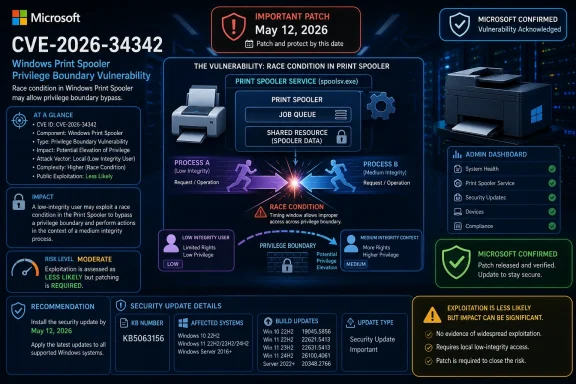
Microsoft published CVE-2026-34342 on May 12, 2026, as an Important Windows Print Spooler elevation-of-privilege vulnerability affecting supported Windows client and server releases, with fixes issued through the May security updates. The bug is not a new PrintNightmare, but it lands on the same scar tissue: a privileged Windows service with a long history of turning mundane printing infrastructure into an enterprise security problem. Microsoft says exploitation is less likely, not publicly disclosed, and not seen in the wild, yet the confirmed race condition still deserves prompt patching because it sits in a component that many administrators have learned to distrust the hard way.
The first thing to notice about CVE-2026-34342 is what it is not. It is not described as remote code execution, it is not listed as actively exploited, and it does not carry the feverish language that surrounded the PrintNightmare cycle in 2021. Microsoft rates the issue Important with a CVSS 3.1 base score of 7.0, and its own exploitability guidance says exploitation is less likely.
That will tempt some readers to mentally file it under “normal Patch Tuesday plumbing.” That would be a mistake, or at least an overcorrection. Print Spooler bugs do not need to be catastrophic on their own to matter; they matter because the service has historically sat at an awkward intersection of user convenience, legacy driver behavior, domain infrastructure, and elevated Windows privileges.
The disclosed weakness is a race condition in Windows Print Spooler components. In plain English, Microsoft is saying the vulnerable code can mishandle concurrent access to a shared resource, and an authorized local attacker may be able to use that timing mistake to raise privileges. The catch is that timing flaws are rarely as clean as marketing severity labels make them sound: they can be unreliable, environment-sensitive, and still useful once an attacker has enough patience or automation.
The more reassuring part is the privilege outcome Microsoft describes. A successful attacker could elevate from a low integrity level to a medium integrity level, not straight to SYSTEM. That distinction matters. It makes CVE-2026-34342 less dramatic than the bugs that let attackers seize the highest local privileges, but it does not make it irrelevant in a Windows estate where attackers often chain “small” privilege gains into a bigger compromise.
That matters because vulnerability triage has become polluted by half-formed intelligence. Security teams now see CVE records before exploit details, scanner alerts before operational proof, and AI-generated writeups that often outrun the underlying evidence. In that environment, a confirmed vendor advisory is not just metadata; it is a boundary marker between “we should watch this” and “we must account for this.”
But confidence also cuts the other way. A confirmed vulnerability means defenders can trust the existence of the issue, and attackers can trust that there is something real to reverse-engineer. Microsoft also credits Marcin Wiazowski working with Trend Micro’s Zero Day Initiative, which suggests the bug came through coordinated disclosure rather than public chaos. That is good news for defenders because patches arrived before public exploitation, but it also starts the clock on patch-diffing by anyone interested in reconstructing the vulnerable code path.
The Exploit Code Maturity metric is listed as Unproven. Public disclosure is “No,” exploitation is “No,” and exploitation is assessed as less likely. Those are meaningful dampeners, especially for organizations already drowning in patch volume. They are not a permission slip to ignore the update.
The modern Windows patching problem is no longer deciding whether every vulnerability is a five-alarm fire. It is deciding which non-burning vulnerabilities should still move ahead of convenience, testing inertia, and change freezes. CVE-2026-34342 belongs in that middle lane: not panic, not procrastination.
High attack complexity is often misunderstood as “safe.” It is better read as “less reliable under generic conditions.” For defenders, that distinction is important because attackers do not need a vulnerability to be universally reliable; they need it to work somewhere useful, often after profiling the target environment.
Race conditions can be maddening for both sides. The defender sees an issue that may require precise timing and environmental setup. The attacker sees an issue that might be brute-forced, looped, or paired with knowledge of how a particular fleet is configured. Automation has made “hard to exploit manually” a less comforting phrase than it used to be.
Microsoft’s FAQ says successful exploitation requires winning a race condition. That is the sentence administrators should hold in their heads when prioritizing. This is not a one-click worm candidate from the description available today, but neither is it a purely theoretical weakness. It is confirmed, patched, and sitting in a Windows service attackers have studied for years.
The consequence Microsoft lists — low integrity to medium integrity — also deserves precision. Low integrity is the sandboxed, constrained world used by mechanisms such as protected-mode application contexts; medium integrity is the normal user desktop context. Moving from low to medium can be a meaningful breakout step even if it is not a full administrative compromise.
Microsoft and administrators have spent years tightening Point and Print behavior, driver installation rules, and spooler exposure on sensitive systems. Those changes were sometimes disruptive precisely because printing had been treated as invisible infrastructure. When security finally arrived, it was experienced as broken printers, help-desk tickets, and angry business units.
CVE-2026-34342 is not a repeat of that episode, but it benefits from the same attacker economics. Print Spooler is widely present, deeply integrated, and historically privileged. Even where the service is not exposed for remote printing, it can still exist locally and still participate in privilege boundaries inside Windows.
The lesson from earlier spooler bugs is not that every new spooler CVE is existential. It is that printing is one of those Windows subsystems where operational convenience has always leaned against security. Enterprises that never finished reducing spooler exposure after 2021 are still carrying more attack surface than they probably intend.
This is why a measured response should not mean a casual one. Install the May 2026 updates, verify that the right builds landed, and revisit whether the Print Spooler should be running on machines that do not print. The best mitigation for a patched vulnerability is the patch; the best mitigation for the next spooler vulnerability is less unnecessary spooler.
That breadth should not surprise anyone. The Print Spooler is not a niche enterprise add-on; it is part of the Windows platform. A local race condition in a shared component will often fan out across many supported releases because the vulnerable logic or its descendants travel with the OS family.
For administrators, the affected-product list creates a familiar problem: the highest-value systems may not be the newest systems. A Windows Server 2025 machine may have cleaner patch management and hotpatch options, while older Server 2012-era systems may sit in the corner running line-of-business dependencies that nobody wants to touch. Those older systems are often where “Important” vulnerabilities quietly become long-lived risk.
Microsoft marks customer action as required across the listed rows. That is worth spelling out because the word “Important” sometimes causes complacency when compared with Critical. In Microsoft’s taxonomy, Important still means the vulnerability can compromise confidentiality, integrity, or availability in meaningful ways, and here the base metrics mark all three impact categories as High.
The existence of hotpatch entries for some supported server and Windows 11 releases also highlights the direction Microsoft wants enterprise updating to go. The company has been trying to make patching less disruptive, especially for server workloads where reboot windows are politically expensive. Whether hotpatching becomes common enough to change vulnerability exposure curves remains a live enterprise question.
That mental model is outdated. Modern intrusions are often built out of stages: initial access, persistence, privilege escalation, credential access, lateral movement, and impact. A bug that helps move from constrained execution into a more useful user context can be valuable even if it does not deliver administrator privileges on its own.
CVE-2026-34342’s low-to-medium integrity path makes this especially relevant to sandbox escape scenarios. A malicious document, browser-adjacent compromise, or contained application context may not be able to do everything an attacker wants. A local Windows vulnerability that helps escape a low-integrity box can become part of a larger chain, even if it never earns a flashy “critical” label by itself.
The absence of user interaction in the CVSS vector is also notable. It means that once the attacker has the required local privileges and conditions, the exploit does not depend on a second user clicking something. That is not the same as remote exploitation, but it does reduce one source of operational friction for an attacker already present on the machine.
Security teams should therefore evaluate this vulnerability less as a standalone apocalypse and more as a possible link in an intrusion chain. In 2026, that is often how Windows privilege bugs earn their keep.
For Windows 10 and Windows 11 endpoints, the update should flow through the usual monthly cumulative update process. For servers, especially print servers and multi-user systems, the change deserves normal testing because print-related updates have a long history of causing operational surprises. That does not argue for delay; it argues for testing with real printers, real drivers, and real workflows rather than assuming a lab VM tells the whole story.
Domain controllers deserve a separate look, not because this CVE is described as remotely exploitable against them, but because the Print Spooler’s presence on domain controllers has been a recurring hardening concern. Many organizations disabled the spooler on DCs after PrintNightmare and related guidance. If yours did, this is a good moment to verify that the configuration has not drifted back.
Print servers are the obvious priority within the “normal patch” bucket. They are where printing is business-critical and where spooler behavior is most exercised. A bug that requires racing a spooler operation may be more interesting on systems that actually handle printing activity than on endpoints where the service is mostly idle.
Endpoint detection teams should not expect a neat signature from the advisory alone. Race-condition exploitation can look like repeated local attempts, spooler oddities, process behavior around printing components, or nothing obvious at all. The primary control is patching, not detection heroics.
The better posture is selective service availability. Workstations that print need printing. Print servers need the spooler. Domain controllers, application servers, jump boxes, and many cloud-hosted Windows workloads often do not. The exact answer depends on environment, but the question should not be optional.
This is where least privilege becomes more than a slogan. A service cannot be exploited if it is not present, reachable, or running in the relevant context. Disabling unnecessary services is not glamorous, and it rarely produces a dashboard that executives admire, but it shrinks the future blast radius of classes of vulnerabilities that have not yet been assigned CVE numbers.
There is also a documentation angle. Many organizations made emergency spooler changes in 2021 and then let those changes become tribal knowledge. Five years later, staff turnover, OS refreshes, and new device management baselines may have erased some of that hardening. CVE-2026-34342 is a useful audit trigger precisely because it is not a crisis.
Administrators should treat the May 2026 update as the immediate fix and spooler minimization as the strategic fix. One closes this door. The other reduces the number of doors in the hallway.
On a locked-down kiosk with no sensitive data and rapid update cadence, this CVE may be background noise. On a shared workstation, terminal server, developer box, or system that handles sensitive workflows while retaining the spooler unnecessarily, it deserves more attention. On a print server, it should be patched promptly because the vulnerable component is central to the server’s purpose.
The Microsoft temporal score of 6.1 reflects the existence of an official fix and the lack of proven exploit code. That is useful for prioritization, but temporal scores age. Once patches are public, reverse-engineering begins. A vulnerability that is “less likely” on release day can become more tractable later if someone publishes analysis or proof-of-concept code.
This is the uncomfortable bargain of Patch Tuesday. Microsoft improves security by publishing fixes, but the act of publishing fixes also gives attackers a map of what changed. The only winning move for defenders is to shorten the window between publication and deployment.
The report confidence value of Confirmed should therefore matter more to patch teams than the absence of exploitation should soothe them. This is a real bug with a real fix. The rest is scheduling discipline.
Yet the advisory still leaves the operational story partially implicit. We do not get detailed root cause, exploit steps, or code-path narrative, for understandable reasons. That means administrators must infer practical risk from metadata and from the Print Spooler’s history.
This is where vendor positioning and defender interpretation diverge. Microsoft is right to avoid overselling risk when there is no public exploitation and exploitation is assessed as less likely. Defenders are also right to treat the Print Spooler as a sensitive subsystem because experience has taught them to do so.
The best reading is not cynical, but calibrated. Microsoft is not saying “drop everything.” Microsoft is saying “this is confirmed, patched, and requires customer action.” For a mature IT organization, that should be enough to move the update into the normal accelerated security lane.
The Windows ecosystem has matured past the point where every CVE needs theatrical urgency. It has not matured past the point where confirmed local privilege flaws in ubiquitous services can be safely ignored.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 The Spooler Is Still a Privilege Boundary, Even When the Score Looks Ordinary
The Spooler Is Still a Privilege Boundary, Even When the Score Looks Ordinary
The first thing to notice about CVE-2026-34342 is what it is not. It is not described as remote code execution, it is not listed as actively exploited, and it does not carry the feverish language that surrounded the PrintNightmare cycle in 2021. Microsoft rates the issue Important with a CVSS 3.1 base score of 7.0, and its own exploitability guidance says exploitation is less likely.That will tempt some readers to mentally file it under “normal Patch Tuesday plumbing.” That would be a mistake, or at least an overcorrection. Print Spooler bugs do not need to be catastrophic on their own to matter; they matter because the service has historically sat at an awkward intersection of user convenience, legacy driver behavior, domain infrastructure, and elevated Windows privileges.
The disclosed weakness is a race condition in Windows Print Spooler components. In plain English, Microsoft is saying the vulnerable code can mishandle concurrent access to a shared resource, and an authorized local attacker may be able to use that timing mistake to raise privileges. The catch is that timing flaws are rarely as clean as marketing severity labels make them sound: they can be unreliable, environment-sensitive, and still useful once an attacker has enough patience or automation.
The more reassuring part is the privilege outcome Microsoft describes. A successful attacker could elevate from a low integrity level to a medium integrity level, not straight to SYSTEM. That distinction matters. It makes CVE-2026-34342 less dramatic than the bugs that let attackers seize the highest local privileges, but it does not make it irrelevant in a Windows estate where attackers often chain “small” privilege gains into a bigger compromise.
Microsoft’s Confidence Signal Cuts Both Ways
The user-facing snippet that matters most here is not the CVSS score. It is the Report Confidence metric. Microsoft marks the vulnerability as confirmed, meaning the vendor is not merely relaying a rumor, an incomplete third-party claim, or a speculative class of behavior.That matters because vulnerability triage has become polluted by half-formed intelligence. Security teams now see CVE records before exploit details, scanner alerts before operational proof, and AI-generated writeups that often outrun the underlying evidence. In that environment, a confirmed vendor advisory is not just metadata; it is a boundary marker between “we should watch this” and “we must account for this.”
But confidence also cuts the other way. A confirmed vulnerability means defenders can trust the existence of the issue, and attackers can trust that there is something real to reverse-engineer. Microsoft also credits Marcin Wiazowski working with Trend Micro’s Zero Day Initiative, which suggests the bug came through coordinated disclosure rather than public chaos. That is good news for defenders because patches arrived before public exploitation, but it also starts the clock on patch-diffing by anyone interested in reconstructing the vulnerable code path.
The Exploit Code Maturity metric is listed as Unproven. Public disclosure is “No,” exploitation is “No,” and exploitation is assessed as less likely. Those are meaningful dampeners, especially for organizations already drowning in patch volume. They are not a permission slip to ignore the update.
The modern Windows patching problem is no longer deciding whether every vulnerability is a five-alarm fire. It is deciding which non-burning vulnerabilities should still move ahead of convenience, testing inertia, and change freezes. CVE-2026-34342 belongs in that middle lane: not panic, not procrastination.
A Race Condition Explains the High Complexity and the Lingering Risk
The CVSS vector says the attack is local, requires low privileges, needs no user interaction, and has high attack complexity. That combination tells a fairly specific story. An attacker cannot simply throw a packet at a machine from the internet and win; they need local execution or a foothold, and they need to win a timing race inside the Print Spooler behavior.High attack complexity is often misunderstood as “safe.” It is better read as “less reliable under generic conditions.” For defenders, that distinction is important because attackers do not need a vulnerability to be universally reliable; they need it to work somewhere useful, often after profiling the target environment.
Race conditions can be maddening for both sides. The defender sees an issue that may require precise timing and environmental setup. The attacker sees an issue that might be brute-forced, looped, or paired with knowledge of how a particular fleet is configured. Automation has made “hard to exploit manually” a less comforting phrase than it used to be.
Microsoft’s FAQ says successful exploitation requires winning a race condition. That is the sentence administrators should hold in their heads when prioritizing. This is not a one-click worm candidate from the description available today, but neither is it a purely theoretical weakness. It is confirmed, patched, and sitting in a Windows service attackers have studied for years.
The consequence Microsoft lists — low integrity to medium integrity — also deserves precision. Low integrity is the sandboxed, constrained world used by mechanisms such as protected-mode application contexts; medium integrity is the normal user desktop context. Moving from low to medium can be a meaningful breakout step even if it is not a full administrative compromise.
The Print Spooler’s Reputation Was Earned, Not Invented
To understand why another Print Spooler CVE gets attention, one has to remember that the service’s bad reputation is not folklore. PrintNightmare turned printer plumbing into a mainstream security story because it showed how old assumptions about printing collided with modern enterprise threat models. A feature designed to make printers usable at scale became a place where drivers, remote queues, privilege checks, and domain roles all tangled together.Microsoft and administrators have spent years tightening Point and Print behavior, driver installation rules, and spooler exposure on sensitive systems. Those changes were sometimes disruptive precisely because printing had been treated as invisible infrastructure. When security finally arrived, it was experienced as broken printers, help-desk tickets, and angry business units.
CVE-2026-34342 is not a repeat of that episode, but it benefits from the same attacker economics. Print Spooler is widely present, deeply integrated, and historically privileged. Even where the service is not exposed for remote printing, it can still exist locally and still participate in privilege boundaries inside Windows.
The lesson from earlier spooler bugs is not that every new spooler CVE is existential. It is that printing is one of those Windows subsystems where operational convenience has always leaned against security. Enterprises that never finished reducing spooler exposure after 2021 are still carrying more attack surface than they probably intend.
This is why a measured response should not mean a casual one. Install the May 2026 updates, verify that the right builds landed, and revisit whether the Print Spooler should be running on machines that do not print. The best mitigation for a patched vulnerability is the patch; the best mitigation for the next spooler vulnerability is less unnecessary spooler.
The Affected List Is Broad Because Windows Is Broad
Microsoft lists a wide range of affected and patched products, including Windows 10, Windows 11, Windows Server 2012 and 2012 R2, Windows Server 2016, Windows Server 2019, Windows Server 2022, Windows Server 2025, and newer Windows 11 version tracks. The fixes are tied to the May 12, 2026 security updates, with different KB numbers and build numbers depending on the operating system generation.That breadth should not surprise anyone. The Print Spooler is not a niche enterprise add-on; it is part of the Windows platform. A local race condition in a shared component will often fan out across many supported releases because the vulnerable logic or its descendants travel with the OS family.
For administrators, the affected-product list creates a familiar problem: the highest-value systems may not be the newest systems. A Windows Server 2025 machine may have cleaner patch management and hotpatch options, while older Server 2012-era systems may sit in the corner running line-of-business dependencies that nobody wants to touch. Those older systems are often where “Important” vulnerabilities quietly become long-lived risk.
Microsoft marks customer action as required across the listed rows. That is worth spelling out because the word “Important” sometimes causes complacency when compared with Critical. In Microsoft’s taxonomy, Important still means the vulnerability can compromise confidentiality, integrity, or availability in meaningful ways, and here the base metrics mark all three impact categories as High.
The existence of hotpatch entries for some supported server and Windows 11 releases also highlights the direction Microsoft wants enterprise updating to go. The company has been trying to make patching less disruptive, especially for server workloads where reboot windows are politically expensive. Whether hotpatching becomes common enough to change vulnerability exposure curves remains a live enterprise question.
Local Bugs Still Matter in the Post-Initial-Access World
A local elevation-of-privilege vulnerability is not usually the first step in an intrusion. The attacker already needs some form of execution or local access, even if that access is constrained. That is why network defenders sometimes underrate local bugs compared with browser, VPN, mail server, or edge appliance vulnerabilities.That mental model is outdated. Modern intrusions are often built out of stages: initial access, persistence, privilege escalation, credential access, lateral movement, and impact. A bug that helps move from constrained execution into a more useful user context can be valuable even if it does not deliver administrator privileges on its own.
CVE-2026-34342’s low-to-medium integrity path makes this especially relevant to sandbox escape scenarios. A malicious document, browser-adjacent compromise, or contained application context may not be able to do everything an attacker wants. A local Windows vulnerability that helps escape a low-integrity box can become part of a larger chain, even if it never earns a flashy “critical” label by itself.
The absence of user interaction in the CVSS vector is also notable. It means that once the attacker has the required local privileges and conditions, the exploit does not depend on a second user clicking something. That is not the same as remote exploitation, but it does reduce one source of operational friction for an attacker already present on the machine.
Security teams should therefore evaluate this vulnerability less as a standalone apocalypse and more as a possible link in an intrusion chain. In 2026, that is often how Windows privilege bugs earn their keep.
The Practical Admin Response Is Boring, Which Is a Compliment
The correct response to CVE-2026-34342 is not an emergency all-hands bridge call unless your environment has special exposure or unusual spooler dependencies. The correct response is disciplined patch management, quick validation, and selective hardening. In other words: the boring part of security that actually works.For Windows 10 and Windows 11 endpoints, the update should flow through the usual monthly cumulative update process. For servers, especially print servers and multi-user systems, the change deserves normal testing because print-related updates have a long history of causing operational surprises. That does not argue for delay; it argues for testing with real printers, real drivers, and real workflows rather than assuming a lab VM tells the whole story.
Domain controllers deserve a separate look, not because this CVE is described as remotely exploitable against them, but because the Print Spooler’s presence on domain controllers has been a recurring hardening concern. Many organizations disabled the spooler on DCs after PrintNightmare and related guidance. If yours did, this is a good moment to verify that the configuration has not drifted back.
Print servers are the obvious priority within the “normal patch” bucket. They are where printing is business-critical and where spooler behavior is most exercised. A bug that requires racing a spooler operation may be more interesting on systems that actually handle printing activity than on endpoints where the service is mostly idle.
Endpoint detection teams should not expect a neat signature from the advisory alone. Race-condition exploitation can look like repeated local attempts, spooler oddities, process behavior around printing components, or nothing obvious at all. The primary control is patching, not detection heroics.
The Bigger Fix Is Still Attack Surface Reduction
Every Print Spooler vulnerability reopens the same uncomfortable conversation: why is the service running where it is not needed? Windows defaults and enterprise image inheritance have historically left services enabled broadly because compatibility wins most internal arguments. Security teams inherit that sprawl and then get blamed when the next CVE turns it into work.The better posture is selective service availability. Workstations that print need printing. Print servers need the spooler. Domain controllers, application servers, jump boxes, and many cloud-hosted Windows workloads often do not. The exact answer depends on environment, but the question should not be optional.
This is where least privilege becomes more than a slogan. A service cannot be exploited if it is not present, reachable, or running in the relevant context. Disabling unnecessary services is not glamorous, and it rarely produces a dashboard that executives admire, but it shrinks the future blast radius of classes of vulnerabilities that have not yet been assigned CVE numbers.
There is also a documentation angle. Many organizations made emergency spooler changes in 2021 and then let those changes become tribal knowledge. Five years later, staff turnover, OS refreshes, and new device management baselines may have erased some of that hardening. CVE-2026-34342 is a useful audit trigger precisely because it is not a crisis.
Administrators should treat the May 2026 update as the immediate fix and spooler minimization as the strategic fix. One closes this door. The other reduces the number of doors in the hallway.
The Scanner Score Will Not Tell the Whole Story
Vulnerability scanners will likely present CVE-2026-34342 as a high-ish, Important Microsoft vulnerability with a CVSS 7.0 score. That is accurate but incomplete. Risk is not just score; it is score multiplied by exposure, role, compensating controls, attacker interest, and patch latency.On a locked-down kiosk with no sensitive data and rapid update cadence, this CVE may be background noise. On a shared workstation, terminal server, developer box, or system that handles sensitive workflows while retaining the spooler unnecessarily, it deserves more attention. On a print server, it should be patched promptly because the vulnerable component is central to the server’s purpose.
The Microsoft temporal score of 6.1 reflects the existence of an official fix and the lack of proven exploit code. That is useful for prioritization, but temporal scores age. Once patches are public, reverse-engineering begins. A vulnerability that is “less likely” on release day can become more tractable later if someone publishes analysis or proof-of-concept code.
This is the uncomfortable bargain of Patch Tuesday. Microsoft improves security by publishing fixes, but the act of publishing fixes also gives attackers a map of what changed. The only winning move for defenders is to shorten the window between publication and deployment.
The report confidence value of Confirmed should therefore matter more to patch teams than the absence of exploitation should soothe them. This is a real bug with a real fix. The rest is scheduling discipline.
Microsoft’s Transparency Is Better, but Still Leaves Defenders Interpreting Shadows
Microsoft’s modern Security Update Guide gives defenders more structured data than the old bulletin era ever did. CVSS vectors, CWE identifiers, exploitability assessments, affected build numbers, and acknowledgements all make triage more rational. CVE-2026-34342 benefits from that transparency: we know it is a race condition, local, high complexity, low privilege, no user interaction, and confirmed.Yet the advisory still leaves the operational story partially implicit. We do not get detailed root cause, exploit steps, or code-path narrative, for understandable reasons. That means administrators must infer practical risk from metadata and from the Print Spooler’s history.
This is where vendor positioning and defender interpretation diverge. Microsoft is right to avoid overselling risk when there is no public exploitation and exploitation is assessed as less likely. Defenders are also right to treat the Print Spooler as a sensitive subsystem because experience has taught them to do so.
The best reading is not cynical, but calibrated. Microsoft is not saying “drop everything.” Microsoft is saying “this is confirmed, patched, and requires customer action.” For a mature IT organization, that should be enough to move the update into the normal accelerated security lane.
The Windows ecosystem has matured past the point where every CVE needs theatrical urgency. It has not matured past the point where confirmed local privilege flaws in ubiquitous services can be safely ignored.
The May Spooler Patch Is a Test of Patch Discipline, Not Nerve
The concrete lesson of CVE-2026-34342 is that Microsoft’s printing subsystem remains security-relevant even when the vulnerability details sound modest. The right response is neither panic nor dismissal, but fast routine execution.- Organizations should deploy the May 12, 2026 Windows security updates to affected client and server systems through their normal managed update channels.
- Administrators should prioritize print servers, shared Windows systems, and machines where the Print Spooler is enabled despite having no business need.
- Security teams should treat Microsoft’s “Exploitation Less Likely” assessment as a prioritization input, not as a reason to defer patching indefinitely.
- Environments that disabled the Print Spooler on domain controllers or other sensitive servers after earlier spooler incidents should verify that those settings have not drifted.
- Patch validation should include real printing workflows where business operations depend on specific drivers, queues, or legacy print paths.
Source: MSRC Security Update Guide - Microsoft Security Response Center