On May 8, 2026, CVE-2026-43338 was published for a Linux kernel Btrfs flaw in which qgroup ioctl operations failed to reserve enough transaction space, allowing quota-heavy operations near low-space conditions to trigger a transaction abort. The bug is not a glamorous remote-code-execution crisis, and that is precisely why it matters. It is the sort of storage-layer failure that turns a theoretical accounting mistake into an operational outage. For WindowsForum readers, the lesson is not “panic about Btrfs,” but “treat Linux filesystems inside modern Windows-adjacent estates as production dependencies, not exotic sidecars.”
CVE-2026-43338 sits in that awkward zone where the language of vulnerability management can make a bug sound either too frightening or too boring. The affected code lives in Btrfs, the copy-on-write Linux filesystem used by many distributions and storage-heavy deployments. The failure mode is a transaction abort caused by insufficient metadata reservation during quota-group operations.
That description will not compete with browser zero-days or wormable SMB flaws for attention. But a filesystem transaction abort is not an academic inconvenience. When the kernel decides it cannot safely complete metadata work, the blast radius can include failed unmounts, forced read-only behavior, interrupted maintenance, and a long evening of explaining why “out of space” did not simply mean “delete a few logs.”
The vulnerability record says the issue has been resolved in the Linux kernel and was received from kernel.org. The National Vulnerability Database had not yet assigned CVSS scoring at the time the record appeared, which leaves defenders in the familiar limbo of needing to prioritize before the scoring machinery catches up. That is not unusual for newly published kernel CVEs, but it does put more pressure on administrators to understand the technical path rather than wait for a red, orange, or yellow badge.
Microsoft’s Security Update Guide also lists the CVE, which is a reminder of how porous the old boundary between “Windows security” and “Linux security” has become. Enterprises running Windows desktops may still depend on Linux kernels through WSL, appliances, developer workstations, containers, cloud images, and mixed storage stacks. A Btrfs quota bug may not be a Windows bug, but it can still become a Windows shop’s incident.
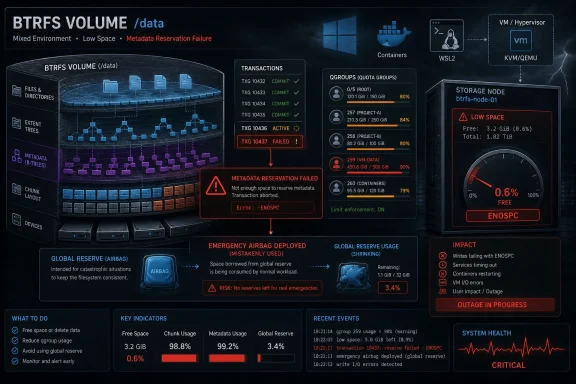
The bug is that predictability depended on a reserve that was not being made. The quota tree could fall back on the global block reserve, which is meant to help the filesystem complete critical metadata operations. That works until it does not, especially when a filesystem is already close to an ENOSPC condition — the kernel’s classic “no space left on device” error.
The reproducer in the CVE record is intentionally extreme. It creates a 1 GB Btrfs filesystem, fills most of it, enables quotas, then creates hundreds of thousands of qgroups. The record itself notes that this does not model a likely real-world workload. But proof-of-concept scripts often compress the weirdness of production into a few brutal lines, and this one makes the failure legible: quota metadata churn consumes transaction resources that were never reserved for it.
The important detail is not that someone will create 400,000 qgroups on a tiny test volume in production. It is that the storage layer had a path where accounting operations could overdraw shared emergency resources. Filesystems are full of such “mostly fine” assumptions, and the closer a volume gets to pressure, the more those assumptions turn into outages.
Quota groups are a good example. On a traditional filesystem, a quota can often be thought of as a ledger attached to a user, group, or project. In Btrfs, shared extents complicate the question of who “owns” space. Snapshots may share blocks until copy-on-write changes occur, and subvolumes may participate in nested accounting relationships.
That is why qgroup behavior has historically been one of Btrfs’s more delicate subsystems. It is not just counting bytes. It is tracking relationships between extents, subvolumes, references, and delayed metadata work. When the CVE description talks about delayed refs generated by updating the quota tree, it is pointing to precisely the kind of deferred filesystem bookkeeping that makes Btrfs flexible and occasionally unforgiving.
The fix, at a high level, is not conceptually dramatic. Reserve enough transaction items before doing the qgroup ioctl work. But in filesystem engineering, that kind of change is significant because reservation policy is part of the safety contract. If the filesystem says “I am beginning this transaction,” it needs to have already budgeted for the metadata consequences.
The problem is that emergency reserves are not meant to be a normal funding source. When ordinary operations rely on the emergency pool, they create competition with the very operations that may be needed to recover from pressure. That is how a quota-management operation can become more than a nuisance.
Think of it as the difference between a server using swap during an unusual spike and an application that is designed to live in swap all day. The first is a tolerable fallback. The second is a design smell waiting for a bad day. CVE-2026-43338 is the filesystem equivalent: qgroup ioctls were using a path that usually worked, but did not establish the reservation discipline needed under stress.
This is also why “low severity” intuition can be misleading before formal scoring arrives. A local administrative operation that causes a transaction abort may not let an attacker steal secrets or run code. But in multi-tenant systems, build farms, hosting environments, lab clusters, and developer platforms, availability failures can be security-relevant. If a less-privileged actor can influence quota operations indirectly, or if automated management tooling can be pushed into a pathological state, the story becomes more interesting than a local-only storage bug.
That script is not a field report. It is a stress lens. Its job is to force the kernel down a path where the missing reservation becomes undeniable. Administrators should resist the temptation to dismiss it simply because the loop count looks silly.
Production systems create their own absurdities. Snapshot retention jobs run longer than expected. CI systems spawn and delete worktrees at high rates. Container hosts accumulate layers, volumes, and subvolume-like structures. Desktop distributions that use Btrfs for rollback may quietly stack snapshots behind the user’s back. Space pressure often arrives not as a single dramatic event, but as an accumulation of ordinary automation.
The failure mode also intersects with an old Btrfs lesson: “free space” is not one number. Data space, metadata space, allocated chunks, unallocated device space, global reserve usage, and quota accounting can all tell different parts of the truth. A filesystem can look roomy in one view and be boxed in from another. CVE-2026-43338 lives in that gap between user-visible capacity and metadata reality.
WSL made Linux filesystems part of the daily developer workstation. Hyper-V, Dev Drive workflows, container tooling, and cloud-hosted Linux build agents have made mixed estates the default rather than the exception. Security teams that patch Windows Server aggressively may still have Linux kernels sitting under appliances, edge boxes, NAS software, CI runners, Kubernetes nodes, or developer images.
The MSRC listing is not evidence that NTFS suddenly has a Btrfs problem. It is evidence that Microsoft’s security ecosystem now tracks vulnerabilities far beyond the traditional Windows desktop boundary. That is good news for visibility, but it can also confuse prioritization. A CVE appearing in Microsoft’s guide does not automatically mean every Windows machine is exposed.
The practical question is narrower: where do you run Linux kernels with Btrfs enabled, and where are qgroups used? If the answer is “nowhere,” the CVE is background noise. If the answer is “our developer fleet, our lab machines, a few appliances, and some cloud images we forgot about,” the issue becomes a useful inventory test.
This is common in kernel land. A bug is identified, fixed upstream, backported into stable trees, and only later surfaced through CVE pipelines. Security tooling then reverses the human order of events: the CVE alert may be the first time many administrators hear about a bug that their distribution kernel may already have fixed.
That is why the right action is not to chase commit hashes in isolation. Most administrators should track their distribution’s kernel advisories and package versions. The kernel.org stable commits show where the fix came from; the vendor kernel package tells you whether your machine actually has it.
For custom kernel users, the story is less forgiving. If you build your own kernels, pin old stable branches, or run appliance-like images with slow-moving kernel trees, you own the backport question. CVE-2026-43338 is a reminder that “we are not vulnerable because this is obscure” is not a patch policy.
The risk is highest where untrusted or semi-trusted users can cause quota-management operations at scale, where automated systems create qgroups or subvolumes aggressively, or where Btrfs volumes are routinely operated near capacity. It is lower on systems that do not use Btrfs, do not enable qgroups, or have already consumed a vendor kernel update carrying the fix.
The artificial reproducer also requires administrative-style setup: formatting a device, mounting it, enabling quotas, and creating many qgroups. That does not look like a drive-by exploit. It looks like a kernel robustness problem exposed by pathological local activity.
Still, robustness problems in filesystems deserve respect. When storage fails, the user experience rarely maps neatly to the CVSS vocabulary. An outage caused by a transaction abort can mean service downtime, delayed backups, failed snapshots, or a recovery window that consumes the same operations team that was supposed to be patching the rest of the fleet.
A small lab server might enable Btrfs quotas because a desktop distribution or management tool expects them. A developer platform might create isolated environments at high volume. A CI farm might churn through subvolumes and snapshots while disk pressure rises. In each case, the human operator may not think of themselves as “using qgroups” in the same way they think of themselves as using Docker, Podman, Snapper, Timeshift, or a distribution rollback feature.
That is the trap. Filesystem features often arrive through higher-level tools. By the time the kernel bug matters, the administrator may be debugging symptoms several layers above the cause.
This is especially true on machines that are chronically near full. Low free space is not just an inconvenience in copy-on-write filesystems; it can change behavior. Metadata reservations, delayed references, chunk allocation, and cleanup ordering become central to whether the filesystem can safely finish what it started.
But bugs like CVE-2026-43338 feed an older anxiety: Btrfs can fail in ways that are hard to explain to people who grew up with simpler filesystems. “Quota ioctl did not reserve enough transaction items for delayed refs” is not the sort of sentence that calms a storage administrator during an outage.
That does not mean the rational answer is to abandon Btrfs. It means the rational answer is to operate it with an accurate mental model. Copy-on-write filesystems buy you features by moving complexity into metadata. Quotas and snapshots are not free. Space pressure is not benign. Emergency reserves are not capacity planning.
The healthier reading is that this bug was found, described precisely, and fixed. Kernel storage code improves through exactly this cycle. The less healthy pattern would be administrators enabling every advanced feature and then treating the filesystem as if it were a black box with infinite transactional slack.
That ambiguity is now a normal part of enterprise security. The kernel may be inside a Linux VM running on Hyper-V. It may be part of a WSL distribution image. It may live under a vendor appliance that reports into a Windows-centered operations dashboard. It may be buried in a container host that the application team considers “infrastructure.”
The fix path depends entirely on where the kernel comes from. Distribution kernels should be updated through the distribution’s package manager and advisory channel. Cloud images should follow the cloud vendor or image publisher’s kernel cadence. Appliances need vendor firmware or OS updates. Custom kernels need manual verification against the stable commits.
The worst answer is to close the ticket because the word “Linux” appears. The second-worst answer is to treat the MSRC listing as proof that Windows Update will solve everything. This is an inventory-driven problem.
On Linux hosts, administrators can inspect filesystem type, Btrfs usage, quota status, and qgroup configuration with standard Btrfs tooling. On managed fleets, the same questions should be translated into whatever inventory platform already exists. The point is not to run ad hoc archaeology on every machine forever; it is to fold filesystem feature state into asset visibility.
The systems worth prioritizing are not necessarily the largest ones. A small but critical developer server with aggressive snapshotting and poor space hygiene can be more exposed than a well-monitored storage node with disciplined capacity thresholds. The CVE’s reproducer uses a tiny filesystem for a reason: pressure makes the bug easier to trigger.
Administrators should also watch for kernel logs mentioning Btrfs transaction aborts, delayed refs, ENOSPC, or global reserve exhaustion. Those messages do not prove CVE-2026-43338 is the cause, but they are exactly the smoke that should prompt a closer look at filesystem health and patch level.
When a CVE appears after a fix has already landed in stable trees, some systems may be patched before the vulnerability is formally tracked. Others may remain exposed because their vendor kernel lags, even though the upstream fix exists. Meanwhile, scanners may flag or miss systems based on version heuristics that do not understand backports.
That is why kernel CVEs require more nuance than application CVEs. Version numbers can mislead when distributions backport fixes without changing the apparent upstream version. Conversely, a machine running an old-looking kernel may be safe, while a custom build with a newer version string may be missing a specific stable fix.
For security teams, the operational discipline is to map CVEs to vendor advisories and package changelogs, not just upstream tags. For administrators, the discipline is to avoid dismissing a CVE simply because there is no exploit kit or dramatic score attached. Filesystem availability is not glamorous, but it is foundational.
Filesystems under space pressure behave differently. Maintenance tasks that are safe at 60 percent utilization become risky at 98 percent. Snapshot cleanup may need space to free space. Quota accounting may need metadata to update the metadata that tells you how much space you have. This is the paradox that catches administrators who treat storage as a bucket rather than a transactional system.
Btrfs makes that paradox visible because it exposes so much metadata behavior. But the general pattern applies across modern storage stacks. Thin provisioning, deduplication, copy-on-write snapshots, reflinks, and layered container filesystems all create situations where apparent free space and operational headroom diverge.
The fix for CVE-2026-43338 closes one kernel bug. It does not remove the need to reserve operational headroom, monitor metadata pressure, and avoid running critical filesystems permanently at the edge. The kernel can be made more robust, but it cannot make poor capacity policy disappear.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Filesystem Bug Becomes a Security Record Because Availability Is Security
A Filesystem Bug Becomes a Security Record Because Availability Is Security
CVE-2026-43338 sits in that awkward zone where the language of vulnerability management can make a bug sound either too frightening or too boring. The affected code lives in Btrfs, the copy-on-write Linux filesystem used by many distributions and storage-heavy deployments. The failure mode is a transaction abort caused by insufficient metadata reservation during quota-group operations.That description will not compete with browser zero-days or wormable SMB flaws for attention. But a filesystem transaction abort is not an academic inconvenience. When the kernel decides it cannot safely complete metadata work, the blast radius can include failed unmounts, forced read-only behavior, interrupted maintenance, and a long evening of explaining why “out of space” did not simply mean “delete a few logs.”
The vulnerability record says the issue has been resolved in the Linux kernel and was received from kernel.org. The National Vulnerability Database had not yet assigned CVSS scoring at the time the record appeared, which leaves defenders in the familiar limbo of needing to prioritize before the scoring machinery catches up. That is not unusual for newly published kernel CVEs, but it does put more pressure on administrators to understand the technical path rather than wait for a red, orange, or yellow badge.
Microsoft’s Security Update Guide also lists the CVE, which is a reminder of how porous the old boundary between “Windows security” and “Linux security” has become. Enterprises running Windows desktops may still depend on Linux kernels through WSL, appliances, developer workstations, containers, cloud images, and mixed storage stacks. A Btrfs quota bug may not be a Windows bug, but it can still become a Windows shop’s incident.
The Broken Assumption Was Small, but It Lived in the Worst Possible Place
The root of CVE-2026-43338 is almost mundane: Btrfs qgroup ioctls joined a transaction without reserving the space needed for the updates they were about to cause. In Btrfs terms, qgroups are quota groups, a mechanism for accounting and limiting space use across subvolumes. They are useful precisely in environments where administrators want dense filesystem layouts to behave predictably.The bug is that predictability depended on a reserve that was not being made. The quota tree could fall back on the global block reserve, which is meant to help the filesystem complete critical metadata operations. That works until it does not, especially when a filesystem is already close to an ENOSPC condition — the kernel’s classic “no space left on device” error.
The reproducer in the CVE record is intentionally extreme. It creates a 1 GB Btrfs filesystem, fills most of it, enables quotas, then creates hundreds of thousands of qgroups. The record itself notes that this does not model a likely real-world workload. But proof-of-concept scripts often compress the weirdness of production into a few brutal lines, and this one makes the failure legible: quota metadata churn consumes transaction resources that were never reserved for it.
The important detail is not that someone will create 400,000 qgroups on a tiny test volume in production. It is that the storage layer had a path where accounting operations could overdraw shared emergency resources. Filesystems are full of such “mostly fine” assumptions, and the closer a volume gets to pressure, the more those assumptions turn into outages.
Btrfs Quotas Are Powerful Because They Are Complicated
Btrfs has long attracted administrators who want modern filesystem features without bolting them on afterward. Snapshots, subvolumes, checksumming, compression, send/receive replication, and online management are part of its appeal. Those same features also make space accounting much harder than it looks from the outside.Quota groups are a good example. On a traditional filesystem, a quota can often be thought of as a ledger attached to a user, group, or project. In Btrfs, shared extents complicate the question of who “owns” space. Snapshots may share blocks until copy-on-write changes occur, and subvolumes may participate in nested accounting relationships.
That is why qgroup behavior has historically been one of Btrfs’s more delicate subsystems. It is not just counting bytes. It is tracking relationships between extents, subvolumes, references, and delayed metadata work. When the CVE description talks about delayed refs generated by updating the quota tree, it is pointing to precisely the kind of deferred filesystem bookkeeping that makes Btrfs flexible and occasionally unforgiving.
The fix, at a high level, is not conceptually dramatic. Reserve enough transaction items before doing the qgroup ioctl work. But in filesystem engineering, that kind of change is significant because reservation policy is part of the safety contract. If the filesystem says “I am beginning this transaction,” it needs to have already budgeted for the metadata consequences.
The Global Reserve Is an Airbag, Not a Checking Account
The most revealing phrase in the CVE description is not “transaction abort.” It is the discussion of “abusing” the global block reserve. Every serious filesystem has mechanisms for getting itself out of tight spots. Btrfs’s global reserve is one of those mechanisms: a pool that can be used when metadata operations need enough breathing room to complete safely.The problem is that emergency reserves are not meant to be a normal funding source. When ordinary operations rely on the emergency pool, they create competition with the very operations that may be needed to recover from pressure. That is how a quota-management operation can become more than a nuisance.
Think of it as the difference between a server using swap during an unusual spike and an application that is designed to live in swap all day. The first is a tolerable fallback. The second is a design smell waiting for a bad day. CVE-2026-43338 is the filesystem equivalent: qgroup ioctls were using a path that usually worked, but did not establish the reservation discipline needed under stress.
This is also why “low severity” intuition can be misleading before formal scoring arrives. A local administrative operation that causes a transaction abort may not let an attacker steal secrets or run code. But in multi-tenant systems, build farms, hosting environments, lab clusters, and developer platforms, availability failures can be security-relevant. If a less-privileged actor can influence quota operations indirectly, or if automated management tooling can be pushed into a pathological state, the story becomes more interesting than a local-only storage bug.
The Reproducer Is Artificial, but the Operational Pattern Is Familiar
The CVE’s test script uses a null block device, a deliberately small filesystem, a large filler file, quota enablement, and a loop that creates qgroups at absurd scale. It then triggers the failure during unmount, when the filesystem must commit and clean up pending work. The kernel log shows Btrfs failing to run delayed refs and aborting the transaction with error -28.That script is not a field report. It is a stress lens. Its job is to force the kernel down a path where the missing reservation becomes undeniable. Administrators should resist the temptation to dismiss it simply because the loop count looks silly.
Production systems create their own absurdities. Snapshot retention jobs run longer than expected. CI systems spawn and delete worktrees at high rates. Container hosts accumulate layers, volumes, and subvolume-like structures. Desktop distributions that use Btrfs for rollback may quietly stack snapshots behind the user’s back. Space pressure often arrives not as a single dramatic event, but as an accumulation of ordinary automation.
The failure mode also intersects with an old Btrfs lesson: “free space” is not one number. Data space, metadata space, allocated chunks, unallocated device space, global reserve usage, and quota accounting can all tell different parts of the truth. A filesystem can look roomy in one view and be boxed in from another. CVE-2026-43338 lives in that gap between user-visible capacity and metadata reality.
Why Windows People Should Not Scroll Past a Linux Filesystem CVE
At first glance, this is a Linux kernel issue for Linux administrators. WindowsForum readers could be forgiven for wondering why it belongs in their queue at all. The answer is that modern Windows environments routinely carry Linux kernels and Linux storage assumptions into places that used to be Windows-only.WSL made Linux filesystems part of the daily developer workstation. Hyper-V, Dev Drive workflows, container tooling, and cloud-hosted Linux build agents have made mixed estates the default rather than the exception. Security teams that patch Windows Server aggressively may still have Linux kernels sitting under appliances, edge boxes, NAS software, CI runners, Kubernetes nodes, or developer images.
The MSRC listing is not evidence that NTFS suddenly has a Btrfs problem. It is evidence that Microsoft’s security ecosystem now tracks vulnerabilities far beyond the traditional Windows desktop boundary. That is good news for visibility, but it can also confuse prioritization. A CVE appearing in Microsoft’s guide does not automatically mean every Windows machine is exposed.
The practical question is narrower: where do you run Linux kernels with Btrfs enabled, and where are qgroups used? If the answer is “nowhere,” the CVE is background noise. If the answer is “our developer fleet, our lab machines, a few appliances, and some cloud images we forgot about,” the issue becomes a useful inventory test.
The Patch Tells Administrators What the Score Does Not
Because NVD scoring was not yet available when the record appeared, the patch trail matters. The relevant stable references show the fix being carried through kernel stable channels, including a 6.19 stable review patch dated April 8, 2026, with the upstream commit attributed before the CVE publication. That chronology matters because it suggests the engineering fix was already moving before the vulnerability record became widely visible.This is common in kernel land. A bug is identified, fixed upstream, backported into stable trees, and only later surfaced through CVE pipelines. Security tooling then reverses the human order of events: the CVE alert may be the first time many administrators hear about a bug that their distribution kernel may already have fixed.
That is why the right action is not to chase commit hashes in isolation. Most administrators should track their distribution’s kernel advisories and package versions. The kernel.org stable commits show where the fix came from; the vendor kernel package tells you whether your machine actually has it.
For custom kernel users, the story is less forgiving. If you build your own kernels, pin old stable branches, or run appliance-like images with slow-moving kernel trees, you own the backport question. CVE-2026-43338 is a reminder that “we are not vulnerable because this is obscure” is not a patch policy.
This Is a Denial-of-Service Story, Not a Data-Theft Story
There is no indication in the public record that CVE-2026-43338 enables remote code execution, privilege escalation, or direct data disclosure. The visible impact is availability: a transaction abort under quota-heavy, low-space conditions. That distinction matters because defenders should neither ignore the bug nor inflate it into something it is not.The risk is highest where untrusted or semi-trusted users can cause quota-management operations at scale, where automated systems create qgroups or subvolumes aggressively, or where Btrfs volumes are routinely operated near capacity. It is lower on systems that do not use Btrfs, do not enable qgroups, or have already consumed a vendor kernel update carrying the fix.
The artificial reproducer also requires administrative-style setup: formatting a device, mounting it, enabling quotas, and creating many qgroups. That does not look like a drive-by exploit. It looks like a kernel robustness problem exposed by pathological local activity.
Still, robustness problems in filesystems deserve respect. When storage fails, the user experience rarely maps neatly to the CVSS vocabulary. An outage caused by a transaction abort can mean service downtime, delayed backups, failed snapshots, or a recovery window that consumes the same operations team that was supposed to be patching the rest of the fleet.
The Quiet Risk Is Automation That Makes the Weird Normal
The most plausible real-world path is not a human typing the reproducer. It is automation. Storage lifecycle scripts, snapshot managers, container cleanup jobs, backup tools, and quota provisioning systems are exactly the kind of software that can convert a weird edge case into a scheduled event.A small lab server might enable Btrfs quotas because a desktop distribution or management tool expects them. A developer platform might create isolated environments at high volume. A CI farm might churn through subvolumes and snapshots while disk pressure rises. In each case, the human operator may not think of themselves as “using qgroups” in the same way they think of themselves as using Docker, Podman, Snapper, Timeshift, or a distribution rollback feature.
That is the trap. Filesystem features often arrive through higher-level tools. By the time the kernel bug matters, the administrator may be debugging symptoms several layers above the cause.
This is especially true on machines that are chronically near full. Low free space is not just an inconvenience in copy-on-write filesystems; it can change behavior. Metadata reservations, delayed references, chunk allocation, and cleanup ordering become central to whether the filesystem can safely finish what it started.
The Btrfs Reputation Problem Gets Another Footnote
Btrfs has spent years moving from “promising but scary” toward “mainstream enough that major distributions trust it for default installs.” It has earned much of that progress. The filesystem is not the experimental curiosity it was a decade ago, and its feature set remains compelling.But bugs like CVE-2026-43338 feed an older anxiety: Btrfs can fail in ways that are hard to explain to people who grew up with simpler filesystems. “Quota ioctl did not reserve enough transaction items for delayed refs” is not the sort of sentence that calms a storage administrator during an outage.
That does not mean the rational answer is to abandon Btrfs. It means the rational answer is to operate it with an accurate mental model. Copy-on-write filesystems buy you features by moving complexity into metadata. Quotas and snapshots are not free. Space pressure is not benign. Emergency reserves are not capacity planning.
The healthier reading is that this bug was found, described precisely, and fixed. Kernel storage code improves through exactly this cycle. The less healthy pattern would be administrators enabling every advanced feature and then treating the filesystem as if it were a black box with infinite transactional slack.
Patch Management Needs to Follow the Kernel, Not the Brand Name
For Windows-heavy organizations, the hardest part of this CVE may be ownership. If the vulnerable component is the Linux kernel, but the alert appeared in a Microsoft-facing security feed, who patches it? The Windows endpoint team? The Linux platform team? The cloud team? The developer productivity group?That ambiguity is now a normal part of enterprise security. The kernel may be inside a Linux VM running on Hyper-V. It may be part of a WSL distribution image. It may live under a vendor appliance that reports into a Windows-centered operations dashboard. It may be buried in a container host that the application team considers “infrastructure.”
The fix path depends entirely on where the kernel comes from. Distribution kernels should be updated through the distribution’s package manager and advisory channel. Cloud images should follow the cloud vendor or image publisher’s kernel cadence. Appliances need vendor firmware or OS updates. Custom kernels need manual verification against the stable commits.
The worst answer is to close the ticket because the word “Linux” appears. The second-worst answer is to treat the MSRC listing as proof that Windows Update will solve everything. This is an inventory-driven problem.
Administrators Should Look for Qgroups Before They Look for Drama
The fastest practical triage is simple: determine whether any relevant systems run Btrfs, whether quotas are enabled, and whether qgroups are used heavily. That is more useful than waiting for a CVSS number. It also separates exposed systems from machines that merely share the same broad operating-system family.On Linux hosts, administrators can inspect filesystem type, Btrfs usage, quota status, and qgroup configuration with standard Btrfs tooling. On managed fleets, the same questions should be translated into whatever inventory platform already exists. The point is not to run ad hoc archaeology on every machine forever; it is to fold filesystem feature state into asset visibility.
The systems worth prioritizing are not necessarily the largest ones. A small but critical developer server with aggressive snapshotting and poor space hygiene can be more exposed than a well-monitored storage node with disciplined capacity thresholds. The CVE’s reproducer uses a tiny filesystem for a reason: pressure makes the bug easier to trigger.
Administrators should also watch for kernel logs mentioning Btrfs transaction aborts, delayed refs, ENOSPC, or global reserve exhaustion. Those messages do not prove CVE-2026-43338 is the cause, but they are exactly the smoke that should prompt a closer look at filesystem health and patch level.
The Security Industry Still Struggles With Kernel CVE Timing
CVE-2026-43338 also illustrates a structural problem in vulnerability response. The kernel community often communicates through patches, mailing lists, stable queues, and distribution backports. Enterprise security programs often communicate through CVEs, dashboards, severity scores, and service-level agreements. Those two worlds overlap, but they are not synchronized.When a CVE appears after a fix has already landed in stable trees, some systems may be patched before the vulnerability is formally tracked. Others may remain exposed because their vendor kernel lags, even though the upstream fix exists. Meanwhile, scanners may flag or miss systems based on version heuristics that do not understand backports.
That is why kernel CVEs require more nuance than application CVEs. Version numbers can mislead when distributions backport fixes without changing the apparent upstream version. Conversely, a machine running an old-looking kernel may be safe, while a custom build with a newer version string may be missing a specific stable fix.
For security teams, the operational discipline is to map CVEs to vendor advisories and package changelogs, not just upstream tags. For administrators, the discipline is to avoid dismissing a CVE simply because there is no exploit kit or dramatic score attached. Filesystem availability is not glamorous, but it is foundational.
The Real Lesson Is Capacity Discipline
It is tempting to make CVE-2026-43338 a story about a missing reservation call. Technically, that is fair. Operationally, the deeper lesson is that capacity discipline is a security control.Filesystems under space pressure behave differently. Maintenance tasks that are safe at 60 percent utilization become risky at 98 percent. Snapshot cleanup may need space to free space. Quota accounting may need metadata to update the metadata that tells you how much space you have. This is the paradox that catches administrators who treat storage as a bucket rather than a transactional system.
Btrfs makes that paradox visible because it exposes so much metadata behavior. But the general pattern applies across modern storage stacks. Thin provisioning, deduplication, copy-on-write snapshots, reflinks, and layered container filesystems all create situations where apparent free space and operational headroom diverge.
The fix for CVE-2026-43338 closes one kernel bug. It does not remove the need to reserve operational headroom, monitor metadata pressure, and avoid running critical filesystems permanently at the edge. The kernel can be made more robust, but it cannot make poor capacity policy disappear.
The CVE That Tells You to Audit Your Assumptions
The concrete response to this vulnerability is not complicated, but it should be deliberate. Treat the CVE as a trigger to verify kernel patch state, Btrfs quota usage, and storage pressure across systems that may not sit neatly inside the Windows or Linux team’s mental boundary.- Systems that do not run Btrfs are not directly affected by this filesystem bug.
- Systems that run Btrfs without quotas or qgroups enabled have a narrower exposure than systems using quota accounting heavily.
- Systems running vendor kernels should be checked against distribution or appliance advisories rather than judged only by upstream version numbers.
- Systems with custom kernels need explicit confirmation that the stable fix for qgroup ioctl transaction reservation has been applied.
- Systems that routinely operate near full capacity deserve priority because the demonstrated failure depends on metadata pressure and ENOSPC conditions.
- Security teams should treat the MSRC listing as a visibility signal, not as proof that Windows Update alone remediates every affected environment.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center