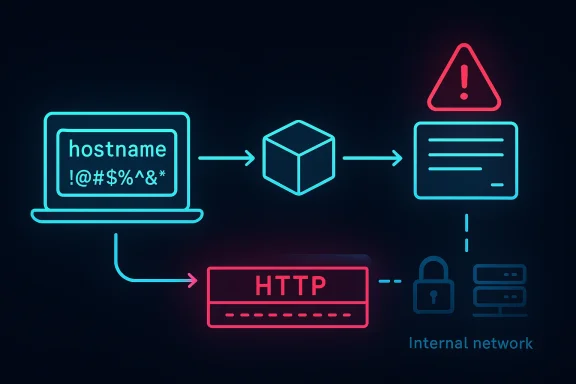
CVE-2026-3632 is one of those vulnerabilities that looks deceptively small in a vendor advisory and yet raises immediate architectural questions for anyone who ships or depends on HTTP client libraries. The flaw in libsoup centers on malformed hostnames that can inject special characters into HTTP headers, which opens the door to HTTP smuggling and, in some situations, server-side request forgery (SSRF). Microsoft’s update guide mirrors the upstream description and the NVD record ties the issue to Red Hat’s disclosure, with the current impact framed as relatively low because SoupServer is not broadly used in internet-facing infrastructure. Even so, the bug is a useful reminder that parser mistakes in foundational networking code can still become security problems far beyond their headline severity.
libsoup is a widely used C library for HTTP networking, and its role in the stack matters because libraries like this are often buried beneath desktop software, automation tools, update clients, and backend services. The current advisory text describes a flaw in hostname validation, which is exactly the sort of bug that tends to sit unnoticed until an attacker finds a way to turn an innocuous string into a protocol primitive. In practical terms, that means a hostname that should have been treated as data may instead be interpreted as part of an HTTP header, or used to reshape the request in ways the application never intended.
The key lesson here is that protocol parsing is security-sensitive, even when the affected component is not a server product in the classic sense. A library that sends requests on behalf of applications can still be an attack surface if the application passes attacker-controlled input into the request path. That is why hostname normalization, character filtering, and strict canonicalization are not cosmetic engineering choices; they are the boundary between a valid outbound request and a malformed message that may be interpreted by intermediaries in dangerous ways.
The advisory also makes an important distinction: the issue is not being presented as a mass-exploitation internet worm or a universally exploitable remote code execution bug. Instead, the likely damage depends on how the application uses libsoup and whether it accepts hostile input that can influence outbound destinations or header construction. That nuance matters because it changes the defensive posture from “patch everything immediately because a public worm is likely” to “patch quickly, but also audit how your software composes HTTP requests.”
There is also a broader ecosystem angle. Vendor triage has already linked the issue to Red Hat advisories and GNOME’s issue tracker, which suggests the bug was understood upstream and then propagated through downstream security channels as a real product risk rather than a theoretical one. In security work, that chain is often the best clue that a flaw deserves operational attention even if the apparent CVSS score is only medium or low.
That distinction helps explain the impact rating. A flaw that can rewrite headers or smuggle requests can be serious, but its exploitability often depends on request construction patterns, intermediary behavior, and whether the application trusts attacker-controlled URL or hostname fields. The attack surface is therefore narrower than a universal remote code execution flaw, but the consequences can still be substantial in the right deployment.
The description also implies that the vulnerable behavior is likely tied to how libsoup handles edge-case input during request assembly. If special characters are allowed through hostname processing, the library may inadvertently build a request that contains a header boundary or a syntax element the caller never intended. Once that happens, downstream devices may disagree on where the request begins and ends, which is exactly the environment in which smuggling thrives.
The practical danger is not just “someone can send a weird request.” It is that the weirdness may survive long enough to pass through a proxy, a gateway, or a service mesh and then be reinterpreted downstream. Once a request is normalized differently at each hop, the security model starts to fracture, because each component thinks it is seeing something valid while actually processing a different message.
That is why this kind of bug often gets more dangerous in layered environments. A single malformed input may be harmless in a direct client-to-server exchange, but when placed behind load balancers, outbound proxies, or multi-hop microservice chains, the same malformed request may become a vehicle for privilege boundary crossing. The risk is not always the initial request; it is the mismatch introduced by the infrastructure around it.
The most obvious abuse cases are internal metadata services, loopback-only endpoints, and administrative interfaces that trust local network placement as a security boundary. But SSRF does not need to hit a famous cloud metadata endpoint to be dangerous. It can also reach plain internal APIs, message brokers, local dashboards, and undocumented service ports that were never designed to survive hostile input.
This is why the true exposure of a library flaw depends on application behavior, not just library presence. A desktop client that fetches a URL chosen by the user is very different from a backend workflow that translates user input into an authenticated outbound request. The same parser bug can be low-value in one product and high-value in another.
One important detail in the record is the absence of a finalized NVD CVSS 4.0 assessment at the time of the summary, alongside a CVSS 3.1 rating that differs between NIST’s initial vector and Red Hat’s more conservative assessment. That split is common when a vulnerability’s practical exploitability depends heavily on deployment patterns, privileges, and user interaction. In plain English, the score tells you the issue exists; your architecture tells you how much it matters.
The advisory also makes clear that the issue is linked to malformed hostname handling, which narrows the remediation question. This is not a case where every HTTP request path is equally suspect. The dangerous behavior likely appears when a program assembles outbound traffic from input that can be influenced, redirected, or passed through multiple layers before being emitted.
From a risk-management perspective, the question is whether the vulnerable code can be reached by attacker-controlled strings in real workflows. If so, the vulnerability becomes a practical SSRF or smuggling issue regardless of whether the library is famous, and the operational importance grows as soon as it touches an internal network boundary. If not, the bug may remain mostly a hardening item until a future product feature makes it reachable.
This is why organizations should avoid the trap of severity by reputation. Some vulnerabilities are high-profile because they hit ubiquitous infrastructure; others are high-value because they live in a narrow but privileged path. CVE-2026-3632 looks more like the second category: limited in scope, but potentially meaningful where outbound request construction intersects with untrusted input.
The larger opportunity is to treat the CVE as a prompt to audit outbound-request code paths, not just the library itself. Many organizations have multiple services that build URLs dynamically, and a single weak normalization pattern can appear in more than one product. If the review happens now, it may close several future attack paths at once.
Another concern is that SSRF bugs are often underestimated until they are chained with other weaknesses. Even if the direct effect seems limited to outbound requests, the real-world impact can include credential abuse, internal enumeration, or interaction with services that were never meant to be externally reachable. That makes post-patch code review just as important as version upgrades.
There is also the subtle but important risk of partial remediation. If only one code path gets fixed while a nearby request-construction path still accepts malformed hostnames, attackers may simply shift to the alternate route. Library fixes help, but application-layer validation often has to move in tandem.
Next, confirm whether your vendor has already shipped a patched package or backport. Because downstream packaging can differ from upstream releases, the safest approach is to verify the exact build present in your environment rather than assuming the headline version number is enough. Treat package metadata, changelogs, and vendor advisories as the source of truth for remediation status.
Finally, review adjacent code paths for the same pattern. If one component allowed malformed hostnames into HTTP headers, there may be other places in the stack where URI parsing, redirect handling, or proxy configuration needs similar hardening. A single CVE often reveals a family resemblance in the surrounding code.
The second thing to watch is whether the issue causes broader hardening in libsoup and adjacent HTTP tooling. A hostname-validation bug often leads to stricter input normalization, stronger test coverage, and more defensive checks around header generation. In the best case, that turns a single vulnerability into a small but meaningful improvement in the library’s overall trust boundary.
The third thing to watch is whether organizations treat this as a one-off library patch or as a chance to review request-building policy across their codebase. If security teams use the event to find other places where user-controlled hostnames can influence outbound connections, the CVE may end up reducing risk well beyond the immediate fix. That is the ideal outcome: a narrow vulnerability that triggers a wider improvement in engineering discipline.
Source: NVD Security Update Guide - Microsoft Security Response Center
 Background
Background
libsoup is a widely used C library for HTTP networking, and its role in the stack matters because libraries like this are often buried beneath desktop software, automation tools, update clients, and backend services. The current advisory text describes a flaw in hostname validation, which is exactly the sort of bug that tends to sit unnoticed until an attacker finds a way to turn an innocuous string into a protocol primitive. In practical terms, that means a hostname that should have been treated as data may instead be interpreted as part of an HTTP header, or used to reshape the request in ways the application never intended.The key lesson here is that protocol parsing is security-sensitive, even when the affected component is not a server product in the classic sense. A library that sends requests on behalf of applications can still be an attack surface if the application passes attacker-controlled input into the request path. That is why hostname normalization, character filtering, and strict canonicalization are not cosmetic engineering choices; they are the boundary between a valid outbound request and a malformed message that may be interpreted by intermediaries in dangerous ways.
The advisory also makes an important distinction: the issue is not being presented as a mass-exploitation internet worm or a universally exploitable remote code execution bug. Instead, the likely damage depends on how the application uses libsoup and whether it accepts hostile input that can influence outbound destinations or header construction. That nuance matters because it changes the defensive posture from “patch everything immediately because a public worm is likely” to “patch quickly, but also audit how your software composes HTTP requests.”
There is also a broader ecosystem angle. Vendor triage has already linked the issue to Red Hat advisories and GNOME’s issue tracker, which suggests the bug was understood upstream and then propagated through downstream security channels as a real product risk rather than a theoretical one. In security work, that chain is often the best clue that a flaw deserves operational attention even if the apparent CVSS score is only medium or low.
Why hostname validation is a security boundary
Hostname parsing looks boring until it is not. A validator that accepts characters it should reject can allow crafted values to break the structure of an HTTP request, and once headers are malformed, middleboxes, proxies, and origin servers may disagree about what the request actually means. That disagreement is the essence of HTTP smuggling: different components parse the same traffic differently, which lets an attacker hide a secondary request inside the first one.Why SSRF is the downstream risk
SSRF is not the first thing most people think of when they hear “hostname bug,” but the connection is straightforward. If an attacker can influence the hostname or destination path in a library that makes outbound requests, they may be able to coerce the program into contacting internal services, metadata endpoints, or otherwise restricted systems. That is especially dangerous in cloud and enterprise environments where a single service account may have network reach that the original user never should have had.What the Vulnerability Actually Means
The published description is unusually direct: libsoup does not properly validate hostnames, allowing special characters to be injected into HTTP headers. That detail is important because it points to a classic class of input-validation failure rather than a memory corruption issue. In other words, the attacker is not necessarily crashing the process; they are changing the semantics of the request so the surrounding HTTP machinery interprets it incorrectly.That distinction helps explain the impact rating. A flaw that can rewrite headers or smuggle requests can be serious, but its exploitability often depends on request construction patterns, intermediary behavior, and whether the application trusts attacker-controlled URL or hostname fields. The attack surface is therefore narrower than a universal remote code execution flaw, but the consequences can still be substantial in the right deployment.
The description also implies that the vulnerable behavior is likely tied to how libsoup handles edge-case input during request assembly. If special characters are allowed through hostname processing, the library may inadvertently build a request that contains a header boundary or a syntax element the caller never intended. Once that happens, downstream devices may disagree on where the request begins and ends, which is exactly the environment in which smuggling thrives.
The likely attacker workflow
An attacker who can influence a URL, redirect target, or host field would try to insert characters that alter HTTP structure rather than just text content. The goal would be to make the library emit malformed headers or split the request in a way that survives validation in one layer but is interpreted differently by another. If they succeed, the “hidden” request can be directed at an internal resource or made to ride along with a legitimate transaction.Why “low impact” is not the same as “ignore it”
The advisory’s note that SoupServer is not a major internet-infrastructure component should not be read as “harmless.” It means the worst-case blast radius is probably smaller than if the bug lived in a widely deployed reverse proxy or gateway, but scope is not the same as severity. In a desktop app, automation agent, or enterprise integration service, even a limited SSRF path can leak credentials, trigger unexpected side effects, or expose internal-only endpoints.HTTP Smuggling, Explained
HTTP smuggling remains one of the most operationally frustrating classes of web vulnerabilities because it exploits disagreement between components. One device may see a single request, another may see two, and that split view allows the attacker to conceal malicious traffic, poison caches, or bypass controls that were supposed to enforce request boundaries. The libsoup issue appears to fit that pattern by letting malformed hostname data contaminate HTTP header construction.The practical danger is not just “someone can send a weird request.” It is that the weirdness may survive long enough to pass through a proxy, a gateway, or a service mesh and then be reinterpreted downstream. Once a request is normalized differently at each hop, the security model starts to fracture, because each component thinks it is seeing something valid while actually processing a different message.
That is why this kind of bug often gets more dangerous in layered environments. A single malformed input may be harmless in a direct client-to-server exchange, but when placed behind load balancers, outbound proxies, or multi-hop microservice chains, the same malformed request may become a vehicle for privilege boundary crossing. The risk is not always the initial request; it is the mismatch introduced by the infrastructure around it.
Why intermediaries matter so much
Intermediaries are where subtle parsing bugs become exploitable. If one component sanitizes or canonicalizes data in a way another component does not, the attacker can ride the gap between them. That is exactly why request-smuggling incidents are often discovered in stacks that mix libraries, reverse proxies, application frameworks, and custom middleware that all think they own the truth.What makes hostname bugs especially tricky
Hostname fields look simple, but they can appear in multiple places: URLs, redirect targets, virtual-host routing, outbound request builders, and logging paths. If a library accepts an untrusted host string and fails to normalize it strictly, the same bug can surface in more than one usage pattern. That makes remediation harder, because a fix in one code path does not guarantee every call site is safe.SSRF and Internal Network Exposure
Server-Side Request Forgery is the part of this CVE that security teams will care about most, because SSRF often turns a modest parsing issue into a pathway for credential theft, internal scanning, or data exfiltration. If libsoup is used to make requests on behalf of a user, and the application allows that user to influence the target hostname, then malformed input may be enough to redirect traffic toward services the user should never see.The most obvious abuse cases are internal metadata services, loopback-only endpoints, and administrative interfaces that trust local network placement as a security boundary. But SSRF does not need to hit a famous cloud metadata endpoint to be dangerous. It can also reach plain internal APIs, message brokers, local dashboards, and undocumented service ports that were never designed to survive hostile input.
This is why the true exposure of a library flaw depends on application behavior, not just library presence. A desktop client that fetches a URL chosen by the user is very different from a backend workflow that translates user input into an authenticated outbound request. The same parser bug can be low-value in one product and high-value in another.
Enterprise versus consumer exposure
Enterprises tend to have the larger SSRF blast radius because they frequently run software with privileged network paths, service accounts, and access to segmented internal zones. Consumers may still be affected indirectly through browsers, desktop clients, or update mechanisms that rely on embedded libraries, but the crown-jewel exposure is usually lower. That said, consumer-facing software that talks to a cloud backend can still be a pivot point if the compromised request reaches privileged infrastructure.What defenders should think about first
The first question is not “is libsoup installed?” but “can any application using libsoup turn user-controlled data into an outbound request?” If the answer is yes, then the next question is whether that request can be influenced at the hostname level, because that is the condition described in the advisory. Once that path exists, the risk moves from abstract library bug to concrete attack surface.Affected Surface and Likely Reach
The NVD entry currently lists glib libsoup in its affected configurations, and the change history shows Red Hat’s initial analysis plus references to its own advisory, a Bugzilla issue, and a GNOME issue tracker entry. That combination strongly suggests the vulnerability is being tracked as a real upstream/downstream coordination problem, not as a one-off misclassification.One important detail in the record is the absence of a finalized NVD CVSS 4.0 assessment at the time of the summary, alongside a CVSS 3.1 rating that differs between NIST’s initial vector and Red Hat’s more conservative assessment. That split is common when a vulnerability’s practical exploitability depends heavily on deployment patterns, privileges, and user interaction. In plain English, the score tells you the issue exists; your architecture tells you how much it matters.
The advisory also makes clear that the issue is linked to malformed hostname handling, which narrows the remediation question. This is not a case where every HTTP request path is equally suspect. The dangerous behavior likely appears when a program assembles outbound traffic from input that can be influenced, redirected, or passed through multiple layers before being emitted.
Why the CPE listing matters
The presence of a GNOME libsoup CPE in the NVD configuration is significant because it indicates this is not just an abstract conceptual flaw in a library interface. It is being treated as a concrete vulnerability in a named software family that downstream tooling can map to packages, advisories, and remediation workflows. For asset owners, that means vulnerability scanners should be able to flag it once their feeds catch up.Why version tracking may still be messy
Library advisories often take time to translate into package-specific fixes because downstream maintainers backport patches differently across distributions and product streams. That means organizations should not rely on the CVE title alone. They should verify the exact package build or vendor advisory, because the “fixed” state may exist under a distribution-specific patch number rather than an upstream version jump.How Serious Is It, Really?
On paper, the published severity looks moderate to low, and the description explicitly downplays the broad infrastructure impact because SoupServer is not commonly used as internet-facing server infrastructure. That is a fair assessment as far as public-facing reverse proxies and general web servers are concerned. The nuance is that many security incidents do not begin in the most obvious places; they begin in applications that inherit trust from their environment.From a risk-management perspective, the question is whether the vulnerable code can be reached by attacker-controlled strings in real workflows. If so, the vulnerability becomes a practical SSRF or smuggling issue regardless of whether the library is famous, and the operational importance grows as soon as it touches an internal network boundary. If not, the bug may remain mostly a hardening item until a future product feature makes it reachable.
This is why organizations should avoid the trap of severity by reputation. Some vulnerabilities are high-profile because they hit ubiquitous infrastructure; others are high-value because they live in a narrow but privileged path. CVE-2026-3632 looks more like the second category: limited in scope, but potentially meaningful where outbound request construction intersects with untrusted input.
The operational reality
In the real world, small library flaws can have outsized consequences when they sit inside automation, update systems, or privileged service agents. Those systems do not need to be internet-facing to matter; they only need to be trusted. Once an attacker reaches the request-generation layer, the next failure is often one of policy, not packet routing.Why security teams should still prioritize it
Even if the immediate exposure is limited, this is the kind of bug that can resurface in future code paths. A hostname validation flaw in one product often reveals a broader need to audit how the organization constructs outbound HTTP traffic. In that sense, the CVE is both a patch item and a design review trigger.Strengths and Opportunities
The good news is that this vulnerability appears to have a relatively clear fix surface. The advisory points to hostname validation and header injection, which means defenders can focus on a specific class of request-construction logic rather than a large, tangled memory-safety problem. That makes it easier to test, easier to backport, and easier to explain to application teams that need to understand why the patch matters.The larger opportunity is to treat the CVE as a prompt to audit outbound-request code paths, not just the library itself. Many organizations have multiple services that build URLs dynamically, and a single weak normalization pattern can appear in more than one product. If the review happens now, it may close several future attack paths at once.
- Clear root cause: the flaw is tied to hostname validation, not a sprawling memory-corruption chain.
- Actionable remediation: defenders can search for unsafe hostname-to-header handling patterns in application code.
- Strong downstream signal: Red Hat, GNOME, and NVD all point in the same direction, improving confidence in the issue’s reality.
- Useful security review trigger: the bug invites a broader audit of outbound HTTP request construction.
- Patchability: validation bugs are generally easier to backport than deep behavioral changes.
- Containable exposure: the advisory suggests the blast radius is limited compared with ubiquitous internet infrastructure flaws.
Why this matters for developers
Developers often assume that library-level request builders are safe as long as they accept strings that “look right.” This CVE is a reminder that looking right is not enough. If the library accepts hostile data, the validation rules must be strict enough to preserve HTTP structure all the way through the stack.Risks and Concerns
The main concern is that the vulnerability sits in a category that security tooling can misjudge. Scanner output may show a moderate score and a seemingly narrow component name, and teams may incorrectly assume the issue is not relevant to them. That is dangerous because the actual risk depends on how each application uses libsoup, especially whether it builds requests from attacker-controlled data.Another concern is that SSRF bugs are often underestimated until they are chained with other weaknesses. Even if the direct effect seems limited to outbound requests, the real-world impact can include credential abuse, internal enumeration, or interaction with services that were never meant to be externally reachable. That makes post-patch code review just as important as version upgrades.
There is also the subtle but important risk of partial remediation. If only one code path gets fixed while a nearby request-construction path still accepts malformed hostnames, attackers may simply shift to the alternate route. Library fixes help, but application-layer validation often has to move in tandem.
- Misleading severity assumptions: low or medium scores can hide meaningful SSRF risk in privileged workflows.
- Scanner blind spots: some vulnerability tools may not map embedded or transitive libsoup use accurately.
- Application-layer exposure: the bug only matters if hostnames can be influenced, but many applications fit that description.
- Infrastructure chaining: smuggling can become much worse when requests pass through proxies or service meshes.
- Partial fixes: one patched code path does not guarantee all outbound request builders are safe.
- Internal network reach: SSRF risk is amplified wherever privileged services trust local placement.
Why this can become a governance issue
Vulnerabilities like this frequently expose gaps between security policy and engineering reality. A team may believe it blocks user input from touching outbound network calls, but a second-order feature, redirect handler, or plugin may reintroduce the path. That is why governance and code review have to track the full request lifecycle, not just the obvious API entry point.What Administrators Should Do
The first step is to inventory where libsoup is actually used, not just where it is installed. If your software stack includes outbound HTTP clients, desktop integrations, or backend agents that can be driven by external input, check whether hostname values can influence request generation. That is the condition most likely to matter for this CVE.Next, confirm whether your vendor has already shipped a patched package or backport. Because downstream packaging can differ from upstream releases, the safest approach is to verify the exact build present in your environment rather than assuming the headline version number is enough. Treat package metadata, changelogs, and vendor advisories as the source of truth for remediation status.
Finally, review adjacent code paths for the same pattern. If one component allowed malformed hostnames into HTTP headers, there may be other places in the stack where URI parsing, redirect handling, or proxy configuration needs similar hardening. A single CVE often reveals a family resemblance in the surrounding code.
Practical triage steps
- Identify applications that depend on libsoup directly or transitively.
- Check whether any of those applications accept external input that affects outbound hosts or URLs.
- Verify whether your distribution or vendor has issued a fixed package build.
- Patch the affected systems and restart services so the updated library is loaded.
- Audit logs and request traces for unusual outbound destinations or malformed header behavior.
- Review application code for custom hostname or redirect normalization logic.
Where to focus first
Prioritize services that can reach internal networks, cloud metadata endpoints, or privileged APIs. Those are the environments where SSRF risk becomes the most consequential. If the affected software is purely local and does not construct outbound requests from untrusted input, the exposure is lower, but it should still be scheduled for remediation.Looking Ahead
The immediate thing to watch is how quickly downstream vendors standardize the fix across their supported builds. The NVD change history already shows the issue moving through vendor advisory channels, so the practical question is not whether it exists, but how quickly the ecosystem converges on a patched state. That matters most for long-lived enterprise systems, where patched packages often arrive through backports rather than upstream version jumps.The second thing to watch is whether the issue causes broader hardening in libsoup and adjacent HTTP tooling. A hostname-validation bug often leads to stricter input normalization, stronger test coverage, and more defensive checks around header generation. In the best case, that turns a single vulnerability into a small but meaningful improvement in the library’s overall trust boundary.
The third thing to watch is whether organizations treat this as a one-off library patch or as a chance to review request-building policy across their codebase. If security teams use the event to find other places where user-controlled hostnames can influence outbound connections, the CVE may end up reducing risk well beyond the immediate fix. That is the ideal outcome: a narrow vulnerability that triggers a wider improvement in engineering discipline.
- Vendor backports and distro-specific fix builds.
- Application updates that replace vulnerable libsoup-linked binaries.
- Code audits for hostname-to-header and redirect-handling logic.
- Proxy and middleware tests that look for request desynchronization behavior.
- SSRF-focused review of any service that can make outbound requests on behalf of users.
Source: NVD Security Update Guide - Microsoft Security Response Center
Last edited: