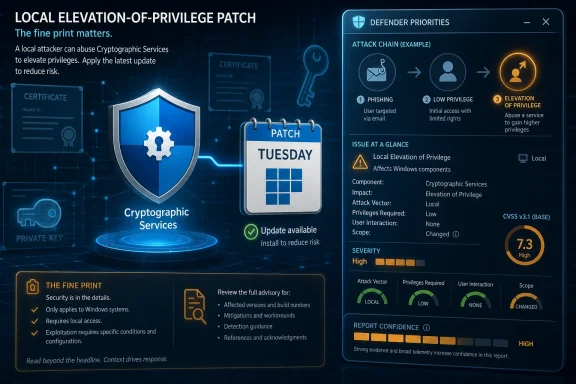
CVE-2026-40377 is a Microsoft Cryptographic Services elevation-of-privilege vulnerability listed in Microsoft’s Security Update Guide on May 12, 2026, affecting Windows systems where the vulnerable cryptographic service component is present and requiring administrators to treat the vendor entry as the authoritative patch signal. The uncomfortable part is not that Microsoft has another local privilege escalation bug; Windows has plenty of those. The uncomfortable part is that the most useful public clue in the advisory may be a scoring metric most patch dashboards flatten into noise. Report Confidence is Microsoft’s way of saying, in CVSS language, how much certainty exists behind the vulnerability’s existence and technical description — and for defenders, that can matter as much as the headline severity.
Patch Tuesday trains everyone to look for the big numbers first. Critical remote-code-execution bugs get the war-room treatment, browser flaws get the emergency change window, and local privilege-escalation vulnerabilities are too often pushed into the “next maintenance cycle” bucket unless active exploitation is confirmed.
That habit is understandable, but it is also risky. Elevation-of-privilege flaws are rarely the first door into an environment; they are the hallway key after the attacker is already inside. A phishing foothold, a stolen low-privilege account, a malicious document, or a compromised developer workstation becomes materially worse when the attacker can turn local access into administrative or SYSTEM-level control.
Cryptographic Services makes that calculus more sensitive. Windows cryptographic plumbing is not an optional niche feature sitting off to the side of the OS. It is part of the trust fabric that touches certificate handling, update validation, code-signing workflows, and a long tail of system operations that administrators would rather not debug during an incident.
That does not mean CVE-2026-40377 is automatically a domain-ending emergency. It means the component name alone should prevent complacency. When Microsoft confirms an elevation-of-privilege bug in a trust-adjacent Windows service, defenders should read past the title and into the scoring language.
That distinction matters because vulnerability management is not only about severity. It is about certainty. A vulnerability with fuzzy details and uncertain reproducibility can still deserve attention, but a vendor-confirmed vulnerability carries a different operational meaning: the affected code owner has acknowledged that the problem exists, and a fix or mitigation path is not merely speculative.
In CVSS v3.1, Report Confidence sits in the temporal metrics group. Base score describes the intrinsic characteristics of the vulnerability; temporal metrics adjust that view based on conditions that change over time, including exploit maturity, remediation status, and confidence in the report. The industry talks endlessly about base scores because they are simple to sort. Temporal signals are messier, but they are closer to how real defenders make decisions.
For CVE-2026-40377, the important lesson is not that Report Confidence magically tells us how to exploit the bug. It does not. It tells us how seriously to treat the existence and description of the bug when public technical details are limited. That is exactly the situation where administrators need a structured signal rather than vibes.
Attackers chain. They get a user context, then they seek persistence, credential material, security-tool bypass, lateral movement, and higher local rights. A reliable local privilege escalation can be the hinge between a contained endpoint incident and a broader enterprise compromise.
That is especially true on shared workstations, jump boxes, developer machines, and servers where low-privilege access is not exotic. If an attacker can execute code as a standard user and then exploit a local Windows service to gain elevated rights, the security boundary that matters to the enterprise has moved.
The public advisory title does not tell us whether CVE-2026-40377 enables SYSTEM access, administrator-equivalent control, or a narrower privilege gain. Microsoft’s scoring vector would normally give that detail through impact and privileges-required fields. But even without overclaiming, the category alone is enough to justify prompt testing and deployment in managed Windows fleets.
That is why a vulnerability in this area deserves more careful handling than a generic local utility bug. A weakness in cryptographic infrastructure does not have to “break encryption” in the Hollywood sense to be consequential. It can matter because trusted services often run with elevated privileges, process sensitive inputs, or mediate decisions about what the operating system should accept as legitimate.
Microsoft’s advisory title identifies this as an elevation-of-privilege issue, not a cryptographic break. That distinction is important. The likely administrative concern is not that attackers can decrypt everyone’s secrets with a single trick, but that a flaw in the service’s implementation or access boundaries may allow a lower-privileged actor to gain rights they should not have.
For WindowsForum readers, that should sound familiar. The Windows security model is full of privileged services exposed to lower-privileged callers through carefully designed interfaces. When those interfaces mishandle permissions, objects, paths, tokens, race conditions, or impersonation, local privilege escalation becomes possible even though the component is “just doing its job.”
The tradeoff is that defenders must act with incomplete information. A sparse advisory forces enterprises to lean on process: identify affected assets, test the cumulative update, deploy in rings, monitor for failures, and watch for later exploitation reporting. That is not satisfying, but it is the reality of Windows patch operations.
Report Confidence helps in that gap. If the vendor has acknowledged the vulnerability, defenders should not wait for a blog post, proof-of-concept, or exploit demo before treating the issue as real. By the time exploit code is public, the patch-management conversation has already moved from prevention to exposure reduction.
This is where some organizations still get the order wrong. They wait for exploit maturity to rise before they prioritize deployment, even when remediation is already available. For local privilege-escalation bugs, that can be a bad bet because exploit details often emerge after reverse engineers compare patched and unpatched binaries.
That dynamic is one reason the window after Patch Tuesday matters. A vulnerability can move from “no known public exploit” to “working proof-of-concept circulating” without the advisory title changing. Local privilege-escalation vulnerabilities are particularly attractive for this treatment because they are useful in post-compromise toolchains and often easier to weaponize once the vulnerable condition is understood.
This does not mean every EoP bug becomes a mass-exploitation event. Many require specific local conditions, timing, privileges, or configuration states. Some are too brittle to use reliably in the field. But defenders do not get to know which category CVE-2026-40377 falls into on day one unless Microsoft says so or independent researchers publish careful analysis.
That uncertainty is exactly why the patch process matters more than the drama level of the advisory. If your organization already treats Windows cumulative updates as a routine hygiene task, CVE-2026-40377 becomes one more reason to keep that machine working. If your patching process depends on public exploit panic, this is the sort of vulnerability that exposes the weakness of that model.
For enterprise workstations, the issue is more strategic. Standard-user enforcement, application control, endpoint detection, browser isolation, and credential hygiene all reduce the chance that a local privilege escalation becomes the decisive move. But none of those controls eliminate the need to patch the underlying OS flaw.
For servers, the risk depends heavily on role. A lightly exposed file server, a Remote Desktop host, a build server, a certificate-related system, or an administration jump box all carry different blast radii. The common thread is that local privilege escalation on a server can turn a modest foothold into persistence, service tampering, credential theft, or lateral movement.
Administrators should also remember that “local” does not always mean “physically at the keyboard.” Remote Desktop sessions, scheduled tasks, web shells, abused management agents, and compromised service accounts can all provide the local execution context needed to exploit a local flaw. In incident response, the attacker’s location is less important than the code execution context they have obtained.
A high base score does not always mean high environmental risk, and a moderate score does not always mean safe to defer. For CVE-2026-40377, the component and vulnerability class should be evaluated against where Cryptographic Services exists in the environment, what systems are internet-adjacent, where users have execution rights, and which endpoints are valuable stepping stones.
Temporal metrics are particularly underused. Exploit code maturity can change quickly. Remediation level changes when Microsoft ships a fix. Report Confidence changes the degree to which defenders should believe the advisory’s premise. Together, those signals help distinguish a theoretical weakness from a confirmed operational risk.
The irony is that many vulnerability scanners ingest these fields but bury them under dashboards. Security teams then spend hours arguing about whether to patch a CVSS 7.8 bug before a CVSS 8.1 bug, while ignoring whether exploit code exists, whether the affected asset is domain-joined, and whether the vendor has confirmed the issue. That is measurement theater, not risk management.
The right response is not panic. It is disciplined execution. Confirm affected Windows versions, review the corresponding cumulative update, test against representative systems, deploy according to risk tiers, and monitor authentication, service health, application compatibility, and endpoint telemetry after rollout.
The operational challenge is that Cryptographic Services can be entangled with update installation, certificate operations, and application trust behavior. If something breaks after patching, the symptom may not say “Cryptographic Services” in friendly letters. That argues for realistic pilot groups rather than blind deferral.
Enterprises with strong endpoint management should be able to move quickly here. The patch should enter normal expedited security deployment channels, especially for administrator workstations, shared systems, exposed servers, and machines used by developers or IT staff. Those systems are often where local privilege escalation has the most leverage.
But more detail also gives attackers a shorter path. A precise root-cause description can become a roadmap, particularly for local privilege-escalation bugs where the vulnerable interface is reachable by authenticated users. Microsoft’s cautious advisory style reflects that tension.
The result is an uncomfortable middle ground. Defenders have enough information to know that the vulnerability exists and that Microsoft considers it worth fixing, but not always enough to model the exploit path. That is where patch governance has to be stronger than curiosity.
The correct enterprise posture is to monitor for further technical analysis without waiting for it. If researchers later publish exploit details or Microsoft revises the advisory to indicate exploitation, the organization should already be well into deployment. Waiting for certainty about attacker behavior is not the same as using Report Confidence; it is confusing proof of exploitation with proof of vulnerability.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s Quietest Security Signal Is Often the One Admins Skip
Microsoft’s Quietest Security Signal Is Often the One Admins Skip
Patch Tuesday trains everyone to look for the big numbers first. Critical remote-code-execution bugs get the war-room treatment, browser flaws get the emergency change window, and local privilege-escalation vulnerabilities are too often pushed into the “next maintenance cycle” bucket unless active exploitation is confirmed.That habit is understandable, but it is also risky. Elevation-of-privilege flaws are rarely the first door into an environment; they are the hallway key after the attacker is already inside. A phishing foothold, a stolen low-privilege account, a malicious document, or a compromised developer workstation becomes materially worse when the attacker can turn local access into administrative or SYSTEM-level control.
Cryptographic Services makes that calculus more sensitive. Windows cryptographic plumbing is not an optional niche feature sitting off to the side of the OS. It is part of the trust fabric that touches certificate handling, update validation, code-signing workflows, and a long tail of system operations that administrators would rather not debug during an incident.
That does not mean CVE-2026-40377 is automatically a domain-ending emergency. It means the component name alone should prevent complacency. When Microsoft confirms an elevation-of-privilege bug in a trust-adjacent Windows service, defenders should read past the title and into the scoring language.
Report Confidence Turns Rumor Into Operational Weight
The text attached to the advisory’s Report Confidence metric is easy to mistake for boilerplate. It explains that the metric measures confidence in the existence of the vulnerability and the credibility of known technical details. In plain English, it asks: are we dealing with a rumor, a partially understood bug, or a vendor-confirmed flaw?That distinction matters because vulnerability management is not only about severity. It is about certainty. A vulnerability with fuzzy details and uncertain reproducibility can still deserve attention, but a vendor-confirmed vulnerability carries a different operational meaning: the affected code owner has acknowledged that the problem exists, and a fix or mitigation path is not merely speculative.
In CVSS v3.1, Report Confidence sits in the temporal metrics group. Base score describes the intrinsic characteristics of the vulnerability; temporal metrics adjust that view based on conditions that change over time, including exploit maturity, remediation status, and confidence in the report. The industry talks endlessly about base scores because they are simple to sort. Temporal signals are messier, but they are closer to how real defenders make decisions.
For CVE-2026-40377, the important lesson is not that Report Confidence magically tells us how to exploit the bug. It does not. It tells us how seriously to treat the existence and description of the bug when public technical details are limited. That is exactly the situation where administrators need a structured signal rather than vibes.
A Local Privilege Bug Is Not a Low-Impact Bug
The phrase “elevation of privilege” has become dangerously familiar. It sounds less dramatic than “remote code execution,” and in many patch queues it is treated as a second-tier category. That may be rational when viewed through a perimeter-defense lens, but modern Windows compromise rarely follows a single-stage script.Attackers chain. They get a user context, then they seek persistence, credential material, security-tool bypass, lateral movement, and higher local rights. A reliable local privilege escalation can be the hinge between a contained endpoint incident and a broader enterprise compromise.
That is especially true on shared workstations, jump boxes, developer machines, and servers where low-privilege access is not exotic. If an attacker can execute code as a standard user and then exploit a local Windows service to gain elevated rights, the security boundary that matters to the enterprise has moved.
The public advisory title does not tell us whether CVE-2026-40377 enables SYSTEM access, administrator-equivalent control, or a narrower privilege gain. Microsoft’s scoring vector would normally give that detail through impact and privileges-required fields. But even without overclaiming, the category alone is enough to justify prompt testing and deployment in managed Windows fleets.
Cryptographic Services Sits Too Close to the Trust Line
Windows Cryptographic Services is the kind of component that disappears when it works and becomes everyone’s problem when it fails. It supports operations around certificates, catalog files, cryptographic messaging, and trust verification. Administrators may not interact with it daily, but Windows does.That is why a vulnerability in this area deserves more careful handling than a generic local utility bug. A weakness in cryptographic infrastructure does not have to “break encryption” in the Hollywood sense to be consequential. It can matter because trusted services often run with elevated privileges, process sensitive inputs, or mediate decisions about what the operating system should accept as legitimate.
Microsoft’s advisory title identifies this as an elevation-of-privilege issue, not a cryptographic break. That distinction is important. The likely administrative concern is not that attackers can decrypt everyone’s secrets with a single trick, but that a flaw in the service’s implementation or access boundaries may allow a lower-privileged actor to gain rights they should not have.
For WindowsForum readers, that should sound familiar. The Windows security model is full of privileged services exposed to lower-privileged callers through carefully designed interfaces. When those interfaces mishandle permissions, objects, paths, tokens, race conditions, or impersonation, local privilege escalation becomes possible even though the component is “just doing its job.”
Microsoft’s Sparse Advisories Are a Feature and a Frustration
Microsoft’s modern Security Update Guide gives administrators standardized scoring, affected products, revision history, and exploitability signals. It is cleaner than the old bulletin era in some ways, but it also often withholds the narrative detail that sysadmins want. That is by design: too much detail too early can help attackers reverse-engineer the flaw faster.The tradeoff is that defenders must act with incomplete information. A sparse advisory forces enterprises to lean on process: identify affected assets, test the cumulative update, deploy in rings, monitor for failures, and watch for later exploitation reporting. That is not satisfying, but it is the reality of Windows patch operations.
Report Confidence helps in that gap. If the vendor has acknowledged the vulnerability, defenders should not wait for a blog post, proof-of-concept, or exploit demo before treating the issue as real. By the time exploit code is public, the patch-management conversation has already moved from prevention to exposure reduction.
This is where some organizations still get the order wrong. They wait for exploit maturity to rise before they prioritize deployment, even when remediation is already available. For local privilege-escalation bugs, that can be a bad bet because exploit details often emerge after reverse engineers compare patched and unpatched binaries.
Patch Tuesday Is Also Reverse-Engineering Tuesday
Every Windows security update is also a research artifact. Once Microsoft ships a fix, attackers and defenders alike can diff binaries, inspect changed code paths, and infer the bug class. The public advisory may remain terse, but the patch itself starts talking.That dynamic is one reason the window after Patch Tuesday matters. A vulnerability can move from “no known public exploit” to “working proof-of-concept circulating” without the advisory title changing. Local privilege-escalation vulnerabilities are particularly attractive for this treatment because they are useful in post-compromise toolchains and often easier to weaponize once the vulnerable condition is understood.
This does not mean every EoP bug becomes a mass-exploitation event. Many require specific local conditions, timing, privileges, or configuration states. Some are too brittle to use reliably in the field. But defenders do not get to know which category CVE-2026-40377 falls into on day one unless Microsoft says so or independent researchers publish careful analysis.
That uncertainty is exactly why the patch process matters more than the drama level of the advisory. If your organization already treats Windows cumulative updates as a routine hygiene task, CVE-2026-40377 becomes one more reason to keep that machine working. If your patching process depends on public exploit panic, this is the sort of vulnerability that exposes the weakness of that model.
The Risk Is Different for Consumers, Workstations, and Servers
For home users, the advice is boring but correct: install the Windows security update when offered, avoid delaying cumulative updates, and do not run untrusted software. A local elevation-of-privilege flaw usually requires the attacker to already have some execution path on the machine. That makes malware exposure, unsafe downloads, and compromised installers the practical entry points.For enterprise workstations, the issue is more strategic. Standard-user enforcement, application control, endpoint detection, browser isolation, and credential hygiene all reduce the chance that a local privilege escalation becomes the decisive move. But none of those controls eliminate the need to patch the underlying OS flaw.
For servers, the risk depends heavily on role. A lightly exposed file server, a Remote Desktop host, a build server, a certificate-related system, or an administration jump box all carry different blast radii. The common thread is that local privilege escalation on a server can turn a modest foothold into persistence, service tampering, credential theft, or lateral movement.
Administrators should also remember that “local” does not always mean “physically at the keyboard.” Remote Desktop sessions, scheduled tasks, web shells, abused management agents, and compromised service accounts can all provide the local execution context needed to exploit a local flaw. In incident response, the attacker’s location is less important than the code execution context they have obtained.
The CVSS Number Is a Starting Point, Not a Patch Queue
CVSS remains useful because it gives the industry a common language. It is far better to have structured fields for attack vector, privileges required, user interaction, impact, remediation level, and report confidence than to rely on adjectives alone. But CVSS becomes dangerous when organizations treat it as an automatic priority engine.A high base score does not always mean high environmental risk, and a moderate score does not always mean safe to defer. For CVE-2026-40377, the component and vulnerability class should be evaluated against where Cryptographic Services exists in the environment, what systems are internet-adjacent, where users have execution rights, and which endpoints are valuable stepping stones.
Temporal metrics are particularly underused. Exploit code maturity can change quickly. Remediation level changes when Microsoft ships a fix. Report Confidence changes the degree to which defenders should believe the advisory’s premise. Together, those signals help distinguish a theoretical weakness from a confirmed operational risk.
The irony is that many vulnerability scanners ingest these fields but bury them under dashboards. Security teams then spend hours arguing about whether to patch a CVSS 7.8 bug before a CVSS 8.1 bug, while ignoring whether exploit code exists, whether the affected asset is domain-joined, and whether the vendor has confirmed the issue. That is measurement theater, not risk management.
Enterprises Should Treat This as a Process Test
CVE-2026-40377 is a useful test of whether an organization’s Windows patching process is mature enough to handle ordinary, important vulnerabilities without theatrics. Not every meaningful security update arrives with a logo, a name, a leaked exploit, or a government warning. Most arrive as one line in a large Microsoft update table.The right response is not panic. It is disciplined execution. Confirm affected Windows versions, review the corresponding cumulative update, test against representative systems, deploy according to risk tiers, and monitor authentication, service health, application compatibility, and endpoint telemetry after rollout.
The operational challenge is that Cryptographic Services can be entangled with update installation, certificate operations, and application trust behavior. If something breaks after patching, the symptom may not say “Cryptographic Services” in friendly letters. That argues for realistic pilot groups rather than blind deferral.
Enterprises with strong endpoint management should be able to move quickly here. The patch should enter normal expedited security deployment channels, especially for administrator workstations, shared systems, exposed servers, and machines used by developers or IT staff. Those systems are often where local privilege escalation has the most leverage.
The Public Detail Gap Cuts Both Ways
Security vendors, researchers, and IT media often pressure Microsoft for more vulnerability detail. That pressure is justified. Better detail helps defenders understand exposure, write detections, prioritize deployment, and explain risk to leadership.But more detail also gives attackers a shorter path. A precise root-cause description can become a roadmap, particularly for local privilege-escalation bugs where the vulnerable interface is reachable by authenticated users. Microsoft’s cautious advisory style reflects that tension.
The result is an uncomfortable middle ground. Defenders have enough information to know that the vulnerability exists and that Microsoft considers it worth fixing, but not always enough to model the exploit path. That is where patch governance has to be stronger than curiosity.
The correct enterprise posture is to monitor for further technical analysis without waiting for it. If researchers later publish exploit details or Microsoft revises the advisory to indicate exploitation, the organization should already be well into deployment. Waiting for certainty about attacker behavior is not the same as using Report Confidence; it is confusing proof of exploitation with proof of vulnerability.
The Real Lesson in CVE-2026-40377 Is Hidden in the Scoring Fine Print
The most concrete reading of CVE-2026-40377 is that Microsoft has documented an elevation-of-privilege vulnerability in Windows Cryptographic Services and placed it into the structured machinery of the Security Update Guide. The most practical reading is that administrators should not let the lack of public exploit detail become an excuse for delay.- Microsoft’s advisory title identifies CVE-2026-40377 as an elevation-of-privilege vulnerability in Cryptographic Services, which makes it relevant to post-compromise risk rather than initial access alone.
- Report Confidence is a CVSS temporal metric that describes how much trust defenders should place in the vulnerability’s existence and known technical details.
- Sparse public details do not mean low risk; they often mean Microsoft is limiting information while still providing enough signal to patch.
- Local privilege escalation matters because attackers commonly chain it after phishing, malware execution, stolen credentials, or remote access abuse.
- Windows fleets should prioritize testing and deployment through normal security-update rings, with extra attention to admin workstations, shared systems, servers, and developer machines.
- Vulnerability teams should use CVSS as structured input, not as a single-number substitute for environmental risk and asset importance.
Source: MSRC Security Update Guide - Microsoft Security Response Center