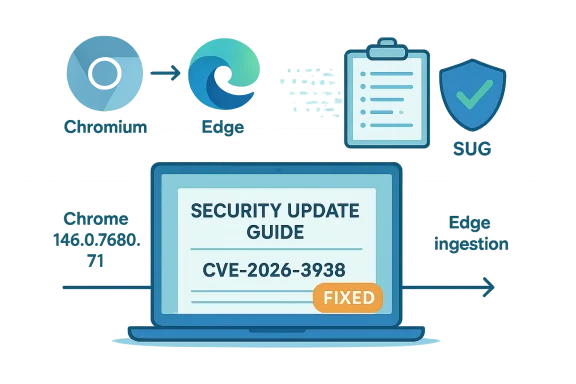
Chromium’s CVE-2026-3938 — described as an insufficient policy enforcement in Clipboard issue — is not a Microsoft-origin bug, but it appears in Microsoft’s Security Update Guide so Edge users and administrators can know exactly when Microsoft Edge (the Chromium-based browser) has absorbed the upstream Chromium/Chrome fix and is therefore no longer vulnerable. (Security Update Guide - Microsoft Security Response Center))
Chromium is an open-source browser engine that supplies the Blink renderer, V8 JavaScript engine, and a range of other subsystems used by Google Chrome and other Chromium-based browsers such as Microsoft Edge, Brave, Opera, and Vivaldi. When a security problem is discovered in Chromium (or in the Chrome shipping build), Google assigns a CVE and ships a fix in a specific Chrome release. Because Microsoft Edge is built on Chromium, Microsoft tracks those upstream CVEs and records them in the Microsoft Security Update Guide (SUG) to signal downstream status: whether Microsoft has ingested the upstrea shipped a patched Edge build.
CVE-2026-3938 was documented as an insufficient policy enforcement in Clipboard that could allow a compromised renderer process to leak cross-origin data via a crafted HTML page. Chromium’s public advisories and vulnerability databases show that the underlying fix was included in Chrome 146.0.7680.71 (and later builds). This means Chrome desktop builds at or above 146.0.7680.71 have the upstream fix applied.
That upstream fix is one half of the chain. Microsoft’s Security Update Guide entry exists to complete the story for Edge users: it documents the Chromium-origin CVE and indicates whethet Edge release has shipped the ingestion. In short, the SUG entry is Microsoft’s operational signal to Edge customers — not an admission that Microsoft authored the vulnerability. (msrc.microsoft.com)
Therefore:
Below are precise steps for desktop users and administrators.
CVE‑2026‑3938 is a textbook case of modern browser ecosystem dynamics: an upstream open-source fix, rapid public disclosure, and downstream vendor tracking to advise customers. For individuals, the fix is straightforward (update your browser). For organizations, the critical work is in mapping Chromium/Chrome fixed builds to your deployed Edge release, validating updates in a test ring, and enforcing mitigations that reduce the overall likelihood of renderer compromise in the first place.
If you need a one‑page procedural summary you can copy into a runbook or a short script to enumerate Edge versions across a fleet, I can provide that next — with concrete command examples for PowerShell, Intune/CMD-managed inventories, and a small KQL query for Microsoft Defender for Endpoint telemetry.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Chromium is an open-source browser engine that supplies the Blink renderer, V8 JavaScript engine, and a range of other subsystems used by Google Chrome and other Chromium-based browsers such as Microsoft Edge, Brave, Opera, and Vivaldi. When a security problem is discovered in Chromium (or in the Chrome shipping build), Google assigns a CVE and ships a fix in a specific Chrome release. Because Microsoft Edge is built on Chromium, Microsoft tracks those upstream CVEs and records them in the Microsoft Security Update Guide (SUG) to signal downstream status: whether Microsoft has ingested the upstrea shipped a patched Edge build.CVE-2026-3938 was documented as an insufficient policy enforcement in Clipboard that could allow a compromised renderer process to leak cross-origin data via a crafted HTML page. Chromium’s public advisories and vulnerability databases show that the underlying fix was included in Chrome 146.0.7680.71 (and later builds). This means Chrome desktop builds at or above 146.0.7680.71 have the upstream fix applied.
That upstream fix is one half of the chain. Microsoft’s Security Update Guide entry exists to complete the story for Edge users: it documents the Chromium-origin CVE and indicates whethet Edge release has shipped the ingestion. In short, the SUG entry is Microsoft’s operational signal to Edge customers — not an admission that Microsoft authored the vulnerability. (msrc.microsoft.com)
What CVE‑2026‑3938 actually is (technical summary)
- The flaw was described as insufficient policy enforcement in the Clipboard subsystem. In practice this means logic that should have prevented access to or transfer of clipboard data under certain cross-origin or permitted contexts did not fully enforce the intended policy.
- The practical impact: if an attacker had already compromised the browser renderer (the untrusted process that renders web content), the attacker could craft a page that reads or causes leakage of clipboard contents originating from a different origin — a cross-origin data leak.
- Chromium classified the issue with a low security severity for the upstream component; that reflects the required precondition (renderer compromise) and the attack surface measured by the Chromium triage team. However, low severity does not mean no risk — it means the exploit chain required additional conditions that raise the bar for successful exploitation.
Why Microsoft lists Chromium CVEs in the Security Update Guide
Microsoft’s Security Update Guide is the definitive downstream catalog for Microsoft products and the CVEs that affect them. Because Microsoft Edge (Chromium-based) is built by taking a Chromium engine snapshot and integrating platform-specific code, Microsoft cannot claim a Chromium-origin fix is present in Edge until Microsoft has merged the upstream patch, validated it, and shipped an Edge build containing the change.Therefore:
- Microsoft records Chromium-assigned CVEs in the SUG to tell Edge customers the vendor-of-origin and the downstream patching s gives administrators one place to confirm: “Has Microsoft shipped an Edge build that contains the upstream Chromium fix?” If yes, the SUG entry will indicate remediation—i.e., Edge is no longer vulnerable. If not, the SUG will show the work as pending ingestion or pending release. (msrc.microsoft.com)
How to verify whether your browser is protected (step‑by‑step)
The basic idea is to (1) find which Chrome/Chromium build fixed the CVE, and (2) confirm your browser’s version is equal or newer than the fixed Chrome/Chromium build — or confirm Microsoft’s SUG shows Edge is not vulnerable. For CVE‑2026‑3938 the upstream fix is in Chrome 146.0.7680.71. Confirm that your browser is at that Chromium revision or higher.Below are precise steps for desktop users and administrators.
1) Find the upstream fixed build (what to compare against)
- Read the official Chrome release notes or trusted CVE databases to find the Chrome build that contains the fix. For CVE‑2026‑3938, Chrome’s stable release notes and CVE registries show the fix in Chrome 146.0.7680.71.
2) Check Google Chrome (desktop)
- Open Chrome.
- In the address bar, type chrome://settings/help and press Enter, or go to the menu → Help → About Google Chrome.
- The About page displays the Chrome version (for example: Chrome 146.0.7680.71). If it is that version or later, Chrome has the upstream fix.
3) Check Microsoft Edge (desktop)
- Open Edge.
- In the address bar, type edge://settings/help and press Enter, or go to the menu → Help and feedback → About Microsoft Edge.
- The About page shows your Microsoft Edge version. For more granular information (including the underlying Chromium revision), type edge://version in the address bar; the page lists the Edge version and the Chromium revision used by that Edge build.
- Compare the Chromium revision on edge://version (or the Edge release notes entry for that build) to the fixed Chromium/Chrome build: Edge is considered protected once Microsoft documents that the Edge release has ingested the upstream change in the Security Update Guide or in its Edge release notes.
4) For managed / enterprise environments
- If Edge is managed via policies (GPO, Intune, WSUS, or other enterprise deployment mechanisms), automatic updates may be deferred. Use your software inventory or endpoint management system to read the installed Edge version string.
- If you need to map Edge build numbers to Chromium revisions at scale, consult Microsoft’s Edge release notes (the product-level release notes identify the included Chromium revision for each Edge release) or use an automated inventory script to collect edge://version output from endpoints.
- If updates are blocked, coordinate with your patch management team to schedule a targeted update that contains the ingestion.
5) Mobile and embedded variants
- Mobile browsers and embedded WebView components may have different version-number mappings. The mobile About screen will show the app version; mapping to an upstream Chromium revision is vendor-dependent and often one step removed in semantics. Always rely on the vendor advisory for mobile builds.
Practical examples: CVE‑2026‑3938 mapping and what it means for you
- Upstream fixed build: Chrome 146.0.7680.71 (Chrome stable desktop release). If your Chrome desktop shows version 146.0.7680.71 or later, Chrome is fixed.
- Microsoft Edge: because Edge gets Chromium fixes on Microsoft’s schedule, your Edge build must include the ingestion. Microsoft will list the CVE in the SUG and indicate whether the Edge release that you can install contains that ingestion. If the SUG shows “not vulnerable” for the latest Edge release, you can confirm by checking edge://version on a machine where the update has been applied.
Severity, exploitability, and real‑world risk
- Public records show Chromium rated CVE‑2026‑3938 with a low security severity in the Chromium triage. That aligns with the precondition that the renderer process must already be compromised for this clipboard policy gap to yield a cross-origin leak. Renderer compromise usually means another exploit or attack vector is already in play.
- At the time of publication, there is no authoritative public advisory stating CVE‑2026‑3938 is being exploited in the wild. However, some third‑party CVE aggregators mention the existence of a public PoC; such third‑party listings should be treated with caution and verified against primary sources before being used as the basis of operational response. If a PoC is present publicly, that raises the urgency for patching in high-security or high-risk environments because it lowers the barrier for attackers to reproduce a leak from an already-compromised renderer.
What administrators and power users should do now (recommended actions)
- Check your browser versions immediately (Edge: edge://settings/help or edge://version; Chrome: chrome://settings/help). If the version is at or above the fixed build, no further action for this CVE is necessary other than routine hygiene.
- For Edge-managed fleets: confirm the SUG entry for CVE‑2026‑3938 and the Edge release notes. If your update cadence is slower than Microsoft’s shipping cadence, prioritize deployment for high-risk endpoints.
- Harden clipboard use: where practical, reduce the risk of sensitive data being in the clipboard by using secure vaults, clearing clipboard contents after pasting, or enforcing OS-level clipboard policies where available.
- Monitor vendor advisories and telemetry: watch MSRC entries and Chrome Releases for any changes to severity, exploitability, or additional remediation guidance. Subscribe to vendor advisories if you manage many endpoints.
- Assume multi-step threats: because CVE‑2026‑3938 requires a compromised renderer to be useful, use this as a reminder to reduce attack surface elsewhere — extension whitelisting, content filtering, and exploit mitigation features (site isolation, strict sandboxing) remain critical.
- Test updates in a staging ring: before broad production rollout, validate that the updated Edge build plays nicely with site compatibility and corporate extensions, especially for managed enterprise extension policies.
How to interpret version strings and Chromium mapping (practical notes)
- Chrome/Chromium releases use semantic-like build numbers (for example, 146.0.7680.71). The important comparison is numeric: if your browser’s Chromium revision is equal to or greater than the fixed revision, you have that upstream fix.
- Microsoft Edge has its own product versioning that can differ from Google Chrome’s product number, even when the underlying Chromium revision matches. The About and version pages in Edge show both the Microsoft Edge product version and — on edge://version — the Chromium revision. Use the Chromium revision when comparing to Chrome’s CVE fixed build.
- Enterprise release channels (Stable, Beta, Dev, Canary) may have different ingestion timelines. Stable-channel Edge builds are the ones enterprise admins typically map against SUG entries.
Policy and operational context: why SUG entries matter for defenders
- The SUG is a formal traceable artifact for security teams. It documents Microsoft’s judgement on whether Edge ships a fix for an upstream CVE and provides a simple verification path for customers: check the recorded status, then check local Edge version.
- SUG entries for Chromium CVEs demonstrate supply-chain transparency: downstream vendors publicly declare the provenance and ingestion status of third‑party fixes, enabling defenders to make version-based risk decisions without having to parse upstream commit logs.
Risks and limitations you should be aware of
- A low severity rating upstream doesn’t eliminate impact in specific environments. For example, clipboard data often contains high-value secrets; exposure in a targeted environment could be consequential even if the general severity is low.
- Relying solely on automatic updates is acceptable for many consumer users, but enterprise environments with controlled update channels need explicit verification and change windows.
- Third-party CVE aggregators and automated feeds can sometimes show incomplete or inconsistent metadata (e.g., PoC availability, exploitation status). Always cross-check with primary vendor advisories (Chrome Releases, Chromium issue tracker) and authoritative CVE registries (NVD, vendor advisories).
- The presence of a CVE in the SUG does not imply Microsoft discovered it — it signifies Microsoft’s downstream tracking and remediation status. Misreading that distinction can lead to confusion in internal reporting.
Quick checklist (practical, actionable)
- Open your browser and check its About page:
- Edge: edge://settings/help or edge://version.
- Chrome: chrome://settings/help or chrome://version.
- Confirm the Chromium/Chrome build that fixed CVE‑2026‑3938: Chrome 146.0.7680.71 (or later).
- If Edge is not updated: schedule or force the update via your usual patch management process. For individual users, click About → let it download and then restart.
- For managed fleets, verify the SUG entry shows remediation for your Edge channel, then deploy to your test ring before broad rollout.
- If you’re a security admin: consider temporary mitigations (extension policy enforcement, site isolation) and monitor telemetry for unusual clipboard access patterns.
Final analysis — strengths, weaknesses, and the bigger picture
Strengths:- The Chromium/Chrome fix targets the specific policy enforcement gap; Google’s rapid release cadence means fixes appear in Chrome stable channels quickly and are publicly documented in Chrome Release notes, providing a clear upstream reference point.
- Microsoft’s practice of recording Chromium CVEs in the Security Update Guide gives Edge customers a centralized, vendor-trusted record for downstream remediation status — a useful tool for compliance and fleet management.
- The downstream ingestion model introduces an inevitable time lag: Chromium fixes appear upstream first and only later are merged, validated, and shipped by downstream browsers. That lag creates windows of vulnerability for downstream products and requires defenders to act on version information rather than CVE publication alone.
- Cross-origin clipboard leaks are subtle, and traditional vulnerability scoring (low/medium/high) can understate the impact for specific organizations where clipboard data routinely contains sensitive artifacts.
- Public PoCs — if present — can reduce the technical barrier for exploitation. Aggregators have mentioned a PoC for CVE‑2026‑3938; defenders should treat such claims carefully and verify before altering their response posture.
CVE‑2026‑3938 is a textbook case of modern browser ecosystem dynamics: an upstream open-source fix, rapid public disclosure, and downstream vendor tracking to advise customers. For individuals, the fix is straightforward (update your browser). For organizations, the critical work is in mapping Chromium/Chrome fixed builds to your deployed Edge release, validating updates in a test ring, and enforcing mitigations that reduce the overall likelihood of renderer compromise in the first place.
If you need a one‑page procedural summary you can copy into a runbook or a short script to enumerate Edge versions across a fleet, I can provide that next — with concrete command examples for PowerShell, Intune/CMD-managed inventories, and a small KQL query for Microsoft Defender for Endpoint telemetry.
Source: MSRC Security Update Guide - Microsoft Security Response Center