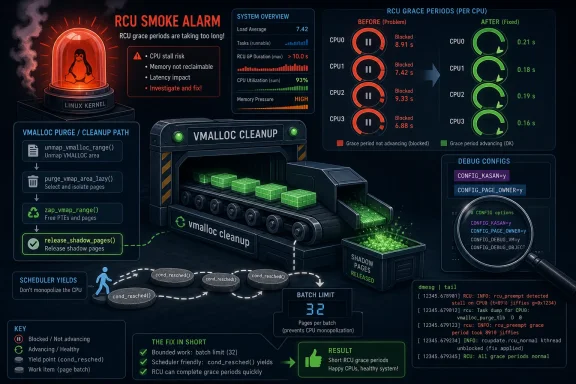
CVE-2026-43292 is a Linux kernel availability vulnerability published by NVD on May 8, 2026, after a kernel.org fix for RCU stalls in
The fix for CVE-2026-43292 is almost comically modest: add periodic
But the smallness of the patch is the story. The Linux kernel is full of code paths that assume cleanup is cheap because cleanup usually is cheap. Turn on memory-debugging infrastructure, make the cleanup list large enough, and suddenly “free some shadow pages” becomes “walk stacks under RCU read lock over and over while other CPUs wait for grace periods that cannot complete.”
That is not a confidentiality breach or privilege escalation. It is worse in the way infrastructure people hate most: it is a stall, a hang, a cascading failure mode. The machine is still there, the task is still running, logs are still being emitted, and yet forward progress is compromised long enough for watchdogs, memory pressure, and orchestration layers to start making bad decisions.
The kernel security ecosystem has increasingly treated these bugs as CVEs because availability is a security property. If a local workload, fuzzer, container, or test harness can push the kernel into a prolonged RCU stall and possible out-of-memory behavior, the operational impact is real even if no shell pops.
That distinction should reduce panic, not interest. The systems most likely to expose this bug are exactly the systems that do the dangerous work before everyone else gets safe kernels: fuzzers, validation farms, debug-enabled staging fleets, and developer machines running experimental workloads. When those boxes stall, the result is not just a local inconvenience. It can mean lost test coverage, false negatives, wedged automation, or a misdiagnosed regression that sends engineers looking in the wrong subsystem.
The vulnerable path begins in vmalloc cleanup. The kernel accumulates virtual mapping areas on a purge list, and
On its own, that may be acceptable. With page-owner tracking enabled, each free can trigger stack capture through
That is why the fix does not change memory accounting, locking design, or KASAN’s conceptual model. It changes the loop’s manners. Every 32 entries, or sooner if the scheduler says rescheduling is needed, the cleanup path yields.
An RCU stall report is the kernel saying that bargain has been violated for too long. It does not necessarily identify a deadlock, and it does not automatically mean memory corruption. It means progress assumptions are breaking: some CPU or task has remained in a state that prevents RCU from completing its housekeeping.
In CVE-2026-43292, the problem is not that one operation is catastrophically expensive. The problem is accumulation. A loop that repeatedly performs expensive free-side work while stack-unwinding under RCU can become, in effect, an unbounded read-side critical section. The kernel is doing legitimate work, but doing too much of it without letting the rest of the system breathe.
That is why this kind of issue is easy to underestimate from the patch alone. A reviewer can look at
The presence of possible OOM behavior raises the stakes further. If cleanup cannot progress smoothly while pressure builds elsewhere, the memory-management system can enter a spiral where the work intended to reclaim or release resources itself consumes scheduling time and delays the mechanisms needed to stabilize the box.
CVE-2026-43292 fits that pattern. NVD had received and published the record, but no CVSS score was listed at the time reflected in the submitted advisory text. The source is kernel.org, not a vendor marketing bulletin. The references point to stable kernel commits rather than a glossy exploit write-up.
For security teams, this creates friction. Patch management systems tend to like severity numbers. Kernel maintainers tend to ship fixes as part of a moving stream where the technical judgment is encoded in the patch, the stable backport, and the affected subsystem. Between those worlds sits an administrator trying to decide whether an unscored kernel CVE deserves attention before the next maintenance window.
The answer is not “treat every unscored Linux CVE as urgent.” That would collapse under its own noise. The answer is to classify by exposure and operational role. A laptop running a distribution kernel without page-owner debugging enabled is not in the same risk category as a syzkaller host, kernel CI worker, or virtualization node running debug kernels for regression hunting.
Microsoft’s appearance in the source trail may also confuse readers. This is not a Windows kernel flaw. It is a Linux kernel vulnerability surfaced through the Microsoft Security Response Center because Microsoft tracks vulnerabilities that may affect its products, services, cloud workloads, Linux-based components, or customer environments. In 2026, Windows and Linux are not separate kingdoms; they are neighbors sharing hypervisors, containers, CI pipelines, developer tooling, and update infrastructure.
A Windows-heavy organization may never manage bare-metal Linux desktops and still have Linux kernels everywhere. They may be inside WSL distributions on developer laptops. They may run on self-hosted GitHub Actions runners. They may underpin appliances. They may sit in Kubernetes nodes, storage gateways, monitoring collectors, or cloud images that nobody in the Windows endpoint team thinks of as “their” patching domain.
CVE-2026-43292 is especially relevant to environments where Linux is used as a diagnostic and development substrate. Kernel fuzzing systems, driver test rigs, security research labs, and performance troubleshooting machines are more likely to run unusual configurations. Those are also environments where a stall can waste human time fast.
The practical question for a Windows administrator is not whether their domain controllers are vulnerable. They are not running this code path. The question is whether their estate includes Linux kernels configured with page-owner tracking and KASAN-like instrumentation, and whether those machines are important enough that a stall can interrupt work, mask another bug, or trigger orchestration failures.
That is a narrower concern, but it is not a trivial one. Modern IT risk is increasingly made of narrow concerns stacked on top of one another.
That second part matters. Systems fail not only when they are overloaded but when code assumes overload is the only danger signal. A debug-enabled cleanup loop can be harmful even before the scheduler’s usual heuristics scream. By forcing a reschedule opportunity after 32 items, the patch puts a hard ceiling on how long this path can ignore the rest of the system.
There is a broader operating-system truth here. Memory cleanup paths are not exempt from latency discipline. The fact that a kernel thread is reclaiming, freeing, purging, or unwinding does not make it harmless. If the path touches expensive instrumentation, it needs the same batching and preemption awareness as any other long-running kernel operation.
The page-owner angle is particularly instructive. Page-owner tracking is there to help humans understand memory behavior. It makes the system more observable by recording allocation provenance. But observability has cost, and in this case the cost is paid during freeing as well as allocation. A feature designed to diagnose memory problems can become part of an availability problem if its overhead is multiplied inside an unbounded loop.
This is not an argument against KASAN or page-owner tracking. It is an argument against pretending debug infrastructure is outside the threat model. The tools used to find bugs run on real machines with real schedulers, and their failure modes deserve production-grade thinking.
That does not make the CVE fix meaningless. It makes the boundary clearer. CVE-2026-43292 is about one specific vmalloc cleanup loop and its failure to reschedule while releasing KASAN shadow pages. Other page-owner-induced stalls may require different patches in different paths.
This distinction is crucial for administrators reading kernel CVEs. A patch can be valid, necessary, and limited. It can reduce one avenue of stalls without making an entire class of debug-kernel latency issues disappear. Security advisories often compress that nuance into a few lines because the advisory’s job is to describe the resolved vulnerability, not the whole subsystem’s ergonomics.
For kernel developers and distro maintainers, the implication is broader. Once one cleanup loop needed a forced reschedule point because instrumentation made it too expensive, adjacent loops deserve scrutiny. The bug pattern is not “KASAN is broken” or “RCU is fragile.” The pattern is “instrumented memory paths can turn linear cleanup into scheduler starvation if they do not yield.”
That is how small fixes become architectural breadcrumbs. They tell maintainers where assumptions aged badly.
CVSS is useful when it exists and when the vulnerability shape maps cleanly to the scoring model. Availability bugs in specialized kernel configurations often do not. Attack vector, privileges required, and scope can be hard to summarize without overstating exposure or understating operational damage.
A plausible exploitation scenario is local and configuration-dependent. An attacker or workload would need a way to drive vmalloc churn and cleanup under the affected debug configuration. That is not the same as a remote unauthenticated wormable bug, but it is enough to matter on shared research systems, multi-tenant test boxes, or CI infrastructure that runs untrusted or semi-trusted workloads.
There is also a class of non-malicious failure here. A fuzzer, stress test, kernel module experiment, or pathological workload may trigger the stall accidentally. In real operations, accidental denial of service still burns time and capacity. Security teams sometimes draw too bright a line between hostile and incidental triggers, but users experience the same frozen machine either way.
For prioritization, the better rubric is practical exposure. If your kernels do not enable the relevant debugging options, urgency is low. If they do, and especially if the machines run adversarial test workloads, the fix belongs in the next kernel update cycle rather than the “someday” pile.
Administrators should avoid matching only on mainline version numbers. A distribution may backport the eight-line fix to an older kernel without changing the headline version in a way that is obvious from
The right check is vendor-specific: review the distribution’s kernel changelog, security advisory, or package metadata for the vmalloc/KASAN RCU-stall fix or the relevant CVE. In regulated environments, capture the vendor advisory or package version in the patch record rather than relying on the upstream commit hash alone.
For those building kernels directly, the fix is straightforward to audit. Look for the
The more complicated question is whether to disable
But cloud providers, platform teams, and large SaaS operators absolutely run debug and instrumented kernels in qualification pipelines. They run fuzzing infrastructure. They maintain custom kernels. They test memory-management changes under heavy churn before those changes reach production fleets. CVE-2026-43292 lives in that pre-production world, and pre-production failures can have production consequences when they slow patch validation or hide regressions.
There is also the virtualization-host question. A Linux host running virtualized workloads can suffer local availability impact if the host kernel stalls. Whether an untrusted guest could realistically trigger the affected host path depends on configuration and exposure details that should not be assumed. Still, infrastructure teams should treat kernel availability bugs in host environments conservatively when debug options are enabled.
For Windows-centric shops using Hyper-V for Linux guests, the direction is usually reversed: the Linux guest stalls, not the Windows host. That still matters when the guest is a build runner, scanner, monitoring component, or developer environment. A hung Linux VM inside an otherwise healthy Windows platform is still an outage for the workflow that depends on it.
This is the dull integration reality of 2026. Windows reliability depends on Linux reliability more often than asset inventories admit.
That said, not every RCU stall is this CVE. RCU is a symptom-reporting mechanism, and many kernel paths can trigger stall warnings. Administrators should resist the urge to paste the first matching log line into a vulnerability spreadsheet and declare causality. The relevant combination is the vmalloc purge path, KASAN release, page-owner tracking, and long-running cleanup without rescheduling.
If you are triaging a live system, the first practical step is to identify the kernel build configuration. Confirm whether KASAN and page-owner tracking are enabled. Then compare the running kernel package with your vendor’s fixed builds. If the box is a test kernel compiled in-house, inspect the source or config repository directly.
For recurring failures, preserve full kernel logs before rebooting. RCU stall traces often contain the exact call stack needed to separate this issue from adjacent page-owner stalls. That distinction matters because a different stack may point to another fix, not this CVE.
That makes debug-kernel availability a first-class concern. A toolchain that finds memory bugs but regularly stalls under pressure will lose trust. Engineers will disable it, reduce coverage, or normalize warnings that should be investigated. In that sense, fixing CVE-2026-43292 is not just about preventing one denial-of-service condition. It is about keeping the diagnostic stack usable.
The Linux kernel community has become very good at finding memory safety defects with automation. Syzkaller and similar systems make obscure paths less obscure by relentlessly generating states human testers would never design. But automated discovery also produces a flood of failure modes that blur the line between bug, vulnerability, and instrumentation artifact.
This CVE is a product of that world. A fuzzer finds a stall. A developer narrows the path. Maintainers add a bounded reschedule point. Stable trees pick it up. A CVE record appears. Somewhere later, an administrator sees an unscored advisory and has to decide whether it matters.
The answer is that it matters most where the same automation and instrumentation are part of the job.
For debug-enabled systems, the calculus changes. If the system runs KASAN, page-owner tracking, fuzzers, kernel stress tests, or untrusted local workloads, this is the kind of availability bug that deserves prompt remediation. The fix is small, stable-bound, and designed to reduce scheduler starvation rather than change visible kernel semantics.
For developers maintaining custom kernels, the patch also has low conceptual risk. It introduces periodic scheduling points into a cleanup loop that could previously run too long. That can alter timing, as any scheduling change can, but the intended effect is precisely to restore system responsiveness under worst-case cleanup loads.
The larger patch-management lesson is to stop using CVSS absence as an excuse for inaction. Classify the machine. Classify the kernel configuration. Classify the workload. Then decide.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
kasan_release_vmalloc_node, where vmalloc cleanup could monopolize CPU time when CONFIG_PAGE_OWNER and KASAN shadow-page freeing collided. The bug is not a headline-grabbing remote exploit, and that is precisely why it is worth paying attention to. It sits in the uncomfortable middle ground between “debug-only corner case” and “production kernel can become unavailable under the wrong pressure.” For administrators running Linux guests, developer workstations, CI fuzzing farms, or Windows-adjacent infrastructure through WSL, Hyper-V, or mixed virtualization stacks, the lesson is familiar: the kernel’s most obscure cleanup paths can still become operational risk.
 A Small Scheduler Yield Becomes a Security Boundary
A Small Scheduler Yield Becomes a Security Boundary
The fix for CVE-2026-43292 is almost comically modest: add periodic cond_resched() calls while walking a vmalloc purge list, with need_resched() providing faster reaction under load and a batch threshold of 32 iterations preventing pathological runs even when the scheduler is not already shouting. Eight lines in mm/vmalloc.c are not the sort of patch that usually causes security teams to update dashboards.But the smallness of the patch is the story. The Linux kernel is full of code paths that assume cleanup is cheap because cleanup usually is cheap. Turn on memory-debugging infrastructure, make the cleanup list large enough, and suddenly “free some shadow pages” becomes “walk stacks under RCU read lock over and over while other CPUs wait for grace periods that cannot complete.”
That is not a confidentiality breach or privilege escalation. It is worse in the way infrastructure people hate most: it is a stall, a hang, a cascading failure mode. The machine is still there, the task is still running, logs are still being emitted, and yet forward progress is compromised long enough for watchdogs, memory pressure, and orchestration layers to start making bad decisions.
The kernel security ecosystem has increasingly treated these bugs as CVEs because availability is a security property. If a local workload, fuzzer, container, or test harness can push the kernel into a prolonged RCU stall and possible out-of-memory behavior, the operational impact is real even if no shell pops.
The Bug Lives Where Debugging Tools Meet Production Assumptions
The conditions matter. CVE-2026-43292 is tied toCONFIG_PAGE_OWNER, a kernel option used to track page allocation ownership, and KASAN, the Kernel Address Sanitizer infrastructure used to detect memory bugs. These are not normally enabled in stripped-down performance-first production kernels, but they are common in test kernels, CI systems, distro debug builds, kernel development, fuzzing, and environments where memory behavior is under investigation.That distinction should reduce panic, not interest. The systems most likely to expose this bug are exactly the systems that do the dangerous work before everyone else gets safe kernels: fuzzers, validation farms, debug-enabled staging fleets, and developer machines running experimental workloads. When those boxes stall, the result is not just a local inconvenience. It can mean lost test coverage, false negatives, wedged automation, or a misdiagnosed regression that sends engineers looking in the wrong subsystem.
The vulnerable path begins in vmalloc cleanup. The kernel accumulates virtual mapping areas on a purge list, and
purge_vmap_node() eventually releases associated KASAN shadow memory through kasan_release_vmalloc_node(). If the purge list contains hundreds or thousands of vmap_area entries, the cleanup loop can call into shadow-page freeing repeatedly.On its own, that may be acceptable. With page-owner tracking enabled, each free can trigger stack capture through
save_stack(), and stack unwinding can hold RCU read-side locks. Repeat that enough times without yielding, and a kernel worker thread can occupy the CPU long enough for RCU to declare that something has gone badly wrong.That is why the fix does not change memory accounting, locking design, or KASAN’s conceptual model. It changes the loop’s manners. Every 32 entries, or sooner if the scheduler says rescheduling is needed, the cleanup path yields.
RCU Stalls Are the Kernel’s Smoke Alarm, Not the Fire
Read-Copy-Update is one of the Linux kernel’s great concurrency bargains. Readers move fast and cheaply while updates wait for readers to pass through grace periods. The bargain works when read-side critical sections are brief enough that the system can eventually observe quiescent states and move on.An RCU stall report is the kernel saying that bargain has been violated for too long. It does not necessarily identify a deadlock, and it does not automatically mean memory corruption. It means progress assumptions are breaking: some CPU or task has remained in a state that prevents RCU from completing its housekeeping.
In CVE-2026-43292, the problem is not that one operation is catastrophically expensive. The problem is accumulation. A loop that repeatedly performs expensive free-side work while stack-unwinding under RCU can become, in effect, an unbounded read-side critical section. The kernel is doing legitimate work, but doing too much of it without letting the rest of the system breathe.
That is why this kind of issue is easy to underestimate from the patch alone. A reviewer can look at
cond_resched() and see a scheduling nicety. An operator sees something else: the difference between a noisy debug machine and a machine that stops answering in the middle of a test run.The presence of possible OOM behavior raises the stakes further. If cleanup cannot progress smoothly while pressure builds elsewhere, the memory-management system can enter a spiral where the work intended to reclaim or release resources itself consumes scheduling time and delays the mechanisms needed to stabilize the box.
The CVE Process Is Catching More “Boring” Kernel Failures
The modern Linux CVE stream includes many records that do not resemble the old mental model of a vulnerability. They may lack a neat attacker story. They may have no NVD score at publication. They may look like ordinary upstream bug fixes annotated after the fact by kernel.org.CVE-2026-43292 fits that pattern. NVD had received and published the record, but no CVSS score was listed at the time reflected in the submitted advisory text. The source is kernel.org, not a vendor marketing bulletin. The references point to stable kernel commits rather than a glossy exploit write-up.
For security teams, this creates friction. Patch management systems tend to like severity numbers. Kernel maintainers tend to ship fixes as part of a moving stream where the technical judgment is encoded in the patch, the stable backport, and the affected subsystem. Between those worlds sits an administrator trying to decide whether an unscored kernel CVE deserves attention before the next maintenance window.
The answer is not “treat every unscored Linux CVE as urgent.” That would collapse under its own noise. The answer is to classify by exposure and operational role. A laptop running a distribution kernel without page-owner debugging enabled is not in the same risk category as a syzkaller host, kernel CI worker, or virtualization node running debug kernels for regression hunting.
Microsoft’s appearance in the source trail may also confuse readers. This is not a Windows kernel flaw. It is a Linux kernel vulnerability surfaced through the Microsoft Security Response Center because Microsoft tracks vulnerabilities that may affect its products, services, cloud workloads, Linux-based components, or customer environments. In 2026, Windows and Linux are not separate kingdoms; they are neighbors sharing hypervisors, containers, CI pipelines, developer tooling, and update infrastructure.
Windows Shops Still Have Linux Kernel Risk
WindowsForum readers do not need to be told that Linux matters inside Microsoft’s ecosystem anymore. WSL made Linux a local developer dependency. Azure made Linux a first-class cloud workload. Hyper-V, containers, Kubernetes, security appliances, build agents, and cross-platform developer pipelines have blurred the operational boundary.A Windows-heavy organization may never manage bare-metal Linux desktops and still have Linux kernels everywhere. They may be inside WSL distributions on developer laptops. They may run on self-hosted GitHub Actions runners. They may underpin appliances. They may sit in Kubernetes nodes, storage gateways, monitoring collectors, or cloud images that nobody in the Windows endpoint team thinks of as “their” patching domain.
CVE-2026-43292 is especially relevant to environments where Linux is used as a diagnostic and development substrate. Kernel fuzzing systems, driver test rigs, security research labs, and performance troubleshooting machines are more likely to run unusual configurations. Those are also environments where a stall can waste human time fast.
The practical question for a Windows administrator is not whether their domain controllers are vulnerable. They are not running this code path. The question is whether their estate includes Linux kernels configured with page-owner tracking and KASAN-like instrumentation, and whether those machines are important enough that a stall can interrupt work, mask another bug, or trigger orchestration failures.
That is a narrower concern, but it is not a trivial one. Modern IT risk is increasingly made of narrow concerns stacked on top of one another.
The Patch Is a Yield, but the Design Lesson Is Backpressure
The kernel fix uses a familiar pattern: do a bounded amount of work, then give the scheduler a chance to run something else.need_resched() handles the obvious case where the scheduler already wants the CPU back. The fixed batch count handles the less obvious case where the loop might still run too long under light load before any external pressure makes the need explicit.That second part matters. Systems fail not only when they are overloaded but when code assumes overload is the only danger signal. A debug-enabled cleanup loop can be harmful even before the scheduler’s usual heuristics scream. By forcing a reschedule opportunity after 32 items, the patch puts a hard ceiling on how long this path can ignore the rest of the system.
There is a broader operating-system truth here. Memory cleanup paths are not exempt from latency discipline. The fact that a kernel thread is reclaiming, freeing, purging, or unwinding does not make it harmless. If the path touches expensive instrumentation, it needs the same batching and preemption awareness as any other long-running kernel operation.
The page-owner angle is particularly instructive. Page-owner tracking is there to help humans understand memory behavior. It makes the system more observable by recording allocation provenance. But observability has cost, and in this case the cost is paid during freeing as well as allocation. A feature designed to diagnose memory problems can become part of an availability problem if its overhead is multiplied inside an unbounded loop.
This is not an argument against KASAN or page-owner tracking. It is an argument against pretending debug infrastructure is outside the threat model. The tools used to find bugs run on real machines with real schedulers, and their failure modes deserve production-grade thinking.
The Syzbot Trail Shows Why Reproduction Is Not Resolution
The patch history also illustrates a recurring kernel-development reality: fixing the reported stack does not necessarily eliminate every symptom in the neighborhood. Syzbot testing reportedly showed a related stall pattern in a different path involving page-owner reset and page freeing. The original patch addressed the unbounded loop inkasan_release_vmalloc_node; similar stack-unwinding pressure could still surface elsewhere.That does not make the CVE fix meaningless. It makes the boundary clearer. CVE-2026-43292 is about one specific vmalloc cleanup loop and its failure to reschedule while releasing KASAN shadow pages. Other page-owner-induced stalls may require different patches in different paths.
This distinction is crucial for administrators reading kernel CVEs. A patch can be valid, necessary, and limited. It can reduce one avenue of stalls without making an entire class of debug-kernel latency issues disappear. Security advisories often compress that nuance into a few lines because the advisory’s job is to describe the resolved vulnerability, not the whole subsystem’s ergonomics.
For kernel developers and distro maintainers, the implication is broader. Once one cleanup loop needed a forced reschedule point because instrumentation made it too expensive, adjacent loops deserve scrutiny. The bug pattern is not “KASAN is broken” or “RCU is fragile.” The pattern is “instrumented memory paths can turn linear cleanup into scheduler starvation if they do not yield.”
That is how small fixes become architectural breadcrumbs. They tell maintainers where assumptions aged badly.
Severity Without a Score Is Still Severity
At publication, the submitted NVD data showed no CVSS 4.0, 3.x, or 2.0 score. That absence will tempt some dashboards to treat the item as undefined noise. In a mature patch program, unscored should not mean unseen.CVSS is useful when it exists and when the vulnerability shape maps cleanly to the scoring model. Availability bugs in specialized kernel configurations often do not. Attack vector, privileges required, and scope can be hard to summarize without overstating exposure or understating operational damage.
A plausible exploitation scenario is local and configuration-dependent. An attacker or workload would need a way to drive vmalloc churn and cleanup under the affected debug configuration. That is not the same as a remote unauthenticated wormable bug, but it is enough to matter on shared research systems, multi-tenant test boxes, or CI infrastructure that runs untrusted or semi-trusted workloads.
There is also a class of non-malicious failure here. A fuzzer, stress test, kernel module experiment, or pathological workload may trigger the stall accidentally. In real operations, accidental denial of service still burns time and capacity. Security teams sometimes draw too bright a line between hostile and incidental triggers, but users experience the same frozen machine either way.
For prioritization, the better rubric is practical exposure. If your kernels do not enable the relevant debugging options, urgency is low. If they do, and especially if the machines run adversarial test workloads, the fix belongs in the next kernel update cycle rather than the “someday” pile.
Distribution Backports Will Matter More Than CVE Text
The CVE record points to multiple stable kernel commits, which is another reminder that “fixed upstream” is not the same as “fixed where you run Linux.” Enterprise distributions, cloud images, vendor appliances, and embedded platforms each carry their own kernel versions and backport policies.Administrators should avoid matching only on mainline version numbers. A distribution may backport the eight-line fix to an older kernel without changing the headline version in a way that is obvious from
uname -r. Conversely, a system may appear modern enough but still be waiting for a vendor kernel package that includes the stable patch.The right check is vendor-specific: review the distribution’s kernel changelog, security advisory, or package metadata for the vmalloc/KASAN RCU-stall fix or the relevant CVE. In regulated environments, capture the vendor advisory or package version in the patch record rather than relying on the upstream commit hash alone.
For those building kernels directly, the fix is straightforward to audit. Look for the
KASAN_RELEASE_BATCH_SIZE definition and the rescheduling check inside kasan_release_vmalloc_node(). If you maintain an internal debug kernel, this is the kind of patch that should be cherry-picked quickly because it reduces noise and false failure during the very work debug kernels are meant to support.The more complicated question is whether to disable
CONFIG_PAGE_OWNER or KASAN in affected environments while waiting. That depends on why they are enabled. Turning them off may avoid this stall pattern, but it also removes diagnostic value. In most serious test environments, updating the kernel is the cleaner answer.The Cloud Angle Is Quiet but Real
Most cloud customers will never see this exact bug. They run provider-supplied kernels or distribution images without the relevant debug options. Managed services hide the kernel entirely. That should prevent the story from being inflated into a general cloud panic.But cloud providers, platform teams, and large SaaS operators absolutely run debug and instrumented kernels in qualification pipelines. They run fuzzing infrastructure. They maintain custom kernels. They test memory-management changes under heavy churn before those changes reach production fleets. CVE-2026-43292 lives in that pre-production world, and pre-production failures can have production consequences when they slow patch validation or hide regressions.
There is also the virtualization-host question. A Linux host running virtualized workloads can suffer local availability impact if the host kernel stalls. Whether an untrusted guest could realistically trigger the affected host path depends on configuration and exposure details that should not be assumed. Still, infrastructure teams should treat kernel availability bugs in host environments conservatively when debug options are enabled.
For Windows-centric shops using Hyper-V for Linux guests, the direction is usually reversed: the Linux guest stalls, not the Windows host. That still matters when the guest is a build runner, scanner, monitoring component, or developer environment. A hung Linux VM inside an otherwise healthy Windows platform is still an outage for the workflow that depends on it.
This is the dull integration reality of 2026. Windows reliability depends on Linux reliability more often than asset inventories admit.
The Fix Tells Administrators Where to Look
The operational signals for CVE-2026-43292 are not subtle if you know what to search for. Logs may show RCU preempt stall messages with stack traces involvingpurge_vmap_node() and kasan_release_vmalloc_node(). The workload may involve cleanup workers, vmalloc activity, KASAN shadow memory, and page-owner stack unwinding.That said, not every RCU stall is this CVE. RCU is a symptom-reporting mechanism, and many kernel paths can trigger stall warnings. Administrators should resist the urge to paste the first matching log line into a vulnerability spreadsheet and declare causality. The relevant combination is the vmalloc purge path, KASAN release, page-owner tracking, and long-running cleanup without rescheduling.
If you are triaging a live system, the first practical step is to identify the kernel build configuration. Confirm whether KASAN and page-owner tracking are enabled. Then compare the running kernel package with your vendor’s fixed builds. If the box is a test kernel compiled in-house, inspect the source or config repository directly.
For recurring failures, preserve full kernel logs before rebooting. RCU stall traces often contain the exact call stack needed to separate this issue from adjacent page-owner stalls. That distinction matters because a different stack may point to another fix, not this CVE.
The Eight-Line Patch Is a Warning About Kernel Debug Culture
Kernel debug features are sometimes treated as temporary scaffolding: enable them, catch bugs, disable them before the serious work begins. In reality, they often run continuously in places that matter. Fuzzing farms do not exist without instrumentation. CI systems need debug kernels to catch regressions early. Security researchers and driver developers live in the noisy middle ground between experiment and operation.That makes debug-kernel availability a first-class concern. A toolchain that finds memory bugs but regularly stalls under pressure will lose trust. Engineers will disable it, reduce coverage, or normalize warnings that should be investigated. In that sense, fixing CVE-2026-43292 is not just about preventing one denial-of-service condition. It is about keeping the diagnostic stack usable.
The Linux kernel community has become very good at finding memory safety defects with automation. Syzkaller and similar systems make obscure paths less obscure by relentlessly generating states human testers would never design. But automated discovery also produces a flood of failure modes that blur the line between bug, vulnerability, and instrumentation artifact.
This CVE is a product of that world. A fuzzer finds a stall. A developer narrows the path. Maintainers add a bounded reschedule point. Stable trees pick it up. A CVE record appears. Somewhere later, an administrator sees an unscored advisory and has to decide whether it matters.
The answer is that it matters most where the same automation and instrumentation are part of the job.
The Patch Window Should Follow the Kernel’s Job, Not the CVE’s Drama
For general-purpose desktops and servers running ordinary distribution kernels, CVE-2026-43292 should be handled through normal kernel updates. There is no evidence in the submitted record of remote exploitation, privilege escalation, or broad default exposure. Panic patching would be performative.For debug-enabled systems, the calculus changes. If the system runs KASAN, page-owner tracking, fuzzers, kernel stress tests, or untrusted local workloads, this is the kind of availability bug that deserves prompt remediation. The fix is small, stable-bound, and designed to reduce scheduler starvation rather than change visible kernel semantics.
For developers maintaining custom kernels, the patch also has low conceptual risk. It introduces periodic scheduling points into a cleanup loop that could previously run too long. That can alter timing, as any scheduling change can, but the intended effect is precisely to restore system responsiveness under worst-case cleanup loads.
The larger patch-management lesson is to stop using CVSS absence as an excuse for inaction. Classify the machine. Classify the kernel configuration. Classify the workload. Then decide.
The Practical Reading for WindowsForum’s Linux-Aware Admins
CVE-2026-43292 is not the kind of vulnerability that should dominate a Patch Tuesday war room, but it is exactly the kind that rewards teams with accurate inventories and punishes teams that treat Linux as somebody else’s problem. The important facts are narrow, concrete, and useful.- CVE-2026-43292 affects a Linux kernel vmalloc cleanup path where KASAN shadow-page release can run too long without yielding when page-owner tracking is enabled.
- The observed failure mode is an RCU stall and possible availability degradation, not a known remote code execution or privilege-escalation path.
- The upstream fix adds scheduler yield points in
kasan_release_vmalloc_node()usingneed_resched(),cond_resched(), and a batch limit of 32 iterations. - Systems most likely to care are debug kernels, fuzzing hosts, kernel CI workers, developer test machines, and other environments with KASAN or
CONFIG_PAGE_OWNERenabled. - Windows-centric organizations should still check Linux guests, WSL-adjacent developer workflows, CI runners, appliances, and cloud images where Linux kernels support critical work.
- Vendor kernel packages and distribution backports are the authoritative remediation path for most administrators, while custom-kernel maintainers can audit the vmalloc patch directly.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center