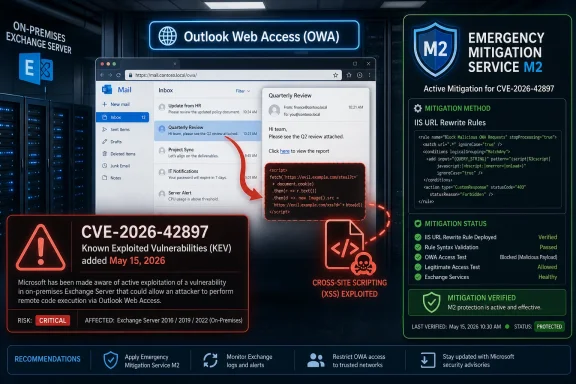
CISA added CVE-2026-42897, a Microsoft Exchange Server cross-site scripting vulnerability affecting Outlook Web Access on on-premises Exchange, to its Known Exploited Vulnerabilities Catalog on May 15, 2026, after evidence showed the flaw was being actively exploited in real-world attacks. The move turns what might otherwise look like another Exchange advisory into an operational deadline for federal agencies and a practical warning for everyone else still running Exchange in their own data centers. Microsoft has not yet shipped a permanent fix, so the immediate story is mitigation, exposure reduction, and the familiar pressure on administrators to defend a system that remains too valuable for attackers to ignore.
The Known Exploited Vulnerabilities Catalog was created to solve a blunt problem: organizations drown in vulnerability data, while attackers focus on a much smaller set of bugs that actually work in the wild. When CISA adds a CVE to the catalog, it is not merely saying that a bug is theoretically serious. It is saying that exploitation has crossed the line from plausible to observed.
That distinction matters for Exchange administrators because the platform has lived through years of emergency weekends, rushed mitigations, and uncomfortable postmortems. Exchange is not just another server workload. It is identity-adjacent, internet-facing in many deployments, rich with sensitive messages, and deeply embedded in authentication, calendaring, and business workflow.
CISA’s May 15 alert is therefore best read less as a bulletin and more as a prioritization command. For Federal Civilian Executive Branch agencies, Binding Operational Directive 22-01 requires remediation by the catalog’s due date. For everyone else, the legal mandate may not apply, but the risk signal does.
The agency’s language is deliberately broad: known exploited vulnerabilities are frequent attack vectors and pose significant risks to the federal enterprise. That phrasing can sound bureaucratic, but it reflects a hard-earned security lesson. Once a bug appears in the KEV catalog, defenders should assume it is either already in attacker playbooks or about to be.
That taxonomy can undersell the impact. Cross-site scripting is one of the oldest web application bug classes, and security teams have seen enough XSS tickets to become numb to the term. But in the context of OWA, arbitrary JavaScript executing in a victim’s browser context can become a powerful foothold for session abuse, phishing, message manipulation, and interface deception.
The reported attack path is especially uncomfortable because it begins with something Exchange exists to process: email. Microsoft said an attacker could exploit the issue by sending a specially crafted message to a user, with execution occurring if the user opens it in Outlook Web Access and certain interaction conditions are met. That is not the same as unauthenticated remote code execution on the server, but it is also not a harmless browser nuisance.
The flaw affects on-premises Exchange Server, including Exchange Server 2016, Exchange Server 2019, and Exchange Server Subscription Edition. Exchange Online is not listed as affected, which will reinforce Microsoft’s long-running argument that cloud-hosted email reduces the operational burden of emergency Exchange defense. For hybrid and on-premises shops, the message is more pointed: ownership of the server still means ownership of the blast radius.
The Emergency Mitigation Service is designed to check Microsoft’s Office Config Service, download signed mitigation configuration, validate it, and apply protections automatically on eligible Exchange Mailbox servers. It is optional, and some administrators disable it because automatic vendor-applied server changes can be a governance headache. Incidents like this are the strongest argument for leaving it enabled, or at least for having a disciplined process to consume its output quickly.
There is a trade-off. Temporary mitigations are not the same as security updates, and Microsoft says as much in its own documentation. They can reduce exposure to active exploitation while a permanent fix is pending, but they are not a substitute for installing the eventual Exchange Security Update when it arrives.
That distinction should shape the response. Applying M2 is not the end of the incident for an Exchange team. It is the moment the team buys time, verifies that the mitigation actually landed, monitors for side effects, and prepares to move again when Microsoft ships the proper fix.
OWA exposure also varies wildly between organizations. Some shops have it behind VPN or conditional access gates. Others publish it broadly because remote work, mobile access, contractors, and legacy assumptions made public webmail a business requirement long ago. The same CVE can be a contained internal nuisance in one environment and a front-door risk in another.
Security teams should resist the urge to treat this as a pure Exchange team problem. If exploitation depends on a user opening a malicious message in OWA, mail filtering, browser hardening, session monitoring, identity protections, and incident response telemetry all matter. The Exchange server is the affected product, but the attack surface is the user’s mail experience.
The vulnerability also lands at a time when many organizations are already trying to decide what to do with their remaining on-premises Exchange footprint. Some servers exist for full mail hosting. Others survive as management anchors in hybrid Microsoft 365 environments. The fewer users who actively rely on OWA, the more defensible it becomes to restrict or disable access while the mitigation and later patch cycle unfold.
CVE-2026-42897 is not the same class of bug as those earlier server-side exploitation chains, and it would be irresponsible to conflate them. But attackers do not need every Exchange vulnerability to look like the last one. They need a reliable path from a exposed service to a useful outcome, and browser-executed script inside OWA can support deception, credential targeting, and session-oriented abuse.
The industry’s tendency to rank vulnerabilities by worst-case technical drama can obscure this. Remote code execution gets the headlines. Cross-site scripting gets filed under “web bug.” Yet attackers often combine less spectacular weaknesses with social engineering and valid sessions because that path blends better with ordinary user behavior.
That is the lesson administrators should carry into this response. The absence of a permanent patch does not mean waiting is acceptable. The presence of a mitigation does not mean the environment is safe. And the label spoofing does not mean the impact is limited to cosmetic deception.
For private-sector IT teams, the practical question is not whether CISA can compel action. It is whether the organization wants to explain later why a known exploited Exchange bug was left unmitigated after both Microsoft and CISA warned about active abuse. That is a hard conversation to win after an intrusion.
The catalog also helps cut through the noise of modern vulnerability management. Every month brings thousands of CVEs, dozens of vendor advisories, and a smaller number of issues that attackers actually operationalize. KEV inclusion moves CVE-2026-42897 into that smaller, uglier category.
This is especially important for smaller organizations that still run Exchange because migration projects are expensive, politically fraught, or unfinished. They may not have a full-time security operations center, but they do have the same exposure characteristics as larger enterprises. Attackers do not need a victim to be sophisticated; they need the target to be reachable and slow.
That is where many emergency responses go wrong. A dashboard says a mitigation exists, a vendor blog says protection is available, and a change ticket says the organization is “covered.” None of that proves that the rewrite rule is present and active on every server that matters.
Microsoft’s documentation provides ways to view applied and blocked mitigations through Exchange PowerShell and the Get-Mitigations script. Administrators should use those checks rather than relying on assumption. They should also review the Exchange mitigation service logs and Windows Application Event Log entries for successful application or errors.
There is a second verification step: understand whether any administrator previously blocked mitigations. Some organizations blocked earlier Exchange emergency mitigations because of compatibility concerns, change-control policy, or distrust of automatic service changes. If M2 is blocked, the server’s risk posture may be very different from what a quick inventory suggests.
Mail security teams should also treat this as a detection problem. Even if exploit details are incomplete or not publicly available, suspicious messages targeting OWA users, unusual OWA behavior, unexpected mailbox rules, anomalous sign-ins, and odd browser session patterns deserve scrutiny. A client-side script execution path may leave different traces than server compromise, but that does not mean it leaves no traces.
User guidance should be precise rather than theatrical. Telling everyone not to open suspicious email is security wallpaper. Telling OWA users that a known exploited Exchange flaw is active, that crafted messages are part of the reported attack path, and that suspicious OWA behavior should be reported immediately is more useful.
For administrators, the event should also trigger an inventory check. If an organization cannot quickly answer which Exchange versions it runs, which servers expose OWA, whether EM Service is enabled, and which mitigations are applied, the vulnerability has revealed a management problem as much as a software problem.
But the conclusion should not be a simplistic “cloud good, on-prem bad.” Cloud email shifts operational responsibility; it does not remove the need for identity hygiene, logging, access control, tenant hardening, and incident response. Many Microsoft 365 compromises begin with credentials, OAuth abuse, misconfiguration, or phishing rather than a server CVE.
Still, on-premises Exchange carries a unique burden. It requires administrators to patch complex infrastructure, maintain certificates, publish web services, manage hybrid connectors, monitor IIS, and respond to emergency mitigations under time pressure. That burden is manageable for mature teams, but it is unforgiving for organizations that treat Exchange as a legacy appliance.
CVE-2026-42897 will therefore become another data point in migration conversations. Not because every organization can move overnight, but because every emergency mitigation makes the hidden cost of staying on-premises more visible. The server may already be paid for. The operational risk is not.
That gap is worse when a vulnerability is already exploited. Public awareness can increase attacker interest, even if exploit details remain incomplete, because defenders have confirmed that something valuable exists. The KEV listing is not an exploit tutorial, but it is a market signal.
Microsoft’s mitigation-first response reflects the reality that software fixes for Exchange are not always instantaneous. Regression risk is real, especially in a product that handles mail transport, web access, calendaring, compliance, and hybrid integration. A rushed patch that breaks production email can create its own crisis.
But attackers do not pause for engineering caution. That is why the mitigation service exists, and why administrators should treat its output as an urgent control rather than a convenience feature. The goal is not perfection in the first 24 hours. The goal is to remove the easiest active path while preparing for the fix that actually closes the vulnerability.
Administrators should confirm the Exchange versions in production, identify OWA exposure, verify whether the Emergency Mitigation Service is running, and check for M2 across every relevant server. Security teams should watch for user reports and unusual OWA activity, while infrastructure teams prepare for Microsoft’s eventual security update.
The key point is sequencing. Mitigate now. Reduce exposure where possible. Monitor for signs of abuse. Patch when the permanent fix arrives. Then remove or reassess temporary controls only after confirming that the fixed build no longer needs them.
There is a cultural point here, too. Exchange incidents reward organizations that maintain boring discipline: asset inventories, change records, tested scripts, working outbound service connectivity, and clear ownership. They punish organizations where mail infrastructure is treated as a dark corner nobody wants to touch.
Source: CISA CISA Adds One Known Exploited Vulnerability to Catalog | CISA
 CISA’s Catalog Is Becoming the Real Patch Tuesday for Exploited Bugs
CISA’s Catalog Is Becoming the Real Patch Tuesday for Exploited Bugs
The Known Exploited Vulnerabilities Catalog was created to solve a blunt problem: organizations drown in vulnerability data, while attackers focus on a much smaller set of bugs that actually work in the wild. When CISA adds a CVE to the catalog, it is not merely saying that a bug is theoretically serious. It is saying that exploitation has crossed the line from plausible to observed.That distinction matters for Exchange administrators because the platform has lived through years of emergency weekends, rushed mitigations, and uncomfortable postmortems. Exchange is not just another server workload. It is identity-adjacent, internet-facing in many deployments, rich with sensitive messages, and deeply embedded in authentication, calendaring, and business workflow.
CISA’s May 15 alert is therefore best read less as a bulletin and more as a prioritization command. For Federal Civilian Executive Branch agencies, Binding Operational Directive 22-01 requires remediation by the catalog’s due date. For everyone else, the legal mandate may not apply, but the risk signal does.
The agency’s language is deliberately broad: known exploited vulnerabilities are frequent attack vectors and pose significant risks to the federal enterprise. That phrasing can sound bureaucratic, but it reflects a hard-earned security lesson. Once a bug appears in the KEV catalog, defenders should assume it is either already in attacker playbooks or about to be.
The Exchange Bug Is “Just XSS” Only If You Ignore Where It Runs
CVE-2026-42897 is described as a Microsoft Exchange Server cross-site scripting vulnerability tied to Outlook Web Access, the browser-based mail experience that many organizations expose precisely because users need mail from everywhere. Microsoft’s advisory language characterizes the issue as a spoofing vulnerability caused by improper neutralization of input during web page generation.That taxonomy can undersell the impact. Cross-site scripting is one of the oldest web application bug classes, and security teams have seen enough XSS tickets to become numb to the term. But in the context of OWA, arbitrary JavaScript executing in a victim’s browser context can become a powerful foothold for session abuse, phishing, message manipulation, and interface deception.
The reported attack path is especially uncomfortable because it begins with something Exchange exists to process: email. Microsoft said an attacker could exploit the issue by sending a specially crafted message to a user, with execution occurring if the user opens it in Outlook Web Access and certain interaction conditions are met. That is not the same as unauthenticated remote code execution on the server, but it is also not a harmless browser nuisance.
The flaw affects on-premises Exchange Server, including Exchange Server 2016, Exchange Server 2019, and Exchange Server Subscription Edition. Exchange Online is not listed as affected, which will reinforce Microsoft’s long-running argument that cloud-hosted email reduces the operational burden of emergency Exchange defense. For hybrid and on-premises shops, the message is more pointed: ownership of the server still means ownership of the blast radius.
Microsoft’s Temporary Fix Puts the Emergency Mitigation Service Back in the Spotlight
The awkward center of this incident is that administrators are being asked to mitigate before they can patch. Microsoft has made an Exchange Emergency Mitigation Service rule available for CVE-2026-42897, identified in Microsoft’s mitigation table as M2. The mitigation uses IIS URL Rewrite configuration, which is exactly the sort of interim control Microsoft introduced after prior Exchange crises showed that waiting for full security updates can leave defenders exposed for too long.The Emergency Mitigation Service is designed to check Microsoft’s Office Config Service, download signed mitigation configuration, validate it, and apply protections automatically on eligible Exchange Mailbox servers. It is optional, and some administrators disable it because automatic vendor-applied server changes can be a governance headache. Incidents like this are the strongest argument for leaving it enabled, or at least for having a disciplined process to consume its output quickly.
There is a trade-off. Temporary mitigations are not the same as security updates, and Microsoft says as much in its own documentation. They can reduce exposure to active exploitation while a permanent fix is pending, but they are not a substitute for installing the eventual Exchange Security Update when it arrives.
That distinction should shape the response. Applying M2 is not the end of the incident for an Exchange team. It is the moment the team buys time, verifies that the mitigation actually landed, monitors for side effects, and prepares to move again when Microsoft ships the proper fix.
The Operational Risk Is Not the CVSS Score, It Is the Workflow
CVE-2026-42897 has been reported with a high severity score, but the score is not the main reason this bug deserves attention. The operational risk comes from where the bug sits in the mail workflow and how hard it is to eliminate email-driven interaction from ordinary business life. A crafted email is not an exotic delivery mechanism; it is the default language of compromise.OWA exposure also varies wildly between organizations. Some shops have it behind VPN or conditional access gates. Others publish it broadly because remote work, mobile access, contractors, and legacy assumptions made public webmail a business requirement long ago. The same CVE can be a contained internal nuisance in one environment and a front-door risk in another.
Security teams should resist the urge to treat this as a pure Exchange team problem. If exploitation depends on a user opening a malicious message in OWA, mail filtering, browser hardening, session monitoring, identity protections, and incident response telemetry all matter. The Exchange server is the affected product, but the attack surface is the user’s mail experience.
The vulnerability also lands at a time when many organizations are already trying to decide what to do with their remaining on-premises Exchange footprint. Some servers exist for full mail hosting. Others survive as management anchors in hybrid Microsoft 365 environments. The fewer users who actively rely on OWA, the more defensible it becomes to restrict or disable access while the mitigation and later patch cycle unfold.
Exchange Keeps Teaching the Same Lesson About Internet-Facing Infrastructure
Microsoft Exchange has become one of the defining enterprise security stories of the last decade because it sits at the intersection of valuable data and unavoidable connectivity. ProxyLogon, ProxyShell, and later Exchange-related emergency advisories taught administrators that internet-facing collaboration infrastructure is not merely business plumbing. It is strategic terrain.CVE-2026-42897 is not the same class of bug as those earlier server-side exploitation chains, and it would be irresponsible to conflate them. But attackers do not need every Exchange vulnerability to look like the last one. They need a reliable path from a exposed service to a useful outcome, and browser-executed script inside OWA can support deception, credential targeting, and session-oriented abuse.
The industry’s tendency to rank vulnerabilities by worst-case technical drama can obscure this. Remote code execution gets the headlines. Cross-site scripting gets filed under “web bug.” Yet attackers often combine less spectacular weaknesses with social engineering and valid sessions because that path blends better with ordinary user behavior.
That is the lesson administrators should carry into this response. The absence of a permanent patch does not mean waiting is acceptable. The presence of a mitigation does not mean the environment is safe. And the label spoofing does not mean the impact is limited to cosmetic deception.
Federal Deadlines Are a Warning Shot for Private Networks
BOD 22-01 directly binds Federal Civilian Executive Branch agencies, but the KEV catalog’s influence extends far beyond Washington. Insurers, auditors, managed security providers, and board-level risk committees increasingly use KEV status as a shortcut for “this vulnerability is no longer theoretical.” That gives the catalog a second life as a de facto enterprise prioritization list.For private-sector IT teams, the practical question is not whether CISA can compel action. It is whether the organization wants to explain later why a known exploited Exchange bug was left unmitigated after both Microsoft and CISA warned about active abuse. That is a hard conversation to win after an intrusion.
The catalog also helps cut through the noise of modern vulnerability management. Every month brings thousands of CVEs, dozens of vendor advisories, and a smaller number of issues that attackers actually operationalize. KEV inclusion moves CVE-2026-42897 into that smaller, uglier category.
This is especially important for smaller organizations that still run Exchange because migration projects are expensive, politically fraught, or unfinished. They may not have a full-time security operations center, but they do have the same exposure characteristics as larger enterprises. Attackers do not need a victim to be sophisticated; they need the target to be reachable and slow.
Administrators Should Verify, Not Assume, That Mitigation Happened
The immediate action for Exchange administrators is to determine whether the M2 mitigation has been applied across every affected server. In environments where the Exchange Emergency Mitigation Service is enabled and has required outbound connectivity, that may happen automatically. In locked-down environments, the service may be disabled, blocked by proxy rules, broken by SSL inspection, or unable to validate the signed mitigation payload.That is where many emergency responses go wrong. A dashboard says a mitigation exists, a vendor blog says protection is available, and a change ticket says the organization is “covered.” None of that proves that the rewrite rule is present and active on every server that matters.
Microsoft’s documentation provides ways to view applied and blocked mitigations through Exchange PowerShell and the Get-Mitigations script. Administrators should use those checks rather than relying on assumption. They should also review the Exchange mitigation service logs and Windows Application Event Log entries for successful application or errors.
There is a second verification step: understand whether any administrator previously blocked mitigations. Some organizations blocked earlier Exchange emergency mitigations because of compatibility concerns, change-control policy, or distrust of automatic service changes. If M2 is blocked, the server’s risk posture may be very different from what a quick inventory suggests.
Temporary Defenses Need a Wider Security Envelope
Because CVE-2026-42897 is tied to OWA and crafted email, mitigation should be paired with practical exposure reduction. Organizations that do not need public OWA should consider restricting access while the permanent fix is pending. Organizations that do need it should review conditional access, multifactor authentication, session lifetime, and geographic or device-based controls.Mail security teams should also treat this as a detection problem. Even if exploit details are incomplete or not publicly available, suspicious messages targeting OWA users, unusual OWA behavior, unexpected mailbox rules, anomalous sign-ins, and odd browser session patterns deserve scrutiny. A client-side script execution path may leave different traces than server compromise, but that does not mean it leaves no traces.
User guidance should be precise rather than theatrical. Telling everyone not to open suspicious email is security wallpaper. Telling OWA users that a known exploited Exchange flaw is active, that crafted messages are part of the reported attack path, and that suspicious OWA behavior should be reported immediately is more useful.
For administrators, the event should also trigger an inventory check. If an organization cannot quickly answer which Exchange versions it runs, which servers expose OWA, whether EM Service is enabled, and which mitigations are applied, the vulnerability has revealed a management problem as much as a software problem.
The Cloud Escape Hatch Looks Better, But It Is Not Magic
Microsoft will inevitably benefit from the contrast between affected on-premises Exchange and unaffected Exchange Online. That contrast is real. When Exchange Online is outside the affected product set, Microsoft can patch, harden, and monitor the service at cloud scale without asking every customer to perform emergency server surgery.But the conclusion should not be a simplistic “cloud good, on-prem bad.” Cloud email shifts operational responsibility; it does not remove the need for identity hygiene, logging, access control, tenant hardening, and incident response. Many Microsoft 365 compromises begin with credentials, OAuth abuse, misconfiguration, or phishing rather than a server CVE.
Still, on-premises Exchange carries a unique burden. It requires administrators to patch complex infrastructure, maintain certificates, publish web services, manage hybrid connectors, monitor IIS, and respond to emergency mitigations under time pressure. That burden is manageable for mature teams, but it is unforgiving for organizations that treat Exchange as a legacy appliance.
CVE-2026-42897 will therefore become another data point in migration conversations. Not because every organization can move overnight, but because every emergency mitigation makes the hidden cost of staying on-premises more visible. The server may already be paid for. The operational risk is not.
The Patch Gap Is Where Attackers Make Their Money
The most dangerous period in many vulnerability events is the gap between disclosure and durable remediation. Defenders are reading advisories, parsing affected versions, checking whether mitigations apply, and waiting for updates. Attackers are doing the same thing with a different goal.That gap is worse when a vulnerability is already exploited. Public awareness can increase attacker interest, even if exploit details remain incomplete, because defenders have confirmed that something valuable exists. The KEV listing is not an exploit tutorial, but it is a market signal.
Microsoft’s mitigation-first response reflects the reality that software fixes for Exchange are not always instantaneous. Regression risk is real, especially in a product that handles mail transport, web access, calendaring, compliance, and hybrid integration. A rushed patch that breaks production email can create its own crisis.
But attackers do not pause for engineering caution. That is why the mitigation service exists, and why administrators should treat its output as an urgent control rather than a convenience feature. The goal is not perfection in the first 24 hours. The goal is to remove the easiest active path while preparing for the fix that actually closes the vulnerability.
The Practical Read for Exchange Shops Running OWA
For organizations running affected on-premises Exchange, the response should be concrete and auditable. This is not a moment for vague assurances that servers are “current,” especially since reports indicate the affected set includes supported Exchange versions and the mitigation applies broadly.Administrators should confirm the Exchange versions in production, identify OWA exposure, verify whether the Emergency Mitigation Service is running, and check for M2 across every relevant server. Security teams should watch for user reports and unusual OWA activity, while infrastructure teams prepare for Microsoft’s eventual security update.
The key point is sequencing. Mitigate now. Reduce exposure where possible. Monitor for signs of abuse. Patch when the permanent fix arrives. Then remove or reassess temporary controls only after confirming that the fixed build no longer needs them.
There is a cultural point here, too. Exchange incidents reward organizations that maintain boring discipline: asset inventories, change records, tested scripts, working outbound service connectivity, and clear ownership. They punish organizations where mail infrastructure is treated as a dark corner nobody wants to touch.
This KEV Entry Turns an Exchange Advisory Into an Action Plan
CISA’s addition of CVE-2026-42897 does not mean every Exchange environment is compromised, and it does not mean panic is useful. It does mean defenders should stop treating the vulnerability as an ordinary advisory waiting its turn in the patch queue.- Organizations running on-premises Exchange Server 2016, Exchange Server 2019, or Exchange Server Subscription Edition should assume CVE-2026-42897 is operationally urgent if OWA is enabled or exposed.
- Exchange Online is not listed as affected, but hybrid organizations should still inventory any remaining on-premises Exchange servers and their published services.
- Microsoft’s M2 emergency mitigation should be verified on each affected server rather than assumed from policy, documentation, or service status alone.
- Temporary mitigation should be followed by monitoring and by installation of the permanent Exchange security update when Microsoft releases it.
- CISA’s KEV listing should elevate this vulnerability in vulnerability management workflows even for organizations that are not bound by federal remediation deadlines.
- Teams that cannot quickly determine Exchange exposure, mitigation state, and OWA usage should treat that uncertainty as a security finding in its own right.
Source: CISA CISA Adds One Known Exploited Vulnerability to Catalog | CISA