 CVE-2026-4224 and the XML parsing risk that should worry Windows admins
CVE-2026-4224 and the XML parsing risk that should worry Windows admins
Microsoft’s vanished CVE-2026-4224 page has left security teams with an uncomfortable gap: a title that points to a stack overflow while parsing XML with deeply nested DTD content models, but no public detail to anchor remediation planning. That combination matters because XML parsing bugs are often deceptively broad, touching desktop apps, server-side middleware, document workflows, and any component that reuses the same parsing libraries. In practical terms, the absence of a live advisory does not mean the risk is absent; it usually means the disclosure path is incomplete, delayed, or still in motion. Microsoft’s Security Update Guide has become the company’s main disclosure channel for CVEs and advisories, so when a CVE page is unreachable, administrators lose exactly the context they need most.Overview
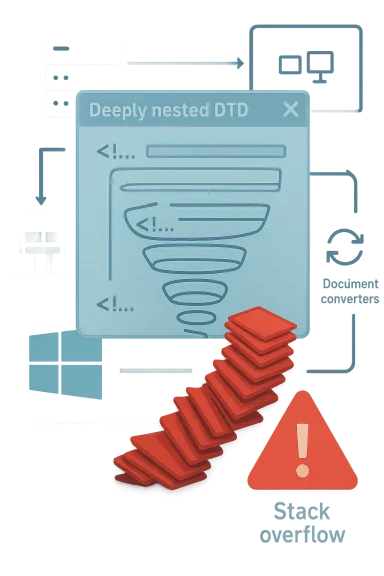
XML remains one of the most persistent attack surfaces in enterprise software because it is both foundational and sprawling. It appears in configuration files, messaging systems, document formats, identity workflows, and web service payloads, often far from the user interface where defenders would otherwise notice it. When a parser fails, the impact can range from denial of service to memory corruption, and a stack overflow immediately raises the stakes because it can, in some cases, lead to code execution rather than a simple crash.The wording attached to CVE-2026-4224 is also telling. “Deeply nested DTD content models” describes a parser edge case that can force excessive recursion or stack growth while resolving document type definitions. That is not a casual malformed input issue; it is the sort of input crafted to stress a parser’s internal control flow, often by exploiting insufficient depth checks or inadequate bounds validation.
Microsoft has a long history of using the Security Update Guide to publish precise vulnerability descriptions and CVSS metadata, and it has steadily expanded the amount of detail available there, including CWE mapping and richer advisory content. That evolution is relevant here because it means security teams now expect disclosure pages to be the authoritative record, not just a bulletin notice. When the page 404s, the operational model breaks: asset owners cannot quickly determine affected products, mitigations, exploitability, or whether the issue was already patched in a monthly release.
The timing matters too. In recent years Microsoft has increasingly used the Security Update Guide as a one-stop disclosure surface for CVEs and related advisories, including cloud-service disclosures that do not always map neatly to traditional product bulletins. That trend has improved transparency, but it also means a missing page stands out more sharply than it would have in the old bulletin era. If CVE-2026-4224 is legitimate and public, then its disappearance suggests either a staging issue, a reclassification, or a publication glitch worth monitoring closely.
Why XML Parsers Keep Breaking
XML parsers are complex because they do more than read tags. They must interpret entities, DTDs, namespaces, validation rules, content models, and document structure, often under tight performance constraints. Every added feature expands the parser’s attack surface, which is why vulnerabilities in XML handling keep reappearing across vendors and decades.A deeply nested DTD content model is especially dangerous because it can trigger recursion-heavy logic. If the parser builds a validation tree or walks nested definitions without enforcing a safe depth limit, the call stack can fill faster than the application expects. That creates a classic recipe for a stack overflow: attacker-controlled structure, repeated traversal, and insufficient guardrails.
The DTD Problem
DTD support exists for legitimate reasons, but it is also a legacy feature with a long history of security friction. Attackers can abuse DTD mechanics to amplify parser work, consume resources, or steer execution into error-prone paths. Even when external entities are disabled, the parser may still need to process the internal structure of a DTD, which is where depth and recursion defects emerge.For defenders, the key point is not just that DTDs are old, but that they are still enabled in enough products to matter. A single parser implementation can be embedded in office software, document conversion tools, middleware, and application frameworks, turning one flaw into a platform-wide concern. The safest assumption is therefore not “XML is just data,” but “XML is executable parser logic with user-controlled shape.”
- DTD parsing can involve recursion, not just linear scanning.
- Nested content models may exhaust stack space before input size limits trigger.
- Parser bugs can surface in applications that never advertise XML support.
- Disabling DTDs outright is not always feasible in enterprise environments.
- Small input files can still cause large parser workloads.
Why Stack Overflows Are Different
Not all parser bugs are equal. A heap overflow may be harder to control but easier to detect; a stack overflow often signals a tight, recursive code path that can fail suddenly and catastrophically. If the overwritten stack state is exploitable, the security impact escalates far beyond a denial of service.That said, exploitation is not automatic. Modern mitigations such as stack canaries, ASLR, CFG, and hardened libraries can raise the bar significantly. But even when exploitation is uncertain, a remotely triggerable stack overflow in a common parser deserves urgent attention because crash reliability alone can be enough to disrupt services.
What the Missing CVE Page Means
An unreachable advisory page is not just an inconvenience for researchers. It deprives blue teams of the normal decision tree they use to determine whether a CVE is relevant, whether a workaround exists, and whether the patch has already shipped. In Microsoft’s current disclosure model, the Security Update Guide is the canonical location for those details, so if the page is missing, the normal workflow stalls.There are several plausible explanations. The page could have been published prematurely and then pulled back, the identifier could be reserved but not yet fully released, or the underlying issue may have been re-scoped into a different advisory. Another possibility is simply a broken routing or localization error in the advisory infrastructure, which Microsoft has occasionally evolved as it expanded the guide and added new advisory types. Regardless of the cause, defenders should treat the absence of detail as a signal to verify patch levels rather than as evidence that the issue is irrelevant.
Operational Impact for IT Teams
For enterprise teams, missing metadata creates immediate friction. Security tools may flag the CVE name, but without a live description there is no clean way to map the issue to affected products, KBs, or deployment rings. That forces teams to rely on secondary signals such as patch notes, package inventories, or vulnerability scanners, which can lag behind the authoritative source.This is where Microsoft’s broader disclosure improvements become a double-edged sword. The richer the guide becomes, the more disruptive it is when one page fails to load, because users have grown to rely on it for specifics rather than generic bulletin summaries. The outcome is more transparency when everything works and more confusion when the guide is incomplete.
- Patch verification becomes harder when product impact is unknown.
- Risk teams must infer urgency from the vulnerability title alone.
- SOC analysts may see scanner alerts without remediation guidance.
- Asset owners may delay action pending confirmation from Microsoft.
- Incident responders lose a clean source for cross-checking exposure.
What Microsoft’s Disclosure Model Tells Us
Microsoft has gradually expanded the Security Update Guide with newer metadata, advisory tabs, CWE mapping, and even machine-readable formats like CSAF. That evolution reflects a clear push toward richer, more actionable security communication. It also means a broken page is more consequential than it once was, because the ecosystem now expects the guide to be the single source of truth for both humans and tooling.Enterprise Exposure: Where XML Lives in the Real World
Enterprise exposure to XML bugs is usually broader than it first appears. The obvious targets are apps that directly parse XML, but the deeper risk lies in shared components: document converters, line-of-business apps, service buses, reporting tools, and identity federation stacks. If the same parser is used in multiple places, one flaw can jump several trust boundaries.XML is especially common in workflows where users think they are handling documents, not code. That includes supply-chain portals, office file import pipelines, finance systems, and integration layers that exchange structured payloads between legacy and modern services. In those settings, an attacker does not need to persuade someone to run a binary; they only need to supply a crafted file or payload.
High-Value Targets
The most attractive targets are systems that process XML automatically and at scale. That includes mail gateways, workflow automation, and server applications that accept customer-submitted documents. A crash in any of those can become a service outage, while an exploitable overflow could become a lateral movement path.Defenders should also remember that XML often hides inside file containers. A document might look like a harmless attachment, but the parser path may be triggered by preview panes, indexing services, or backend content extraction. That means the attack surface extends beyond the application window that users interact with directly.
- Content management systems often parse XML during ingestion.
- Identity platforms still use XML-based protocols in some workflows.
- Document generation tools may process untrusted templates.
- Integration brokers often normalize XML before routing messages.
- Search and preview services can invoke parsing without explicit user action.
Consumer and SMB Impact
Consumer impact is likely to be more indirect, but it can still be meaningful. Desktop productivity suites, PDF and office converters, and synchronization tools often bundle XML components that handle content automatically. Even if the flaw is not exploitable in a consumer browser, it may still affect the apps users trust most for opening files.For small businesses, the issue can be even more acute because patch cadence is slower and visibility is weaker. SMBs frequently depend on default configurations, third-party middleware, and older document workflows, which means XML-related issues can sit unnoticed until a crash or exploit forces the issue.
Attack Mechanics and Real-World Exploitability
The phrase stack overflow parsing XML suggests a parser control-flow defect rather than a logic bug. In practical exploitation terms, an attacker would likely need to supply carefully structured XML that drives recursive descent or validation logic into excessive depth. The attacker’s goal would be to push the parser into overwriting return-oriented stack state or at least crashing a service deterministically.That said, modern exploitability is highly context-dependent. The same parser bug may be a simple denial of service in one process and a code execution opportunity in another, depending on compiler protections, calling conventions, and memory layout. In other words, the vulnerability title tells us the shape of the bug, but not the exploit path.
What Makes It Hard to Exploit
There are several reasons a stack overflow in XML parsing might not translate cleanly into reliable exploitation. The parser may stop before the stack is fully corrupted, modern mitigations may block return-address hijacking, or the vulnerable code path may be gated behind specific parser settings. In some products, the parser may even run inside a low-privilege sandbox or a less useful process context.Still, defenders should not be reassured too quickly. Attackers do not need perfect reliability if the bug can be triggered repeatedly across a fleet, and even denial-of-service issues can be used operationally to disrupt services, distract responders, or probe for exploitable variants.
- Structured XML can be tiny yet recursively expensive.
- Exploit reliability depends on compiler and OS mitigations.
- Library reuse can expose many products at once.
- Sandboxing may reduce impact but not eliminate risk.
- “Only a crash” can still be operationally severe.
Why Deep Nesting Matters
Deep nesting is a classic stressor because every recursive step consumes stack space and adds parser state. Once the parser’s recursion limit is too generous or absent, the input can force a pathological path long before application-level safeguards notice. That is why depth limits are a core control for parsers, not an optional performance tweak.The broader lesson is that parsers need defense in depth. Input validation, recursion bounds, memory safety, and safe default configuration all matter. If one layer fails, the others must still prevent the worst-case outcome.
Microsoft’s Security Update Guide and Why It Matters Here
Microsoft has spent years turning the Security Update Guide into a more detailed disclosure platform. It now carries richer descriptions, standardized vulnerability taxonomy, and increasingly machine-readable outputs. That matters because security teams have come to depend on the guide not merely for headlines, but for patch planning, compliance records, and exposure analysis.The implication for CVE-2026-4224 is straightforward: if the page is missing, the normal dependency chain breaks. Scan data may still identify the CVE, but the guide is where many administrators confirm the affected products and decide whether a deployment is urgent. Microsoft’s newer disclosure posture has made that page central to operational security, so even a temporary outage can create real confusion.
The Transparency Tradeoff
Greater transparency is helpful only if it is reliable. Microsoft’s move to publish more data elements, including CWE mappings and machine-readable records, has improved automation and analyst efficiency. But it also raises the cost of inconsistency, because security operations teams now sync their workflows to the guide’s structure.That is why missing or withdrawn pages can create more uncertainty than older bulletin-style communications ever did. The ecosystem now expects precision. When precision disappears, teams are left triangulating from patch Tuesday notes, advisory fragments, and scanner signatures.
What Administrators Should Infer
The prudent inference is that CVE-2026-4224 should be treated as potentially relevant until proven otherwise. If the title is accurate, then XML-consuming applications and services are the first places to check. If the page later returns with a different scope or severity, the risk may narrow; but until then, the conservative stance is to assume a meaningful parsing defect exists somewhere in Microsoft’s software stack or a component it distributes.Patch Strategy and Defensive Priorities
If a parser vulnerability is suspected, the best response is disciplined verification rather than panic. Start by identifying where XML parsing occurs in your environment, then map those paths to Microsoft products, embedded components, and third-party applications. The goal is to determine whether the vulnerable code is directly reachable, indirectly reachable, or not present at all.Because the disclosure page is unavailable, administrators should lean on patch hygiene. That means reviewing the latest cumulative updates, checking whether dependent applications shipped their own remediation, and ensuring endpoint protection and application control are configured to catch suspicious file handling. If the issue later turns out to be more limited, the work still pays off by improving visibility into XML-heavy workflows.
Practical Triage Steps
A good triage process should be short, repeatable, and evidence-driven. Teams do not need to know every exploit detail to reduce risk; they need a reliable method to find exposed systems quickly and confirm patch status. In a large estate, that matters more than the theoretical exploit path.- Inventory products that parse XML directly or indirectly.
- Check whether those products use Microsoft-shipped libraries or components.
- Review the latest security updates for the affected release channels.
- Test sample XML workloads in a staging environment after patching.
- Watch for crashes, parser exceptions, or unusual recursion failures.
- Confirm that endpoint and server telemetry captures parsing anomalies.
Defensive Controls That Help
Several controls are useful regardless of the final CVE details. Limiting DTD processing where feasible, reducing the privileges of parsing services, and segmenting document ingestion workloads can all blunt exploitation attempts. Those steps are not a substitute for patches, but they can reduce the blast radius if a malformed XML payload reaches a vulnerable component.- Restrict XML parsing to trusted services where possible.
- Disable DTDs in applications that do not require them.
- Run conversion services under low-privilege accounts.
- Isolate document-processing pipelines from core infrastructure.
- Log parser failures and repeated recursion-related exceptions.
Strengths and Opportunities
The good news is that this issue, at least by title, is the sort of problem defenders can reason about quickly. XML parsing flaws tend to have identifiable choke points, and organizations that already practice asset discovery and patch discipline will be better positioned than those that treat document handling as low risk. The missing CVE page is inconvenient, but it also creates an opportunity to tighten visibility around a class of software that often escapes scrutiny. Stronger parser governance now can pay dividends well beyond this one CVE.- XML parsing paths are usually discoverable through application inventory.
- Stack-based parser defects often concentrate in a few shared components.
- Patch verification can be automated once affected products are known.
- Document-processing pipelines are good candidates for isolation.
- DTD-reduction policies improve resilience beyond a single vulnerability.
- Security teams can use the gap to improve dependency mapping.
- Telemetry enhancements will help detect future parser abuse.
Risks and Concerns
The biggest risk is ambiguity. Without a live advisory, teams may underestimate the issue, assume it is not broadly relevant, or wait for confirmation until after attackers have had time to test the weakness. XML vulnerabilities are also dangerous because they can hide in places defenders do not routinely inspect, and a parser bug in one component can cascade across products that share the same code path. In security operations, uncertainty itself becomes an attack surface when it slows response.- Missing advisory details can delay patch decisions.
- Shared XML libraries can widen exposure across products.
- Recursive parser defects may crash critical services.
- Document ingestion paths are often less monitored than web apps.
- Small organizations may not know where XML parsing occurs.
- Scanner output without context can lead to misprioritization.
- A pulled page may indicate an unresolved disclosure issue.
Looking Ahead
The next few disclosure cycles will matter more than usual. If Microsoft restores the page, updates the CVE record, or folds it into a different advisory, that will clarify scope and urgency. If not, security teams should continue treating the identifier as a marker for a likely parser flaw and keep checking patch notes, KB releases, and any late-added advisory text in the Security Update Guide.The broader lesson is that disclosure infrastructure now matters nearly as much as the vulnerability itself. Microsoft has invested heavily in turning the Security Update Guide into a richer source of truth, which is good for defenders when it works and frustrating when it does not. In a world where parsing bugs can affect everything from office documents to backend integration stacks, even a missing page can become a security event in its own right.
- Verify the advisory’s status in the next Security Update Guide refresh.
- Recheck cumulative update notes for XML-related parser fixes.
- Audit systems that process user-supplied XML or XML-like content.
- Monitor for parser crashes in document and integration services.
- Revisit DTD policies and recursion limits across the estate.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: