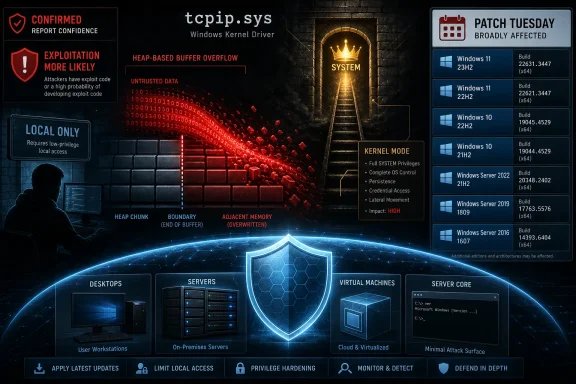
Microsoft disclosed CVE-2026-33837 on May 12, 2026, as an Important Windows TCP/IP local elevation-of-privilege vulnerability caused by a heap-based buffer overflow that lets an authorized low-privilege attacker interact with tcpip.sys and gain kernel-level privileges on affected Windows systems. The bug is not remotely wormable in the terrifying BlueKeep sense, and Microsoft says it was not publicly disclosed or exploited when published. But the uncomfortable part is elsewhere: Microsoft also rates exploitation as more likely, confirms the technical basis, and ships fixes across a strikingly broad Windows estate. For defenders, this is the kind of vulnerability that rarely wins headlines and often wins intrusions.
The phrase “Windows TCP/IP vulnerability” still carries a charge in the Windows world. It evokes remote packets, exposed services, IPv6 parsing bugs, and the nightmare scenario of unauthenticated compromise from the network edge. CVE-2026-33837 is not that. Microsoft’s own vector puts the attack path at local access, with low privileges required and no user interaction.
That distinction matters, but it should not comfort anyone too much. Local elevation-of-privilege vulnerabilities are the connective tissue of modern Windows compromise. They do not usually begin the intrusion; they convert a foothold into control.
The affected component is tcpip.sys, the kernel driver that underpins Windows networking. Microsoft describes the root cause as a heap-based buffer overflow in Windows TCP/IP, and says exploitation could allow an attacker already running code with limited privileges to obtain elevated, kernel-level privileges. In other words, this is a post-compromise accelerator buried inside one of the operating system’s most fundamental subsystems.
That is why the “local” label can be misleading outside a scoring table. An attacker who phishes a user, lands in a browser sandbox, abuses a misconfigured service account, or compromises a low-privilege endpoint through another bug may still need a reliable way to break upward. CVE-2026-33837 is exactly the kind of flaw that can sit in the second act of an intrusion, after initial access but before credential theft, defense evasion, and lateral movement.
Microsoft’s rating captures that tension. The maximum severity is Important, not Critical, because the attacker needs some existing access. Yet the base CVSS score is 7.8, with high impact to confidentiality, integrity, and availability. The vulnerability is not a front door. It is a stairwell to the machine room.
That combination is classic local privilege escalation: the attacker must already be on the box, but once there, the path is expected to be repeatable and does not require a second user to click, approve, or cooperate. Low attack complexity is the part admins should not ignore. It means Microsoft is not modeling this as a fragile, race-heavy stunt that only works in a lab under ideal conditions.
The temporal metrics are equally revealing. Microsoft marks exploit code maturity as unproven, meaning there was no public exploit code at publication time or the exploit remains theoretical. But Microsoft also marks report confidence as confirmed and remediation level as official fix. The company is saying, in effect: the bug is real, the technical basis is credible, and patches are available, even if weaponized public code was not known at disclosure.
This is where the user-supplied metric language around report confidence becomes more than glossary text. Report confidence measures not just whether the vulnerability exists, but how much reliable technical knowledge exists around it. A confirmed rating means defenders should not treat the advisory as a vague placeholder or speculative concern. It means the vendor acknowledges enough about the flaw for remediation to be urgent and for attackers to have a meaningful starting point once patches reveal changed code paths.
Microsoft also lists “Exploitation More Likely.” That phrase is not a guarantee of imminent exploitation, but in patch-management terms it is a prioritization signal. For Windows shops drowning in monthly CVEs, the difference between “less likely” and “more likely” is the difference between routine deployment and accelerated validation.
But the publication of a patch changes the incentives. Attackers routinely diff Windows updates, compare vulnerable and fixed binaries, and search for the code paths Microsoft touched. For a kernel-adjacent or kernel-mode local privilege escalation bug, that process can be especially attractive because the reward is so useful: privilege escalation on fully patched-looking systems that are merely one cumulative update behind.
This is the uncomfortable choreography of Patch Tuesday. Microsoft releases fixes so customers can protect themselves, but the same artifacts can help capable adversaries reconstruct the bug. The more broadly deployed the affected component, the richer the target set becomes for attackers who can tolerate a few days or weeks of reverse engineering.
CVE-2026-33837 is not helped by obscurity. Windows TCP/IP is not a niche optional component installed by a small subset of users. It is core plumbing. The affected products span modern client releases, long-term Windows Server lines, Server Core installations, older supported Windows 10 versions, and extended-support server generations.
The practical message is simple: “not exploited yet” is not the same thing as “low priority.” For local elevation bugs, exploitation often appears after public disclosure, not before it. The lag is the defender’s opportunity.
Microsoft’s executive summary is terse: a heap-based buffer overflow in Windows TCP/IP allows an authorized attacker to elevate privileges locally. That brevity is normal for MSRC advisories, especially when the company wants to avoid handing attackers a recipe. But the stated exploit path adds an important detail: the attacker runs code with limited privileges and interacts with the tcpip.sys kernel driver to gain kernel-level privileges.
That tells defenders where to place the bug mentally. This is not a vulnerability where a malicious packet from the Internet directly compromises an unpatched host. It is a vulnerability where code already executing on the host can abuse a kernel driver interface or code path. The exposed surface may be local, but the consequences are system-wide.
Kernel-level privileges are qualitatively different from administrator privileges in many defensive models. Kernel execution can help disable security tooling, hide processes, tamper with logs, manipulate credentials, and bypass protections designed around user-mode boundaries. Even if modern Windows includes layers of hardening such as virtualization-based security, driver signing, and kernel-mode code integrity, a kernel bug remains among the most valuable building blocks an attacker can acquire.
That is why tcpip.sys vulnerabilities deserve careful treatment even when they are local. The component’s job is ordinary. Its privilege is not.
That breadth matters operationally. A shop may think of its risk in terms of “Windows 11 laptops” or “Server 2022 hosts,” but vulnerabilities in common OS components often cut across neatly separated asset classes. The same CVE can require desktop endpoint deployment, server maintenance windows, golden image updates, VDI refreshes, cloud VM patch baselines, and exception handling for legacy workloads.
The fixed build numbers also reinforce the usual cumulative-update reality. On Windows 11 24H2, Microsoft lists fixed builds in the 26100 branch; on Windows 11 25H2, fixed builds in the 26200 branch; on Windows 10 22H2, the fixed build is in the 19045 branch. Windows Server 2025 and Windows Server 2022 include both standard security updates and hotpatch update paths for certain configurations.
For administrators, this means the remediation task is not simply “install the KB.” It is “confirm the build.” Windows Update, WSUS, Configuration Manager, Intune, Autopatch, third-party patch tools, and image pipelines can all report success differently. The build number remains the cleanest evidence that a machine actually crossed the patched threshold.
Older servers deserve particular attention. Windows Server 2012 and 2012 R2 still appear in many real environments because business applications, industrial systems, or budget cycles outlive mainstream support plans. Microsoft shipping updates for them in this advisory does not make them modern; it means enough organizations still depend on them that a kernel-level privilege escalation bug in shared Windows code cannot be ignored.
Developer workstations are one obvious category. They often have compilers, scripting tools, package managers, cached credentials, source access, and intermittent administrative workflows. A local privilege escalation bug on a developer laptop can turn a compromised browser session or malicious package into a supply-chain problem.
Jump boxes and admin workstations are another. These systems are supposed to be hardened precisely because they sit near privileged credentials. A local kernel escalation on such a machine is not merely an endpoint incident; it is a possible path into domain administration, cloud consoles, management planes, and backup infrastructure.
Multi-user servers deserve a different kind of scrutiny. Remote Desktop Session Host, shared engineering servers, legacy app servers, and systems where service accounts run custom code all increase the chance that a low-privilege context exists for an attacker to abuse. The local requirement does not reduce risk much if untrusted or semi-trusted users already run code there.
Then there are servers that process untrusted input through services that might be compromised by other vulnerabilities. A web application flaw, deserialization bug, exposed management console, or leaked credential may provide low-privilege execution. CVE-2026-33837 could then become the privilege escalator that turns an application compromise into operating system control.
This is the right mental model: not “Can the attacker reach TCP/IP from the Internet?” but “Where would local SYSTEM or kernel-level escalation materially worsen an intrusion already in progress?” That question produces a very different patch queue.
But hotpatching should not become a psychological workaround for verification. If anything, it raises the need to know which machines are eligible, which are on the right baseline, and which received the hotpatch versus the conventional cumulative update. A hotpatch entry in an advisory is not a guarantee that every server in the fleet can take the hotpatch path.
The most disciplined organizations will treat CVE-2026-33837 as a test of patch telemetry. Can the team identify affected Windows versions? Can it distinguish Windows Server Core from desktop experience installations? Can it confirm build numbers after deployment? Can it find the stubborn machines that stopped reporting, failed prerequisites, or live outside standard management?
That last category is usually where local privilege escalation bugs linger. The forgotten VM, the lab subnet, the app team’s unmanaged server, the branch office PC that only connects intermittently — these are not edge cases to an attacker. They are inventory mistakes waiting to be converted into footholds.
Microsoft’s “customer action required” field is marked required across the listed rows. That sounds banal, but it is the clearest instruction in the advisory. There is an official fix. Apply it. Then prove that it applied.
Microsoft marks report confidence as confirmed. That means the vulnerability is not merely rumored, inferred, or based on incomplete public chatter. The vendor has enough confidence in the existence and technical details to publish the CVE, assign the weakness as CWE-122, ship fixes, and describe the exploit path involving limited-privilege code interacting with tcpip.sys.
At the same time, Microsoft marks exploit code maturity as unproven. This creates a common but important asymmetry: defenders know the bug is real before the public knows how to exploit it. That is the ideal remediation window. Waiting for exploit proof-of-concept code to appear is an expensive way to validate someone else’s reverse engineering.
The “Exploitation More Likely” assessment sharpens the point. Microsoft is not saying exploitation is already happening, and it is not saying exploit code is public. It is saying that, given the characteristics of the bug, exploitation is more likely than not within its exploitability-index framework. For a local kernel escalation bug with low complexity and no user interaction, that judgment is not surprising.
This is where patch prioritization should separate vulnerability management from headline management. A remote code execution zero-day will always dominate the room. But a reliable local privilege escalation vulnerability in a core Windows driver is often what turns yesterday’s low-severity foothold into tomorrow’s incident report.
The system is better than the alternative, but it does not freeze adversaries in place. Once the patch is released, the delta between vulnerable and fixed code becomes a research target. Skilled actors can study the changes, identify the vulnerable logic, and attempt to construct a working exploit. The acknowledgement and CWE classification add context, not a full exploit path, but they still sit inside a broader information package.
That is not an argument for less disclosure. It is an argument for faster remediation. The purpose of coordinated disclosure is to give defenders the first move. It is wasted if organizations treat the first move as a calendar invite for next quarter.
There is also a community benefit to Microsoft’s increasing use of CWE mapping. Calling out CWE-122 tells defenders and researchers what class of failure is involved: heap-based buffer overflow. That helps security teams reason about exploitability, detection expectations, and the likelihood that memory-safety mitigations may complicate but not eliminate exploitation.
For WindowsForum readers, this is the larger architectural story. Windows continues to carry enormous amounts of privileged C and C++ code in core subsystems. Microsoft has invested heavily in mitigations, sandboxing, kernel hardening, and more recently memory-safe language work in selected areas. But bugs like CVE-2026-33837 show why the platform’s security future depends not only on monthly patching, but on reducing entire classes of memory-corruption bugs over time.
The risk profile is different from enterprise, but the chain logic is the same. Consumer malware often starts in user space and then seeks persistence, credential access, tamper resistance, and security-tool bypass. Kernel-level elevation makes those goals easier.
Windows 10 users should pay particular attention because the Windows 10 lifecycle has become more fragmented. Different editions, enrollment states, and support paths affect whether a machine is still receiving the right updates. If Windows Update is failing or paused indefinitely, this is the sort of CVE that argues for fixing the update problem rather than rationalizing it.
Windows 11 users should verify the installed build after patching, especially in mixed fleets where 23H2, 24H2, 25H2, and 26H1 may coexist. Version labels alone are not enough. The build number is what tells you whether the relevant fix landed.
Power users who manage family machines, home labs, or small-business networks should think like admins here. Inventory first, update second, verify third. The vulnerability’s broad product coverage makes assumptions dangerous.
Endpoint detection tools may catch exploit behavior, memory anomalies, suspicious driver interactions, token manipulation, or post-exploitation activity. But relying on detection for a kernel-level local privilege escalation bug is a poor substitute for patching. By the time the behavior is visible, the attacker may already have crossed the boundary the patch was meant to protect.
That does not mean defenders are blind. They should still look for low-privilege processes spawning unexpected elevated children, unusual service creation, credential dumping attempts, tampering with security agents, and suspicious activity around admin tools. But those are downstream symptoms, not reliable exploit indicators.
The best detection strategy is therefore inventory-driven. Which systems are missing the fixed build? Which machines are internet-facing and also unpatched? Which hosts permit low-privilege interactive logon? Which servers run exposed applications under accounts that could provide an initial foothold? Those questions turn a CVE into a remediation campaign.
For security teams with mature telemetry, CVE-2026-33837 is a chance to connect vulnerability data with identity and exposure data. A rarely used workstation with no privileged access is one risk. A domain admin jump host one update behind is another. CVSS cannot tell you that. Your environment can.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 The Dangerous Word Is Local, Not TCP/IP
The Dangerous Word Is Local, Not TCP/IP
The phrase “Windows TCP/IP vulnerability” still carries a charge in the Windows world. It evokes remote packets, exposed services, IPv6 parsing bugs, and the nightmare scenario of unauthenticated compromise from the network edge. CVE-2026-33837 is not that. Microsoft’s own vector puts the attack path at local access, with low privileges required and no user interaction.That distinction matters, but it should not comfort anyone too much. Local elevation-of-privilege vulnerabilities are the connective tissue of modern Windows compromise. They do not usually begin the intrusion; they convert a foothold into control.
The affected component is tcpip.sys, the kernel driver that underpins Windows networking. Microsoft describes the root cause as a heap-based buffer overflow in Windows TCP/IP, and says exploitation could allow an attacker already running code with limited privileges to obtain elevated, kernel-level privileges. In other words, this is a post-compromise accelerator buried inside one of the operating system’s most fundamental subsystems.
That is why the “local” label can be misleading outside a scoring table. An attacker who phishes a user, lands in a browser sandbox, abuses a misconfigured service account, or compromises a low-privilege endpoint through another bug may still need a reliable way to break upward. CVE-2026-33837 is exactly the kind of flaw that can sit in the second act of an intrusion, after initial access but before credential theft, defense evasion, and lateral movement.
Microsoft’s rating captures that tension. The maximum severity is Important, not Critical, because the attacker needs some existing access. Yet the base CVSS score is 7.8, with high impact to confidentiality, integrity, and availability. The vulnerability is not a front door. It is a stairwell to the machine room.
Microsoft’s Scoring Tells a Sharper Story Than the Severity Label
Severity labels compress risk into something executives can skim and ticketing systems can sort. CVSS vectors, while imperfect, often tell the more useful story. CVE-2026-33837 is scored as local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, and high impact across confidentiality, integrity, and availability.That combination is classic local privilege escalation: the attacker must already be on the box, but once there, the path is expected to be repeatable and does not require a second user to click, approve, or cooperate. Low attack complexity is the part admins should not ignore. It means Microsoft is not modeling this as a fragile, race-heavy stunt that only works in a lab under ideal conditions.
The temporal metrics are equally revealing. Microsoft marks exploit code maturity as unproven, meaning there was no public exploit code at publication time or the exploit remains theoretical. But Microsoft also marks report confidence as confirmed and remediation level as official fix. The company is saying, in effect: the bug is real, the technical basis is credible, and patches are available, even if weaponized public code was not known at disclosure.
This is where the user-supplied metric language around report confidence becomes more than glossary text. Report confidence measures not just whether the vulnerability exists, but how much reliable technical knowledge exists around it. A confirmed rating means defenders should not treat the advisory as a vague placeholder or speculative concern. It means the vendor acknowledges enough about the flaw for remediation to be urgent and for attackers to have a meaningful starting point once patches reveal changed code paths.
Microsoft also lists “Exploitation More Likely.” That phrase is not a guarantee of imminent exploitation, but in patch-management terms it is a prioritization signal. For Windows shops drowning in monthly CVEs, the difference between “less likely” and “more likely” is the difference between routine deployment and accelerated validation.
The Absence of Public Exploitation Is a Clock, Not a Shield
Microsoft says CVE-2026-33837 was not publicly disclosed and not exploited at the time of original publication. That is good news in the narrow sense. It means defenders are not already chasing known in-the-wild campaigns tied to this CVE, at least according to Microsoft’s initial disclosure.But the publication of a patch changes the incentives. Attackers routinely diff Windows updates, compare vulnerable and fixed binaries, and search for the code paths Microsoft touched. For a kernel-adjacent or kernel-mode local privilege escalation bug, that process can be especially attractive because the reward is so useful: privilege escalation on fully patched-looking systems that are merely one cumulative update behind.
This is the uncomfortable choreography of Patch Tuesday. Microsoft releases fixes so customers can protect themselves, but the same artifacts can help capable adversaries reconstruct the bug. The more broadly deployed the affected component, the richer the target set becomes for attackers who can tolerate a few days or weeks of reverse engineering.
CVE-2026-33837 is not helped by obscurity. Windows TCP/IP is not a niche optional component installed by a small subset of users. It is core plumbing. The affected products span modern client releases, long-term Windows Server lines, Server Core installations, older supported Windows 10 versions, and extended-support server generations.
The practical message is simple: “not exploited yet” is not the same thing as “low priority.” For local elevation bugs, exploitation often appears after public disclosure, not before it. The lag is the defender’s opportunity.
tcpip.sys Is Not Just a Network Driver, It Is Part of the Trust Boundary
It is tempting to think of TCP/IP as packet handling and port listening, but tcpip.sys sits in kernel mode and participates in a dense ecosystem of networking, filtering, virtualization, containerization, VPNs, firewalls, endpoint security, and cloud management agents. A memory corruption bug there is not just a networking oddity. It is a potential route into the most privileged execution context on the machine.Microsoft’s executive summary is terse: a heap-based buffer overflow in Windows TCP/IP allows an authorized attacker to elevate privileges locally. That brevity is normal for MSRC advisories, especially when the company wants to avoid handing attackers a recipe. But the stated exploit path adds an important detail: the attacker runs code with limited privileges and interacts with the tcpip.sys kernel driver to gain kernel-level privileges.
That tells defenders where to place the bug mentally. This is not a vulnerability where a malicious packet from the Internet directly compromises an unpatched host. It is a vulnerability where code already executing on the host can abuse a kernel driver interface or code path. The exposed surface may be local, but the consequences are system-wide.
Kernel-level privileges are qualitatively different from administrator privileges in many defensive models. Kernel execution can help disable security tooling, hide processes, tamper with logs, manipulate credentials, and bypass protections designed around user-mode boundaries. Even if modern Windows includes layers of hardening such as virtualization-based security, driver signing, and kernel-mode code integrity, a kernel bug remains among the most valuable building blocks an attacker can acquire.
That is why tcpip.sys vulnerabilities deserve careful treatment even when they are local. The component’s job is ordinary. Its privilege is not.
The Patch List Shows a Vulnerability Across Generations, Not a Single Release Mistake
The affected product list is broad enough to make this feel less like a Windows 11-era regression and more like a flaw in shared networking code carried across generations. Microsoft lists fixes for Windows 11 versions 23H2, 24H2, 25H2, and 26H1; Windows 10 versions 21H2 and 22H2; Windows Server 2016, 2019, 2022, 2022 23H2, and 2025; and older Windows Server 2012 and 2012 R2 variants. Server Core installations are explicitly included for multiple server releases.That breadth matters operationally. A shop may think of its risk in terms of “Windows 11 laptops” or “Server 2022 hosts,” but vulnerabilities in common OS components often cut across neatly separated asset classes. The same CVE can require desktop endpoint deployment, server maintenance windows, golden image updates, VDI refreshes, cloud VM patch baselines, and exception handling for legacy workloads.
The fixed build numbers also reinforce the usual cumulative-update reality. On Windows 11 24H2, Microsoft lists fixed builds in the 26100 branch; on Windows 11 25H2, fixed builds in the 26200 branch; on Windows 10 22H2, the fixed build is in the 19045 branch. Windows Server 2025 and Windows Server 2022 include both standard security updates and hotpatch update paths for certain configurations.
For administrators, this means the remediation task is not simply “install the KB.” It is “confirm the build.” Windows Update, WSUS, Configuration Manager, Intune, Autopatch, third-party patch tools, and image pipelines can all report success differently. The build number remains the cleanest evidence that a machine actually crossed the patched threshold.
Older servers deserve particular attention. Windows Server 2012 and 2012 R2 still appear in many real environments because business applications, industrial systems, or budget cycles outlive mainstream support plans. Microsoft shipping updates for them in this advisory does not make them modern; it means enough organizations still depend on them that a kernel-level privilege escalation bug in shared Windows code cannot be ignored.
The Enterprise Risk Is Not Internet Exposure, It Is Blast Radius
Security teams often prioritize vulnerabilities by external exposure. That is rational when a bug can be hit over the network by anyone with an IP address. CVE-2026-33837 does not fit that model. It should instead be prioritized by where low-privilege code execution is plausible and where privilege escalation would be most damaging.Developer workstations are one obvious category. They often have compilers, scripting tools, package managers, cached credentials, source access, and intermittent administrative workflows. A local privilege escalation bug on a developer laptop can turn a compromised browser session or malicious package into a supply-chain problem.
Jump boxes and admin workstations are another. These systems are supposed to be hardened precisely because they sit near privileged credentials. A local kernel escalation on such a machine is not merely an endpoint incident; it is a possible path into domain administration, cloud consoles, management planes, and backup infrastructure.
Multi-user servers deserve a different kind of scrutiny. Remote Desktop Session Host, shared engineering servers, legacy app servers, and systems where service accounts run custom code all increase the chance that a low-privilege context exists for an attacker to abuse. The local requirement does not reduce risk much if untrusted or semi-trusted users already run code there.
Then there are servers that process untrusted input through services that might be compromised by other vulnerabilities. A web application flaw, deserialization bug, exposed management console, or leaked credential may provide low-privilege execution. CVE-2026-33837 could then become the privilege escalator that turns an application compromise into operating system control.
This is the right mental model: not “Can the attacker reach TCP/IP from the Internet?” but “Where would local SYSTEM or kernel-level escalation materially worsen an intrusion already in progress?” That question produces a very different patch queue.
Hotpatching Helps, but It Does Not Remove the Need for Proof
Microsoft’s affected-products table includes security hotpatch updates for some Windows Server 2022, Windows Server 2025, and Windows 11 24H2/25H2 entries. That is an important operational detail because hotpatching can reduce reboot pressure, especially in cloud and server environments where uptime windows are painfully negotiated.But hotpatching should not become a psychological workaround for verification. If anything, it raises the need to know which machines are eligible, which are on the right baseline, and which received the hotpatch versus the conventional cumulative update. A hotpatch entry in an advisory is not a guarantee that every server in the fleet can take the hotpatch path.
The most disciplined organizations will treat CVE-2026-33837 as a test of patch telemetry. Can the team identify affected Windows versions? Can it distinguish Windows Server Core from desktop experience installations? Can it confirm build numbers after deployment? Can it find the stubborn machines that stopped reporting, failed prerequisites, or live outside standard management?
That last category is usually where local privilege escalation bugs linger. The forgotten VM, the lab subnet, the app team’s unmanaged server, the branch office PC that only connects intermittently — these are not edge cases to an attacker. They are inventory mistakes waiting to be converted into footholds.
Microsoft’s “customer action required” field is marked required across the listed rows. That sounds banal, but it is the clearest instruction in the advisory. There is an official fix. Apply it. Then prove that it applied.
Report Confidence Is the Quiet Alarm Bell
The user’s excerpt focuses on report confidence, and that is the right lens for this CVE. Report confidence is easy to skip because it looks like scoring-system furniture. In this case, it is doing real work.Microsoft marks report confidence as confirmed. That means the vulnerability is not merely rumored, inferred, or based on incomplete public chatter. The vendor has enough confidence in the existence and technical details to publish the CVE, assign the weakness as CWE-122, ship fixes, and describe the exploit path involving limited-privilege code interacting with tcpip.sys.
At the same time, Microsoft marks exploit code maturity as unproven. This creates a common but important asymmetry: defenders know the bug is real before the public knows how to exploit it. That is the ideal remediation window. Waiting for exploit proof-of-concept code to appear is an expensive way to validate someone else’s reverse engineering.
The “Exploitation More Likely” assessment sharpens the point. Microsoft is not saying exploitation is already happening, and it is not saying exploit code is public. It is saying that, given the characteristics of the bug, exploitation is more likely than not within its exploitability-index framework. For a local kernel escalation bug with low complexity and no user interaction, that judgment is not surprising.
This is where patch prioritization should separate vulnerability management from headline management. A remote code execution zero-day will always dominate the room. But a reliable local privilege escalation vulnerability in a core Windows driver is often what turns yesterday’s low-severity foothold into tomorrow’s incident report.
Coordinated Disclosure Still Leaves Attackers a Map
Microsoft credits h4urek, associated with secsys lab at Fudan University, in the acknowledgements for this vulnerability. That is a sign of coordinated vulnerability disclosure functioning as intended: a researcher reports a bug, the vendor investigates, and fixes ship with public credit.The system is better than the alternative, but it does not freeze adversaries in place. Once the patch is released, the delta between vulnerable and fixed code becomes a research target. Skilled actors can study the changes, identify the vulnerable logic, and attempt to construct a working exploit. The acknowledgement and CWE classification add context, not a full exploit path, but they still sit inside a broader information package.
That is not an argument for less disclosure. It is an argument for faster remediation. The purpose of coordinated disclosure is to give defenders the first move. It is wasted if organizations treat the first move as a calendar invite for next quarter.
There is also a community benefit to Microsoft’s increasing use of CWE mapping. Calling out CWE-122 tells defenders and researchers what class of failure is involved: heap-based buffer overflow. That helps security teams reason about exploitability, detection expectations, and the likelihood that memory-safety mitigations may complicate but not eliminate exploitation.
For WindowsForum readers, this is the larger architectural story. Windows continues to carry enormous amounts of privileged C and C++ code in core subsystems. Microsoft has invested heavily in mitigations, sandboxing, kernel hardening, and more recently memory-safe language work in selected areas. But bugs like CVE-2026-33837 show why the platform’s security future depends not only on monthly patching, but on reducing entire classes of memory-corruption bugs over time.
Home PCs Are Not Exempt From the Enterprise Logic
For home users, the action is straightforward: install the May 2026 Windows security update for your supported Windows version and do not delay it because the CVE is “only local.” A local privilege escalation vulnerability can still be chained with malware, malicious installers, cracked software, game cheats, browser exploits, document attacks, or stolen low-privilege credentials.The risk profile is different from enterprise, but the chain logic is the same. Consumer malware often starts in user space and then seeks persistence, credential access, tamper resistance, and security-tool bypass. Kernel-level elevation makes those goals easier.
Windows 10 users should pay particular attention because the Windows 10 lifecycle has become more fragmented. Different editions, enrollment states, and support paths affect whether a machine is still receiving the right updates. If Windows Update is failing or paused indefinitely, this is the sort of CVE that argues for fixing the update problem rather than rationalizing it.
Windows 11 users should verify the installed build after patching, especially in mixed fleets where 23H2, 24H2, 25H2, and 26H1 may coexist. Version labels alone are not enough. The build number is what tells you whether the relevant fix landed.
Power users who manage family machines, home labs, or small-business networks should think like admins here. Inventory first, update second, verify third. The vulnerability’s broad product coverage makes assumptions dangerous.
Detection Will Be Harder Than Patching
Local privilege escalation bugs are notoriously difficult to detect once exploited. There may be no obvious inbound network event, no suspicious email click, and no single log entry that says “kernel privilege escalation occurred.” The exploit may happen inside a short-lived process that quickly hands off to a more durable payload.Endpoint detection tools may catch exploit behavior, memory anomalies, suspicious driver interactions, token manipulation, or post-exploitation activity. But relying on detection for a kernel-level local privilege escalation bug is a poor substitute for patching. By the time the behavior is visible, the attacker may already have crossed the boundary the patch was meant to protect.
That does not mean defenders are blind. They should still look for low-privilege processes spawning unexpected elevated children, unusual service creation, credential dumping attempts, tampering with security agents, and suspicious activity around admin tools. But those are downstream symptoms, not reliable exploit indicators.
The best detection strategy is therefore inventory-driven. Which systems are missing the fixed build? Which machines are internet-facing and also unpatched? Which hosts permit low-privilege interactive logon? Which servers run exposed applications under accounts that could provide an initial foothold? Those questions turn a CVE into a remediation campaign.
For security teams with mature telemetry, CVE-2026-33837 is a chance to connect vulnerability data with identity and exposure data. A rarely used workstation with no privileged access is one risk. A domain admin jump host one update behind is another. CVSS cannot tell you that. Your environment can.
The May Patch Window Has a Kernel-Shaped Priority
The concrete response to CVE-2026-33837 is less glamorous than the vulnerability itself. Patch supported Windows systems, verify fixed builds, and prioritize systems where low-privilege code execution would be easy or privilege escalation would be catastrophic. The advisory’s combination of confirmed report confidence and “Exploitation More Likely” should move this above routine backlog handling.- Organizations should deploy the May 12, 2026 Windows security updates for affected Windows client and server versions rather than waiting for public exploit code.
- Administrators should verify remediation by build number, not merely by update history or a management console success state.
- Servers that allow interactive user sessions, run exposed applications, or host privileged management workflows should move toward the front of the patch queue.
- Windows Server Core installations are affected where listed, so minimal server deployments should not be assumed safe by design.
- The lack of known exploitation at publication is a temporary advantage for defenders, not a reason to defer remediation.
- Home users and small offices should treat this as a normal but important Windows security update, especially on machines that install untrusted software or share accounts.
Source: MSRC Security Update Guide - Microsoft Security Response Center