On May 6, 2026, CVE-2026-43119 was published for a Linux kernel Bluetooth flaw in
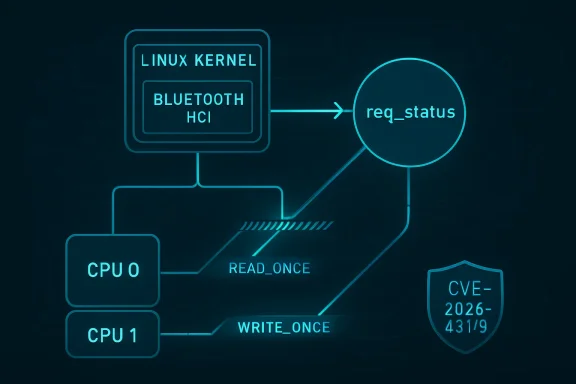
CVE-2026-43119 is not the sort of bug that arrives with a logo, a leaked exploit, or a dramatic vendor advisory. It is a concurrency flaw in the Linux Bluetooth Host Controller Interface synchronization path, specifically around the
The short version is that one path writes
That is the entire scandal: one integer-like status value, touched from multiple places, not consistently protected. In old-fashioned bug triage, that might have been filed as a cleanup. In 2026 kernel security, it earns a CVE because plain C access to shared state in concurrent kernel code is not a harmless style violation.
The fix does not introduce a new mutex or redesign the Bluetooth command engine. It annotates the accesses so the compiler and the kernel memory model understand what the programmer intended. That distinction matters, because data races are not just about two CPUs doing something surprising; they are also about the compiler being free to transform code in ways that make the source-level mental model false.
The problem described in CVE-2026-43119 is that
That might sound like ordinary kernel messiness, but the CVE text makes the concurrency issue explicit:
This is why the issue is not fixed by optimism. If a field is shared between execution contexts, the code needs either locking, atomic operations, or explicit annotations that match the intended synchronization story. The Bluetooth code had a partially locked story, which is often more dangerous than an obviously unlocked one, because reviewers can see the lock and assume the invariant is stronger than it is.
The result is a data race, a phrase that has become more prominent in kernel CVEs because the kernel has spent years making its memory model more explicit. A data race does not automatically mean an attacker gets code execution. It means the program has concurrent plain accesses to the same memory location without a sufficient ordering or serialization guarantee, and at least one access is a write.
The CVE description calls out two concrete compiler hazards: load fusing in a
In single-threaded C, that optimization is often legal and desirable. In kernel code observing state updated by another CPU, it can turn a live wait into stale logic. The code looks as if it is polling shared state, but the generated machine code may not behave that way unless the access is marked.
That is the part of this CVE that deserves attention from IT pros who normally do not read Bluetooth patches. The bug is not a buffer overflow, a missing bounds check, or a wrong permission check. It is a mismatch between the code’s concurrency contract and the language/compiler contract. In a modern kernel, that mismatch is security-relevant.
For administrators, CVSS is useful when it describes a fully understood vulnerability. It is less useful in the early hours of kernel CVE publication, especially for bugs like this one. A data race may be very hard to exploit directly, may manifest only under rare timing, or may become important only when combined with device behavior, driver quirks, or another bug.
The Linux kernel’s recent CVE practice has also made the ecosystem noisier. Many upstream fixes now receive CVE identifiers even when the practical exploitability is uncertain. That is good for traceability but frustrating for patch prioritization, because a terse kernel commit can suddenly become a vulnerability record before distributions have published their own severity judgments.
CVE-2026-43119 sits directly in that tension. The record describes a real race and a real fix. It does not, by itself, prove remote compromise, local privilege escalation, or a reliable denial-of-service path. But it does identify a condition in privileged kernel Bluetooth code where concurrent state handling was not expressed safely.
That makes it the kind of bug enterprises should patch through normal kernel update channels rather than panic over. It is not a headline emergency on the evidence currently available. It is also not something to wave away because the patch is small.
On desktops, Bluetooth often means keyboards, mice, headphones, game controllers, phones, and wearables. On laptops, it may share silicon, power management, and firmware update paths with Wi-Fi. On embedded systems and kiosks, it may be enabled because the hardware platform ships that way, even if nobody thinks of it as part of the application.
The HCI layer is especially important because it is where the host stack talks to the controller. A bug in HCI synchronization does not automatically imply that a nearby attacker can exploit it over the air. But it does live in a part of the stack that processes asynchronous events and command completions from Bluetooth hardware.
That asynchronous nature is why races matter here. Bluetooth is not a neat request-response protocol executed by one thread in isolation. Commands are queued, events arrive, workqueues run, cancellations happen, connections abort, and error recovery may fire while other work is in progress.
The CVE’s mention of separate workqueues is therefore not a footnote. It is the architecture. The bug exists because two pieces of kernel work that sound related are not necessarily serialized by being “Bluetooth work.” They are scheduled in different places and can run at the same time.
The Linux kernel cannot pretend it is ordinary ISO C running in a single-threaded universe. It relies on carefully documented primitives to communicate ordering, atomicity, and visibility. When the code accesses shared state without those primitives, the compiler may optimize based on assumptions that are valid for normal C but dangerous for concurrent kernel execution.
This is why
There is an important restraint in the fix. The patch does not appear to claim that
The danger for defenders is that narrow fixes can look unimportant on dashboards. A scanner sees a CVE. A ticket gets created. Someone asks for the CVSS score. If none exists, the item may be deferred. But the actual engineering signal is that upstream found shared kernel state whose access pattern needed to be made explicit.
The Microsoft Security Response Center listing is also a reminder that vulnerability visibility no longer follows operating system tribal lines. Microsoft tracks CVEs affecting open-source components, cloud workloads, developer environments, and customer deployments that may sit adjacent to Windows estates. A Linux kernel Bluetooth flaw may matter to a Windows-centric organization because the fleet is no longer Windows-only.
The practical question is not whether every Windows admin should drop everything for CVE-2026-43119. They should not. The practical question is whether asset inventory, patch management, and exposure assumptions include Linux systems with Bluetooth-capable kernels. In many organizations, the answer is messier than the CMDB suggests.
For client devices, the risk calculus depends on whether Bluetooth is enabled and whether users pair with untrusted devices. For servers, the more important question is why Bluetooth is present at all. Many rack servers do not need it, but small-form-factor PCs, edge boxes, industrial systems, and repurposed desktop hardware often blur that line.
For virtualized and containerized environments, the situation is different again. Containers share the host kernel, so kernel vulnerabilities are patched at the host, not inside the container image. Virtual machines have their own kernels, but Bluetooth passthrough or USB device passthrough can create unexpected hardware exposure in labs and specialty deployments.
The old model implicitly favored spectacular bugs. The new model captures more of the maintenance reality: use-after-free fixes, missing locks, incorrect lifetime rules, uninitialized values, and race annotations. The downside is that vulnerability databases can make every kernel patch sound equally ominous while withholding the context administrators need.
This is where distribution advisories still matter. Red Hat, Ubuntu, Debian, SUSE, Arch, Fedora, and downstream appliance vendors do the operational work of mapping upstream commits to shipped kernels, affected products, and support timelines. A CVE record tells you a vulnerability exists upstream. Your vendor’s kernel package tells you whether your machines are actually exposed and whether a fixed build is available.
The upstream stable references in the record indicate that the fix was applied across multiple maintained kernel lines. That is significant because Bluetooth bugs often span several versions, and the affected code may not be confined to bleeding-edge kernels. But the exact exposure for any given system depends on the kernel tree, configuration, backports, and vendor patches.
For enterprise IT, the right response is disciplined triage. Determine whether your Linux endpoints or appliances use affected kernel branches. Check whether Bluetooth is enabled or compiled in. Watch vendor advisories for severity and package availability. Then patch in the next appropriate maintenance window unless your environment has unusually high Bluetooth exposure.
That caveat matters because Bluetooth vulnerabilities are easy to overhype. The word “Bluetooth” invites images of drive-by compromise from a parking lot. The word “kernel” invites the assumption of instant root. The reality is usually more constrained, more hardware-dependent, and more timing-sensitive.
At the same time, dismissing the bug because exploitability is unclear would be a mistake. Race conditions often become more interesting when attackers can influence scheduling, trigger repeated operations, or combine a fragile state machine with another bug. Kernel Bluetooth code has all the ingredients that make concurrency hard: asynchronous events, device state transitions, cancellation paths, and error handling.
The most honest assessment is that CVE-2026-43119 is a low-noise, technically real kernel race whose practical impact has not yet been fully characterized publicly. That makes it a patching issue, not a panic issue. It also makes it a useful case study in how security fixes now look when the vulnerability is less about a dramatic crash and more about making undefined behavior impossible.
That is exactly why such patches matter. Operating systems become secure not only through heroic mitigations and emergency zero-day fixes, but through thousands of small corrections that remove ambiguity. A compiler no longer gets to make a dangerous assumption. A workqueue interaction no longer depends on wishful thinking. A future maintainer sees the access pattern marked as concurrent.
This is also a reminder that lockless code has a documentation burden. If a field is intentionally read without a lock, the code should say so through the right primitive. If it is not intentional, the code should be locked. What is not sustainable is the middle ground where one path locks, another path does not, and everyone hopes the scheduler is kind.
For Linux users, the actionable advice is simple: take kernel updates seriously even when the CVE wording looks microscopic. For organizations, the strategic advice is broader: improve the path from upstream kernel CVE to local exposure decision. The faster you can answer “Do we run this code, in this configuration, on these machines?” the less you have to rely on generic severity scores.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
hci_sync, where unsynchronized reads and writes of hdev->req_status could create a data race across separate kernel workqueues. The fix is small, almost boring: annotate the shared status field with READ_ONCE() and WRITE_ONCE(). The lesson is not boring at all. This is the kind of vulnerability record that shows how modern kernel security increasingly lives in the gray zone between “no obvious exploit” and “the compiler is allowed to make this worse.”
 A Bluetooth CVE That Looks Tiny Until You Read It Like a Kernel Developer
A Bluetooth CVE That Looks Tiny Until You Read It Like a Kernel Developer
CVE-2026-43119 is not the sort of bug that arrives with a logo, a leaked exploit, or a dramatic vendor advisory. It is a concurrency flaw in the Linux Bluetooth Host Controller Interface synchronization path, specifically around the hdev->req_status field used to track the state of synchronous HCI command requests.The short version is that one path writes
hdev->req_status under hdev->req_lock, while several other paths read or write the same field without holding that lock. Those paths include command work, event completion, cancellation, and connection abort logic. Because some of them run on different workqueues, they can execute on different CPUs at the same time.That is the entire scandal: one integer-like status value, touched from multiple places, not consistently protected. In old-fashioned bug triage, that might have been filed as a cleanup. In 2026 kernel security, it earns a CVE because plain C access to shared state in concurrent kernel code is not a harmless style violation.
The fix does not introduce a new mutex or redesign the Bluetooth command engine. It annotates the accesses so the compiler and the kernel memory model understand what the programmer intended. That distinction matters, because data races are not just about two CPUs doing something surprising; they are also about the compiler being free to transform code in ways that make the source-level mental model false.
The Vulnerability Is in the Gap Between Locking and Reality
The Linux Bluetooth stack uses HCI commands to talk to controllers, whether they are USB dongles, laptop radios, combo Wi-Fi/Bluetooth chips, or virtualized devices. Synchronous command helpers are meant to provide a structured way to send a command and wait for a result. That machinery needs state, andhdev->req_status is one of the fields that says whether a request is pending, completed, canceled, or otherwise done.The problem described in CVE-2026-43119 is that
__hci_cmd_sync_sk() sets hdev->req_status while holding hdev->req_lock, but other functions touch the same field without that protection. hci_send_cmd_sync() reads it from command work. hci_cmd_sync_complete() reads and writes it when an HCI event completes. The cancellation helpers read and write it. hci_abort_conn() reads it during connection abort handling.That might sound like ordinary kernel messiness, but the CVE text makes the concurrency issue explicit:
__hci_cmd_sync_sk() runs on hdev->req_workqueue, while hci_send_cmd_sync() runs on hdev->workqueue. Those are not simply two call paths that happen not to overlap. They are separate workqueues that may run concurrently on different CPUs.This is why the issue is not fixed by optimism. If a field is shared between execution contexts, the code needs either locking, atomic operations, or explicit annotations that match the intended synchronization story. The Bluetooth code had a partially locked story, which is often more dangerous than an obviously unlocked one, because reviewers can see the lock and assume the invariant is stronger than it is.
The result is a data race, a phrase that has become more prominent in kernel CVEs because the kernel has spent years making its memory model more explicit. A data race does not automatically mean an attacker gets code execution. It means the program has concurrent plain accesses to the same memory location without a sufficient ordering or serialization guarantee, and at least one access is a write.
READ_ONCE and WRITE_ONCE Are Not Cosmetic Paint
The patch for CVE-2026-43119 usesREAD_ONCE() and WRITE_ONCE() around concurrent accesses to hdev->req_status. To a casual reader, that looks like the kernel equivalent of adding comments. It is not.READ_ONCE() tells the compiler to perform a single load from memory for that expression and not invent clever substitutions based on assumptions that are illegal in concurrent kernel code. WRITE_ONCE() similarly forces a single store and helps prevent transformations that could split, merge, elide, or reorder access in ways that break the intended behavior. These primitives are not full locks, but they are part of how Linux expresses shared-state access safely.The CVE description calls out two concrete compiler hazards: load fusing in a
wait_event condition and store reordering. Load fusing is particularly subtle. A programmer may write code expecting a value to be reread each time a wait condition is evaluated, while a compiler may decide that repeated loads from the same plain C object can be collapsed under its normal optimization rules.In single-threaded C, that optimization is often legal and desirable. In kernel code observing state updated by another CPU, it can turn a live wait into stale logic. The code looks as if it is polling shared state, but the generated machine code may not behave that way unless the access is marked.
That is the part of this CVE that deserves attention from IT pros who normally do not read Bluetooth patches. The bug is not a buffer overflow, a missing bounds check, or a wrong permission check. It is a mismatch between the code’s concurrency contract and the language/compiler contract. In a modern kernel, that mismatch is security-relevant.
The Absence of a CVSS Score Is Not a Reassurance
At publication, the NVD record for CVE-2026-43119 was awaiting enrichment and did not yet include NIST CVSS 4.0, CVSS 3.x, or CVSS 2.0 scoring. That lack of a score is easy to misread. It does not mean the bug is harmless; it means the scoring apparatus has not caught up with the disclosure.For administrators, CVSS is useful when it describes a fully understood vulnerability. It is less useful in the early hours of kernel CVE publication, especially for bugs like this one. A data race may be very hard to exploit directly, may manifest only under rare timing, or may become important only when combined with device behavior, driver quirks, or another bug.
The Linux kernel’s recent CVE practice has also made the ecosystem noisier. Many upstream fixes now receive CVE identifiers even when the practical exploitability is uncertain. That is good for traceability but frustrating for patch prioritization, because a terse kernel commit can suddenly become a vulnerability record before distributions have published their own severity judgments.
CVE-2026-43119 sits directly in that tension. The record describes a real race and a real fix. It does not, by itself, prove remote compromise, local privilege escalation, or a reliable denial-of-service path. But it does identify a condition in privileged kernel Bluetooth code where concurrent state handling was not expressed safely.
That makes it the kind of bug enterprises should patch through normal kernel update channels rather than panic over. It is not a headline emergency on the evidence currently available. It is also not something to wave away because the patch is small.
Bluetooth Keeps Becoming a Kernel Security Boundary
Bluetooth has always been awkward from a security perspective because it is both local and wireless. It is not “remote” in the Internet sense, but it does cross a physical boundary. It deals with untrusted devices, complex protocol states, and controller firmware that may not behave exactly as the host expects.On desktops, Bluetooth often means keyboards, mice, headphones, game controllers, phones, and wearables. On laptops, it may share silicon, power management, and firmware update paths with Wi-Fi. On embedded systems and kiosks, it may be enabled because the hardware platform ships that way, even if nobody thinks of it as part of the application.
The HCI layer is especially important because it is where the host stack talks to the controller. A bug in HCI synchronization does not automatically imply that a nearby attacker can exploit it over the air. But it does live in a part of the stack that processes asynchronous events and command completions from Bluetooth hardware.
That asynchronous nature is why races matter here. Bluetooth is not a neat request-response protocol executed by one thread in isolation. Commands are queued, events arrive, workqueues run, cancellations happen, connections abort, and error recovery may fire while other work is in progress.
The CVE’s mention of separate workqueues is therefore not a footnote. It is the architecture. The bug exists because two pieces of kernel work that sound related are not necessarily serialized by being “Bluetooth work.” They are scheduled in different places and can run at the same time.
This Is a Compiler-Aware Security Bug, Not Just a CPU Race
Many people still think of race conditions as timing accidents: CPU 1 writes, CPU 2 reads, and depending on who wins, the program behaves differently. CVE-2026-43119 is more nuanced. The concern includes what the compiler is allowed to do before the CPUs ever execute the code.The Linux kernel cannot pretend it is ordinary ISO C running in a single-threaded universe. It relies on carefully documented primitives to communicate ordering, atomicity, and visibility. When the code accesses shared state without those primitives, the compiler may optimize based on assumptions that are valid for normal C but dangerous for concurrent kernel execution.
This is why
READ_ONCE() and WRITE_ONCE() are meaningful even though they are not locks. They do not solve every memory ordering problem. They do, however, prevent a class of compiler transformations that would make lockless communication unreliable. They are the minimum vocabulary the kernel uses to say: this access is intentional, concurrent, and must happen as written.There is an important restraint in the fix. The patch does not appear to claim that
req_status needs a new synchronization design. It says that the existing concurrent accesses should be annotated to prevent compiler optimizations from affecting correctness. That is a narrower claim, but in security engineering, narrow claims are often the most credible ones.The danger for defenders is that narrow fixes can look unimportant on dashboards. A scanner sees a CVE. A ticket gets created. Someone asks for the CVSS score. If none exists, the item may be deferred. But the actual engineering signal is that upstream found shared kernel state whose access pattern needed to be made explicit.
Windows Shops Should Still Care About a Linux Bluetooth CVE
WindowsForum.com readers do not all run Linux on the desktop, but many run Linux somewhere. It may be in Hyper-V guests, WSL-adjacent development workflows, Proxmox hosts, Kubernetes nodes, NAS appliances, security cameras, lab machines, Steam Decks, routers, or dual-boot laptops. Bluetooth support may be enabled even when nobody is thinking about it.The Microsoft Security Response Center listing is also a reminder that vulnerability visibility no longer follows operating system tribal lines. Microsoft tracks CVEs affecting open-source components, cloud workloads, developer environments, and customer deployments that may sit adjacent to Windows estates. A Linux kernel Bluetooth flaw may matter to a Windows-centric organization because the fleet is no longer Windows-only.
The practical question is not whether every Windows admin should drop everything for CVE-2026-43119. They should not. The practical question is whether asset inventory, patch management, and exposure assumptions include Linux systems with Bluetooth-capable kernels. In many organizations, the answer is messier than the CMDB suggests.
For client devices, the risk calculus depends on whether Bluetooth is enabled and whether users pair with untrusted devices. For servers, the more important question is why Bluetooth is present at all. Many rack servers do not need it, but small-form-factor PCs, edge boxes, industrial systems, and repurposed desktop hardware often blur that line.
For virtualized and containerized environments, the situation is different again. Containers share the host kernel, so kernel vulnerabilities are patched at the host, not inside the container image. Virtual machines have their own kernels, but Bluetooth passthrough or USB device passthrough can create unexpected hardware exposure in labs and specialty deployments.
The Kernel CVE Firehose Rewards Process Over Drama
One reason CVE-2026-43119 feels anticlimactic is that the modern Linux kernel vulnerability pipeline increasingly assigns CVEs to fixes that are precise, technical, and not necessarily accompanied by exploit narratives. That shift has been controversial. It improves transparency and backport tracking, but it also produces records that security teams struggle to rank.The old model implicitly favored spectacular bugs. The new model captures more of the maintenance reality: use-after-free fixes, missing locks, incorrect lifetime rules, uninitialized values, and race annotations. The downside is that vulnerability databases can make every kernel patch sound equally ominous while withholding the context administrators need.
This is where distribution advisories still matter. Red Hat, Ubuntu, Debian, SUSE, Arch, Fedora, and downstream appliance vendors do the operational work of mapping upstream commits to shipped kernels, affected products, and support timelines. A CVE record tells you a vulnerability exists upstream. Your vendor’s kernel package tells you whether your machines are actually exposed and whether a fixed build is available.
The upstream stable references in the record indicate that the fix was applied across multiple maintained kernel lines. That is significant because Bluetooth bugs often span several versions, and the affected code may not be confined to bleeding-edge kernels. But the exact exposure for any given system depends on the kernel tree, configuration, backports, and vendor patches.
For enterprise IT, the right response is disciplined triage. Determine whether your Linux endpoints or appliances use affected kernel branches. Check whether Bluetooth is enabled or compiled in. Watch vendor advisories for severity and package availability. Then patch in the next appropriate maintenance window unless your environment has unusually high Bluetooth exposure.
The Exploit Story Is Still Mostly Hypothetical
There is no need to invent an exploit chain where the public record does not provide one. CVE-2026-43119 describes a data race and a correctness fix. It does not currently establish that an unauthenticated nearby attacker can reliably crash a machine, escalate privileges, or execute code.That caveat matters because Bluetooth vulnerabilities are easy to overhype. The word “Bluetooth” invites images of drive-by compromise from a parking lot. The word “kernel” invites the assumption of instant root. The reality is usually more constrained, more hardware-dependent, and more timing-sensitive.
At the same time, dismissing the bug because exploitability is unclear would be a mistake. Race conditions often become more interesting when attackers can influence scheduling, trigger repeated operations, or combine a fragile state machine with another bug. Kernel Bluetooth code has all the ingredients that make concurrency hard: asynchronous events, device state transitions, cancellation paths, and error handling.
The most honest assessment is that CVE-2026-43119 is a low-noise, technically real kernel race whose practical impact has not yet been fully characterized publicly. That makes it a patching issue, not a panic issue. It also makes it a useful case study in how security fixes now look when the vulnerability is less about a dramatic crash and more about making undefined behavior impossible.
The Small Patch Carries a Large Maintenance Message
The beauty and frustration of this CVE is that the fix is the kind of change many users will never notice. No new feature appears. No command-line tool changes. Bluetooth devices should not behave differently in any visible way. The kernel simply becomes more explicit about how a shared status field is accessed.That is exactly why such patches matter. Operating systems become secure not only through heroic mitigations and emergency zero-day fixes, but through thousands of small corrections that remove ambiguity. A compiler no longer gets to make a dangerous assumption. A workqueue interaction no longer depends on wishful thinking. A future maintainer sees the access pattern marked as concurrent.
This is also a reminder that lockless code has a documentation burden. If a field is intentionally read without a lock, the code should say so through the right primitive. If it is not intentional, the code should be locked. What is not sustainable is the middle ground where one path locks, another path does not, and everyone hopes the scheduler is kind.
For Linux users, the actionable advice is simple: take kernel updates seriously even when the CVE wording looks microscopic. For organizations, the strategic advice is broader: improve the path from upstream kernel CVE to local exposure decision. The faster you can answer “Do we run this code, in this configuration, on these machines?” the less you have to rely on generic severity scores.
The Real Signal in CVE-2026-43119 Is the Word “Workqueue”
Before this CVE disappears into the patch-management queue, it is worth pulling out the concrete operational lessons. They are not dramatic, but they are the difference between treating kernel CVEs as noise and treating them as useful telemetry.- CVE-2026-43119 affects Linux kernel Bluetooth HCI synchronization code around concurrent access to
hdev->req_status. - The published fix uses
READ_ONCE()andWRITE_ONCE()annotations rather than a broad redesign of the Bluetooth command path. - The risk comes from separate workqueues that can run concurrently on different CPUs, not from a single obviously broken call path.
- The NVD record was awaiting enrichment at publication, so the absence of a CVSS score should not be treated as proof of low impact.
- Systems with Bluetooth enabled, Bluetooth hardware present, or vendor kernels carrying the affected code should receive fixed kernel packages through normal update channels.
- Windows-centric environments should still inventory Linux hosts, appliances, developer machines, and edge systems where Bluetooth-capable kernels may be running outside the traditional desktop fleet.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center