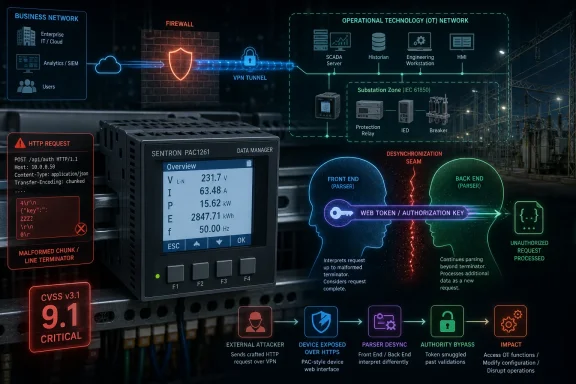
On May 14, 2026, CISA republished Siemens ProductCERT advisory SSA-783943 warning that Siemens SENTRON 7KT PAC1261 Data Manager devices before version 2.1.0 can expose authorization tokens through an HTTP request smuggling flaw in Go’s net/http package. The immediate fix is plain enough: update to version 2.1.0 or later. The more interesting story is how a language-runtime parsing bug becomes an industrial-control-system risk with a CVSS 3.1 score of 9.1. This is not another generic “patch your software” bulletin; it is a reminder that modern OT devices now inherit the same web-stack fragility as cloud applications, only with much less room for operational improvisation.
The Siemens SENTRON 7KT PAC1261 Data Manager sits in the unglamorous but important layer of energy monitoring: the place where measurements, device state, and administrative access meet. It is not a consumer router or a general-purpose Windows server, but it does expose a web server, and that is enough to pull it into the same class of problems that has plagued reverse proxies, API gateways, and backend services for years.
The vulnerability is tracked as CVE-2025-22871 and classified under CWE-444, the category for inconsistent interpretation of HTTP requests. In plainer English, two HTTP components can disagree about where one request ends and the next begins. When that happens, an attacker may be able to hide, splice, or queue a request in a way the front end and back end interpret differently.
Siemens’ advisory says the bug can allow an attacker to retrieve authorization tokens that may be used to gain administrative control over the device. That is the sentence administrators should not skim past. The issue is not merely that malformed HTTP traffic can cause confusion; it is that the confusion can cross the boundary into credential material and control of the appliance.
CISA’s republication adds the broader industrial framing. The affected sector is energy, deployments are worldwide, and the vendor headquarters are in Germany. The advisory is a direct conversion of Siemens’ CSAF advisory, which means the government notice is not adding investigative color so much as amplifying a vendor disclosure that Siemens considers serious enough to push into the ICS security ecosystem.
But HTTP request smuggling has always lived in those seams. A front-end component, proxy, load balancer, or intermediary may parse one version of the message, while the backend server parses another. If one component treats a malformed chunk boundary as legitimate and another treats it differently, the attacker can create a desynchronization that changes how requests are processed.
In a cloud application, this may be routed through a chain of CDNs, API gateways, service meshes, and backend frameworks. In an OT device, the chain may be shorter, but the consequences can be less forgiving. The vulnerable appliance may be sitting in a protected network segment, yet it still carries a web management surface that users trust for configuration, monitoring, and administrative actions.
That is why it is misleading to treat this as “just a Go vulnerability.” Siemens is not telling operators to update their Go toolchain; it is telling them to update a Data Manager firmware/software release. The embedded product is the exposure boundary, and the vendor-supplied update is the practical remediation path.
The supply-chain lesson is familiar but worth restating: when vendors build device management layers on mainstream software stacks, they inherit mainstream software defects. That is usually a good tradeoff, because mature libraries are better than bespoke parsers. But it also means industrial products are increasingly swept into the cadence of language runtime security advisories, and asset owners need processes that can absorb that cadence without treating every update as an exceptional event.
Chunked transfer encoding is designed to let a client send a request body in pieces. Each chunk is preceded by a size, and the receiving server uses those sizes to know how much data belongs to the current request. If parser A and parser B disagree over a chunk-size line, the request boundary can shift.
That boundary shift is the attack surface. A request that the front end considers harmless may be processed by the backend as something else. A later user’s request may be prefixed, delayed, or combined with attacker-controlled content. In some request-smuggling scenarios, the payoff is cache poisoning or bypassing access controls; in this Siemens advisory, the stated risk is retrieval of authorization tokens and possible administrative control.
The CVSS vector published for the issue is stark: network attack vector, low attack complexity, no privileges required, no user interaction, unchanged scope, high confidentiality impact, high integrity impact, and no availability impact. That combination explains the 9.1 critical rating. The device does not need to crash for the vulnerability to matter; in fact, a quiet token theft path is often worse than a noisy denial-of-service bug.
The absence of an availability impact should not comfort anyone responsible for an industrial environment. Availability is the sacred metric in OT, but confidentiality and integrity are how attackers get leverage before availability is touched. If administrative control is obtained, the availability question becomes a matter of what the attacker chooses to do next.
On a device-management interface, an administrative token can be a master key. It may allow configuration changes, access to device data, or changes to how the appliance communicates with other systems. Even when a token cannot directly alter downstream equipment, it can help an attacker map the environment, alter logging behavior, or stage follow-on attacks.
That is why the practical response cannot stop at installing version 2.1.0. Updating closes the known parsing flaw, but organizations should also think about token hygiene. Sessions active before patching may deserve revocation, especially if the interface was reachable from networks with broad user access or if monitoring suggests suspicious HTTP traffic.
This is where IT and OT habits often diverge. In enterprise web operations, rotating sessions after a critical auth-adjacent web flaw is normal. In OT, teams may be more cautious about changing state on a device during production hours, especially when access is tightly scheduled. The right answer is not panic-rotation of every credential at once, but neither is it “patch and forget.”
The advisory does not say exploitation has been observed in the wild, and the provided material does not include a public proof-of-concept. That matters. But exploitation status is not the same as exploitability, and a network-reachable administrative interface with a token exposure path is exactly the kind of condition defenders should treat as time-sensitive.
That convergence has been underway for years. Industrial devices gained web dashboards because browsers are universal, training costs are lower, and remote management is convenient. Vendors gained faster development cycles by using standard languages and libraries. Operators gained visibility and integration.
They also gained a larger and more familiar attack surface. The same classes of bugs that affect SaaS platforms can now sit inside devices that were historically managed through specialized software or local interfaces. Authentication tokens, browser sessions, HTTP proxies, TLS termination, API endpoints, and firmware update portals are now part of the industrial control conversation.
This is not an argument against web interfaces. It is an argument against pretending that putting a web interface on an OT device is a neutral design choice. Once a device speaks HTTP and manages administrative state, it must be governed like a web-exposed asset, even if it sits on a plant network rather than the public internet.
For WindowsForum readers, the connection is not academic. Many administrators who manage Windows estates also own the “everything else” bucket: jump hosts, monitoring appliances, power management consoles, facility systems, and vendor dashboards that live adjacent to Active Directory and enterprise remote-access tools. The Siemens advisory is the kind of issue that falls between teams unless asset ownership is explicit.
The difficulty, as always, is not reading the recommendation. It is finding the devices, proving their versions, scheduling the update, validating the update, and documenting the result. In industrial environments, even a straightforward vendor fix can become a coordination exercise across maintenance windows, site operations, safety processes, and change-control boards.
That makes inventory the first test of maturity. If a team cannot quickly answer whether it has SENTRON 7KT PAC1261 Data Manager devices, where they are, what version they run, and which network paths can reach their web interfaces, then the vulnerability has already revealed a process gap. The patch may close the CVE, but the inventory gap will remain for the next advisory.
The second test is exposure. Siemens and CISA both emphasize protecting network access to control-system devices. In practice, that means these management interfaces should not be reachable from the internet, should not be broadly reachable from business networks, and should not be casually reachable from every workstation that happens to sit inside a corporate VLAN.
The third test is remote access. VPNs are often presented as the safer path, and they usually are safer than direct exposure. But a VPN is not a magic boundary; it is an access concentrator whose security depends on its configuration, patch level, identity controls, and the health of connected endpoints. If a compromised laptop can reach the device’s web server after VPN authentication, the device is still exposed to attacker-controlled traffic.
The most important caveat is architectural. Request smuggling often depends on how multiple HTTP components interact. The Go net/http description itself refers to cases where a Go server is used with another server that incorrectly accepts a bare LF as part of a chunk extension. That means real-world exploitability may depend on the exact deployment path, intermediaries, and how the device’s web server is reached.
But defenders should be careful with that caveat. “May depend on architecture” is not a reason to defer remediation when the vendor has shipped a fixed version and the affected device can govern administrative control. It is a reason to prioritize exposure review alongside patching, not a reason to litigate whether a lab exploit exactly matches a site topology.
In enterprise environments, security teams sometimes blunt every critical advisory with contextual skepticism: not internet-facing, behind VPN, only accessible to admins, no known exploit. Those details matter for prioritization, but they can also become a ritual of delay. For an OT-adjacent device, the better question is whether the interface is reachable by any system that could plausibly be compromised.
That includes Windows admin workstations, engineering laptops, monitoring servers, remote support hosts, and jump boxes. A management web interface does not need to be on Shodan to be useful to an attacker. It only needs to be reachable after the attacker has landed somewhere else.
Siemens owns the product fix and the product-specific guidance. CISA amplifies the issue into the ICS advisory stream so operators, sector risk managers, and security teams see it in the same workflow as other industrial advisories. For asset owners, the distinction is less important than the combined effect: a vendor patch exists, the affected range is clear, and the government ICS channel now flags the issue.
There is also a subtle benefit to CSAF-style advisories becoming part of this pipeline. Machine-readable security advisories can help organizations automate detection, ticketing, and vulnerability management. But automation only works when the asset inventory can match the product identity and version data in the advisory.
That remains one of the hardest problems in industrial environments. A vulnerability scanner may not safely probe every OT segment. A configuration database may not include firmware versions. A device may be known locally by panel name, cabinet location, or operational function rather than vendor product name. The result is that a crisp CSAF advisory can still land in a foggy operational environment.
This is where Windows and infrastructure teams can help. Many organizations already have mature processes around Windows patch baselines, endpoint inventory, certificate tracking, and identity governance. Those muscles need to extend to web-managed industrial appliances, especially when those appliances participate in energy monitoring and facility operations.
Segmentation is the difference between a critical vulnerability and a critical incident. A device that can only be reached from a hardened jump host under monitored administrative workflows is a very different target from one reachable across a flat corporate network. The vulnerability is the same; the attack opportunity is not.
But segmentation can become an excuse when treated as a permanent compensating control. Firewalls drift. Temporary rules become permanent. Vendor support access expands. Remote access exceptions accumulate. A plant network that was well isolated three years ago may now have pathways created for monitoring dashboards, cloud telemetry, managed service providers, or emergency support.
That is why the Siemens fix still matters even in a well-segmented environment. Defense in depth means the firewall and the firmware are both doing their jobs. It does not mean one is allowed to fail indefinitely because the other appears intact.
The most practical approach is staged urgency. Identify whether affected devices exist. Confirm whether they run versions before 2.1.0. Restrict management access while planning the update. Apply the vendor fix during an approved maintenance window. Then review logs, sessions, and access paths as part of closure, not as an optional afterthought.
Windows infrastructure often surrounds these devices. The browser used to administer the Data Manager runs on a Windows workstation. The jump server may be Windows Server. The identity workflow may depend on Active Directory groups, privileged access workstations, RDP controls, VPN clients, endpoint detection, and logging pipelines. Even when the vulnerable code is not Microsoft’s, the access path often crosses Microsoft-managed terrain.
That makes this a shared-responsibility problem inside the enterprise. OT engineers understand operational consequences and maintenance windows. IT administrators understand endpoint compromise, remote access, identity, and network monitoring. Security teams understand advisory triage and exploit chains. None of those groups can close the loop alone.
The right internal ticket should not simply say “Siemens device vulnerable.” It should identify owners, locations, current versions, reachable networks, compensating controls, update plan, rollback considerations, and post-update validation. That may sound bureaucratic, but it is the difference between advisory handling and actual risk reduction.
There is also a monitoring angle. If web logs are available, teams should look for malformed chunked requests, unusual HTTP parsing errors, unexpected session behavior, or administrative access from unusual hosts. Many embedded devices have limited logging, but upstream firewalls, proxies, VPN concentrators, and jump hosts may still provide enough telemetry to spot suspicious access patterns.
This is not unique to Go. Similar stories have played out with OpenSSL, Java logging libraries, XML parsers, container runtimes, compression libraries, and HTTP stacks across multiple ecosystems. The modern device is an assembly of components, and component vulnerabilities become product vulnerabilities through packaging, configuration, and exposure.
The uncomfortable part for asset owners is timing. Language ecosystems can move quickly, issuing patches and advisories at software-development speed. Industrial product updates move through vendor validation and operational change windows. The gap between those clocks is where risk accumulates.
Vendors can narrow the gap by publishing clear affected-version tables, fixed releases, and operational mitigations. Siemens has done the essential part here: affected versions are all releases before V2.1.0, and the remediation is to update to V2.1.0 or later. Asset owners then have to do the part no advisory can do for them: translate that into local action.
For procurement and architecture teams, there is a longer-term implication. Buyers should ask vendors how third-party and open-source component vulnerabilities are tracked, how quickly runtime flaws are remediated, how advisories are delivered, and whether products expose management interfaces that can be disabled, restricted, or centrally logged. Those questions are no longer niche security checklist items; they are lifecycle requirements.
That includes naming the product correctly. “SENTRON 7KT PAC1261 Data Manager” is the kind of asset name that may appear in procurement records, panel documentation, engineering spreadsheets, or vendor portals, but not necessarily in an enterprise CMDB. If vulnerability management depends only on agents installed on Windows and Linux endpoints, devices like this can sit outside the map.
It also includes understanding administrative paths. A management interface that is not internet-facing may still be reachable from a general admin subnet. A contractor VPN profile may have broader access than intended. A remote support workstation may bridge business and OT networks. Those paths define whether a network-level vulnerability is theoretical or actionable.
Finally, it includes recognizing when a product update should trigger credential and session review. Because Siemens describes token retrieval as a possible consequence, defenders should consider whether administrative sessions, stored tokens, or related credentials need attention after patching. That decision should be risk-based, but it should be deliberate.
The recurring mistake in advisory response is treating the vendor fix as the only artifact. The better artifact is a closed loop: asset identified, version confirmed, exposure reduced, update applied, access reviewed, monitoring checked, and documentation updated. That is the kind of loop that makes the next advisory less chaotic.
Source: CISA Siemens SENTRON 7KT PAC1261 Data Manager | CISA
 A Power Metering Appliance Becomes a Web Security Story
A Power Metering Appliance Becomes a Web Security Story
The Siemens SENTRON 7KT PAC1261 Data Manager sits in the unglamorous but important layer of energy monitoring: the place where measurements, device state, and administrative access meet. It is not a consumer router or a general-purpose Windows server, but it does expose a web server, and that is enough to pull it into the same class of problems that has plagued reverse proxies, API gateways, and backend services for years.The vulnerability is tracked as CVE-2025-22871 and classified under CWE-444, the category for inconsistent interpretation of HTTP requests. In plainer English, two HTTP components can disagree about where one request ends and the next begins. When that happens, an attacker may be able to hide, splice, or queue a request in a way the front end and back end interpret differently.
Siemens’ advisory says the bug can allow an attacker to retrieve authorization tokens that may be used to gain administrative control over the device. That is the sentence administrators should not skim past. The issue is not merely that malformed HTTP traffic can cause confusion; it is that the confusion can cross the boundary into credential material and control of the appliance.
CISA’s republication adds the broader industrial framing. The affected sector is energy, deployments are worldwide, and the vendor headquarters are in Germany. The advisory is a direct conversion of Siemens’ CSAF advisory, which means the government notice is not adding investigative color so much as amplifying a vendor disclosure that Siemens considers serious enough to push into the ICS security ecosystem.
The Bug Is in Go, but the Exposure Is in the Product
The technical root of CVE-2025-22871 is in Go’s net/http package. Specifically, the package improperly accepted a bare line feed as a line terminator in chunked data chunk-size lines. That sounds microscopic, and in one sense it is: a difference in how a parser treats a single character during HTTP/1.1 chunked transfer parsing.But HTTP request smuggling has always lived in those seams. A front-end component, proxy, load balancer, or intermediary may parse one version of the message, while the backend server parses another. If one component treats a malformed chunk boundary as legitimate and another treats it differently, the attacker can create a desynchronization that changes how requests are processed.
In a cloud application, this may be routed through a chain of CDNs, API gateways, service meshes, and backend frameworks. In an OT device, the chain may be shorter, but the consequences can be less forgiving. The vulnerable appliance may be sitting in a protected network segment, yet it still carries a web management surface that users trust for configuration, monitoring, and administrative actions.
That is why it is misleading to treat this as “just a Go vulnerability.” Siemens is not telling operators to update their Go toolchain; it is telling them to update a Data Manager firmware/software release. The embedded product is the exposure boundary, and the vendor-supplied update is the practical remediation path.
The supply-chain lesson is familiar but worth restating: when vendors build device management layers on mainstream software stacks, they inherit mainstream software defects. That is usually a good tradeoff, because mature libraries are better than bespoke parsers. But it also means industrial products are increasingly swept into the cadence of language runtime security advisories, and asset owners need processes that can absorb that cadence without treating every update as an exceptional event.
Request Smuggling Is a Parser Argument with Operational Consequences
HTTP request smuggling is one of those vulnerability classes that sounds abstract until it is mapped onto a real workflow. The attacker is not necessarily “logging in” in the ordinary sense. Instead, they are manipulating how the server pipeline interprets the stream of bytes that make up HTTP traffic.Chunked transfer encoding is designed to let a client send a request body in pieces. Each chunk is preceded by a size, and the receiving server uses those sizes to know how much data belongs to the current request. If parser A and parser B disagree over a chunk-size line, the request boundary can shift.
That boundary shift is the attack surface. A request that the front end considers harmless may be processed by the backend as something else. A later user’s request may be prefixed, delayed, or combined with attacker-controlled content. In some request-smuggling scenarios, the payoff is cache poisoning or bypassing access controls; in this Siemens advisory, the stated risk is retrieval of authorization tokens and possible administrative control.
The CVSS vector published for the issue is stark: network attack vector, low attack complexity, no privileges required, no user interaction, unchanged scope, high confidentiality impact, high integrity impact, and no availability impact. That combination explains the 9.1 critical rating. The device does not need to crash for the vulnerability to matter; in fact, a quiet token theft path is often worse than a noisy denial-of-service bug.
The absence of an availability impact should not comfort anyone responsible for an industrial environment. Availability is the sacred metric in OT, but confidentiality and integrity are how attackers get leverage before availability is touched. If administrative control is obtained, the availability question becomes a matter of what the attacker chooses to do next.
The Admin Token Is the Real Blast Radius
The phrase “retrieve authorization tokens” deserves more attention than the CVE mechanics. Tokens are the modern web’s substitute for repeatedly presenting credentials. Once issued, they can carry authority until they expire, are revoked, or are invalidated by session logic.On a device-management interface, an administrative token can be a master key. It may allow configuration changes, access to device data, or changes to how the appliance communicates with other systems. Even when a token cannot directly alter downstream equipment, it can help an attacker map the environment, alter logging behavior, or stage follow-on attacks.
That is why the practical response cannot stop at installing version 2.1.0. Updating closes the known parsing flaw, but organizations should also think about token hygiene. Sessions active before patching may deserve revocation, especially if the interface was reachable from networks with broad user access or if monitoring suggests suspicious HTTP traffic.
This is where IT and OT habits often diverge. In enterprise web operations, rotating sessions after a critical auth-adjacent web flaw is normal. In OT, teams may be more cautious about changing state on a device during production hours, especially when access is tightly scheduled. The right answer is not panic-rotation of every credential at once, but neither is it “patch and forget.”
The advisory does not say exploitation has been observed in the wild, and the provided material does not include a public proof-of-concept. That matters. But exploitation status is not the same as exploitability, and a network-reachable administrative interface with a token exposure path is exactly the kind of condition defenders should treat as time-sensitive.
Critical Infrastructure Still Depends on Ordinary Web Plumbing
One reason this advisory stands out is that it collapses the false boundary between web application security and industrial security. The affected product is deployed in energy environments, but the vulnerable component is a web server parsing HTTP. The attacker’s conceptual toolkit is not a ladder logic exploit or a proprietary protocol decoder; it is web desynchronization.That convergence has been underway for years. Industrial devices gained web dashboards because browsers are universal, training costs are lower, and remote management is convenient. Vendors gained faster development cycles by using standard languages and libraries. Operators gained visibility and integration.
They also gained a larger and more familiar attack surface. The same classes of bugs that affect SaaS platforms can now sit inside devices that were historically managed through specialized software or local interfaces. Authentication tokens, browser sessions, HTTP proxies, TLS termination, API endpoints, and firmware update portals are now part of the industrial control conversation.
This is not an argument against web interfaces. It is an argument against pretending that putting a web interface on an OT device is a neutral design choice. Once a device speaks HTTP and manages administrative state, it must be governed like a web-exposed asset, even if it sits on a plant network rather than the public internet.
For WindowsForum readers, the connection is not academic. Many administrators who manage Windows estates also own the “everything else” bucket: jump hosts, monitoring appliances, power management consoles, facility systems, and vendor dashboards that live adjacent to Active Directory and enterprise remote-access tools. The Siemens advisory is the kind of issue that falls between teams unless asset ownership is explicit.
Version 2.1.0 Is the Simple Answer, Not the Whole Program
Siemens’ vendor fix is to update the SENTRON 7KT PAC1261 Data Manager to version 2.1.0 or later. That is the clearest and most important action. If an organization has affected devices running any version earlier than 2.1.0, the device is in the known-affected range.The difficulty, as always, is not reading the recommendation. It is finding the devices, proving their versions, scheduling the update, validating the update, and documenting the result. In industrial environments, even a straightforward vendor fix can become a coordination exercise across maintenance windows, site operations, safety processes, and change-control boards.
That makes inventory the first test of maturity. If a team cannot quickly answer whether it has SENTRON 7KT PAC1261 Data Manager devices, where they are, what version they run, and which network paths can reach their web interfaces, then the vulnerability has already revealed a process gap. The patch may close the CVE, but the inventory gap will remain for the next advisory.
The second test is exposure. Siemens and CISA both emphasize protecting network access to control-system devices. In practice, that means these management interfaces should not be reachable from the internet, should not be broadly reachable from business networks, and should not be casually reachable from every workstation that happens to sit inside a corporate VLAN.
The third test is remote access. VPNs are often presented as the safer path, and they usually are safer than direct exposure. But a VPN is not a magic boundary; it is an access concentrator whose security depends on its configuration, patch level, identity controls, and the health of connected endpoints. If a compromised laptop can reach the device’s web server after VPN authentication, the device is still exposed to attacker-controlled traffic.
The CVSS Score Is High Because the Precondition Is Common
A 9.1 CVSS score can look dramatic, especially for a flaw involving a subtle HTTP parsing edge case. But the score follows from the assumed conditions: reachable over the network, no authentication needed to trigger the vulnerable path, low complexity, and a path to high confidentiality and integrity impact. In other words, once the management interface is reachable, the vulnerability does not require an insider account or social engineering.The most important caveat is architectural. Request smuggling often depends on how multiple HTTP components interact. The Go net/http description itself refers to cases where a Go server is used with another server that incorrectly accepts a bare LF as part of a chunk extension. That means real-world exploitability may depend on the exact deployment path, intermediaries, and how the device’s web server is reached.
But defenders should be careful with that caveat. “May depend on architecture” is not a reason to defer remediation when the vendor has shipped a fixed version and the affected device can govern administrative control. It is a reason to prioritize exposure review alongside patching, not a reason to litigate whether a lab exploit exactly matches a site topology.
In enterprise environments, security teams sometimes blunt every critical advisory with contextual skepticism: not internet-facing, behind VPN, only accessible to admins, no known exploit. Those details matter for prioritization, but they can also become a ritual of delay. For an OT-adjacent device, the better question is whether the interface is reachable by any system that could plausibly be compromised.
That includes Windows admin workstations, engineering laptops, monitoring servers, remote support hosts, and jump boxes. A management web interface does not need to be on Shodan to be useful to an attacker. It only needs to be reachable after the attacker has landed somewhere else.
CISA’s Republication Is a Signal About Visibility, Not Ownership
CISA’s notice is explicitly a republication of Siemens ProductCERT’s advisory. The agency says the advisory was converted from Siemens’ CSAF content and is provided as-is for visibility. That framing matters because it tells us where the technical ownership sits.Siemens owns the product fix and the product-specific guidance. CISA amplifies the issue into the ICS advisory stream so operators, sector risk managers, and security teams see it in the same workflow as other industrial advisories. For asset owners, the distinction is less important than the combined effect: a vendor patch exists, the affected range is clear, and the government ICS channel now flags the issue.
There is also a subtle benefit to CSAF-style advisories becoming part of this pipeline. Machine-readable security advisories can help organizations automate detection, ticketing, and vulnerability management. But automation only works when the asset inventory can match the product identity and version data in the advisory.
That remains one of the hardest problems in industrial environments. A vulnerability scanner may not safely probe every OT segment. A configuration database may not include firmware versions. A device may be known locally by panel name, cabinet location, or operational function rather than vendor product name. The result is that a crisp CSAF advisory can still land in a foggy operational environment.
This is where Windows and infrastructure teams can help. Many organizations already have mature processes around Windows patch baselines, endpoint inventory, certificate tracking, and identity governance. Those muscles need to extend to web-managed industrial appliances, especially when those appliances participate in energy monitoring and facility operations.
Segmentation Is Not a Substitute for Patching
CISA’s recommended practices will sound familiar: minimize network exposure, keep control-system devices off the internet, place control networks behind firewalls, isolate them from business networks, and use secure remote-access methods when needed. None of that is novel. The fact that it must be repeated in nearly every ICS advisory is the point.Segmentation is the difference between a critical vulnerability and a critical incident. A device that can only be reached from a hardened jump host under monitored administrative workflows is a very different target from one reachable across a flat corporate network. The vulnerability is the same; the attack opportunity is not.
But segmentation can become an excuse when treated as a permanent compensating control. Firewalls drift. Temporary rules become permanent. Vendor support access expands. Remote access exceptions accumulate. A plant network that was well isolated three years ago may now have pathways created for monitoring dashboards, cloud telemetry, managed service providers, or emergency support.
That is why the Siemens fix still matters even in a well-segmented environment. Defense in depth means the firewall and the firmware are both doing their jobs. It does not mean one is allowed to fail indefinitely because the other appears intact.
The most practical approach is staged urgency. Identify whether affected devices exist. Confirm whether they run versions before 2.1.0. Restrict management access while planning the update. Apply the vendor fix during an approved maintenance window. Then review logs, sessions, and access paths as part of closure, not as an optional afterthought.
The Windows Admin’s Role Is Bigger Than the Windows Fleet
For a Windows-heavy shop, this advisory may arrive through an OT channel, a CISA feed, a Siemens contact, a vulnerability management platform, or a forwarded email from facilities. The easy reaction is to route it away: not Windows, not our patch. That is exactly how web-managed appliances become blind spots.Windows infrastructure often surrounds these devices. The browser used to administer the Data Manager runs on a Windows workstation. The jump server may be Windows Server. The identity workflow may depend on Active Directory groups, privileged access workstations, RDP controls, VPN clients, endpoint detection, and logging pipelines. Even when the vulnerable code is not Microsoft’s, the access path often crosses Microsoft-managed terrain.
That makes this a shared-responsibility problem inside the enterprise. OT engineers understand operational consequences and maintenance windows. IT administrators understand endpoint compromise, remote access, identity, and network monitoring. Security teams understand advisory triage and exploit chains. None of those groups can close the loop alone.
The right internal ticket should not simply say “Siemens device vulnerable.” It should identify owners, locations, current versions, reachable networks, compensating controls, update plan, rollback considerations, and post-update validation. That may sound bureaucratic, but it is the difference between advisory handling and actual risk reduction.
There is also a monitoring angle. If web logs are available, teams should look for malformed chunked requests, unusual HTTP parsing errors, unexpected session behavior, or administrative access from unusual hosts. Many embedded devices have limited logging, but upstream firewalls, proxies, VPN concentrators, and jump hosts may still provide enough telemetry to spot suspicious access patterns.
The Go Runtime Lesson Will Keep Repeating
Go has become a popular language for infrastructure software because it produces portable binaries, includes a capable standard library, and suits network services well. That popularity means a net/http bug can have a wide blast radius across products that do not obviously advertise themselves as Go applications. Operators may never see Go in the product UI, yet Go can still be in the management plane.This is not unique to Go. Similar stories have played out with OpenSSL, Java logging libraries, XML parsers, container runtimes, compression libraries, and HTTP stacks across multiple ecosystems. The modern device is an assembly of components, and component vulnerabilities become product vulnerabilities through packaging, configuration, and exposure.
The uncomfortable part for asset owners is timing. Language ecosystems can move quickly, issuing patches and advisories at software-development speed. Industrial product updates move through vendor validation and operational change windows. The gap between those clocks is where risk accumulates.
Vendors can narrow the gap by publishing clear affected-version tables, fixed releases, and operational mitigations. Siemens has done the essential part here: affected versions are all releases before V2.1.0, and the remediation is to update to V2.1.0 or later. Asset owners then have to do the part no advisory can do for them: translate that into local action.
For procurement and architecture teams, there is a longer-term implication. Buyers should ask vendors how third-party and open-source component vulnerabilities are tracked, how quickly runtime flaws are remediated, how advisories are delivered, and whether products expose management interfaces that can be disabled, restricted, or centrally logged. Those questions are no longer niche security checklist items; they are lifecycle requirements.
The Patch Is Small; the Governance Lesson Is Not
The concrete facts of this advisory are narrow: one Siemens product family, versions before 2.1.0, one Go net/http request-smuggling CVE, a vendor update, and standard ICS network-hardening guidance. The governance lesson is broader. Industrial security now depends on whether organizations can treat embedded web interfaces as first-class assets in vulnerability management.That includes naming the product correctly. “SENTRON 7KT PAC1261 Data Manager” is the kind of asset name that may appear in procurement records, panel documentation, engineering spreadsheets, or vendor portals, but not necessarily in an enterprise CMDB. If vulnerability management depends only on agents installed on Windows and Linux endpoints, devices like this can sit outside the map.
It also includes understanding administrative paths. A management interface that is not internet-facing may still be reachable from a general admin subnet. A contractor VPN profile may have broader access than intended. A remote support workstation may bridge business and OT networks. Those paths define whether a network-level vulnerability is theoretical or actionable.
Finally, it includes recognizing when a product update should trigger credential and session review. Because Siemens describes token retrieval as a possible consequence, defenders should consider whether administrative sessions, stored tokens, or related credentials need attention after patching. That decision should be risk-based, but it should be deliberate.
The recurring mistake in advisory response is treating the vendor fix as the only artifact. The better artifact is a closed loop: asset identified, version confirmed, exposure reduced, update applied, access reviewed, monitoring checked, and documentation updated. That is the kind of loop that makes the next advisory less chaotic.
What the Siemens 7KT PAC1261 Advisory Really Changes
This advisory is not a reason to panic, but it is a reason to move with discipline. The highest-value response is a focused sweep of affected deployments, followed by patching and access review rather than a generic blast of security theater.- Organizations running Siemens SENTRON 7KT PAC1261 Data Manager should treat every version before V2.1.0 as affected and plan an update to V2.1.0 or later.
- Teams should verify whether the device’s web interface is reachable from business networks, VPN-connected endpoints, jump hosts, or any system outside a tightly controlled management path.
- Administrators should consider session invalidation or token review after patching, especially where the management interface was broadly reachable or suspicious HTTP traffic is observed.
- Security teams should not dismiss the issue simply because it originates in Go’s net/http package; the product-level impact is administrative control of an OT-relevant device.
- Asset owners should use the advisory as a test of whether their inventory can connect vendor product names, deployed versions, physical locations, and network exposure quickly enough to support real vulnerability response.
Source: CISA Siemens SENTRON 7KT PAC1261 Data Manager | CISA