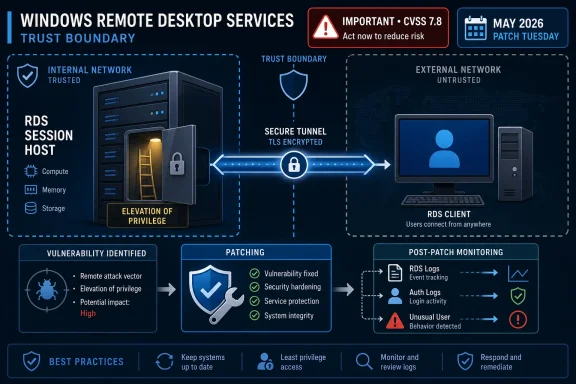
Microsoft disclosed CVE-2026-40398 on May 12, 2026, as an Important-rated Windows Remote Desktop Services elevation-of-privilege vulnerability, with no public disclosure or active exploitation reported at release time and a CVSS base score of 7.8. That combination is easy to misread: not a wormable BlueKeep sequel, not a remote-code-execution emergency, but not background noise either. The real story is that Remote Desktop remains one of Windows’ most consequential trust boundaries, and privilege escalation inside that boundary is exactly the kind of bug administrators tend to underestimate until it becomes part of an intrusion chain.
Remote Desktop Services has a branding problem in vulnerability management. Put “Remote Desktop” and “vulnerability” in the same sentence, and many administrators immediately think of exposed TCP 3389, internet scanning, credential stuffing, and the long shadow of BlueKeep. CVE-2026-40398 is not being described that way.
Microsoft’s classification is elevation of privilege, not remote code execution. That matters. An attacker would not, based on the public description, simply spray packets at an unpatched RDS host and seize control from the outside. The more plausible risk is post-access: someone who already has some foothold, session, credential, or local execution path uses the flaw to climb higher on the affected Windows system.
That makes it less theatrical but still operationally serious. Modern Windows intrusions are rarely single-bug stories. They are sequences: phishing or stolen credentials for entry, living-off-the-land tooling for movement, a local or service-specific privilege escalation for control, and then persistence or data theft. A Windows Remote Desktop Services privilege bug fits neatly into that middle act.
The “Important” label should be read in that context. It is not Microsoft saying “ignore this.” It is Microsoft saying the bug lacks the pre-authenticated, no-user, network-worm profile that pushes a vulnerability into the rarest emergency tier. For defenders, that is not permission to defer indefinitely; it is permission to prioritize rationally.
That distinction is important. A vague rumor about a possible flaw in Remote Desktop Services is one kind of risk. A vendor-confirmed CVE in the Security Update Guide is another. Even without a proof of concept, the existence of the bug is no longer speculative.
At the same time, Microsoft’s restraint leaves defenders with a familiar gap. Security teams want to know whether the flaw sits in session handling, service permissions, broker logic, device redirection, clipboard plumbing, profile loading, licensing, or another RDS component entirely. That information changes how quickly an organization can identify compensating controls, hunt for pre-patch abuse, or judge exposure in unusual deployments.
Microsoft has reasons for not handing attackers a map. But the gap does push more work onto administrators, who must infer practical risk from the surrounding metadata. In this case, the metadata says: a confirmed Windows Remote Desktop Services elevation-of-privilege flaw, Important severity, 7.8 CVSS base score, no known public disclosure, and no known exploitation at release. That is enough to act, but not enough to build a clever workaround with confidence.
That is why the “Remote Desktop Services” label needs careful interpretation. Remote Desktop is a network-facing feature, but an elevation-of-privilege issue generally assumes the attacker has already crossed some earlier boundary. In an enterprise, that earlier boundary may be depressingly mundane: a reused password, a help-desk account, an exposed jump box, a compromised contractor machine, or a low-privilege user who can log on through RDS.
For Windows Server administrators, the risk is sharper where Remote Desktop is used as a daily operations plane. Domain controllers, management servers, file servers, Remote Desktop Session Hosts, and line-of-business application servers often receive interactive administrative logons. If a low-privilege session can be converted into broader local control, the server’s role determines how bad the blast radius becomes.
For client administrators, the calculus is different but not absent. Windows Pro and Enterprise machines with Remote Desktop enabled, developer workstations, lab systems, and privileged admin workstations can all become stepping stones. The value of the bug depends less on the icon in Settings and more on who logs in, what privileges they carry, and what credentials or tokens become reachable after escalation.
Patch Tuesday is a race with a delayed starting gun. Once Microsoft publishes patches, attackers can diff binaries, inspect changed code paths, and develop exploit hypotheses. For privilege escalation bugs, that process can be especially attractive because the attack does not need to solve internet-scale reliability problems. It only needs to work after an attacker already has a toe inside the machine.
This is why “not exploited” is a status field, not a prediction. Many vulnerabilities go from obscure Patch Tuesday rows to working exploit chains only after researchers and criminals study the fix. The absence of a public exploit on May 12, 2026, is good news; it is not a durable mitigation.
That timeline matters for administrators who run staged patching. It is reasonable to test cumulative updates before wide deployment, especially on RDS-heavy infrastructure where regressions can disrupt users. But the testing window should be measured in days and deployment waves, not vague promises to circle back next month.
A Remote Desktop session is not just a screen stream. It is an authenticated, interactive Windows logon with access to devices, profiles, clipboard channels, credentials, network resources, and local services. In enterprise environments, RDS often sits next to privileged workflows even when it is not supposed to.
That is why elevation of privilege inside the RDS surface deserves more attention than a generic local privilege escalation on a random desktop component. The systems exposing RDS are often administratively valuable. The people using them often have elevated rights somewhere else. The sessions themselves can become a bridge between identity, endpoint, and server risk.
The uncomfortable truth is that many organizations still use Remote Desktop as a substitute for a mature administration model. They restrict internet exposure, perhaps place RDS behind a VPN, and assume the job is done. CVE-2026-40398 is a reminder that the internal attack surface still matters after the perimeter is narrowed.
But patching is only part of the defensive story. If Remote Desktop is enabled broadly, if ordinary users can log on to servers, if local administrator rights are scattered across endpoints, or if domain admins routinely open interactive RDP sessions to lower-trust systems, then a bug like this has more room to matter. The update closes the known flaw; hygiene determines whether the next similar flaw becomes a crisis.
Enterprises should treat this as a prompt to re-check RDS exposure. That does not mean panic-disabling Remote Desktop everywhere. It means asking whether RDS access is limited to managed networks, whether Network Level Authentication is required where appropriate, whether privileged logons are isolated, and whether session hosts are patched early enough to avoid becoming soft targets.
For smaller shops, the lesson is simpler. If Remote Desktop is enabled because it was convenient once, it should be turned off when it is no longer needed. If it must remain on, access should be restricted, accounts should be hardened with multifactor authentication where the architecture supports it, and administrators should avoid using high-value credentials on systems that do not need them.
That is how privilege bugs get buried. Security teams triage by criticality, exploitation, exposure, and business impact. That is rational. But when every month brings a long spreadsheet of CVEs, “Important, not exploited” can become shorthand for “later,” and “later” can quietly become “never.”
RDS should push this one up the queue. Not necessarily to the very top above actively exploited or unauthenticated critical bugs, but above the mass of low-context local issues that affect components with little practical exposure. Remote Desktop is too common in administrative pathways to treat as just another Windows subsystem.
The right prioritization is boring but defensible: patch internet-facing and remotely accessible infrastructure first, then RDS session hosts and management servers, then privileged workstations and general endpoints. If an organization already has exploit-based prioritization tooling, CVE-2026-40398 should be enriched with asset context rather than judged by the CVSS number alone.
Credential theft, browser exploits, malicious documents, software supply-chain compromises, help-desk social engineering, and exposed remote-access services all create low-privilege footholds. Once inside, the attacker’s next question is not philosophical. It is practical: how do I become SYSTEM, dump credentials, tamper with security tools, or pivot to a more valuable host?
That is where CVE-2026-40398 belongs in the mental model. It is not the front door. It may be the stairwell.
This framing also explains why defenders should watch for secondary signals after patching. Failed or unusual RDS logons, new local administrator membership, unexpected service creation, suspicious child processes from session-related services, and credential access activity on RDS hosts all matter more when a privilege escalation has been patched. Microsoft has not published exploit mechanics, so hunting cannot be overly specific, but the behavior around post-logon escalation is familiar enough to monitor.
For CVE-2026-40398, the confidence that the vulnerability exists is strong because the vendor has acknowledged it and issued updates. The confidence that outsiders understand the exact root cause appears lower, at least from public reporting at release. That combination favors defenders who patch quickly and frustrates attackers who need to reverse-engineer the fix.
The danger is complacency in the middle. Some administrators hear “no public exploit” and infer that the vulnerability is theoretical. It is not. Others hear “Remote Desktop” and infer BlueKeep-level urgency. That is not what Microsoft’s classification says either.
The honest reading is narrower and more useful: this is a confirmed Windows Remote Desktop Services privilege-escalation vulnerability with meaningful impact if an attacker already has the necessary access path. The less public detail exists, the more the patch itself becomes the cleanest mitigation.
That does not mean every Remote Desktop Session Host is crown-jewel infrastructure. A server delivering a published app to ordinary users has a different risk profile from a jump server used by domain admins. But both are concentration points: many users, many sessions, many tokens, and often a broader network reach than a normal endpoint.
CVE-2026-40398 should therefore trigger an inventory question. Which machines run or expose Remote Desktop Services? Which of those accept privileged users? Which are reachable from user VLANs, VPN pools, vendor networks, or the internet? Which are patched first, and which are patched only after someone complains?
If the organization cannot answer those questions, the vulnerability has already done useful work as a diagnostic. The most dangerous RDS deployment is not necessarily the one with the newest CVE. It is the one nobody owns.
For sysadmins, the important distinction is between exposure and exploitability. A vulnerability can require local or authenticated access and still be urgent on servers where many users log in. Shared RDS hosts, administrative jump boxes, and vendor-access systems deserve faster patching than a random workstation with Remote Desktop disabled.
For security teams, this CVE is another argument for pairing patch management with identity discipline. Local admin sprawl, unmanaged service accounts, and high-privilege interactive logons turn privilege-escalation vulnerabilities from isolated bugs into domain-risk accelerants. The patch closes one door, but the access model determines how many attackers ever reach the hallway.
CVE-2026-40398 is a useful test of whether an organization’s patching culture can handle nuance. It is not the biggest fire in Microsoft’s May 2026 release, and the public facts do not support treating it like a wormable emergency. But Remote Desktop is too close to the machinery of Windows administration for a confirmed privilege-escalation flaw to sit untouched, and the organizations that move calmly now will have fewer surprises when the exploit details eventually catch up with the patch.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Remote Desktop’s Scariest Bugs Are Not Always the Ones With “Remote” in the Name
Remote Desktop’s Scariest Bugs Are Not Always the Ones With “Remote” in the Name
Remote Desktop Services has a branding problem in vulnerability management. Put “Remote Desktop” and “vulnerability” in the same sentence, and many administrators immediately think of exposed TCP 3389, internet scanning, credential stuffing, and the long shadow of BlueKeep. CVE-2026-40398 is not being described that way.Microsoft’s classification is elevation of privilege, not remote code execution. That matters. An attacker would not, based on the public description, simply spray packets at an unpatched RDS host and seize control from the outside. The more plausible risk is post-access: someone who already has some foothold, session, credential, or local execution path uses the flaw to climb higher on the affected Windows system.
That makes it less theatrical but still operationally serious. Modern Windows intrusions are rarely single-bug stories. They are sequences: phishing or stolen credentials for entry, living-off-the-land tooling for movement, a local or service-specific privilege escalation for control, and then persistence or data theft. A Windows Remote Desktop Services privilege bug fits neatly into that middle act.
The “Important” label should be read in that context. It is not Microsoft saying “ignore this.” It is Microsoft saying the bug lacks the pre-authenticated, no-user, network-worm profile that pushes a vulnerability into the rarest emergency tier. For defenders, that is not permission to defer indefinitely; it is permission to prioritize rationally.
Microsoft’s Sparse Disclosure Is a Security Feature and a Patch-Planning Problem
The public page for CVE-2026-40398 gives administrators the essentials but withholds the exploit recipe. That is now the familiar shape of many Patch Tuesday entries: product, impact, severity, CVSS score, exploitation status, and remediation path, but little about the underlying bug class. The user-submitted metric description points to the key signal here: confidence in the vulnerability is high because Microsoft has acknowledged and patched it, even if the root technical details remain limited.That distinction is important. A vague rumor about a possible flaw in Remote Desktop Services is one kind of risk. A vendor-confirmed CVE in the Security Update Guide is another. Even without a proof of concept, the existence of the bug is no longer speculative.
At the same time, Microsoft’s restraint leaves defenders with a familiar gap. Security teams want to know whether the flaw sits in session handling, service permissions, broker logic, device redirection, clipboard plumbing, profile loading, licensing, or another RDS component entirely. That information changes how quickly an organization can identify compensating controls, hunt for pre-patch abuse, or judge exposure in unusual deployments.
Microsoft has reasons for not handing attackers a map. But the gap does push more work onto administrators, who must infer practical risk from the surrounding metadata. In this case, the metadata says: a confirmed Windows Remote Desktop Services elevation-of-privilege flaw, Important severity, 7.8 CVSS base score, no known public disclosure, and no known exploitation at release. That is enough to act, but not enough to build a clever workaround with confidence.
CVSS 7.8 Is the Number That Says “Local Power Move”
A 7.8 CVSS base score is a familiar shape in Windows privilege escalation bugs. It usually reflects a flaw that is not remotely exploitable from scratch but can produce high-impact compromise once an attacker can run code in the right local context. In plain English, this is the kind of vulnerability that may turn a limited user into a much more powerful one.That is why the “Remote Desktop Services” label needs careful interpretation. Remote Desktop is a network-facing feature, but an elevation-of-privilege issue generally assumes the attacker has already crossed some earlier boundary. In an enterprise, that earlier boundary may be depressingly mundane: a reused password, a help-desk account, an exposed jump box, a compromised contractor machine, or a low-privilege user who can log on through RDS.
For Windows Server administrators, the risk is sharper where Remote Desktop is used as a daily operations plane. Domain controllers, management servers, file servers, Remote Desktop Session Hosts, and line-of-business application servers often receive interactive administrative logons. If a low-privilege session can be converted into broader local control, the server’s role determines how bad the blast radius becomes.
For client administrators, the calculus is different but not absent. Windows Pro and Enterprise machines with Remote Desktop enabled, developer workstations, lab systems, and privileged admin workstations can all become stepping stones. The value of the bug depends less on the icon in Settings and more on who logs in, what privileges they carry, and what credentials or tokens become reachable after escalation.
“No Exploitation Detected” Is a Snapshot, Not a Warranty
The most comforting part of the May 12 disclosure is that CVE-2026-40398 was not listed as publicly disclosed or actively exploited at release. That should lower the temperature. It should not end the conversation.Patch Tuesday is a race with a delayed starting gun. Once Microsoft publishes patches, attackers can diff binaries, inspect changed code paths, and develop exploit hypotheses. For privilege escalation bugs, that process can be especially attractive because the attack does not need to solve internet-scale reliability problems. It only needs to work after an attacker already has a toe inside the machine.
This is why “not exploited” is a status field, not a prediction. Many vulnerabilities go from obscure Patch Tuesday rows to working exploit chains only after researchers and criminals study the fix. The absence of a public exploit on May 12, 2026, is good news; it is not a durable mitigation.
That timeline matters for administrators who run staged patching. It is reasonable to test cumulative updates before wide deployment, especially on RDS-heavy infrastructure where regressions can disrupt users. But the testing window should be measured in days and deployment waves, not vague promises to circle back next month.
RDS Is a Trust Boundary Masquerading as a Convenience Feature
Remote Desktop is often treated as plumbing. It is the thing admins use when PowerShell is inconvenient, when a vendor needs access, when a legacy app has a GUI, or when a session host delivers desktops to users. That everyday quality hides how much trust RDS concentrates.A Remote Desktop session is not just a screen stream. It is an authenticated, interactive Windows logon with access to devices, profiles, clipboard channels, credentials, network resources, and local services. In enterprise environments, RDS often sits next to privileged workflows even when it is not supposed to.
That is why elevation of privilege inside the RDS surface deserves more attention than a generic local privilege escalation on a random desktop component. The systems exposing RDS are often administratively valuable. The people using them often have elevated rights somewhere else. The sessions themselves can become a bridge between identity, endpoint, and server risk.
The uncomfortable truth is that many organizations still use Remote Desktop as a substitute for a mature administration model. They restrict internet exposure, perhaps place RDS behind a VPN, and assume the job is done. CVE-2026-40398 is a reminder that the internal attack surface still matters after the perimeter is narrowed.
The Patch Is the Fix, but Configuration Decides the Blast Radius
The primary remediation is straightforward: apply Microsoft’s May 2026 security updates for affected Windows versions. In the cumulative-update era, that means most organizations will not be hunting for a standalone RDS patch so much as validating and deploying the relevant monthly Windows update across servers and clients.But patching is only part of the defensive story. If Remote Desktop is enabled broadly, if ordinary users can log on to servers, if local administrator rights are scattered across endpoints, or if domain admins routinely open interactive RDP sessions to lower-trust systems, then a bug like this has more room to matter. The update closes the known flaw; hygiene determines whether the next similar flaw becomes a crisis.
Enterprises should treat this as a prompt to re-check RDS exposure. That does not mean panic-disabling Remote Desktop everywhere. It means asking whether RDS access is limited to managed networks, whether Network Level Authentication is required where appropriate, whether privileged logons are isolated, and whether session hosts are patched early enough to avoid becoming soft targets.
For smaller shops, the lesson is simpler. If Remote Desktop is enabled because it was convenient once, it should be turned off when it is no longer needed. If it must remain on, access should be restricted, accounts should be hardened with multifactor authentication where the architecture supports it, and administrators should avoid using high-value credentials on systems that do not need them.
Patch Tuesday’s Bigger Noise Should Not Bury This One
The May 2026 Patch Tuesday release was crowded, and CVE-2026-40398 was not the loudest entry. Microsoft’s May batch included a large set of fixes, with more dramatic items elsewhere in the Windows and Microsoft ecosystem. A pre-authentication Netlogon remote code execution flaw, for instance, naturally draws more attention than an RDS elevation-of-privilege issue.That is how privilege bugs get buried. Security teams triage by criticality, exploitation, exposure, and business impact. That is rational. But when every month brings a long spreadsheet of CVEs, “Important, not exploited” can become shorthand for “later,” and “later” can quietly become “never.”
RDS should push this one up the queue. Not necessarily to the very top above actively exploited or unauthenticated critical bugs, but above the mass of low-context local issues that affect components with little practical exposure. Remote Desktop is too common in administrative pathways to treat as just another Windows subsystem.
The right prioritization is boring but defensible: patch internet-facing and remotely accessible infrastructure first, then RDS session hosts and management servers, then privileged workstations and general endpoints. If an organization already has exploit-based prioritization tooling, CVE-2026-40398 should be enriched with asset context rather than judged by the CVSS number alone.
The Exploit Chain Is the Real Unit of Risk
One reason elevation-of-privilege bugs are chronically underrated is that they sound incomplete. “The attacker needs local access” is often presented as though it ends the threat model. In reality, local access is frequently the starting point attackers already have.Credential theft, browser exploits, malicious documents, software supply-chain compromises, help-desk social engineering, and exposed remote-access services all create low-privilege footholds. Once inside, the attacker’s next question is not philosophical. It is practical: how do I become SYSTEM, dump credentials, tamper with security tools, or pivot to a more valuable host?
That is where CVE-2026-40398 belongs in the mental model. It is not the front door. It may be the stairwell.
This framing also explains why defenders should watch for secondary signals after patching. Failed or unusual RDS logons, new local administrator membership, unexpected service creation, suspicious child processes from session-related services, and credential access activity on RDS hosts all matter more when a privilege escalation has been patched. Microsoft has not published exploit mechanics, so hunting cannot be overly specific, but the behavior around post-logon escalation is familiar enough to monitor.
The Confidence Metric Cuts Both Ways
The supplied description of the confidence metric is more than CVSS trivia. It captures a tension in vulnerability response: the more certain the existence of a flaw, and the more credible the technical details, the more urgency defenders should attach. But more available detail also helps attackers.For CVE-2026-40398, the confidence that the vulnerability exists is strong because the vendor has acknowledged it and issued updates. The confidence that outsiders understand the exact root cause appears lower, at least from public reporting at release. That combination favors defenders who patch quickly and frustrates attackers who need to reverse-engineer the fix.
The danger is complacency in the middle. Some administrators hear “no public exploit” and infer that the vulnerability is theoretical. It is not. Others hear “Remote Desktop” and infer BlueKeep-level urgency. That is not what Microsoft’s classification says either.
The honest reading is narrower and more useful: this is a confirmed Windows Remote Desktop Services privilege-escalation vulnerability with meaningful impact if an attacker already has the necessary access path. The less public detail exists, the more the patch itself becomes the cleanest mitigation.
Administrators Should Treat RDS Hosts as Tier-Zero Adjacent
In Microsoft-heavy environments, tiering models often focus on domain controllers, identity systems, certificate authorities, virtualization hosts, backup infrastructure, and privileged access workstations. RDS servers do not always get the same treatment. They should at least be considered adjacent to that tier when they host administrative sessions.That does not mean every Remote Desktop Session Host is crown-jewel infrastructure. A server delivering a published app to ordinary users has a different risk profile from a jump server used by domain admins. But both are concentration points: many users, many sessions, many tokens, and often a broader network reach than a normal endpoint.
CVE-2026-40398 should therefore trigger an inventory question. Which machines run or expose Remote Desktop Services? Which of those accept privileged users? Which are reachable from user VLANs, VPN pools, vendor networks, or the internet? Which are patched first, and which are patched only after someone complains?
If the organization cannot answer those questions, the vulnerability has already done useful work as a diagnostic. The most dangerous RDS deployment is not necessarily the one with the newest CVE. It is the one nobody owns.
The Practical Reading for WindowsForum Readers
For home lab users, enthusiasts, and small-business admins, CVE-2026-40398 is not a reason to unplug every Windows machine. It is a reason to stop treating Remote Desktop as harmless just because it sits behind a password. If RDP is exposed directly to the internet, that remains a bad idea independent of this CVE.For sysadmins, the important distinction is between exposure and exploitability. A vulnerability can require local or authenticated access and still be urgent on servers where many users log in. Shared RDS hosts, administrative jump boxes, and vendor-access systems deserve faster patching than a random workstation with Remote Desktop disabled.
For security teams, this CVE is another argument for pairing patch management with identity discipline. Local admin sprawl, unmanaged service accounts, and high-privilege interactive logons turn privilege-escalation vulnerabilities from isolated bugs into domain-risk accelerants. The patch closes one door, but the access model determines how many attackers ever reach the hallway.
The May RDS Fix Belongs in the First Real Patch Wave
CVE-2026-40398 does not demand theatrical emergency messaging, but it does deserve a concrete deployment plan. The best response is neither panic nor indifference; it is fast, boring execution.- Organizations should deploy the May 2026 Windows security updates to affected systems after normal compatibility testing, with RDS servers and administrative jump hosts near the front of the queue.
- Administrators should verify whether Remote Desktop is enabled only where it is needed and reachable only from approved networks or access brokers.
- Teams should avoid using high-value administrative credentials in ordinary RDP sessions on lower-trust systems.
- Security monitoring should pay attention to unusual RDS logons, privilege changes, new services, and suspicious post-logon behavior on systems awaiting patches.
- Asset owners should treat shared RDS hosts and jump servers as privileged infrastructure, not as generic Windows servers.
CVE-2026-40398 is a useful test of whether an organization’s patching culture can handle nuance. It is not the biggest fire in Microsoft’s May 2026 release, and the public facts do not support treating it like a wormable emergency. But Remote Desktop is too close to the machinery of Windows administration for a confirmed privilege-escalation flaw to sit untouched, and the organizations that move calmly now will have fewer surprises when the exploit details eventually catch up with the patch.
Source: MSRC Security Update Guide - Microsoft Security Response Center