CVE-2026-43198 is a Linux kernel TCP/IPv6 race-condition flaw disclosed by kernel.org and published in NVD on May 6, 2026, involving tcp_v6_syn_recv_sock(), where a newly created child socket can become visible to other CPUs before its IPv6 state is fully initialized. That sounds like an obscure corner of the networking stack, because it is. But the bug is also a neat example of why modern kernel security increasingly turns on ordering, visibility, and concurrency rather than cartoonish buffer overflows. The fix is small; the lesson for Linux fleet owners is not.
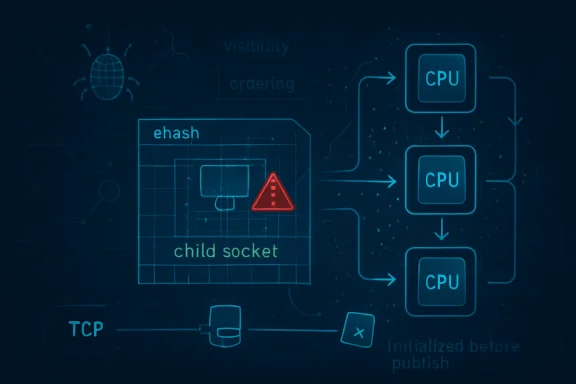
The core of CVE-2026-43198 is a timing mistake in the Linux TCP stack. In the vulnerable path, tcp_v6_syn_recv_sock() calls tcp_v4_syn_recv_sock(), which creates a child socket for a new TCP connection. The problem is that tcp_v4_syn_recv_sock() can insert that child socket into the established-hash table before the IPv6-specific fields have been corrected.
That ehash insertion matters because it is the moment the child socket becomes visible to other CPUs. Once a socket is in that table, other kernel code may find it, inspect it, and act on it. The kernel was effectively publishing an object while part of the object still pointed at the listener’s IPv6 state rather than the child socket’s own state.
The vulnerable window is narrow, but concurrency bugs live in narrow windows. On a busy multi-core system, “narrow” is not the same thing as “theoretical.” The report was surfaced by syzbot, the automated kernel fuzzing infrastructure that has become one of the Linux project’s most reliable finders of exactly this class of bug.
The patch moves the problematic IPv6-mapped child initialization into a helper named tcp_v6_mapped_child_init(), called earlier from tcp_v4_syn_recv_sock() before the ehash insertion. In plain English: initialize the child before putting it where the rest of the kernel can see it.
That would be the wrong instinct. The useful signal here is not a polished CVSS vector; it is the kernel commit language. The commit says the code after tcp_v4_syn_recv_sock() was “done too late,” that the child socket was already visible from the TCP ehash table, and that “bad things can happen,” as syzbot found. Kernel maintainers are not in the habit of writing breathless advisories, so the understated prose is itself meaningful.
This is also why Linux vulnerability management has become more uncomfortable for enterprises. The kernel’s CNA process now turns many upstream fixes into CVEs, sometimes before downstream distributions have attached the familiar labels security teams expect. The result is a widening gap between the engineering truth and the spreadsheet truth.
The engineering truth is that a race in TCP socket creation has been fixed. The spreadsheet truth, for now, is that the NVD record has no score. If your patch policy depends only on the latter, you are already behind the people maintaining the code.
Modern Linux servers often listen on IPv6 sockets capable of receiving IPv4-mapped connections, depending on application configuration and system defaults. In those cases, the boundary between IPv4 and IPv6 handling is not a clean architectural wall. It is a code path full of compatibility decisions made so applications can accept traffic without caring too much about address family details.
That convenience is usually a win. But it also means a vulnerability with “v6” in the function name can matter in environments whose operators believe they are mostly IPv4 shops. Dual-stack behavior has a way of turning assumptions into attack surface.
The practical takeaway is not “disable IPv6 everywhere,” a reflexive answer that often breaks more than it fixes. The better answer is to inventory which hosts expose TCP services on dual-stack sockets, which kernels they run, and whether their distribution has pulled in the stable fix.
That timeline is worth dwelling on. The bug did not need a public exploit to become a security issue. It needed an automated system capable of forcing weird interleavings in kernel code and a maintainer community willing to treat those findings as real defects.
This is the world kernel security now occupies. Memory safety remains important, but concurrency safety is just as unforgiving. A field initialized a few instructions too late can create an object lifetime or state-consistency problem that only appears under pressure, on the right hardware, with the right timing.
Security teams accustomed to vulnerability descriptions that say “remote code execution” or “privilege escalation” may find this unsatisfying. But kernel maintainers do not patch races in the TCP connection path for sport. The absence of a public exploit chain does not make the bug benign; it simply means the published record has not yet translated the engineering risk into a familiar security headline.
That is what a good kernel fix often looks like. The more dramatic a networking patch appears, the more nervous operators should become about regressions. Here, the fix aligns the lifecycle of the child socket with the kernel’s visibility rules: prepare the object first, then publish it.
There is a deep lesson in that ordering. High-performance networking stacks are built to avoid unnecessary locks, and Linux TCP has spent decades shaving overhead from connection setup. That performance pressure creates code paths where objects are born, referenced, hashed, and handed to other CPUs with very little ceremony.
The vulnerability sits in precisely that tension. TCP connection setup must be fast, especially on systems handling large numbers of short-lived connections. But speed does not excuse publishing partially initialized state. In kernel space, once another CPU can see an object, the object has to be ready for all the things that CPU is legally allowed to do.
The most obvious consumer context is Windows Subsystem for Linux, but it is not the only one. Azure, Linux-based appliances, container hosts, and Microsoft-maintained Linux images have made “Linux kernel bug” a relevant phrase inside Microsoft’s security ecosystem. The old Windows-versus-Linux taxonomy is less useful when the same enterprise laptop may run Windows 11, WSL, Docker workloads, and cloud-managed Linux guests in the same working day.
That does not mean CVE-2026-43198 is a Windows TCP/IP vulnerability. It is not tcpip.sys, and administrators should not confuse it with Windows-native TCP/IP issues. It is a Linux kernel networking flaw that appears in a Microsoft vulnerability guide because Microsoft has Linux customers to guide.
For WindowsForum readers, that distinction matters. If you are managing Windows endpoints with WSL enabled, Linux developer workstations, Hyper-V guests, or Azure Linux fleets, this CVE belongs on your radar. If you are managing only conventional Windows hosts with no Linux kernel exposure, the operational path is different.
That should keep the response measured. This is not a reason to tear down dual-stack networking overnight or make emergency firewall changes without testing. Race bugs in kernel networking can be serious, but they also need careful translation into actual exposure: kernel version, enabled code paths, reachable services, packet path, and distro backport status.
The right operational posture is disciplined urgency. Treat the fix as security-relevant, prioritize internet-facing Linux systems and high-throughput internal services, and monitor your distribution advisories. But do not invent a severity rating that the public record has not yet established.
This is where IT teams earn their keep. The job is not to panic before NVD enrichment lands, nor to wait passively for a CVSS score to bless reality. The job is to map an upstream kernel fix onto your fleet faster than attackers can map it onto their testing rigs.
That means the question “am I affected?” will not always be answered by comparing your kernel version to a mainline tag. A Red Hat, Ubuntu, Debian, SUSE, Oracle, Amazon, or Azure kernel may carry the fix while presenting a version string that appears older. Conversely, a custom kernel or appliance build may miss the fix even if it looks superficially modern.
Administrators should look for distribution advisories and package changelogs that mention CVE-2026-43198 or the tcp_v6_syn_recv_sock() race fix. If those are not available yet, the next best signal is whether the relevant stable commit has landed in the vendor’s kernel source package. In larger environments, this is a case for vulnerability management teams and Linux platform engineers to work together rather than fire tickets at each other.
Container users should also avoid a common mistake. Updating a container image usually does not update the host kernel. If the vulnerable code is in the host kernel, the fix belongs in the host OS, node image, hypervisor guest, or managed Kubernetes node pool—not merely in application containers.
The most exposed systems are likely those accepting TCP connections at scale, particularly internet-facing Linux hosts and dual-stack services. Load balancers, proxies, web servers, mail gateways, VPN concentrators, Kubernetes ingress nodes, and service meshes all deserve earlier attention than a developer VM hidden behind a NAT. The vulnerable path is in connection establishment, so listening services matter.
Network controls cannot reliably “filter out” a race inside socket creation, but they can reduce who can reach the vulnerable path. Restricting unnecessary listening ports, tightening security groups, pruning stale IPv6 exposure, and removing accidental dual-stack bindings are all sensible hygiene steps. These are not substitutes for the patch; they are ways to narrow the blast radius while the patch moves through change control.
The most useful mitigation may be observability. If a kernel update causes regressions in TCP handling, teams need to know quickly. If suspicious connection storms hit unpatched services, teams need enough telemetry to separate ordinary internet background noise from targeted probing.
The gap between those worlds is now a risk of its own. Attackers can read commits too. They do not need NVD to tell them that a race in TCP child socket initialization is worth studying. They can diff the patch, identify the changed ordering, and test whether reachable services can be coerced into the bad interleaving.
Defenders should not pretend every kernel CVE is equally urgent. The flood of Linux CVE assignments has made that impossible. But defenders also cannot outsource prioritization entirely to enrichment pipelines. A vulnerability in a driver for obscure hardware and a vulnerability in TCP connection setup are not the same kind of problem, even if both spend a few days with no NVD score.
The better model is contextual triage. Code path, exposure, subsystem, exploit preconditions, vendor patch availability, and fleet role should all carry weight. CVE-2026-43198 lands in a subsystem that many servers expose by design, which is why it deserves attention before the paperwork is complete.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Socket Became Public Before It Was Ready
A Socket Became Public Before It Was Ready
The core of CVE-2026-43198 is a timing mistake in the Linux TCP stack. In the vulnerable path, tcp_v6_syn_recv_sock() calls tcp_v4_syn_recv_sock(), which creates a child socket for a new TCP connection. The problem is that tcp_v4_syn_recv_sock() can insert that child socket into the established-hash table before the IPv6-specific fields have been corrected.That ehash insertion matters because it is the moment the child socket becomes visible to other CPUs. Once a socket is in that table, other kernel code may find it, inspect it, and act on it. The kernel was effectively publishing an object while part of the object still pointed at the listener’s IPv6 state rather than the child socket’s own state.
The vulnerable window is narrow, but concurrency bugs live in narrow windows. On a busy multi-core system, “narrow” is not the same thing as “theoretical.” The report was surfaced by syzbot, the automated kernel fuzzing infrastructure that has become one of the Linux project’s most reliable finders of exactly this class of bug.
The patch moves the problematic IPv6-mapped child initialization into a helper named tcp_v6_mapped_child_init(), called earlier from tcp_v4_syn_recv_sock() before the ehash insertion. In plain English: initialize the child before putting it where the rest of the kernel can see it.
The CVE Is Sparse Because the Kernel Is Telling a Different Story
As of publication, NVD marks the record as awaiting enrichment. There is no NVD CVSS score, no NIST severity rating, and no completed weakness enumeration. That absence will tempt some readers to treat CVE-2026-43198 as operationally unimportant.That would be the wrong instinct. The useful signal here is not a polished CVSS vector; it is the kernel commit language. The commit says the code after tcp_v4_syn_recv_sock() was “done too late,” that the child socket was already visible from the TCP ehash table, and that “bad things can happen,” as syzbot found. Kernel maintainers are not in the habit of writing breathless advisories, so the understated prose is itself meaningful.
This is also why Linux vulnerability management has become more uncomfortable for enterprises. The kernel’s CNA process now turns many upstream fixes into CVEs, sometimes before downstream distributions have attached the familiar labels security teams expect. The result is a widening gap between the engineering truth and the spreadsheet truth.
The engineering truth is that a race in TCP socket creation has been fixed. The spreadsheet truth, for now, is that the NVD record has no score. If your patch policy depends only on the latter, you are already behind the people maintaining the code.
IPv6-Mapped Traffic Turns a Small Bug Into a Fleet Question
The affected function name points directly at IPv6, but administrators should be careful not to file this mentally under “IPv6-only.” The interesting path here involves IPv6 handling around sockets that also intersect with IPv4 behavior, including IPv6-mapped child initialization. That is exactly the kind of dual-stack plumbing many organizations run without thinking about it.Modern Linux servers often listen on IPv6 sockets capable of receiving IPv4-mapped connections, depending on application configuration and system defaults. In those cases, the boundary between IPv4 and IPv6 handling is not a clean architectural wall. It is a code path full of compatibility decisions made so applications can accept traffic without caring too much about address family details.
That convenience is usually a win. But it also means a vulnerability with “v6” in the function name can matter in environments whose operators believe they are mostly IPv4 shops. Dual-stack behavior has a way of turning assumptions into attack surface.
The practical takeaway is not “disable IPv6 everywhere,” a reflexive answer that often breaks more than it fixes. The better answer is to inventory which hosts expose TCP services on dual-stack sockets, which kernels they run, and whether their distribution has pulled in the stable fix.
Syzbot Is Now Part of the Security Boundary
The most important actor in this story may not be an attacker, a vendor, or a researcher with a branded logo. It is syzbot. The automated fuzzing system found a Kernel Concurrency Sanitizer data-race report involving tcp_assign_congestion_control and tcp_v6_syn_recv_sock(), with the report landing in February 2026 and the fix later referenced by the CVE record.That timeline is worth dwelling on. The bug did not need a public exploit to become a security issue. It needed an automated system capable of forcing weird interleavings in kernel code and a maintainer community willing to treat those findings as real defects.
This is the world kernel security now occupies. Memory safety remains important, but concurrency safety is just as unforgiving. A field initialized a few instructions too late can create an object lifetime or state-consistency problem that only appears under pressure, on the right hardware, with the right timing.
Security teams accustomed to vulnerability descriptions that say “remote code execution” or “privilege escalation” may find this unsatisfying. But kernel maintainers do not patch races in the TCP connection path for sport. The absence of a public exploit chain does not make the bug benign; it simply means the published record has not yet translated the engineering risk into a familiar security headline.
The Fix Is Surgical, Which Is Exactly Why It Matters
The patch does not redesign TCP. It does not add a giant mitigation layer or introduce a new administrator-facing knob. It moves initialization earlier, before publication, and removes a redundant tcp_sync_mss() call because the later context is no longer the right one.That is what a good kernel fix often looks like. The more dramatic a networking patch appears, the more nervous operators should become about regressions. Here, the fix aligns the lifecycle of the child socket with the kernel’s visibility rules: prepare the object first, then publish it.
There is a deep lesson in that ordering. High-performance networking stacks are built to avoid unnecessary locks, and Linux TCP has spent decades shaving overhead from connection setup. That performance pressure creates code paths where objects are born, referenced, hashed, and handed to other CPUs with very little ceremony.
The vulnerability sits in precisely that tension. TCP connection setup must be fast, especially on systems handling large numbers of short-lived connections. But speed does not excuse publishing partially initialized state. In kernel space, once another CPU can see an object, the object has to be ready for all the things that CPU is legally allowed to do.
Microsoft’s Appearance in the Story Is a Windows Subsystem Reminder
The user-facing source for many Windows administrators is the Microsoft Security Response Center entry, not kernel.org. That can look odd at first glance: why is Microsoft tracking a Linux kernel CVE? The answer is that Microsoft now ships, hosts, or depends on Linux in enough places that Linux kernel vulnerabilities can become Microsoft customer guidance.The most obvious consumer context is Windows Subsystem for Linux, but it is not the only one. Azure, Linux-based appliances, container hosts, and Microsoft-maintained Linux images have made “Linux kernel bug” a relevant phrase inside Microsoft’s security ecosystem. The old Windows-versus-Linux taxonomy is less useful when the same enterprise laptop may run Windows 11, WSL, Docker workloads, and cloud-managed Linux guests in the same working day.
That does not mean CVE-2026-43198 is a Windows TCP/IP vulnerability. It is not tcpip.sys, and administrators should not confuse it with Windows-native TCP/IP issues. It is a Linux kernel networking flaw that appears in a Microsoft vulnerability guide because Microsoft has Linux customers to guide.
For WindowsForum readers, that distinction matters. If you are managing Windows endpoints with WSL enabled, Linux developer workstations, Hyper-V guests, or Azure Linux fleets, this CVE belongs on your radar. If you are managing only conventional Windows hosts with no Linux kernel exposure, the operational path is different.
The Risk Is Real, but the Hype Should Stay Outside the Change Window
There is no public NVD severity score yet. The CVE text does not claim known exploitation. The available technical record describes a race condition found by syzbot and fixed upstream, not a weaponized exploit circulating in the wild.That should keep the response measured. This is not a reason to tear down dual-stack networking overnight or make emergency firewall changes without testing. Race bugs in kernel networking can be serious, but they also need careful translation into actual exposure: kernel version, enabled code paths, reachable services, packet path, and distro backport status.
The right operational posture is disciplined urgency. Treat the fix as security-relevant, prioritize internet-facing Linux systems and high-throughput internal services, and monitor your distribution advisories. But do not invent a severity rating that the public record has not yet established.
This is where IT teams earn their keep. The job is not to panic before NVD enrichment lands, nor to wait passively for a CVSS score to bless reality. The job is to map an upstream kernel fix onto your fleet faster than attackers can map it onto their testing rigs.
Distro Backports Will Matter More Than Mainline Version Strings
The upstream references include stable kernel commits, which is good news and also a complication. Most production Linux systems do not run vanilla mainline kernels. They run distribution kernels with backported fixes, vendor patch stacks, and version numbers that can mislead anyone reading them too literally.That means the question “am I affected?” will not always be answered by comparing your kernel version to a mainline tag. A Red Hat, Ubuntu, Debian, SUSE, Oracle, Amazon, or Azure kernel may carry the fix while presenting a version string that appears older. Conversely, a custom kernel or appliance build may miss the fix even if it looks superficially modern.
Administrators should look for distribution advisories and package changelogs that mention CVE-2026-43198 or the tcp_v6_syn_recv_sock() race fix. If those are not available yet, the next best signal is whether the relevant stable commit has landed in the vendor’s kernel source package. In larger environments, this is a case for vulnerability management teams and Linux platform engineers to work together rather than fire tickets at each other.
Container users should also avoid a common mistake. Updating a container image usually does not update the host kernel. If the vulnerable code is in the host kernel, the fix belongs in the host OS, node image, hypervisor guest, or managed Kubernetes node pool—not merely in application containers.
The Bug’s Shape Rewards Defense in Depth
CVE-2026-43198 is a kernel bug, so patching is the clean answer. But patching kernel fleets is never instantaneous, especially where uptime, compliance windows, and vendor certification collide. That makes exposure reduction relevant even when no workaround is formally listed.The most exposed systems are likely those accepting TCP connections at scale, particularly internet-facing Linux hosts and dual-stack services. Load balancers, proxies, web servers, mail gateways, VPN concentrators, Kubernetes ingress nodes, and service meshes all deserve earlier attention than a developer VM hidden behind a NAT. The vulnerable path is in connection establishment, so listening services matter.
Network controls cannot reliably “filter out” a race inside socket creation, but they can reduce who can reach the vulnerable path. Restricting unnecessary listening ports, tightening security groups, pruning stale IPv6 exposure, and removing accidental dual-stack bindings are all sensible hygiene steps. These are not substitutes for the patch; they are ways to narrow the blast radius while the patch moves through change control.
The most useful mitigation may be observability. If a kernel update causes regressions in TCP handling, teams need to know quickly. If suspicious connection storms hit unpatched services, teams need enough telemetry to separate ordinary internet background noise from targeted probing.
The Old CVSS Reflex Is Failing Kernel Security
This CVE illustrates a broader shift that many enterprises still resist. CVSS is useful, but it is slow, lossy, and often least helpful during the first hours or days of a kernel disclosure. Kernel engineering reality arrives as patches, mailing-list reports, stack traces, and stable commits. Security operations reality wants normalized scores, affected-product tables, and vendor dashboards.The gap between those worlds is now a risk of its own. Attackers can read commits too. They do not need NVD to tell them that a race in TCP child socket initialization is worth studying. They can diff the patch, identify the changed ordering, and test whether reachable services can be coerced into the bad interleaving.
Defenders should not pretend every kernel CVE is equally urgent. The flood of Linux CVE assignments has made that impossible. But defenders also cannot outsource prioritization entirely to enrichment pipelines. A vulnerability in a driver for obscure hardware and a vulnerability in TCP connection setup are not the same kind of problem, even if both spend a few days with no NVD score.
The better model is contextual triage. Code path, exposure, subsystem, exploit preconditions, vendor patch availability, and fleet role should all carry weight. CVE-2026-43198 lands in a subsystem that many servers expose by design, which is why it deserves attention before the paperwork is complete.
The Patch Queue Has a TCP Race Near the Front
The practical response to CVE-2026-43198 is not complicated, but it does require precision. Treat this as a Linux kernel update issue first, a vulnerability-scanner issue second, and a Microsoft issue only where Microsoft-managed Linux components are actually in your environment.- Systems running Linux kernels with the affected TCP/IPv6 code path should receive vendor kernel updates that include the tcp_v6_syn_recv_sock() race fix.
- Internet-facing Linux services and high-volume dual-stack listeners should move ahead of low-exposure desktops and lab machines in the rollout order.
- WSL, Azure Linux workloads, Linux virtual machines, and managed Kubernetes nodes should be checked separately because each may receive kernel fixes through a different update channel.
- Container image rebuilds alone are not enough when the vulnerable code lives in the host or node kernel.
- Security teams should not wait for a CVSS score before beginning inventory and patch planning, but they also should not describe the bug as exploited or critical unless vendor data later supports that claim.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center