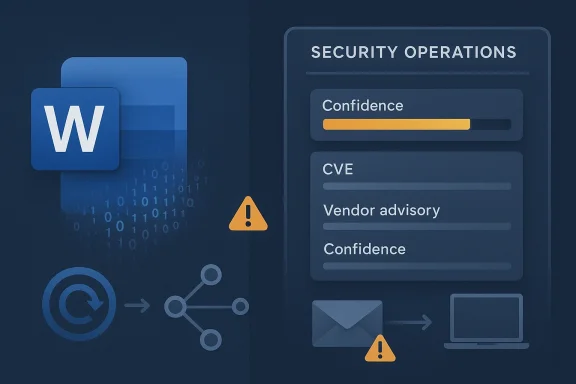
Microsoft’s CVE-2026-33822 entry for Microsoft Word Information Disclosure Vulnerability is a good example of why vendor metadata matters as much as the CVE label itself. The public record may be sparse on exploit mechanics, but Microsoft’s own framing tells defenders that the issue is real enough to track, real enough to patch, and serious enough to warrant attention even before a full technical write-up exists. In practice, that means security teams should treat the advisory as actionable intelligence, not as a theoretical notice. The broader lesson is that modern vulnerability triage increasingly depends on confidence signals, not just raw severity scores.
Microsoft’s handling of Word-related information disclosure issues has long followed a familiar pattern: concise public descriptions, limited exploit detail, and a fix that changes how Word handles memory or file parsing. The classic precedent is CVE-2020-1502, where Microsoft Word was described as improperly disclosing memory contents and the remediation changed how certain Word functions handled objects in memory . That older case is useful because it shows the kind of disclosure Microsoft tends to make when it wants to alert defenders without handing attackers a playbook.
The significance of CVE-2026-33822 is therefore not just that Word has another information disclosure issue. It is that Microsoft’s current vulnerability-tracking model now places greater emphasis on confidence — how certain the vendor is that the flaw exists and how credible the known technical details are. That distinction matters because many enterprise defenders use Microsoft’s update guidance as the first stop for triage, prioritization, and remediation planning.
Information disclosure vulnerabilities rarely make headlines the way remote code execution bugs do, but they can still be operationally important. A disclosure flaw can expose memory, pointers, internal structures, tokens, or document-derived data that later helps an attacker chain into something more destructive. In Word’s case, the underlying concern is especially sensitive because Office documents are among the most common attack vectors in enterprise environments.
This also fits into a broader trend across Microsoft’s ecosystem. Office, Windows, and adjacent productivity components increasingly serve as both user productivity tools and security boundaries. When a bug lives inside a widely deployed editor like Word, even a narrow information leak can have outsized consequences because the application sits at the intersection of email, collaboration, cloud sync, and document conversion workflows.
A final historical point matters: Microsoft’s security guidance has steadily become more structured and more machine-readable. The company’s push toward CSAF and richer update-guide metadata reflects a recognition that defenders need faster, more automated ways to sort real risk from noise. CVE-2026-33822 should be read in that context. It is not only a vulnerability record; it is part of a more mature disclosure ecosystem.
For defenders, that means the important question is not whether the bug directly executes code. It is whether the leak can be used to support follow-on exploitation. In a modern endpoint environment, that answer is often yes, especially when the vulnerable app is a document processor with broad file-format support and deep integration into the operating system.
The broader implication is that memory disclosure in Office products is never trivial. Word processes complex inputs, embedded objects, external references, and legacy document formats, all of which create opportunities for parser edge cases. Even when Microsoft publishes few technical details, the component name alone can tell seasoned defenders a lot about likely attack surface.
This matters because the public technical details around many Microsoft advisories are intentionally restrained. The company does not want to publish exploit-enabling minutiae, but it still needs to tell customers enough to act. The confidence signal bridges that gap by giving defenders a sense of certainty without exposing too much mechanism.
That balance has become more visible as Microsoft modernizes its disclosure process. The company’s adoption of machine-readable CSAF and structured update-guide data shows a clear intent to make vulnerability response more machine-assisted and less ad hoc. In that environment, confidence becomes a sort of metadata shorthand for urgency.
A useful way to think about the signal is this:
The application also sits close to the human decision layer. Email attachments, shared files, legal documents, and business reports are all familiar Word entry points. Attackers exploit that familiarity by embedding malicious content in workflows users already trust.
Enterprises also face the multiplication effect. One vulnerable Word installation may not be a crisis; thousands of endpoints with different patch cadences, preview panes, and document automation tools absolutely can be. The same vulnerability can be mild in a single-user context and significant in a managed fleet.
That is why Word advisories often deserve fleet-wide attention, not just per-device caution. In operational terms, the risk is not the CVE in isolation. It is the interaction between the CVE and the organization’s document-handling habits.
What changed over time is not the basic pattern, but the surrounding ecosystem. Today, Word files are more likely to move through cloud storage, synced workspaces, collaboration platforms, and email security gateways. That increases the chances that a vulnerable file is inspected or processed by multiple systems before it reaches the user.
The implication is subtle but important: even a “simple” Word leak can have systemic reach if it exists inside a modern enterprise document lifecycle. The file may be opened once by a user, previewed by a service, scanned by a DLP tool, and rendered in a browser-based interface. Every step is an exposure opportunity.
It also means trust the shape of the bug. Microsoft rarely invents a Word disclosure advisory for no reason. If the company is willing to publish the CVE, then there is usually enough certainty to justify operational action even when the exploit details are sparse.
These bugs are often subtle because they can survive ordinary testing. They may only appear with a specially crafted document, a particular field combination, or a malformed embedded element. That is why controlled malicious input is so often the trigger.
The important point is not to guess the exact bug, but to understand the defensive implication: the flaw probably sits in a parsing or rendering path that is difficult to reason about from the outside. That makes vendor patching and hardening especially valuable because attackers can exploit edge cases that normal users never see.
For defenders, the sparse detail should not be read as uncertainty alone. It often means the vendor is balancing helpfulness against operational safety. The right response is to patch first and wait for subsequent research later.
That is why context matters more than the raw label. A medium-severity disclosure in a niche utility is not the same as a medium-severity disclosure in Word. Word sits in workflows that matter to business continuity, compliance, and privacy.
The best interpretation is therefore conditional. If the bug is exploitable only with user interaction, and if the leak is limited, then the direct impact may be bounded. But if the leak can aid a chain into code execution or credential theft, the effective risk rises quickly.
This is where Microsoft’s update-guide structure helps. The vendor’s move toward standardized vulnerability metadata and machine-readable advisories is meant to accelerate customer remediation workflows. That is not just a convenience feature; it is an operational necessity in large environments.
A second issue is validation. Office patches can affect add-ins, macros, document templates, and downstream automation. So the security team may need to balance urgency against regression risk. Still, patch delay should be the exception, not the default.
The governance angle is equally important. If a company has strict controls for executable code but relaxed policies for documents, it may be underestimating Word as an attack channel. Malicious documents remain one of the most efficient routes into enterprise environments because they travel through legitimate business processes.
The practical response is simple but effective. Keep Office updated, treat unsolicited documents skeptically, and avoid enabling unnecessary preview or auto-open behaviors. In security terms, boring discipline is often the best defense.
A special concern for smaller organizations is shared-device usage. If multiple users rely on the same machine or if local admin rights are too broad, the impact of a successful document-based attack can increase. That makes baseline hardening as important as patching.
That is why awareness training still matters. Not because users will spot every malicious file, but because cautious behavior reduces the chance that the first stage of the attack succeeds.
That has competitive implications. Vendors that can show stronger sandboxing, tighter document isolation, or safer rendering architectures may use that to differentiate themselves. Likewise, security buyers may weigh the maturity of update channels as heavily as feature sets.
The broader market effect is subtle but real. Each new Office disclosure hardens the case for zero-trust document handling, cloud-based sandboxing, and layered content inspection. It also raises expectations that office software should be designed to fail safely when fed malformed inputs.
That stance supports the company’s position in enterprise markets where security posture is a purchasing factor. But it also sets a standard that competitors must match: not just patching, but communicating risk in a way defenders can actually use.
The key question is not whether the vulnerability exists — Microsoft’s advisory structure already answers that — but how much attacker value the leaked information provides. If researchers show that the disclosure can be chained into memory corruption bypasses, token exposure, or reliable exploitation, then the practical risk rises materially. If the issue remains a narrow leak with limited exploit utility, the impact stays important but bounded.
Security teams should be prepared to move quickly while preserving operational stability. That means patch validation, endpoint inventory, and document flow review should happen together, not in isolation. In the real world, security and uptime have to be managed in the same room.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Microsoft’s handling of Word-related information disclosure issues has long followed a familiar pattern: concise public descriptions, limited exploit detail, and a fix that changes how Word handles memory or file parsing. The classic precedent is CVE-2020-1502, where Microsoft Word was described as improperly disclosing memory contents and the remediation changed how certain Word functions handled objects in memory . That older case is useful because it shows the kind of disclosure Microsoft tends to make when it wants to alert defenders without handing attackers a playbook.The significance of CVE-2026-33822 is therefore not just that Word has another information disclosure issue. It is that Microsoft’s current vulnerability-tracking model now places greater emphasis on confidence — how certain the vendor is that the flaw exists and how credible the known technical details are. That distinction matters because many enterprise defenders use Microsoft’s update guidance as the first stop for triage, prioritization, and remediation planning.
Information disclosure vulnerabilities rarely make headlines the way remote code execution bugs do, but they can still be operationally important. A disclosure flaw can expose memory, pointers, internal structures, tokens, or document-derived data that later helps an attacker chain into something more destructive. In Word’s case, the underlying concern is especially sensitive because Office documents are among the most common attack vectors in enterprise environments.
This also fits into a broader trend across Microsoft’s ecosystem. Office, Windows, and adjacent productivity components increasingly serve as both user productivity tools and security boundaries. When a bug lives inside a widely deployed editor like Word, even a narrow information leak can have outsized consequences because the application sits at the intersection of email, collaboration, cloud sync, and document conversion workflows.
A final historical point matters: Microsoft’s security guidance has steadily become more structured and more machine-readable. The company’s push toward CSAF and richer update-guide metadata reflects a recognition that defenders need faster, more automated ways to sort real risk from noise. CVE-2026-33822 should be read in that context. It is not only a vulnerability record; it is part of a more mature disclosure ecosystem.
What the Vulnerability Class Usually Means
An information disclosure issue in Microsoft Word generally means the application reveals data it should not expose, often due to memory handling mistakes, parser behavior, or assumptions about document structure. The older CVE-2020-1502 description is instructive: Word was said to improperly disclose the contents of memory, and the remediation altered how certain functions managed objects in memory . That is a classic sign of a bug that may leak bytes, pointers, or other internal data.Why disclosure bugs matter
Disclosure bugs often get dismissed as “only” confidentiality problems, but that is too narrow. In real attack chains, information leaks can eliminate randomness, reveal addresses, or expose hidden state that makes a separate exploit much easier to land. A vulnerability that leaks memory may not be the final step in a compromise, but it can be the step that makes the next exploit reliable.For defenders, that means the important question is not whether the bug directly executes code. It is whether the leak can be used to support follow-on exploitation. In a modern endpoint environment, that answer is often yes, especially when the vulnerable app is a document processor with broad file-format support and deep integration into the operating system.
The broader implication is that memory disclosure in Office products is never trivial. Word processes complex inputs, embedded objects, external references, and legacy document formats, all of which create opportunities for parser edge cases. Even when Microsoft publishes few technical details, the component name alone can tell seasoned defenders a lot about likely attack surface.
The likely attack shape
Most Word disclosure bugs rely on user interaction. That may mean opening a malicious document, previewing a file in a managed environment, or processing content through an automated document pipeline. The pattern is usually social engineering plus a crafted file, not a drive-by exploit.- A malicious document is typically the initial lure.
- The victim usually has to open or process the file.
- The leak may expose memory or internal document state.
- The information can then support a second-stage exploit.
Microsoft’s Confidence Metric and Why It Matters
The user-facing description you provided points to Microsoft’s confidence metric, and that is the most important clue in the advisory model. Microsoft says the metric measures how certain the company is that the vulnerability exists and how credible the known technical details are. That makes it a triage signal, not just a documentation note.Confidence is operational intelligence
A high-confidence entry tells defenders that Microsoft believes the bug is real and sufficiently understood to justify remediation. A lower-confidence entry may reflect limited public evidence, incomplete exploit understanding, or a still-evolving research picture. Either way, the score or confidence wording shapes how fast security teams move.This matters because the public technical details around many Microsoft advisories are intentionally restrained. The company does not want to publish exploit-enabling minutiae, but it still needs to tell customers enough to act. The confidence signal bridges that gap by giving defenders a sense of certainty without exposing too much mechanism.
That balance has become more visible as Microsoft modernizes its disclosure process. The company’s adoption of machine-readable CSAF and structured update-guide data shows a clear intent to make vulnerability response more machine-assisted and less ad hoc. In that environment, confidence becomes a sort of metadata shorthand for urgency.
How defenders should interpret it
The right reading is pragmatic. If Microsoft has assigned a clear CVE and attached a confidence indicator, the issue should be treated as genuine unless there is strong evidence to the contrary. In other words, don’t wait for a researcher blog post before you patch.A useful way to think about the signal is this:
- The CVE confirms vendor acknowledgment.
- The impact label tells you the security class.
- The confidence metric tells you how much faith to place in the public technical picture.
- The patch status tells you what action is available now.
Word’s Place in the Attack Surface
Microsoft Word remains one of the most heavily targeted desktop applications in the world. It is present on endpoints, in virtual desktops, in remote work environments, and inside countless workflow automations. That ubiquity makes it attractive not just to malware authors, but also to state-aligned operators and financially motivated attackers.Why Word is a frequent target
Word handles rich, complex document content and has to remain compatible with decades of file-format history. That means it must safely parse both modern and legacy inputs, often under conditions where users expect rendering and editing to be instantaneous. Every parser, object handler, preview path, and embedded-content path is another opportunity for a defect.The application also sits close to the human decision layer. Email attachments, shared files, legal documents, and business reports are all familiar Word entry points. Attackers exploit that familiarity by embedding malicious content in workflows users already trust.
- Word documents are common in phishing campaigns.
- Office previews can expose content before a full open.
- Collaborative workflows can distribute malicious files quickly.
- Legacy formats keep broad compatibility pressure on parsers.
Enterprise vs consumer impact
For consumers, the immediate risk is usually narrower: targeted phishing, malicious documents, and secondary compromise. For enterprises, the effect can be broader because Word is frequently tied to identity systems, document management, remote collaboration, and cloud storage. A leak in a corporate document pipeline may reveal more sensitive information than the same leak on a personal laptop.Enterprises also face the multiplication effect. One vulnerable Word installation may not be a crisis; thousands of endpoints with different patch cadences, preview panes, and document automation tools absolutely can be. The same vulnerability can be mild in a single-user context and significant in a managed fleet.
That is why Word advisories often deserve fleet-wide attention, not just per-device caution. In operational terms, the risk is not the CVE in isolation. It is the interaction between the CVE and the organization’s document-handling habits.
Historical Context: Office Disclosure Bugs Are a Pattern
CVE-2026-33822 is not an isolated anomaly. Microsoft Office has had a long trail of memory disclosure and parser-related weaknesses over the years, and those bugs often share a common shape: a crafted file, a user interaction requirement, and a remediation that hardens internal object handling.The old pattern still matters
The CVE-2020-1502 entry is especially relevant because it describes Word improperly disclosing memory contents and notes that an attacker would need to craft a special document and convince a user to open it . That is a textbook example of the Office attack model that defenders have been dealing with for years.What changed over time is not the basic pattern, but the surrounding ecosystem. Today, Word files are more likely to move through cloud storage, synced workspaces, collaboration platforms, and email security gateways. That increases the chances that a vulnerable file is inspected or processed by multiple systems before it reaches the user.
The implication is subtle but important: even a “simple” Word leak can have systemic reach if it exists inside a modern enterprise document lifecycle. The file may be opened once by a user, previewed by a service, scanned by a DLP tool, and rendered in a browser-based interface. Every step is an exposure opportunity.
Why the history matters for response
Security teams should not think of the new CVE as a one-off Word defect. They should treat it as part of a recurring category of issues that tends to appear whenever Office must balance compatibility, performance, and memory safety. That means the right defense is layered: patching, attachment filtering, preview control, and user awareness.It also means trust the shape of the bug. Microsoft rarely invents a Word disclosure advisory for no reason. If the company is willing to publish the CVE, then there is usually enough certainty to justify operational action even when the exploit details are sparse.
Technical Interpretation of the Likely Root Cause
Without public exploit details, defenders should avoid pretending to know the exact root cause. Still, the surrounding evidence suggests the kind of flaw category Word disclosure bugs often fall into: object handling mistakes, parser boundary issues, or improper memory disclosure during document processing. The earlier CVE-2020-1502 language specifically points to Word functions handling objects in memory, which is a useful precedent .What a likely bug class looks like
A Word information disclosure issue may arise when the application reads data beyond a valid structure, leaks uninitialized memory, or reveals internal pointers that were meant to stay private. It may also happen when an embedded object, document component, or rendering path exposes bytes that should have been cleared first.These bugs are often subtle because they can survive ordinary testing. They may only appear with a specially crafted document, a particular field combination, or a malformed embedded element. That is why controlled malicious input is so often the trigger.
The important point is not to guess the exact bug, but to understand the defensive implication: the flaw probably sits in a parsing or rendering path that is difficult to reason about from the outside. That makes vendor patching and hardening especially valuable because attackers can exploit edge cases that normal users never see.
Why details are intentionally sparse
Microsoft has a strong incentive not to over-disclose exploit mechanics. Even when the company provides enough data for customers to act, it generally avoids publishing the kind of low-level information that makes weaponization easier. That restraint is deliberate and consistent with broader coordinated vulnerability disclosure practice.For defenders, the sparse detail should not be read as uncertainty alone. It often means the vendor is balancing helpfulness against operational safety. The right response is to patch first and wait for subsequent research later.
What the Score and Severity Usually Tell Us
Information disclosure vulnerabilities are often scored below their more dangerous counterparts because they do not directly execute code. But that does not mean they are low priority. The real question is how useful the leaked information is and how easy the trigger condition is to satisfy.Low severity is not low importance
A vulnerability that leaks memory in a widely used application can still help attackers bypass mitigations, map out process state, or extract data that should have remained opaque. If the leak is local and user-triggered, the impact may be constrained, but in enterprise environments the scale of deployment can amplify the risk.That is why context matters more than the raw label. A medium-severity disclosure in a niche utility is not the same as a medium-severity disclosure in Word. Word sits in workflows that matter to business continuity, compliance, and privacy.
The best interpretation is therefore conditional. If the bug is exploitable only with user interaction, and if the leak is limited, then the direct impact may be bounded. But if the leak can aid a chain into code execution or credential theft, the effective risk rises quickly.
What defenders should ask
Security teams should be asking a few practical questions:- Is the vulnerable Word build present across managed endpoints?
- Are preview panes or document conversion services in use?
- Do users routinely open external or partner-supplied documents?
- Is patch deployment centralized or fragmented?
- Are there compensating controls for Office attachment handling?
Enterprise Operational Impact
In enterprises, a Word information disclosure vulnerability should be treated as more than a user-level annoyance. Word is deeply embedded in mail flow, compliance archives, collaboration tools, and knowledge-sharing systems, which means a weakness in the parser or memory-handling layer can reverberate across multiple control planes.Patch management implications
The first operational burden is straightforward: inventory and patching. Security teams need to identify which Office channels, update rings, and Word versions are in scope. The newer the organization’s automated update process, the faster the response can be; the more fragmented the estate, the slower and riskier it becomes.This is where Microsoft’s update-guide structure helps. The vendor’s move toward standardized vulnerability metadata and machine-readable advisories is meant to accelerate customer remediation workflows. That is not just a convenience feature; it is an operational necessity in large environments.
A second issue is validation. Office patches can affect add-ins, macros, document templates, and downstream automation. So the security team may need to balance urgency against regression risk. Still, patch delay should be the exception, not the default.
Workflow and governance exposure
Enterprises should also consider document intake points. Email gateways, DLP tools, document management systems, and sandboxing platforms often process Word files before humans do. If the vulnerability can be triggered in any of those layers, the organization’s exposure expands beyond desktops.The governance angle is equally important. If a company has strict controls for executable code but relaxed policies for documents, it may be underestimating Word as an attack channel. Malicious documents remain one of the most efficient routes into enterprise environments because they travel through legitimate business processes.
Consumer and Small Business Impact
For individual users and small businesses, the risk profile is different, but it is not negligible. The most likely threat is still a crafted document delivered through email, messaging, or cloud sharing. The attack may not look spectacular, but it can expose sensitive data or prime the system for additional compromise.Why smaller environments still matter
Small businesses often have fewer layers of inspection and slower patch cadence than large enterprises. That means a user who opens a malicious Word file may be closer to the endpoint of the attack chain than they realize. If the disclosure exposes memory or internal document data, an attacker may leverage that foothold for further abuse.The practical response is simple but effective. Keep Office updated, treat unsolicited documents skeptically, and avoid enabling unnecessary preview or auto-open behaviors. In security terms, boring discipline is often the best defense.
A special concern for smaller organizations is shared-device usage. If multiple users rely on the same machine or if local admin rights are too broad, the impact of a successful document-based attack can increase. That makes baseline hardening as important as patching.
The social engineering factor
Users are more likely to trust Word documents than unfamiliar file types. Attackers know this, and they routinely exploit it with invoices, contracts, delivery notices, HR forms, and meeting material. Even if a disclosure bug is not immediately visible to the victim, it may be the hidden step behind a convincing lure.That is why awareness training still matters. Not because users will spot every malicious file, but because cautious behavior reduces the chance that the first stage of the attack succeeds.
Competitive and Market Implications
Security bugs in Word are not just a Microsoft problem. They affect how enterprises evaluate productivity suites, document workflows, and endpoint controls across the market. When a major vendor publishes another information disclosure advisory for a flagship application, it reinforces the reality that no mainstream office suite is free from parser risk.What rivals learn
Competing productivity vendors can read this kind of disclosure as validation of a broader market truth: document parsing is inherently risky. The difference between products is often not the absence of bugs, but the speed of patching, the transparency of advisories, and the quality of mitigations.That has competitive implications. Vendors that can show stronger sandboxing, tighter document isolation, or safer rendering architectures may use that to differentiate themselves. Likewise, security buyers may weigh the maturity of update channels as heavily as feature sets.
The broader market effect is subtle but real. Each new Office disclosure hardens the case for zero-trust document handling, cloud-based sandboxing, and layered content inspection. It also raises expectations that office software should be designed to fail safely when fed malformed inputs.
Why Microsoft’s messaging matters commercially
Microsoft’s confidence metric is more than a security detail. It is part of the company’s reputation management in an environment where customers want clarity, speed, and trust. By signaling confidence in the flaw’s existence while withholding exploit details, Microsoft tries to maintain both operational usefulness and responsible disclosure discipline.That stance supports the company’s position in enterprise markets where security posture is a purchasing factor. But it also sets a standard that competitors must match: not just patching, but communicating risk in a way defenders can actually use.
Strengths and Opportunities
Microsoft’s vulnerability disclosure model has a few clear strengths here. It gives defenders a named issue, a vendor-backed classification, and a confidence signal that can be operationalized quickly. That combination is far better than leaving customers to infer risk from rumor or secondary reporting.- The confidence metric helps separate confirmed issues from speculation.
- The CVE record gives security teams a stable tracking identifier.
- The information disclosure class is clear enough for prioritization.
- The advisory model supports rapid patch mapping.
- Microsoft’s structured guidance is increasingly suited to automation.
- The bug class is familiar, which makes defensive playbooks easier to apply.
- Enterprises can integrate the signal into risk-based patch scheduling.
Risks and Concerns
The main concern is that information disclosure bugs are easy to underestimate. If a leak appears small or local, teams may push it down the priority list even though it could enable chaining, reconnaissance, or stealthier follow-on compromise. That is especially dangerous in environments where Word documents are a routine business dependency.- Users may assume “information disclosure” means low urgency.
- Attackers can chain leaks into more powerful exploits.
- Document-based lures remain highly effective.
- Preview and automation paths can widen exposure.
- Fragmented Office patching can slow remediation.
- Third-party add-ins may complicate validation.
- Sparse public detail can create false reassurance.
What to Watch Next
The next phase of this story will depend on whether Microsoft later expands the advisory, whether independent researchers publish technical analysis, and whether the issue begins to appear in threat-intelligence reporting. If history is any guide, more detail may emerge after patch adoption begins and defenders start validating exposure across their fleets.The key question is not whether the vulnerability exists — Microsoft’s advisory structure already answers that — but how much attacker value the leaked information provides. If researchers show that the disclosure can be chained into memory corruption bypasses, token exposure, or reliable exploitation, then the practical risk rises materially. If the issue remains a narrow leak with limited exploit utility, the impact stays important but bounded.
Security teams should be prepared to move quickly while preserving operational stability. That means patch validation, endpoint inventory, and document flow review should happen together, not in isolation. In the real world, security and uptime have to be managed in the same room.
- Verify which Word and Office versions are deployed.
- Confirm whether preview panes or auto-render paths are enabled.
- Review email and document gateway policies for malicious attachments.
- Prioritize patching on internet-facing and high-risk user groups.
- Watch for any later Microsoft guidance or revised confidence language.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: