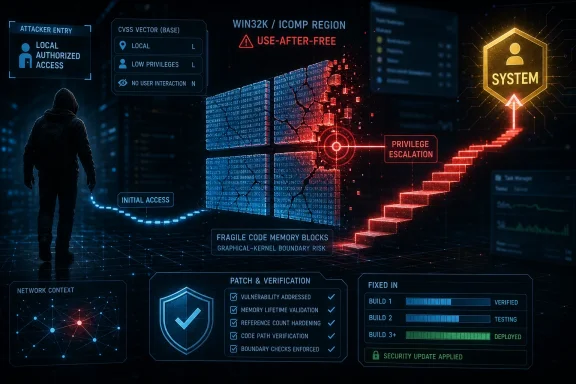
Microsoft disclosed CVE-2026-33840 on May 12, 2026 as an Important Win32k elevation-of-privilege flaw in Windows 11 and Windows Server 2025 that lets a locally authorized attacker exploit a use-after-free bug and gain SYSTEM privileges. The uncomfortable part is not the label “Important,” which Windows admins have learned can hide plenty of operational pain. It is the combination Microsoft chose: low attack complexity, no user interaction, confirmed report confidence, and “exploitation more likely.” This is the sort of local bug that rarely wins headlines by itself but often becomes the hinge in a real intrusion chain.
CVE-2026-33840 is not a remote code execution bug, and that distinction matters. An attacker cannot simply point traffic at an exposed Windows service and pop a machine over the network. Microsoft’s own scoring describes the attack vector as local and requires low privileges before exploitation.
That should not lull anyone into treating it as routine housekeeping. Local privilege escalation is the second act of many compromises: the phishing payload lands, the stolen credentials work, the browser sandbox cracks, or the malicious insider already has a foothold. What turns a nuisance into a breach is the move from “I can run as a user” to “I can run as the machine.”
SYSTEM remains the prize because it changes the economics of the intrusion. With SYSTEM-level control, attackers can tamper with security tooling, dump credentials, install persistent services, reach into protected parts of the OS, and pivot toward domain assets. The bug’s local nature narrows the front door, but the privilege gained widens every corridor behind it.
Microsoft’s score lands at CVSS 7.8 for the base severity and 6.8 for the temporal score. That is familiar territory for Windows elevation-of-privilege bugs: high enough to demand prioritization, not high enough to trigger the panic reflex usually reserved for wormable or unauthenticated network flaws. The danger with CVSS is that a single number can flatten the story. In this case, the story is in the vector.
The weakness classification is CWE-416: use after free. That phrase is familiar because it describes a class of memory-safety failures where software continues to use a memory object after it has been released. In kernel-adjacent or kernel-mode contexts, such bugs can become especially serious because the attacker is not merely crashing an application; they may be manipulating memory in a privileged execution environment.
Microsoft’s summary is concise: use after free in Windows Win32K - ICOMP allows an authorized attacker to elevate privileges locally. That is not a full exploit narrative, and we should not pretend it is. But it tells administrators enough to understand the defensive posture: the vulnerability is confirmed by the vendor, the root-cause category is known, and the expected impact is elevation to SYSTEM.
Win32k bugs also carry a particular operational sting because they tend to affect ordinary Windows endpoints, not just special-purpose server roles. A browser exploit, document exploit, malicious installer, remote access foothold, or living-off-the-land session can all benefit from a reliable local privilege escalation path. The vulnerability may not be the first compromise, but it can become the step that makes the compromise durable.
The low attack complexity rating is particularly important. Microsoft is not saying a successful exploit requires unusual timing, rare system conditions, or a highly specific configuration. In CVSS language, low complexity means attackers can expect repeatable success against the vulnerable component once the preconditions are met. That is one reason local privilege escalation bugs become useful quickly after patches ship and reverse engineering begins.
The “privileges required: low” metric also matters more than it appears. Low privilege does not mean harmless; it means the attacker starts from a normal authorized context. In enterprise terms, that could be a compromised standard user account, a low-rights malware process, or a foothold obtained through some other vulnerability. Windows security architecture assumes that low-privileged code should remain boxed in. CVE-2026-33840 is about breaking that assumption.
The confidentiality, integrity, and availability impacts are all marked high. That is CVSS shorthand for the consequence of successful exploitation, not a promise that every exploit will perform every action. Still, the direction is clear: once the bug is exploited, the attacker’s relationship to the machine changes fundamentally.
That matters because confirmed bugs have a different afterlife from speculative ones. Once a vendor ships a fix, attackers can compare old and new binaries, isolate the patched code path, and begin reconstructing the vulnerability. The more precise the advisory, the easier it is for defenders to prioritize; the same precision can also help exploit developers understand where to look.
This is the constant tension in modern vulnerability disclosure. Transparency helps administrators make sane patching decisions. It also gives the offensive ecosystem a starting map. In this case, Microsoft has named the component, the weakness class, the privilege outcome, and the exploitability expectation. That is not an exploit, but it is enough to raise the priority of the patch.
The temporal metric also says exploit code maturity is unproven. That means Microsoft did not list public exploit code at original publication. But “unproven” is not “unlikely,” and Microsoft separately assessed exploitation as more likely. The practical reading is simple: there may not be public working code today, but defenders should assume capable researchers and attackers will study the fix.
But Patch Tuesday has its own strange physics. The moment the patch becomes public, the vulnerability starts moving from private knowledge into a wider technical ecosystem. Security vendors analyze it for detection logic. Administrators test it. Attackers diff it. Researchers probe it. A bug that was not publicly exploited on Tuesday morning can become far more understandable by Friday.
The “Exploitation More Likely” assessment is therefore the line administrators should circle. Microsoft uses that language when it believes exploit development is plausible enough to affect prioritization. For a local elevation-of-privilege flaw, that usually means the bug has characteristics that make it attractive as a post-compromise tool.
This is not a call to panic-patch every domain controller without testing. It is a call to avoid placing this CVE in the low-priority bucket just because it is not remote and not already exploited. The correct comparison is not between this bug and a wormable SMB disaster. The correct comparison is between this bug and every other local privilege escalation path attackers might use after the first foothold.
For Windows 11 version 24H2 and 25H2, Microsoft lists both x64 and ARM64 systems. For Windows 11 version 26H1, Microsoft lists x64 and ARM64 builds as well. The fixed build numbers differ by release branch, as expected, with 24H2 moving into the 26100.84xx range, 25H2 into the 26200.84xx range, and 26H1 into the 28000.2113 build.
Windows Server 2025 is listed twice: once for the standard installation and once for Server Core. Both show required customer action, and both include security update and hotpatch update paths. That is notable because Server Core’s smaller footprint does not make it immune to every class of Windows kernel or graphical subsystem-adjacent vulnerability.
The presence of hotpatch updates for several entries also reflects Microsoft’s evolving server servicing model. Hotpatching can reduce reboot pressure, which matters in production environments, but it should not become an excuse for vague patch status. For a vulnerability like this, administrators need to know not only that a system is “managed,” but that it has reached a fixed build.
SYSTEM is not just “administrator, but more.” It is the context under which much of Windows itself operates. Malware running as SYSTEM can disable or blind endpoint controls if tamper protections fail, create services, manipulate protected files, scrape credentials from memory under the right conditions, and make itself harder to remove. In incident response, discovering a transition to SYSTEM often changes the assumed blast radius.
This is why local privilege escalation vulnerabilities are so valuable in chained attacks. A phishing document may provide execution as a user. A stolen VPN credential may provide access to a workstation. A misconfigured remote management tool may provide a weak foothold. But attackers still need privilege, persistence, and movement. CVE-2026-33840 appears to serve the privilege part of that chain.
The phrase “authorized attacker” can also mislead casual readers. It does not mean an insider with legitimate administrative authority. It means the attacker already has some authorized local capability, even if that capability came from compromising a user or process. In real networks, that is not a rare precondition.
For Windows Server 2025, the exposure model is different. Servers may have fewer interactive users, but they also concentrate value. A compromised web application worker, scheduled task, low-privileged service account, or management session can become far more dangerous if paired with a reliable local SYSTEM escalation. Server Core reduces some surface area, but it does not erase the need to patch kernel-adjacent vulnerabilities.
Administrators should therefore resist a single fleet-wide priority label. Internet-facing servers with low-privileged workloads deserve careful attention. Developer workstations and admin workstations deserve urgency because they are privilege-rich environments. General user endpoints should be patched on the normal accelerated security cadence, especially where users have access to sensitive systems.
The bigger lesson is that patch order should follow attack paths, not just CVSS scores. A 7.8 local privilege escalation flaw on privileged access workstations may deserve faster treatment than a higher-scored issue on a well-isolated lab system. CVSS helps triage, but environment decides risk.
The affected Windows 11 24H2 systems show fixed builds in the 26100.8457 and 26100.8390 range, depending on the update path. Windows 11 25H2 systems show fixed builds in the 26200.8457 and 26200.8390 range. Windows 11 26H1 systems show build 28000.2113. Windows Server 2025 entries show 26100.32860 and 26100.32772 for the listed update paths.
That build-number detail is valuable because KB installation status can be messy. Supersedence, hotpatching, failed reboots, paused update rings, and partially remediated machines can all make dashboards look healthier than the estate really is. Build verification gives administrators a more concrete signal.
Security teams should also watch for machines outside the obvious Windows Update flow. Golden images, VDI pools, offline servers, test rings, kiosk devices, and ARM64 laptops can lag behind. The advisory explicitly includes ARM64 Windows 11 systems, which is a reminder that the Windows endpoint estate is becoming more heterogeneous.
Coordinated disclosure is not glamorous, but it is the security ecosystem working as designed. A researcher finds a bug, reports it, the vendor investigates, the patch ships, and customers get enough information to act. The system is imperfect, but the alternative is usually worse: silent exploitation, public proof-of-concept drops without fixes, or vague advisories that leave defenders guessing.
Still, coordinated disclosure does not remove urgency. It merely starts the race from a better line. Once the patch exists, offensive analysis becomes easier. Microsoft’s “exploitation more likely” tag is the warning that this one may not stay academically interesting for long.
For enterprises, the right response is disciplined speed. Test the update where business risk demands it, deploy quickly to the highest-risk rings, and verify fixed builds. The worst response is to treat “not exploited” as an indefinite grace period.
That does not mean Windows is uniquely broken or that mitigations have failed. It means large, compatibility-heavy operating systems carry technical debt in places that matter. Win32k exists because decades of applications expect Windows to behave in certain ways. Security engineering has to harden that reality, not an idealized greenfield OS.
The “ICOMP” detail in Microsoft’s summary may mean little to most admins, but the pattern means plenty. A component deep enough to matter, reachable enough to exploit locally, and privileged enough to yield SYSTEM is exactly the kind of bug attackers want in their toolbox. When such a bug also has low complexity and confirmed report confidence, it deserves to move up the queue.
The broader Microsoft story is also about transparency. The advisory includes the CWE classification, CVSS vector, temporal scoring, exploitability assessment, affected products, fixed builds, and acknowledgements. That is useful. It lets defenders reason about risk instead of relying solely on a severity adjective.
The concrete takeaways are straightforward:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s “Important” Label Undersells the Shape of the Risk
Microsoft’s “Important” Label Undersells the Shape of the Risk
CVE-2026-33840 is not a remote code execution bug, and that distinction matters. An attacker cannot simply point traffic at an exposed Windows service and pop a machine over the network. Microsoft’s own scoring describes the attack vector as local and requires low privileges before exploitation.That should not lull anyone into treating it as routine housekeeping. Local privilege escalation is the second act of many compromises: the phishing payload lands, the stolen credentials work, the browser sandbox cracks, or the malicious insider already has a foothold. What turns a nuisance into a breach is the move from “I can run as a user” to “I can run as the machine.”
SYSTEM remains the prize because it changes the economics of the intrusion. With SYSTEM-level control, attackers can tamper with security tooling, dump credentials, install persistent services, reach into protected parts of the OS, and pivot toward domain assets. The bug’s local nature narrows the front door, but the privilege gained widens every corridor behind it.
Microsoft’s score lands at CVSS 7.8 for the base severity and 6.8 for the temporal score. That is familiar territory for Windows elevation-of-privilege bugs: high enough to demand prioritization, not high enough to trigger the panic reflex usually reserved for wormable or unauthenticated network flaws. The danger with CVSS is that a single number can flatten the story. In this case, the story is in the vector.
Win32k Remains the Old, Busy, Dangerous Road Through Windows
The vulnerable component named by Microsoft is Windows Win32K, more specifically the ICOMP area referenced in the advisory’s summary. Win32k has long been one of the places defenders watch carefully because it sits close to the messy boundary between graphical user interfaces, kernel-mode behavior, and user-controlled inputs. It is old Windows infrastructure doing old Windows jobs in a world where attackers have become very good at turning complexity into leverage.The weakness classification is CWE-416: use after free. That phrase is familiar because it describes a class of memory-safety failures where software continues to use a memory object after it has been released. In kernel-adjacent or kernel-mode contexts, such bugs can become especially serious because the attacker is not merely crashing an application; they may be manipulating memory in a privileged execution environment.
Microsoft’s summary is concise: use after free in Windows Win32K - ICOMP allows an authorized attacker to elevate privileges locally. That is not a full exploit narrative, and we should not pretend it is. But it tells administrators enough to understand the defensive posture: the vulnerability is confirmed by the vendor, the root-cause category is known, and the expected impact is elevation to SYSTEM.
Win32k bugs also carry a particular operational sting because they tend to affect ordinary Windows endpoints, not just special-purpose server roles. A browser exploit, document exploit, malicious installer, remote access foothold, or living-off-the-land session can all benefit from a reliable local privilege escalation path. The vulnerability may not be the first compromise, but it can become the step that makes the compromise durable.
The CVSS Vector Says More Than the Severity Banner
The CVSS vector for CVE-2026-33840 is blunt in the places that matter: local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, and high impact to confidentiality, integrity, and availability. That is the standard shape of a serious Windows local privilege escalation issue. It does not need a victim to click again after the attacker already has local execution.The low attack complexity rating is particularly important. Microsoft is not saying a successful exploit requires unusual timing, rare system conditions, or a highly specific configuration. In CVSS language, low complexity means attackers can expect repeatable success against the vulnerable component once the preconditions are met. That is one reason local privilege escalation bugs become useful quickly after patches ship and reverse engineering begins.
The “privileges required: low” metric also matters more than it appears. Low privilege does not mean harmless; it means the attacker starts from a normal authorized context. In enterprise terms, that could be a compromised standard user account, a low-rights malware process, or a foothold obtained through some other vulnerability. Windows security architecture assumes that low-privileged code should remain boxed in. CVE-2026-33840 is about breaking that assumption.
The confidentiality, integrity, and availability impacts are all marked high. That is CVSS shorthand for the consequence of successful exploitation, not a promise that every exploit will perform every action. Still, the direction is clear: once the bug is exploited, the attacker’s relationship to the machine changes fundamentally.
Report Confidence Is the Quiet Metric That Deserves Attention
The user-facing phrase that often gets skipped in vulnerability write-ups is “Report Confidence.” Here it is marked confirmed. In Microsoft’s CVSS presentation, that means the vulnerability is not merely rumored or inferred from partial public research; the vendor or author has confirmed its existence, or detailed reports and functional reproduction are available.That matters because confirmed bugs have a different afterlife from speculative ones. Once a vendor ships a fix, attackers can compare old and new binaries, isolate the patched code path, and begin reconstructing the vulnerability. The more precise the advisory, the easier it is for defenders to prioritize; the same precision can also help exploit developers understand where to look.
This is the constant tension in modern vulnerability disclosure. Transparency helps administrators make sane patching decisions. It also gives the offensive ecosystem a starting map. In this case, Microsoft has named the component, the weakness class, the privilege outcome, and the exploitability expectation. That is not an exploit, but it is enough to raise the priority of the patch.
The temporal metric also says exploit code maturity is unproven. That means Microsoft did not list public exploit code at original publication. But “unproven” is not “unlikely,” and Microsoft separately assessed exploitation as more likely. The practical reading is simple: there may not be public working code today, but defenders should assume capable researchers and attackers will study the fix.
“Not Publicly Disclosed” and “Not Exploited” Are Starting Conditions, Not Comfort Blankets
Microsoft’s exploitability table says CVE-2026-33840 was not publicly disclosed and not known to be exploited at the time of original publication. That is good news, but it is narrowly good news. It means defenders are not already chasing a known zero-day campaign associated with this CVE, at least according to Microsoft’s initial advisory.But Patch Tuesday has its own strange physics. The moment the patch becomes public, the vulnerability starts moving from private knowledge into a wider technical ecosystem. Security vendors analyze it for detection logic. Administrators test it. Attackers diff it. Researchers probe it. A bug that was not publicly exploited on Tuesday morning can become far more understandable by Friday.
The “Exploitation More Likely” assessment is therefore the line administrators should circle. Microsoft uses that language when it believes exploit development is plausible enough to affect prioritization. For a local elevation-of-privilege flaw, that usually means the bug has characteristics that make it attractive as a post-compromise tool.
This is not a call to panic-patch every domain controller without testing. It is a call to avoid placing this CVE in the low-priority bucket just because it is not remote and not already exploited. The correct comparison is not between this bug and a wormable SMB disaster. The correct comparison is between this bug and every other local privilege escalation path attackers might use after the first foothold.
The Affected List Shows Microsoft’s Modern Windows Center of Gravity
The affected product list is concentrated on current Windows platforms: Windows 11 versions 24H2, 25H2, and 26H1, along with Windows Server 2025 and Server Core installation. That product spread makes this a modern estate problem rather than a legacy one. The systems at issue are exactly the ones many organizations are standardizing on or preparing to standardize on.For Windows 11 version 24H2 and 25H2, Microsoft lists both x64 and ARM64 systems. For Windows 11 version 26H1, Microsoft lists x64 and ARM64 builds as well. The fixed build numbers differ by release branch, as expected, with 24H2 moving into the 26100.84xx range, 25H2 into the 26200.84xx range, and 26H1 into the 28000.2113 build.
Windows Server 2025 is listed twice: once for the standard installation and once for Server Core. Both show required customer action, and both include security update and hotpatch update paths. That is notable because Server Core’s smaller footprint does not make it immune to every class of Windows kernel or graphical subsystem-adjacent vulnerability.
The presence of hotpatch updates for several entries also reflects Microsoft’s evolving server servicing model. Hotpatching can reduce reboot pressure, which matters in production environments, but it should not become an excuse for vague patch status. For a vulnerability like this, administrators need to know not only that a system is “managed,” but that it has reached a fixed build.
The SYSTEM Outcome Makes This a Post-Compromise Multiplier
Microsoft’s advisory answers the core operational question directly: a successful attacker could gain SYSTEM privileges. That answer is short, but it is the article. Everything else is prioritization around that consequence.SYSTEM is not just “administrator, but more.” It is the context under which much of Windows itself operates. Malware running as SYSTEM can disable or blind endpoint controls if tamper protections fail, create services, manipulate protected files, scrape credentials from memory under the right conditions, and make itself harder to remove. In incident response, discovering a transition to SYSTEM often changes the assumed blast radius.
This is why local privilege escalation vulnerabilities are so valuable in chained attacks. A phishing document may provide execution as a user. A stolen VPN credential may provide access to a workstation. A misconfigured remote management tool may provide a weak foothold. But attackers still need privilege, persistence, and movement. CVE-2026-33840 appears to serve the privilege part of that chain.
The phrase “authorized attacker” can also mislead casual readers. It does not mean an insider with legitimate administrative authority. It means the attacker already has some authorized local capability, even if that capability came from compromising a user or process. In real networks, that is not a rare precondition.
Patch Management Has to Treat Endpoint and Server Risk Differently
For Windows 11 endpoints, the main issue is exposure volume. Workstations are where users browse, open files, authenticate to cloud services, run collaboration tools, plug in devices, and encounter the internet’s daily sludge. A local elevation-of-privilege flaw on endpoints can give commodity malware and targeted intruders a way to turn an initial user-mode foothold into full device control.For Windows Server 2025, the exposure model is different. Servers may have fewer interactive users, but they also concentrate value. A compromised web application worker, scheduled task, low-privileged service account, or management session can become far more dangerous if paired with a reliable local SYSTEM escalation. Server Core reduces some surface area, but it does not erase the need to patch kernel-adjacent vulnerabilities.
Administrators should therefore resist a single fleet-wide priority label. Internet-facing servers with low-privileged workloads deserve careful attention. Developer workstations and admin workstations deserve urgency because they are privilege-rich environments. General user endpoints should be patched on the normal accelerated security cadence, especially where users have access to sensitive systems.
The bigger lesson is that patch order should follow attack paths, not just CVSS scores. A 7.8 local privilege escalation flaw on privileged access workstations may deserve faster treatment than a higher-scored issue on a well-isolated lab system. CVSS helps triage, but environment decides risk.
The Fix Is Official, but Verification Is the Real Work
Microsoft lists the remediation level as official fix, which means security updates are available. That should move the conversation from “should we patch?” to “how do we prove we are patched?” In modern Windows estates, the hard part is rarely knowing that Patch Tuesday exists. The hard part is closing the gap between update approval and actual build compliance.The affected Windows 11 24H2 systems show fixed builds in the 26100.8457 and 26100.8390 range, depending on the update path. Windows 11 25H2 systems show fixed builds in the 26200.8457 and 26200.8390 range. Windows 11 26H1 systems show build 28000.2113. Windows Server 2025 entries show 26100.32860 and 26100.32772 for the listed update paths.
That build-number detail is valuable because KB installation status can be messy. Supersedence, hotpatching, failed reboots, paused update rings, and partially remediated machines can all make dashboards look healthier than the estate really is. Build verification gives administrators a more concrete signal.
Security teams should also watch for machines outside the obvious Windows Update flow. Golden images, VDI pools, offline servers, test rings, kiosk devices, and ARM64 laptops can lag behind. The advisory explicitly includes ARM64 Windows 11 systems, which is a reminder that the Windows endpoint estate is becoming more heterogeneous.
Researcher Credit Hints at Coordinated Disclosure, Not a Fire Drill
Microsoft credits Minjea Park with Stealien and an anonymous reporter. That acknowledgement is worth noting because it suggests coordinated vulnerability disclosure rather than a public scramble. In practical terms, defenders appear to have received a patch before public exploit code was known and before Microsoft reported active exploitation.Coordinated disclosure is not glamorous, but it is the security ecosystem working as designed. A researcher finds a bug, reports it, the vendor investigates, the patch ships, and customers get enough information to act. The system is imperfect, but the alternative is usually worse: silent exploitation, public proof-of-concept drops without fixes, or vague advisories that leave defenders guessing.
Still, coordinated disclosure does not remove urgency. It merely starts the race from a better line. Once the patch exists, offensive analysis becomes easier. Microsoft’s “exploitation more likely” tag is the warning that this one may not stay academically interesting for long.
For enterprises, the right response is disciplined speed. Test the update where business risk demands it, deploy quickly to the highest-risk rings, and verify fixed builds. The worst response is to treat “not exploited” as an indefinite grace period.
The Real Lesson Is That Memory Safety Still Haunts the Windows Trust Boundary
Use-after-free bugs are not new, and Win32k elevation-of-privilege bugs are not new. That is precisely why this advisory feels familiar. The security industry has spent years talking about memory-safe languages, sandboxing, virtualization-based security, exploit mitigations, and kernel attack surface reduction. Yet old classes of memory corruption continue to produce very current patch pressure.That does not mean Windows is uniquely broken or that mitigations have failed. It means large, compatibility-heavy operating systems carry technical debt in places that matter. Win32k exists because decades of applications expect Windows to behave in certain ways. Security engineering has to harden that reality, not an idealized greenfield OS.
The “ICOMP” detail in Microsoft’s summary may mean little to most admins, but the pattern means plenty. A component deep enough to matter, reachable enough to exploit locally, and privileged enough to yield SYSTEM is exactly the kind of bug attackers want in their toolbox. When such a bug also has low complexity and confirmed report confidence, it deserves to move up the queue.
The broader Microsoft story is also about transparency. The advisory includes the CWE classification, CVSS vector, temporal scoring, exploitability assessment, affected products, fixed builds, and acknowledgements. That is useful. It lets defenders reason about risk instead of relying solely on a severity adjective.
The Patch Tuesday Signal Hidden in One Win32k Advisory
CVE-2026-33840 is a reminder that the most dangerous Patch Tuesday items are not always the most spectacular ones. A local elevation-of-privilege bug can be quiet, technical, and deeply useful to attackers. It is the exploit that comes after the exploit.The concrete takeaways are straightforward:
- Organizations should prioritize CVE-2026-33840 on Windows 11 24H2, 25H2, and 26H1 endpoints that handle privileged access, sensitive data, or high-risk user activity.
- Windows Server 2025 and Server Core systems should be verified against fixed builds rather than treated as safe because they are less interactive than desktops.
- The absence of known exploitation at publication should be balanced against Microsoft’s assessment that exploitation is more likely.
- The confirmed report confidence and use-after-free classification suggest defenders should expect researchers and attackers to study the patch closely.
- Security teams should validate update deployment through build inventory, especially where hotpatching, update rings, or deferred reboots can obscure true remediation status.
Source: MSRC Security Update Guide - Microsoft Security Response Center