CVE-2026-43267 is a newly published Linux kernel vulnerability, disclosed on May 6, 2026, in the Realtek rtw89 Wi-Fi driver, where a zero beacon interval discovered during fuzz testing could trigger a division-by-zero fault in beacon tracking code. The fix is almost comically small: if the driver sees a beacon interval of zero, it falls back to 100 TU, the ordinary Wi-Fi default. But the story is not the size of the patch. It is how modern kernel security increasingly turns on whether boring assumptions in hardware-adjacent code survive contact with malformed state.
The Linux kernel has spent decades accumulating defensive machinery, but device drivers remain where the kernel’s old bargain with hardware is most visible. Drivers translate the messy outside world into assumptions the rest of the operating system can live with. When one of those assumptions is “this value will never be zero,” the difference between stable networking and a kernel crash can be a single missing guard.
CVE-2026-43267 lives in that unglamorous territory. The vulnerable component is
The vulnerability description says fuzz testing found that
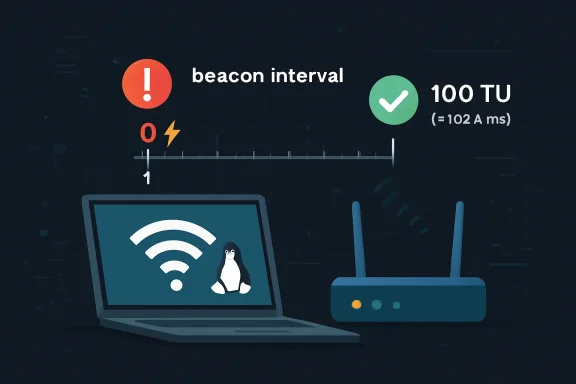
That is why the fix sets a default value of 100 TU when the interval is zero. In Wi-Fi, a TU, or time unit, is 1,024 microseconds, and 100 TU is the familiar roughly 102.4 millisecond beacon interval commonly used by access points. The patch is less a clever mitigation than an admission that driver code must defend itself even against states that upper layers are supposed to prevent.
That instinct is understandable, but it can misread kernel risk. A crash in user space is an application problem. A crash in kernel space is a system problem. If reachable through malformed wireless state, buggy firmware interaction, or hostile local testing, a small arithmetic flaw can become a denial-of-service condition against a machine that otherwise appears fully patched and healthy.
The CVE record, at publication, had not yet been enriched by NVD with CVSS scoring. That absence is important because it leaves defenders in the familiar gray zone between “assigned CVE” and “actionable severity.” There is no NVD base score yet, no official NIST vector, and no evidence in the public record of active exploitation. But there is a patch, and in kernel operations, patched arithmetic bugs tend to age poorly when ignored.
The word “potential” in the description should not lull administrators into dismissing it. Fuzzing finds states that normal users rarely create, but kernel history is full of rare states that became reachable once someone cared enough to shape the inputs. Wireless stacks are especially uncomfortable because they sit at the boundary of local hardware, nearby radio traffic, firmware behavior, and privileged kernel code.
This does not mean every laptop with Realtek Wi-Fi is under immediate threat. It means the correct operational posture is boring: track whether your kernel stream has absorbed the stable fix, deploy it through normal update channels, and do not wait for an exploit headline before treating kernel driver patches as real maintenance.
Realtek Wi-Fi chips are common in cost-sensitive laptops and desktops, including systems that Windows users may dual-boot into Linux or repurpose as homelab nodes. For WindowsForum readers, that matters because the affected machines are often not exotic Linux appliances. They are ordinary PCs: spare laptops running Fedora, Debian, Ubuntu, Arch, Proxmox-adjacent lab installs, or lightweight desktop distributions after Windows support became inconvenient.
The rtw89 family has also been a recurring subject of user frustration around suspend/resume behavior, firmware quirks, power management, and kernel-version compatibility. That does not make this CVE a direct sequel to every “Realtek Wi-Fi is broken again” forum thread. It does, however, place the bug in a driver ecosystem where small edge-case fixes can have outsized practical value.
Driver reliability and driver security are often the same discipline wearing different badges. A code path hardened against an impossible value is also a code path less likely to strand a laptop after wake, break roaming behavior, or produce a kernel splat that users misattribute to the desktop environment. The safest driver is usually the one that assumes less and validates more.
That is the deeper lesson of CVE-2026-43267: Linux hardware support is not merely about whether a device enumerates and passes traffic. It is about whether every strange condition between firmware, mac80211 state, and the driver is handled without turning an input anomaly into a kernel-level failure.
In this case, the cracked assumption was simple: the beacon interval should not be zero. In a perfectly polite world, it would not be. Wireless access points are expected to advertise sensible beacon timing, upper layers are expected to populate connection state sanely, and drivers are expected to receive values that make physical and mathematical sense.
The kernel does not run in a perfectly polite world. It runs on hardware with firmware blobs, imperfect ACPI tables, vendor-specific behavior, suspend/resume races, regulatory-domain changes, and sometimes malicious input. A fuzzer’s job is to be the impolite world in a lab before the impolite world arrives in production.
That is why these small CVEs keep appearing in subsystems that ordinary users never think about. The kernel is not suddenly becoming less secure because more driver arithmetic bugs receive CVE IDs. In many cases, the opposite is true: the project is surfacing and backporting faults that previously might have lived as obscure crash reports, distribution bugs, or “my Wi-Fi randomly dies” folklore.
There is a mild absurdity in assigning a globally tracked CVE to a fallback from zero to 100 TU. But that absurdity is the modern vulnerability ecosystem in miniature. Once a bug can crash privileged code, and once it has a stable fix, the machinery of disclosure, tracking, and downstream patch management takes over.
The answer is that Microsoft is no longer just a Windows vendor in the operational lives of its customers. Azure runs Linux. Windows Subsystem for Linux has normalized Linux environments on Windows workstations. Defender, Intune, GitHub, Azure Kubernetes Service, and cloud images all pull Microsoft deeper into the Linux security supply chain. Even when a CVE is not a Windows bug, Microsoft’s ecosystem may still need to index, explain, or route it.
For enterprise defenders, this matters because vulnerability management tools rarely respect old platform boundaries. A fleet may include Windows endpoints, Linux build agents, developer laptops, Azure VMs, container hosts, network appliances, and dual-boot test rigs. The same security team is expected to know which CVEs matter to which assets, even when the CVE appears in a Microsoft portal but names a Linux wireless driver.
That ambiguity is where many patching mistakes happen. An admin sees “Linux kernel” and assumes it is irrelevant to a Windows estate. Another sees “MSRC” and assumes there must be a Windows update. Neither conclusion is necessarily right. The useful question is narrower: do you manage Linux systems using the affected rtw89 driver, and will your distribution ship the relevant stable kernel fix?
This is also a reminder that SBOM-style asset awareness is not a luxury project. If you cannot tell which laptops or lab machines use Realtek rtw89 hardware, you cannot distinguish noise from action. The CVE may be low drama, but the operational discipline it tests is the same discipline required for high-drama vulnerabilities.
The absence of a score does not mean the absence of risk. It means the record is awaiting enrichment. In practice, security teams should treat the upstream description, affected component, exploit preconditions, and patch availability as the first layer of triage while waiting for formal scoring.
For CVE-2026-43267, the likely impact class is denial of service rather than code execution, based on the public description. The bug is a division-by-zero condition in beacon tracking calculations, not a heap overflow or use-after-free. That distinction matters because it reduces the urgency for most environments, but it does not reduce the need to patch through normal channels.
There is also no public indication, as of the disclosure, that attackers are exploiting this vulnerability. That should lower panic, not priority. The correct response is not emergency maintenance windows across every Linux desktop. It is making sure the issue is captured in kernel update intake, tested where Realtek Wi-Fi matters, and not lost because the CVSS column is blank.
The kernel community’s stable process exists precisely to move small, correct fixes into supported branches without forcing every user onto the bleeding edge. If your distribution tracks stable kernels responsibly, this is the sort of fix that should arrive as part of ordinary kernel update cadence. If you pin kernels indefinitely because “Wi-Fi works right now,” this is the sort of fix you will miss.
That value is not arbitrary in practical Wi-Fi terms. A 100 TU beacon interval is a conventional default across many access point configurations, and using it avoids the immediate arithmetic hazard while keeping beacon tracking behavior in a plausible range. It is the kind of defensive default that kernel code should prefer when faced with impossible input: safe enough to continue, simple enough to review, and unlikely to introduce a new class of failure.
This is not always the right pattern. Some invalid inputs should abort operations, refuse association, or tear down state. But for timing calculations in a driver that has already reached beacon tracking, a conservative fallback can be better than converting a malformed state into a machine-wide fault.
The important point is that the fallback happens inside the driver. It does not rely on the rest of the stack to sanitize the value first. Kernel hardening has been moving in this direction for years: every layer should validate what it consumes, even if another layer was supposed to validate what it produced.
That is not redundancy for its own sake. It is how large systems survive. In a kernel, there are too many paths, too many devices, and too many timing-sensitive transitions to trust any single invariant absolutely.
The public CVE text for CVE-2026-43267 does not establish a remote over-the-air exploit. It says fuzz testing found a zero beacon interval condition that could lead to division by zero in subsequent calculations. That is narrower than saying any attacker can crash any nearby Linux laptop with a crafted beacon frame.
Still, defenders should be careful with the word “local.” A Wi-Fi driver processes information derived from the wireless environment, negotiated connection state, firmware reports, and kernel networking structures. Even when exploitation requires unusual conditions, the affected code sits closer to untrusted reality than, say, a parser for a root-only configuration file.
For consumer users, the practical advice is straightforward: update your kernel when your distribution provides the fix. For sysadmins, the more useful framing is exposure mapping. Machines with Realtek rtw89 Wi-Fi that regularly move through hostile or uncontrolled wireless environments deserve more attention than stationary servers without wireless hardware.
For homelab users, the issue is also a reminder not to treat laptops as maintenance-free servers. A repurposed laptop running Linux in a closet may still carry its Wi-Fi driver, firmware, and power-management baggage, even if Ethernet is the only intended network path. Disabling unused wireless hardware can be as sensible as patching it.
That habit is understandable, but it carries a security cost. Kernel CVEs like CVE-2026-43267 are exactly what pinned systems miss. A user who froze a kernel to preserve Realtek Wi-Fi stability may unknowingly preserve the very driver bug that upstream has fixed.
Enterprise Linux distributions reduce this tension by backporting security fixes into older supported kernel streams. Rolling distributions reduce it by moving quickly. The danger zone is the unmanaged middle: personal machines, lab boxes, boutique kernels, out-of-tree driver builds, and systems where the kernel was manually held after one bad update.
The rtw89 ecosystem has seen enough compatibility complaints that some users rely on external driver trees or custom builds. That may be necessary for hardware enablement on some systems, but it complicates security intake. When a fix lands upstream, users of downstream or unofficial driver copies must ask whether their code actually contains the patch.
This is where WindowsForum’s mixed audience has an advantage. Windows admins already understand driver provenance because Windows has trained them to care about OEM packages, Windows Update drivers, and vendor support channels. The same instinct applies on Linux: know whether your wireless driver comes from the distribution kernel, an external repository, or a local workaround you forgot about six months ago.
This creates a strange experience for defenders. A vulnerability appears with an identifier, a short description, and commit references, but without the severity score that dictates SLA timers. Automation sees “new CVE.” Humans see “not enough detail.” The result is either overreaction or neglect.
The better posture is to separate acknowledgement from escalation. A new kernel driver CVE should enter the intake queue immediately, but its response tier should be based on asset exposure and patch availability rather than raw novelty. A Realtek Wi-Fi crash bug on developer laptops is not the same as a remotely exploitable flaw in an Internet-facing VPN appliance.
That said, waiting for perfect enrichment can be its own failure mode. NVD delays have become a fact of life, and high-quality upstream metadata can be enough to act. In this case, the fix is known, the component is known, and the failure mode is described. That is sufficient for most organizations to begin tracking distribution updates.
The vulnerability industry still has not fully adjusted to the volume of kernel CVEs produced by systematic review and fuzzing. Not every CVE is a five-alarm fire. But every CVE is a small test of whether an organization can translate public software maintenance into actual risk reduction.
That means the relevant question is not merely “does upstream have a patch?” It is “which kernel build on my machines contains the patch?” For rolling-release users, the answer may arrive quickly. For long-term support users, the answer may be a backported fix with no obvious version-number jump. For vendor appliances, the answer may be buried in release notes.
The three upstream stable commit references attached to the CVE record indicate that the fix is being carried through supported kernel lines rather than left as a mainline-only improvement. That is encouraging, but it still leaves the last mile to distributions and administrators. Kernel security is delivered through packaging, reboot discipline, and hardware-aware testing.
Reboot discipline deserves emphasis. A patched kernel package sitting on disk is not the same as a patched running kernel. Linux systems can remain vulnerable to kernel-level bugs until they actually boot into the fixed kernel, unless live patching covers the specific issue — and driver fixes like this are not always natural live-patching candidates.
For desktop fleets, the operational bottleneck is often user tolerance. Kernel updates interrupt work, and Wi-Fi regressions are visible immediately. The safest approach is to pilot the update on representative Realtek hardware, watch for connectivity regressions, and then move quickly rather than indefinitely.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Tiny Wi-Fi Bug Exposes a Big Kernel Reality
A Tiny Wi-Fi Bug Exposes a Big Kernel Reality
The Linux kernel has spent decades accumulating defensive machinery, but device drivers remain where the kernel’s old bargain with hardware is most visible. Drivers translate the messy outside world into assumptions the rest of the operating system can live with. When one of those assumptions is “this value will never be zero,” the difference between stable networking and a kernel crash can be a single missing guard.CVE-2026-43267 lives in that unglamorous territory. The vulnerable component is
rtw89, the in-kernel Realtek Wi-Fi driver family used by a long list of modern consumer laptops, mini PCs, and desktops with Realtek wireless chipsets. The affected code path is beacon tracking, part of the machinery that lets a Wi-Fi client keep time with an access point’s periodic beacon frames.The vulnerability description says fuzz testing found that
bss_conf->beacon_int might be zero. That matters because beacon interval arithmetic assumes a nonzero divisor. Once zero sneaks in, the kernel can hit a division-by-zero condition — not a Hollywood exploit chain, but exactly the kind of fault that can panic a machine, drop connectivity, or make a workstation unreliable in ways that are maddening to diagnose.That is why the fix sets a default value of 100 TU when the interval is zero. In Wi-Fi, a TU, or time unit, is 1,024 microseconds, and 100 TU is the familiar roughly 102.4 millisecond beacon interval commonly used by access points. The patch is less a clever mitigation than an admission that driver code must defend itself even against states that upper layers are supposed to prevent.
The Vulnerability Is Mundane, Which Is Precisely Why It Matters
Security teams often rank vulnerabilities by spectacle. Remote code execution gets headlines. Authentication bypasses get emergency calls. Division-by-zero bugs get sorted into the administrative pile unless there is evidence of exploitation or a particularly exposed attack surface.That instinct is understandable, but it can misread kernel risk. A crash in user space is an application problem. A crash in kernel space is a system problem. If reachable through malformed wireless state, buggy firmware interaction, or hostile local testing, a small arithmetic flaw can become a denial-of-service condition against a machine that otherwise appears fully patched and healthy.
The CVE record, at publication, had not yet been enriched by NVD with CVSS scoring. That absence is important because it leaves defenders in the familiar gray zone between “assigned CVE” and “actionable severity.” There is no NVD base score yet, no official NIST vector, and no evidence in the public record of active exploitation. But there is a patch, and in kernel operations, patched arithmetic bugs tend to age poorly when ignored.
The word “potential” in the description should not lull administrators into dismissing it. Fuzzing finds states that normal users rarely create, but kernel history is full of rare states that became reachable once someone cared enough to shape the inputs. Wireless stacks are especially uncomfortable because they sit at the boundary of local hardware, nearby radio traffic, firmware behavior, and privileged kernel code.
This does not mean every laptop with Realtek Wi-Fi is under immediate threat. It means the correct operational posture is boring: track whether your kernel stream has absorbed the stable fix, deploy it through normal update channels, and do not wait for an exploit headline before treating kernel driver patches as real maintenance.
Realtek’s rtw89 Sits Where Linux Is Most Dependent on Vendor Reality
The rtw89 driver exists because Linux users need modern Realtek wireless hardware to work without downloading out-of-tree code from random repositories. That is a major improvement over the bad old days of driver roulette, but it also brings a predictable consequence: hardware enablement code becomes part of the kernel’s security perimeter.Realtek Wi-Fi chips are common in cost-sensitive laptops and desktops, including systems that Windows users may dual-boot into Linux or repurpose as homelab nodes. For WindowsForum readers, that matters because the affected machines are often not exotic Linux appliances. They are ordinary PCs: spare laptops running Fedora, Debian, Ubuntu, Arch, Proxmox-adjacent lab installs, or lightweight desktop distributions after Windows support became inconvenient.
The rtw89 family has also been a recurring subject of user frustration around suspend/resume behavior, firmware quirks, power management, and kernel-version compatibility. That does not make this CVE a direct sequel to every “Realtek Wi-Fi is broken again” forum thread. It does, however, place the bug in a driver ecosystem where small edge-case fixes can have outsized practical value.
Driver reliability and driver security are often the same discipline wearing different badges. A code path hardened against an impossible value is also a code path less likely to strand a laptop after wake, break roaming behavior, or produce a kernel splat that users misattribute to the desktop environment. The safest driver is usually the one that assumes less and validates more.
That is the deeper lesson of CVE-2026-43267: Linux hardware support is not merely about whether a device enumerates and passes traffic. It is about whether every strange condition between firmware, mac80211 state, and the driver is handled without turning an input anomaly into a kernel-level failure.
Fuzzing Has Become the Kernel’s Unpaid Night Shift
The most revealing phrase in the CVE description is “during fuzz testing.” Fuzzing is not glamorous, but it has become one of the most productive security tools for large C codebases. Instead of waiting for a human to imagine every invalid state, fuzzers bombard code with unexpected combinations until assumptions crack.In this case, the cracked assumption was simple: the beacon interval should not be zero. In a perfectly polite world, it would not be. Wireless access points are expected to advertise sensible beacon timing, upper layers are expected to populate connection state sanely, and drivers are expected to receive values that make physical and mathematical sense.
The kernel does not run in a perfectly polite world. It runs on hardware with firmware blobs, imperfect ACPI tables, vendor-specific behavior, suspend/resume races, regulatory-domain changes, and sometimes malicious input. A fuzzer’s job is to be the impolite world in a lab before the impolite world arrives in production.
That is why these small CVEs keep appearing in subsystems that ordinary users never think about. The kernel is not suddenly becoming less secure because more driver arithmetic bugs receive CVE IDs. In many cases, the opposite is true: the project is surfacing and backporting faults that previously might have lived as obscure crash reports, distribution bugs, or “my Wi-Fi randomly dies” folklore.
There is a mild absurdity in assigning a globally tracked CVE to a fallback from zero to 100 TU. But that absurdity is the modern vulnerability ecosystem in miniature. Once a bug can crash privileged code, and once it has a stable fix, the machinery of disclosure, tracking, and downstream patch management takes over.
The MSRC Listing Is a Reminder That Windows Shops Run More Than Windows
The user-facing source for many admins may be Microsoft’s Security Update Guide, not kernel.org. That can make CVE-2026-43267 look odd at first glance: why is a Linux kernel Wi-Fi driver issue showing up in the orbit of Microsoft security tracking?The answer is that Microsoft is no longer just a Windows vendor in the operational lives of its customers. Azure runs Linux. Windows Subsystem for Linux has normalized Linux environments on Windows workstations. Defender, Intune, GitHub, Azure Kubernetes Service, and cloud images all pull Microsoft deeper into the Linux security supply chain. Even when a CVE is not a Windows bug, Microsoft’s ecosystem may still need to index, explain, or route it.
For enterprise defenders, this matters because vulnerability management tools rarely respect old platform boundaries. A fleet may include Windows endpoints, Linux build agents, developer laptops, Azure VMs, container hosts, network appliances, and dual-boot test rigs. The same security team is expected to know which CVEs matter to which assets, even when the CVE appears in a Microsoft portal but names a Linux wireless driver.
That ambiguity is where many patching mistakes happen. An admin sees “Linux kernel” and assumes it is irrelevant to a Windows estate. Another sees “MSRC” and assumes there must be a Windows update. Neither conclusion is necessarily right. The useful question is narrower: do you manage Linux systems using the affected rtw89 driver, and will your distribution ship the relevant stable kernel fix?
This is also a reminder that SBOM-style asset awareness is not a luxury project. If you cannot tell which laptops or lab machines use Realtek rtw89 hardware, you cannot distinguish noise from action. The CVE may be low drama, but the operational discipline it tests is the same discipline required for high-drama vulnerabilities.
The Missing CVSS Score Should Not Become an Excuse
At publication, NVD had not yet assigned CVSS 4.0, CVSS 3.x, or CVSS 2.0 metrics. That is normal for newly received CVEs, especially those flowing from fast-moving upstream projects. It is also an increasingly common pain point for defenders who have built dashboards around severity numbers.The absence of a score does not mean the absence of risk. It means the record is awaiting enrichment. In practice, security teams should treat the upstream description, affected component, exploit preconditions, and patch availability as the first layer of triage while waiting for formal scoring.
For CVE-2026-43267, the likely impact class is denial of service rather than code execution, based on the public description. The bug is a division-by-zero condition in beacon tracking calculations, not a heap overflow or use-after-free. That distinction matters because it reduces the urgency for most environments, but it does not reduce the need to patch through normal channels.
There is also no public indication, as of the disclosure, that attackers are exploiting this vulnerability. That should lower panic, not priority. The correct response is not emergency maintenance windows across every Linux desktop. It is making sure the issue is captured in kernel update intake, tested where Realtek Wi-Fi matters, and not lost because the CVSS column is blank.
The kernel community’s stable process exists precisely to move small, correct fixes into supported branches without forcing every user onto the bleeding edge. If your distribution tracks stable kernels responsibly, this is the sort of fix that should arrive as part of ordinary kernel update cadence. If you pin kernels indefinitely because “Wi-Fi works right now,” this is the sort of fix you will miss.
The Patch Shows the Value of Defensive Defaults
There is something elegant about the chosen mitigation. The code does not attempt to infer user intent, reset the device, or build a new policy layer. It simply says: if the beacon interval is zero, use 100 TU.That value is not arbitrary in practical Wi-Fi terms. A 100 TU beacon interval is a conventional default across many access point configurations, and using it avoids the immediate arithmetic hazard while keeping beacon tracking behavior in a plausible range. It is the kind of defensive default that kernel code should prefer when faced with impossible input: safe enough to continue, simple enough to review, and unlikely to introduce a new class of failure.
This is not always the right pattern. Some invalid inputs should abort operations, refuse association, or tear down state. But for timing calculations in a driver that has already reached beacon tracking, a conservative fallback can be better than converting a malformed state into a machine-wide fault.
The important point is that the fallback happens inside the driver. It does not rely on the rest of the stack to sanitize the value first. Kernel hardening has been moving in this direction for years: every layer should validate what it consumes, even if another layer was supposed to validate what it produced.
That is not redundancy for its own sake. It is how large systems survive. In a kernel, there are too many paths, too many devices, and too many timing-sensitive transitions to trust any single invariant absolutely.
Wi-Fi Bugs Are Local, Until They Aren’t Operationally Local
Wireless vulnerabilities occupy an awkward threat category. They are often not Internet-reachable in the way server vulnerabilities are, but they are not purely local either. Radio proximity, malicious access points, roaming behavior, and shared environments complicate the boundary.The public CVE text for CVE-2026-43267 does not establish a remote over-the-air exploit. It says fuzz testing found a zero beacon interval condition that could lead to division by zero in subsequent calculations. That is narrower than saying any attacker can crash any nearby Linux laptop with a crafted beacon frame.
Still, defenders should be careful with the word “local.” A Wi-Fi driver processes information derived from the wireless environment, negotiated connection state, firmware reports, and kernel networking structures. Even when exploitation requires unusual conditions, the affected code sits closer to untrusted reality than, say, a parser for a root-only configuration file.
For consumer users, the practical advice is straightforward: update your kernel when your distribution provides the fix. For sysadmins, the more useful framing is exposure mapping. Machines with Realtek rtw89 Wi-Fi that regularly move through hostile or uncontrolled wireless environments deserve more attention than stationary servers without wireless hardware.
For homelab users, the issue is also a reminder not to treat laptops as maintenance-free servers. A repurposed laptop running Linux in a closet may still carry its Wi-Fi driver, firmware, and power-management baggage, even if Ethernet is the only intended network path. Disabling unused wireless hardware can be as sensible as patching it.
The Bigger Problem Is Kernel Pinning Masquerading as Stability
Linux desktop users often learn to fear kernel updates for good reasons. A new kernel can regress graphics, break suspend, change wireless behavior, or upset a proprietary module. The predictable response is kernel pinning: find the version that works and hold onto it.That habit is understandable, but it carries a security cost. Kernel CVEs like CVE-2026-43267 are exactly what pinned systems miss. A user who froze a kernel to preserve Realtek Wi-Fi stability may unknowingly preserve the very driver bug that upstream has fixed.
Enterprise Linux distributions reduce this tension by backporting security fixes into older supported kernel streams. Rolling distributions reduce it by moving quickly. The danger zone is the unmanaged middle: personal machines, lab boxes, boutique kernels, out-of-tree driver builds, and systems where the kernel was manually held after one bad update.
The rtw89 ecosystem has seen enough compatibility complaints that some users rely on external driver trees or custom builds. That may be necessary for hardware enablement on some systems, but it complicates security intake. When a fix lands upstream, users of downstream or unofficial driver copies must ask whether their code actually contains the patch.
This is where WindowsForum’s mixed audience has an advantage. Windows admins already understand driver provenance because Windows has trained them to care about OEM packages, Windows Update drivers, and vendor support channels. The same instinct applies on Linux: know whether your wireless driver comes from the distribution kernel, an external repository, or a local workaround you forgot about six months ago.
The CVE Pipeline Is Getting Faster Than Human Attention
CVE-2026-43267 was received from kernel.org and published before NVD enrichment had caught up. That is increasingly the normal tempo. Upstream projects, CNAs, advisories, mirrors, scanners, and vendor portals can all surface a record before analysts have filled in every field that enterprise workflows expect.This creates a strange experience for defenders. A vulnerability appears with an identifier, a short description, and commit references, but without the severity score that dictates SLA timers. Automation sees “new CVE.” Humans see “not enough detail.” The result is either overreaction or neglect.
The better posture is to separate acknowledgement from escalation. A new kernel driver CVE should enter the intake queue immediately, but its response tier should be based on asset exposure and patch availability rather than raw novelty. A Realtek Wi-Fi crash bug on developer laptops is not the same as a remotely exploitable flaw in an Internet-facing VPN appliance.
That said, waiting for perfect enrichment can be its own failure mode. NVD delays have become a fact of life, and high-quality upstream metadata can be enough to act. In this case, the fix is known, the component is known, and the failure mode is described. That is sufficient for most organizations to begin tracking distribution updates.
The vulnerability industry still has not fully adjusted to the volume of kernel CVEs produced by systematic review and fuzzing. Not every CVE is a five-alarm fire. But every CVE is a small test of whether an organization can translate public software maintenance into actual risk reduction.
The Real Action Is in Distribution Kernels
Most users should not be pulling individual commits from kernel.org. The right fix path is through the kernel packages supplied by the distribution or vendor that supports the machine. Fedora, Ubuntu, Debian, Arch, openSUSE, enterprise distributions, and downstream appliance vendors each have their own timing and backport policies.That means the relevant question is not merely “does upstream have a patch?” It is “which kernel build on my machines contains the patch?” For rolling-release users, the answer may arrive quickly. For long-term support users, the answer may be a backported fix with no obvious version-number jump. For vendor appliances, the answer may be buried in release notes.
The three upstream stable commit references attached to the CVE record indicate that the fix is being carried through supported kernel lines rather than left as a mainline-only improvement. That is encouraging, but it still leaves the last mile to distributions and administrators. Kernel security is delivered through packaging, reboot discipline, and hardware-aware testing.
Reboot discipline deserves emphasis. A patched kernel package sitting on disk is not the same as a patched running kernel. Linux systems can remain vulnerable to kernel-level bugs until they actually boot into the fixed kernel, unless live patching covers the specific issue — and driver fixes like this are not always natural live-patching candidates.
For desktop fleets, the operational bottleneck is often user tolerance. Kernel updates interrupt work, and Wi-Fi regressions are visible immediately. The safest approach is to pilot the update on representative Realtek hardware, watch for connectivity regressions, and then move quickly rather than indefinitely.
The Small Patch That Should Change Your Triage
The practical read on CVE-2026-43267 is neither panic nor dismissal. It is a modest kernel driver hardening fix with a plausible denial-of-service impact, a narrow affected component, and no public CVSS score at initial publication. That makes it an ideal candidate for disciplined routine patching.- Systems using Linux kernels with the Realtek rtw89 Wi-Fi driver should be checked against distribution kernel updates that include the upstream fix.
- The vulnerability is best understood as a potential kernel stability and denial-of-service issue, not as a publicly demonstrated remote code execution flaw.
- The absence of NVD scoring on May 6, 2026 should not stop teams from tracking the patch through their normal vulnerability-management process.
- Machines that do not use Realtek rtw89 hardware are unlikely to have meaningful exposure to this specific bug, though they may still receive the fix as part of broader kernel updates.
- Users who rely on pinned kernels, custom kernels, or out-of-tree Realtek driver builds should verify the patch directly rather than assuming their distribution will handle it.
- Administrators should remember that installing a fixed kernel package is not enough; the machine must boot into the fixed kernel for the driver change to take effect.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center