CVE-2026-43191 is a newly published Linux kernel vulnerability from kernel.org, dated May 6, 2026, affecting AMD’s display driver path where DCN35 hardware can hang when TMDS output is disabled and a PHY PLL transition is not handled atomically. It is not a headline-grabbing remote-code-execution bug, and the NVD has not yet assigned a CVSS score. But it is exactly the kind of low-level graphics-stack flaw that matters to Linux desktop users, workstation owners, and administrators who learned long ago that “just a display bug” can still mean “the machine is gone.” The real story is not panic; it is the increasing visibility of kernel reliability fixes as security records in a world where GPU drivers now sit on the fault line between performance, power management, virtualization, and system availability.
The description of CVE-2026-43191 reads like a kernel commit message because that is essentially what it is. In the Linux kernel’s AMD display code, a fix titled “drm/amd/display: Adjust PHY FSM transition to TX_EN-to-PLL_ON for TMDS on DCN35” was assigned a CVE after being accepted into the stable stream. The issue centers on a backport from AMD’s newer DCN401 display code to DCN35, a display core generation used in recent AMD GPU and APU platforms.
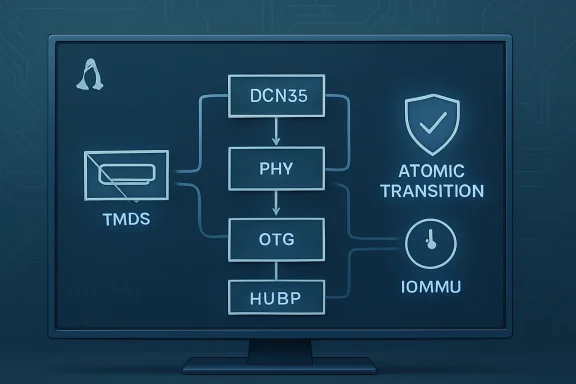
The immediate bug is narrow: when disabling TMDS output, the driver could turn off the PHY PLL in a way that left the OTG, or Output Timing Generator, stuck. TMDS is the signaling family historically associated with DVI and HDMI-style display output, while the PHY PLL is the clocking component that helps drive the physical display link. If those words sound obscure, that is the point: this vulnerability lives in the choreography between display hardware blocks that most users never see until their screen goes black and the system stops responding.
The kernel note says the stuck OTG can lead to a hang in DCHVM’s ability to acknowledge invalidations when it believes the HUBP is still on but is no longer receiving global sync. That is not a user-facing error message; it is a description of internal display pipeline state going incoherent. The important operational translation is simpler: under the wrong timing conditions, the graphics display pipeline can get stuck badly enough that the system may hang.
This is the sort of vulnerability that challenges the public’s mental model of CVEs. Many people hear CVE and imagine an exploit kit, a phishing chain, or a privilege-escalation primitive. Here the risk is availability, not data theft. Yet availability is one of the classic legs of security, and a reproducible machine hang can be a security problem when it can be triggered by local access, display hotplug behavior, or workload patterns that administrators cannot reliably control.
Kernel developers spend enormous effort hiding this kind of fragility from users. A modern display stack is not simply drawing pixels and sending them to a monitor. It is negotiating link training, clocks, power states, compression, color formats, panel self-refresh, audio over HDMI, variable refresh behavior, display hotplug events, and system-wide memory interactions. The more power-efficient and dynamic the hardware becomes, the more state transitions must be perfectly sequenced.
The bug’s shape is familiar to anyone who has debugged suspend/resume failures, multi-monitor black screens, or GPU resets that never quite recover. A subsystem saves power by turning something off. Another subsystem still believes it is alive. A timing generator waits for sync that never comes. A memory-management component waits for an acknowledgment that never arrives. The user sees none of this; the user sees a frozen desktop.
The fix is not described as adding a new permission check or blocking malicious input. It is a change to hardware state-machine handling: do the TX_EN-to-PLL_ON transition in a way that cannot be torn in half by scheduling. That distinction matters because it explains why the patch is both mundane and important. The vulnerability is not about a hacker smuggling code through HDMI. It is about a kernel driver making a promise to hardware and then being interrupted before the promise is fulfilled.
DCN, AMD’s Display Core Next architecture, is where much of that complexity lands. Each generation adds support for new display engines and platform behaviors, while also retaining compatibility with older signaling paths such as TMDS. The CVE’s reference to DCN35 and DCN401 is a reminder that fixes often travel sideways through the hardware family tree. A behavior corrected in one generation may need to be deliberately backported to another, but not always by copying code wholesale.
That last detail is unusually revealing. The kernel text says there is a functional difference in when eDP output is disabled in the DCN401 code, so the developers did not want to use that implementation directly. In other words, even closely related display hardware generations are not interchangeable abstractions. A fix can be conceptually shared but mechanically different.
This is why graphics bugs linger and why users sometimes experience regressions that seem impossible to reproduce outside a particular laptop, monitor, dock, cable, kernel version, and compositor. The Linux graphics stack is open, but open does not mean simple. It means the machinery is visible enough that, eventually, a one-line symptom can be traced back to a timing edge in a PHY finite-state machine.
For security teams, that creates noise. A vulnerability scanner may not know whether this is a practical threat to a headless server, a developer workstation, or a gaming laptop. A compliance dashboard may flatten “local display hang on AMD DCN35 with TMDS output” into the same red column as a network-facing flaw. The result is predictable: administrators either overreact to every kernel CVE or learn to tune out the category entirely.
But dismissing this record as mere CVE inflation would be too easy. The CVE label also does useful work. It gives distributions, vendors, managed fleets, and downstream advisories a common handle for tracking a fix that might otherwise disappear inside a large stable kernel release. It lets administrators ask a concrete question: does my kernel contain the stable commits that resolve CVE-2026-43191?
The weakness is not the existence of the CVE. The weakness is the ecosystem around it. NVD enrichment lag, absent CVSS data, and sparse vendor context leave users guessing about urgency. The record tells us what was fixed, but not enough about who is realistically exposed or how often the triggering condition occurs. That gap is where responsible IT judgment has to replace automated severity theater.
The CVE description points toward a hang involving invalidation acknowledgments and an IOMMU watchdog. That language matters because it places the problem beyond a harmless screen blank. The display subsystem’s state can interfere with a broader platform mechanism responsible for memory translation and device coordination. Once those layers start waiting on each other, recovery may be outside the reach of the desktop environment.
Administrators should resist two equal and opposite mistakes. The first is treating this as an internet-facing emergency. There is no evidence in the public description of remote exploitation, code execution, privilege escalation, or data exposure. The second mistake is ignoring it because it is “only graphics.” Anyone who has managed Linux laptops at scale knows that display hangs are among the most expensive bugs to diagnose precisely because they are intermittent, hardware-dependent, and often invisible to remote logging after the failure.
Security severity and operational severity are not always the same thing. CVE-2026-43191 may eventually receive a moderate or low score, depending on scoring assumptions. But in an affected environment with AMD DCN35 hardware and TMDS-connected displays, the practical severity could be high enough to justify prompt kernel updates.
That collision is part of the broader AMD Linux display story. Enthusiasts have spent years tracking HDMI limitations, display flickering, multi-monitor quirks, dock weirdness, and refresh-rate edge cases. Not all of those are related to this CVE, and it would be irresponsible to pretend every black screen on AMD Linux is CVE-2026-43191. But the vulnerability belongs to the same family of problems: display output is a hardware protocol negotiation, not a passive cable.
The specific failure when disabling TMDS output is also revealing. Users do not only “use” displays; they constantly transition them. Screens sleep. Laptops dock and undock. Compositors reconfigure outputs. Games change display modes. KVM switches move focus. HDMI receivers power-cycle. External monitors advertise new EDID data. A bug in output disablement is therefore not trapped in some rare shutdown path. It can live inside everyday behavior.
That is why an atomic state transition is not an academic nicety. The faster and more dynamic the desktop becomes, the more often these transitions happen under scheduling pressure. A graphics stack that works in a lab with one monitor may behave differently when the user is running a compositor, a browser using GPU acceleration, a game, a virtual machine, and a monitor that wakes slowly from sleep.
The backport dimension is important. The kernel description says the change was made for DCN401 and then adapted back to DCN35. That tells us the maintainers saw the pattern as relevant beyond one implementation. It also shows the care required to avoid creating a new bug while fixing the old one, since the eDP disable behavior differed between the two code paths.
For users, the stable-kernel process is both a blessing and a source of confusion. A fix may exist upstream before it appears in a distribution kernel. A rolling distribution may pick it up quickly, while an enterprise distribution may carry it as a vendor backport without changing the visible kernel version dramatically. A user searching only for a mainline version number may therefore reach the wrong conclusion.
This is where distribution advisories matter more than raw kernel archaeology. The practical question is not simply whether Linux has fixed CVE-2026-43191 in some branch. The practical question is whether your distribution’s kernel package includes the relevant amdgpu display fix. That answer will vary across Fedora, Ubuntu, Debian, Arch, openSUSE, enterprise rebuilds, appliance vendors, and custom kernels.
The second answer is that GPU-driver failure modes are cross-platform in spirit even when the codebases differ. Windows and Linux do not share the same AMD display driver stack, and this CVE is specifically about the Linux kernel’s drm/amd/display code. But the underlying pressures are familiar to anyone who has installed a Radeon driver update and watched a monitor fail to wake, flicker, lose audio, or renegotiate at the wrong refresh rate.
The third answer is operational. IT teams increasingly manage hardware, not just operating systems. A fleet may contain Windows workstations, Linux build machines, hypervisors, and developer laptops with nearly identical AMD platforms. If a display-engine erratum or driver sequencing problem appears in one OS, it may inform troubleshooting instincts across the fleet even when the patch paths differ.
That does not mean Windows users need to hunt for CVE-2026-43191 in Windows Update. Based on the public description, this is a Linux kernel vulnerability, not a Microsoft Windows display-driver advisory. The Microsoft Security Response Center may index CVE records broadly, but the fix described here lives in the Linux kernel’s AMD DRM driver.
The absence of a score should not be mistaken for absence of risk. It means the scoring authority has not completed its assessment. In the meantime, administrators have to read the vulnerability description, map it to their hardware, and decide whether the availability impact matters in their environment. That is slower than looking at a number, but it is also more accurate.
A likely triage path begins with exposure. Headless Linux servers without AMD display output are unlikely to care. Linux desktops, workstations, laptops, and HTPCs using AMD graphics with HDMI or DVI-style TMDS output deserve attention. Systems using docks, KVMs, adapters, or frequent monitor hotplug events deserve more attention, because they live in the world where display-output disable and re-enable paths are exercised often.
The next triage point is kernel sourcing. If you run a distribution kernel, watch your vendor’s security and kernel update channels. If you run mainline or custom kernels, verify whether the relevant stable commits are included. If you operate immutable or appliance-style Linux systems, the fix may arrive under a vendor bundle rather than an obvious kernel CVE line item.
The word “atomic” should also temper assumptions about reproducibility. Bugs involving pre-emption windows are notoriously timing-sensitive. One user may never hit the condition. Another may trigger it repeatedly with the same monitor, cable, compositor, and workload. A third may see it only after suspend, only through a KVM, or only when a display powers down under load.
That makes the fix more important, not less. A cleanly reproducible crash is at least easy to identify. A timing-dependent display hang can masquerade as a bad cable, a flaky monitor, a compositor regression, a BIOS issue, a power-management quirk, or a failing GPU. The patch collapses one branch of that diagnostic tree.
This also explains why kernel developers treat such fixes seriously even when they do not resemble classical security vulnerabilities. The kernel is the layer that must remain coherent when hardware does surprising things. If a display transition can wedge memory-invalidation acknowledgment long enough for a watchdog timeout, the driver contract has failed in a way users cannot reasonably work around.
For affected users, the practical mitigation is to install a kernel containing the fix. Temporary workarounds may include avoiding the TMDS path where possible, using DisplayPort instead of HDMI or DVI-style output, reducing hotplug churn, or disabling aggressive display sleep on systems that repeatedly hang. But those are operational bandages, not security remediation.
The distinction matters because Linux desktop users often become unpaid QA engineers for their own machines. They accumulate kernel parameters, compositor toggles, and monitor rituals that keep one setup stable. CVE-2026-43191 is a reminder that some failures are not configuration sins. Sometimes the driver simply needs a corrected transition sequence.
Enterprises should be especially careful about workaround folklore. If an AMD-based Linux workstation fleet is affected, the answer should not be a wiki page full of folk remedies. It should be a kernel update plan, a validation pass against common monitor and dock configurations, and clear guidance about which systems are in scope.
The kernel community optimizes for traceability and correctness. Security operations teams optimize for prioritization and action. Desktop users optimize for whether the machine wakes up tomorrow. A CVE like this touches all three audiences and satisfies none of them completely on its own.
What would better translation look like? It would say, plainly, that this is a Linux AMD display-driver availability issue affecting DCN35 TMDS output handling; that the plausible impact is a local system hang rather than remote compromise; that the fix is in specific stable kernel commits; and that distribution kernels may include the fix through backports. That context is not fluff. It is the difference between informed patching and dashboard panic.
Until the ecosystem provides that translation consistently, publications and community forums have to fill the gap. That is not ideal, but it is necessary. The modern vulnerability feed is too noisy for raw identifiers to be useful by themselves, and too important to ignore entirely.
A practical inventory pass should start with Linux systems using AMD GPUs or APUs. From there, narrow the focus to machines using HDMI, DVI, HDMI adapters, KVMs, docks, or display paths likely to exercise TMDS output. Laptops with only internal eDP panels may be less exposed to this specific TMDS path, though mixed internal and external display configurations deserve caution.
The next step is kernel validation. Rolling-release users may already have the fix if they are current, depending on timing and package selection. Enterprise and long-term-support users need to check vendor advisories and changelogs rather than assume their older version number is vulnerable or safe. Custom-kernel users should inspect whether the stable commits corresponding to the fix have been applied.
Finally, administrators should collect symptoms carefully. A machine that hangs during monitor sleep, HDMI disconnect, dock removal, KVM switching, display reconfiguration, or compositor mode changes may fit the pattern. A generic graphics crash under gaming load may not. The CVE is a useful lead, not a universal explanation for every AMD display complaint.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Display Patch Becomes a Security Event
A Display Patch Becomes a Security Event
The description of CVE-2026-43191 reads like a kernel commit message because that is essentially what it is. In the Linux kernel’s AMD display code, a fix titled “drm/amd/display: Adjust PHY FSM transition to TX_EN-to-PLL_ON for TMDS on DCN35” was assigned a CVE after being accepted into the stable stream. The issue centers on a backport from AMD’s newer DCN401 display code to DCN35, a display core generation used in recent AMD GPU and APU platforms.The immediate bug is narrow: when disabling TMDS output, the driver could turn off the PHY PLL in a way that left the OTG, or Output Timing Generator, stuck. TMDS is the signaling family historically associated with DVI and HDMI-style display output, while the PHY PLL is the clocking component that helps drive the physical display link. If those words sound obscure, that is the point: this vulnerability lives in the choreography between display hardware blocks that most users never see until their screen goes black and the system stops responding.
The kernel note says the stuck OTG can lead to a hang in DCHVM’s ability to acknowledge invalidations when it believes the HUBP is still on but is no longer receiving global sync. That is not a user-facing error message; it is a description of internal display pipeline state going incoherent. The important operational translation is simpler: under the wrong timing conditions, the graphics display pipeline can get stuck badly enough that the system may hang.
This is the sort of vulnerability that challenges the public’s mental model of CVEs. Many people hear CVE and imagine an exploit kit, a phishing chain, or a privilege-escalation primitive. Here the risk is availability, not data theft. Yet availability is one of the classic legs of security, and a reproducible machine hang can be a security problem when it can be triggered by local access, display hotplug behavior, or workload patterns that administrators cannot reliably control.
The Atomic Transition Is the Whole Bug
The phrase that matters most in the kernel description is “the transition to PLL_ON needs to be atomic.” That is the tell. The driver was moving hardware between states, but the sequence was vulnerable to interruption: the executing thread could be pre-empted before completing the transition, and the IOMMU watchdog could time out before the display subsystem recovered into a coherent state.Kernel developers spend enormous effort hiding this kind of fragility from users. A modern display stack is not simply drawing pixels and sending them to a monitor. It is negotiating link training, clocks, power states, compression, color formats, panel self-refresh, audio over HDMI, variable refresh behavior, display hotplug events, and system-wide memory interactions. The more power-efficient and dynamic the hardware becomes, the more state transitions must be perfectly sequenced.
The bug’s shape is familiar to anyone who has debugged suspend/resume failures, multi-monitor black screens, or GPU resets that never quite recover. A subsystem saves power by turning something off. Another subsystem still believes it is alive. A timing generator waits for sync that never comes. A memory-management component waits for an acknowledgment that never arrives. The user sees none of this; the user sees a frozen desktop.
The fix is not described as adding a new permission check or blocking malicious input. It is a change to hardware state-machine handling: do the TX_EN-to-PLL_ON transition in a way that cannot be torn in half by scheduling. That distinction matters because it explains why the patch is both mundane and important. The vulnerability is not about a hacker smuggling code through HDMI. It is about a kernel driver making a promise to hardware and then being interrupted before the promise is fulfilled.
AMD’s Linux Display Stack Is Carrying More of the Platform
AMD’s open Linux graphics stack has matured dramatically over the past decade. The amdgpu driver is not a hobbyist side road; it is the default path for Radeon graphics, Ryzen APUs, handheld gaming PCs, Linux gaming rigs, workstations, and an expanding set of OEM devices. That success also means AMD’s display code is now exposed to more monitors, docks, adapters, kernels, compositors, refresh rates, and user expectations than ever before.DCN, AMD’s Display Core Next architecture, is where much of that complexity lands. Each generation adds support for new display engines and platform behaviors, while also retaining compatibility with older signaling paths such as TMDS. The CVE’s reference to DCN35 and DCN401 is a reminder that fixes often travel sideways through the hardware family tree. A behavior corrected in one generation may need to be deliberately backported to another, but not always by copying code wholesale.
That last detail is unusually revealing. The kernel text says there is a functional difference in when eDP output is disabled in the DCN401 code, so the developers did not want to use that implementation directly. In other words, even closely related display hardware generations are not interchangeable abstractions. A fix can be conceptually shared but mechanically different.
This is why graphics bugs linger and why users sometimes experience regressions that seem impossible to reproduce outside a particular laptop, monitor, dock, cable, kernel version, and compositor. The Linux graphics stack is open, but open does not mean simple. It means the machinery is visible enough that, eventually, a one-line symptom can be traced back to a timing edge in a PHY finite-state machine.
The CVE Label Is Doing Two Jobs at Once
There is a legitimate debate over whether every kernel reliability fix deserves a CVE. The Linux kernel community’s more expansive approach has produced a flood of records that can look absurd to enterprise scanners: thousands of kernel CVEs, many with terse commit-message descriptions and incomplete severity data. CVE-2026-43191 arrives with NVD enrichment still pending, no NVD CVSS score, and a description that requires display-driver literacy to parse.For security teams, that creates noise. A vulnerability scanner may not know whether this is a practical threat to a headless server, a developer workstation, or a gaming laptop. A compliance dashboard may flatten “local display hang on AMD DCN35 with TMDS output” into the same red column as a network-facing flaw. The result is predictable: administrators either overreact to every kernel CVE or learn to tune out the category entirely.
But dismissing this record as mere CVE inflation would be too easy. The CVE label also does useful work. It gives distributions, vendors, managed fleets, and downstream advisories a common handle for tracking a fix that might otherwise disappear inside a large stable kernel release. It lets administrators ask a concrete question: does my kernel contain the stable commits that resolve CVE-2026-43191?
The weakness is not the existence of the CVE. The weakness is the ecosystem around it. NVD enrichment lag, absent CVSS data, and sparse vendor context leave users guessing about urgency. The record tells us what was fixed, but not enough about who is realistically exposed or how often the triggering condition occurs. That gap is where responsible IT judgment has to replace automated severity theater.
Availability Bugs Are Still Security Bugs When the Machine Stops
A system hang is not as dramatic as credential theft, but it is not benign. On a single-user desktop, it means lost work and a forced reboot. On a workstation running long jobs, it can mean corrupted output, missed deadlines, and hours of diagnostic churn. On a kiosk, trading floor, lab machine, signage system, classroom fleet, or remote office workstation, availability is not a luxury feature.The CVE description points toward a hang involving invalidation acknowledgments and an IOMMU watchdog. That language matters because it places the problem beyond a harmless screen blank. The display subsystem’s state can interfere with a broader platform mechanism responsible for memory translation and device coordination. Once those layers start waiting on each other, recovery may be outside the reach of the desktop environment.
Administrators should resist two equal and opposite mistakes. The first is treating this as an internet-facing emergency. There is no evidence in the public description of remote exploitation, code execution, privilege escalation, or data exposure. The second mistake is ignoring it because it is “only graphics.” Anyone who has managed Linux laptops at scale knows that display hangs are among the most expensive bugs to diagnose precisely because they are intermittent, hardware-dependent, and often invisible to remote logging after the failure.
Security severity and operational severity are not always the same thing. CVE-2026-43191 may eventually receive a moderate or low score, depending on scoring assumptions. But in an affected environment with AMD DCN35 hardware and TMDS-connected displays, the practical severity could be high enough to justify prompt kernel updates.
The HDMI Legacy Path Keeps Showing Up in Modern Bugs
TMDS is old technology by computing standards, but it is not obsolete in the environments that matter. HDMI displays, DVI adapters, KVM switches, conference-room gear, capture devices, docks, and embedded panels continue to rely on legacy display signaling paths or compatibility modes. Modern GPUs must therefore support both the new and the old, often simultaneously, while users expect hotplugging and power management to behave perfectly.That collision is part of the broader AMD Linux display story. Enthusiasts have spent years tracking HDMI limitations, display flickering, multi-monitor quirks, dock weirdness, and refresh-rate edge cases. Not all of those are related to this CVE, and it would be irresponsible to pretend every black screen on AMD Linux is CVE-2026-43191. But the vulnerability belongs to the same family of problems: display output is a hardware protocol negotiation, not a passive cable.
The specific failure when disabling TMDS output is also revealing. Users do not only “use” displays; they constantly transition them. Screens sleep. Laptops dock and undock. Compositors reconfigure outputs. Games change display modes. KVM switches move focus. HDMI receivers power-cycle. External monitors advertise new EDID data. A bug in output disablement is therefore not trapped in some rare shutdown path. It can live inside everyday behavior.
That is why an atomic state transition is not an academic nicety. The faster and more dynamic the desktop becomes, the more often these transitions happen under scheduling pressure. A graphics stack that works in a lab with one monitor may behave differently when the user is running a compositor, a browser using GPU acceleration, a game, a virtual machine, and a monitor that wakes slowly from sleep.
Stable Backports Are Where the Real Linux Desktop Is Made
The patch behind CVE-2026-43191 did not arrive as a glossy driver release with a marketing bullet. It moved through the Linux graphics and stable-kernel machinery. There was an upstream commit, then stable backporting activity, and eventually a CVE record from kernel.org. This is how a large portion of Linux desktop reliability actually improves: incrementally, through narrowly scoped fixes that rarely make headlines unless they break something.The backport dimension is important. The kernel description says the change was made for DCN401 and then adapted back to DCN35. That tells us the maintainers saw the pattern as relevant beyond one implementation. It also shows the care required to avoid creating a new bug while fixing the old one, since the eDP disable behavior differed between the two code paths.
For users, the stable-kernel process is both a blessing and a source of confusion. A fix may exist upstream before it appears in a distribution kernel. A rolling distribution may pick it up quickly, while an enterprise distribution may carry it as a vendor backport without changing the visible kernel version dramatically. A user searching only for a mainline version number may therefore reach the wrong conclusion.
This is where distribution advisories matter more than raw kernel archaeology. The practical question is not simply whether Linux has fixed CVE-2026-43191 in some branch. The practical question is whether your distribution’s kernel package includes the relevant amdgpu display fix. That answer will vary across Fedora, Ubuntu, Debian, Arch, openSUSE, enterprise rebuilds, appliance vendors, and custom kernels.
Windows Users Should Still Pay Attention
WindowsForum.com readers may reasonably ask why a Linux kernel CVE belongs in their feed. The first answer is straightforward: many Windows users now run Linux too, whether through dual-boot gaming rigs, home labs, developer laptops, WSL-adjacent workflows, SteamOS-like devices, Proxmox hosts with GPU passthrough, or mixed fleets where Windows and Linux machines sit side by side. The desktop OS border is more porous than it used to be.The second answer is that GPU-driver failure modes are cross-platform in spirit even when the codebases differ. Windows and Linux do not share the same AMD display driver stack, and this CVE is specifically about the Linux kernel’s drm/amd/display code. But the underlying pressures are familiar to anyone who has installed a Radeon driver update and watched a monitor fail to wake, flicker, lose audio, or renegotiate at the wrong refresh rate.
The third answer is operational. IT teams increasingly manage hardware, not just operating systems. A fleet may contain Windows workstations, Linux build machines, hypervisors, and developer laptops with nearly identical AMD platforms. If a display-engine erratum or driver sequencing problem appears in one OS, it may inform troubleshooting instincts across the fleet even when the patch paths differ.
That does not mean Windows users need to hunt for CVE-2026-43191 in Windows Update. Based on the public description, this is a Linux kernel vulnerability, not a Microsoft Windows display-driver advisory. The Microsoft Security Response Center may index CVE records broadly, but the fix described here lives in the Linux kernel’s AMD DRM driver.
The NVD Gap Leaves Administrators in the Dark
At publication, the CVE record is marked as awaiting NVD enrichment, and the NVD has not supplied CVSS 4.0, CVSS 3.x, or CVSS 2.0 scoring. That is not unusual for fresh kernel CVEs, but it is inconvenient. Security teams have built workflows around severity ratings, and here the official scorecard is blank precisely when triage decisions need to be made.The absence of a score should not be mistaken for absence of risk. It means the scoring authority has not completed its assessment. In the meantime, administrators have to read the vulnerability description, map it to their hardware, and decide whether the availability impact matters in their environment. That is slower than looking at a number, but it is also more accurate.
A likely triage path begins with exposure. Headless Linux servers without AMD display output are unlikely to care. Linux desktops, workstations, laptops, and HTPCs using AMD graphics with HDMI or DVI-style TMDS output deserve attention. Systems using docks, KVMs, adapters, or frequent monitor hotplug events deserve more attention, because they live in the world where display-output disable and re-enable paths are exercised often.
The next triage point is kernel sourcing. If you run a distribution kernel, watch your vendor’s security and kernel update channels. If you run mainline or custom kernels, verify whether the relevant stable commits are included. If you operate immutable or appliance-style Linux systems, the fix may arrive under a vendor bundle rather than an obvious kernel CVE line item.
The Risk Is Narrow, but the Failure Mode Is Ugly
The best reading of CVE-2026-43191 is that it is a targeted availability flaw in a specific hardware-driver path. The worst reading is that it can freeze a machine in a way that looks like random GPU instability. Both can be true. Narrow bugs are still painful when they sit in high-frequency code paths used by real hardware.The word “atomic” should also temper assumptions about reproducibility. Bugs involving pre-emption windows are notoriously timing-sensitive. One user may never hit the condition. Another may trigger it repeatedly with the same monitor, cable, compositor, and workload. A third may see it only after suspend, only through a KVM, or only when a display powers down under load.
That makes the fix more important, not less. A cleanly reproducible crash is at least easy to identify. A timing-dependent display hang can masquerade as a bad cable, a flaky monitor, a compositor regression, a BIOS issue, a power-management quirk, or a failing GPU. The patch collapses one branch of that diagnostic tree.
This also explains why kernel developers treat such fixes seriously even when they do not resemble classical security vulnerabilities. The kernel is the layer that must remain coherent when hardware does surprising things. If a display transition can wedge memory-invalidation acknowledgment long enough for a watchdog timeout, the driver contract has failed in a way users cannot reasonably work around.
This Is Not the Moment for Cable Folklore
Display bugs invite superstition. Swap the cable. Disable VRR. Change the refresh rate. Avoid HDMI. Turn off sleep. Pin the kernel. Use DisplayPort. Unplug the second monitor. Some of that advice may help in particular cases, but it is not a substitute for a driver fix when the documented problem is a bad hardware state transition.For affected users, the practical mitigation is to install a kernel containing the fix. Temporary workarounds may include avoiding the TMDS path where possible, using DisplayPort instead of HDMI or DVI-style output, reducing hotplug churn, or disabling aggressive display sleep on systems that repeatedly hang. But those are operational bandages, not security remediation.
The distinction matters because Linux desktop users often become unpaid QA engineers for their own machines. They accumulate kernel parameters, compositor toggles, and monitor rituals that keep one setup stable. CVE-2026-43191 is a reminder that some failures are not configuration sins. Sometimes the driver simply needs a corrected transition sequence.
Enterprises should be especially careful about workaround folklore. If an AMD-based Linux workstation fleet is affected, the answer should not be a wiki page full of folk remedies. It should be a kernel update plan, a validation pass against common monitor and dock configurations, and clear guidance about which systems are in scope.
The Kernel CVE Flood Needs Better Translation
CVE-2026-43191 is part of a larger communications problem around Linux security. Kernel.org can publish a precise technical record, NVD can lag behind on enrichment, distributions can backport fixes under their own package versions, and end users can be left staring at an identifier with no score and a paragraph full of acronyms. That is not a failure of any one party. It is a failure of translation across layers.The kernel community optimizes for traceability and correctness. Security operations teams optimize for prioritization and action. Desktop users optimize for whether the machine wakes up tomorrow. A CVE like this touches all three audiences and satisfies none of them completely on its own.
What would better translation look like? It would say, plainly, that this is a Linux AMD display-driver availability issue affecting DCN35 TMDS output handling; that the plausible impact is a local system hang rather than remote compromise; that the fix is in specific stable kernel commits; and that distribution kernels may include the fix through backports. That context is not fluff. It is the difference between informed patching and dashboard panic.
Until the ecosystem provides that translation consistently, publications and community forums have to fill the gap. That is not ideal, but it is necessary. The modern vulnerability feed is too noisy for raw identifiers to be useful by themselves, and too important to ignore entirely.
The Patch Notes Tell Administrators Where to Look
For administrators trying to act on CVE-2026-43191, the most useful clues are in the wording. The affected area isdrm/amd/display, specifically the DCN35 hardware sequencing code. The trigger involves disabling TMDS output. The failure involves the PHY PLL, OTG, DCHVM invalidation acknowledgments, HUBP state, global sync, and the IOMMU watchdog. Those nouns are not decorative; they define the blast radius.A practical inventory pass should start with Linux systems using AMD GPUs or APUs. From there, narrow the focus to machines using HDMI, DVI, HDMI adapters, KVMs, docks, or display paths likely to exercise TMDS output. Laptops with only internal eDP panels may be less exposed to this specific TMDS path, though mixed internal and external display configurations deserve caution.
The next step is kernel validation. Rolling-release users may already have the fix if they are current, depending on timing and package selection. Enterprise and long-term-support users need to check vendor advisories and changelogs rather than assume their older version number is vulnerable or safe. Custom-kernel users should inspect whether the stable commits corresponding to the fix have been applied.
Finally, administrators should collect symptoms carefully. A machine that hangs during monitor sleep, HDMI disconnect, dock removal, KVM switching, display reconfiguration, or compositor mode changes may fit the pattern. A generic graphics crash under gaming load may not. The CVE is a useful lead, not a universal explanation for every AMD display complaint.
The Signal Hidden Inside This Small AMD Display CVE
The concrete lesson of CVE-2026-43191 is not that AMD graphics on Linux are unsafe. It is that the display stack has become a security-relevant availability surface, and kernel maintenance now exposes that fact one CVE at a time. This record is narrow enough to avoid panic but specific enough to deserve action where the hardware and display path match.- Systems running Linux with AMD DCN35-era graphics and TMDS-style output are the machines most worth checking first.
- The public record describes a hang condition, not remote code execution or data theft.
- The NVD had not provided a CVSS score at the time the record appeared, so administrators need to triage by exposure rather than by number.
- The proper remediation is a kernel update containing the AMD display-driver fix, preferably through the system’s normal distribution channel.
- Workarounds such as avoiding HDMI-style output may reduce risk temporarily, but they should not replace patching.
- Windows systems are not the target of this Linux kernel driver CVE, though mixed-platform AMD fleets should still track the hardware lesson.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center