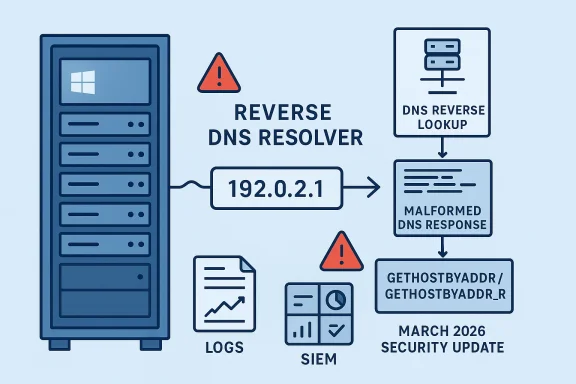
Microsoft’s March 2026 security guidance includes CVE-2026-4437, a flaw described as a case where gethostbyaddr and gethostbyaddr_r may incorrectly handle a DNS response. The wording is brief, but it signals a bug in a long-standing reverse-lookup path that many applications still depend on for logging, authentication decisions, and network hygiene. For Windows administrators, the practical significance is less about a flashy exploit story and more about the risk that a malformed or unexpected DNS reply could destabilize or mislead software that still relies on legacy resolver APIs.
Reverse DNS remains one of those infrastructure features that most people only notice when it fails. Applications call gethostbyaddr or its reentrant sibling gethostbyaddr_r to translate an IP address back into a hostname, often for audit logs, access controls, or “who is this client?” checks. Those calls are old, widely embedded, and still present in a surprising amount of enterprise software because they are easy to use and often deeply inherited from earlier network stacks.
Microsoft’s own Security Update Guide has become the canonical place where these issues are tracked, with the company increasingly centralizing CVE and advisory information in that portal and its associated feeds. Microsoft says the guide is a one-stop source for security update information, including CVEs and additional advisory data that may not fit the standard CVE format, which makes it the right place to watch for nuance around cases like this one. That matters because a short CVE title often hides a broader operational story about impact, exploitability, and what exactly breaks when the edge case is hit.
The naming of gethostbyaddr and gethostbyaddr_r also points to a familiar tension in platform engineering: backwards compatibility versus modern safety. Resolver APIs from earlier network eras can be brittle when confronted with today’s heterogeneous DNS environments, where split-horizon configurations, response truncation, recursive chains, and security products all influence what comes back from a lookup. A flaw in response handling is therefore not just a parser bug; it is a reminder that name resolution still sits on a stack of assumptions built for a much simpler internet.
Microsoft has not framed this as one of the high-drama classes that dominate headlines, such as a remote code execution in a server daemon or a wormable protocol bug. Instead, the description suggests a correctness or validation failure in the way the APIs interpret DNS data. That kind of bug can be just as important in the enterprise, because it may create false trust, false negatives, crashes, or application misbehavior in code paths that are difficult to test exhaustively.
That wording is intentionally broad, and that breadth is important. It leaves open several possible failure modes: an application may receive a malformed result, a lookup may return misleading data, or a library may mishandle memory or state while parsing the answer. The public description alone does not tell us which of those paths applies, so defenders should avoid overfitting the advisory into a single scenario that the vendor has not confirmed.
Microsoft’s security documentation ecosystem has gradually moved toward faster publication, better filtering, and machine-readable advisory data. That shift is useful here because it encourages defenders to think about vulnerability intelligence as a live operational feed rather than a static bulletin. If an issue is described in terse terms on the first day, later metadata and revisions often provide the real clues about severity and affected surfaces.
There is also a broader pattern in Microsoft’s recent CVE catalog: many issues in March 2026 are affecting infrastructure primitives rather than end-user apps alone. That reflects the reality of modern Windows environments, where networking, graphics, kernel, and identity components all sit on critical-path code. Even when a bug is not obviously remote code execution, it can still matter because it touches foundational behavior used by countless downstream processes.
The immediate enterprise question is therefore not “Can an attacker pop a shell with this?” but rather “What business logic depends on trustworthy reverse DNS?” That shift in framing is crucial, because resolver bugs frequently become enabling conditions for other failures. In a large environment, they can also undermine incident response by making host attribution less reliable than teams assume.
One consequence is that response-handling bugs can create security ambiguity. If a host lookup returns the wrong record, software may log an incorrect peer identity or associate a request with the wrong system. If the bug instead causes the API to reject valid data, the result can be availability impact: failed lookups, degraded service, or fallback behavior that was never meant to be a security boundary.
That makes a security bulletin like this one a warning shot for software vendors as much as for customers. Any code that wraps or depends on these APIs should be reviewed for assumptions about null termination, fixed buffer sizes, and error handling. Especially in mixed environments, the same endpoint may be used by old line-of-business software, system utilities, and third-party agents that each interpret failures differently.
The problem is compounded by the fact that many organizations still use reverse DNS as a convenience signal even when they know it is not authoritative. An internal dashboard might display a hostname rather than an IP address because it is easier for operators to read. That is harmless until the lookup path starts returning inconsistent answers, at which point people may chase phantom issues in the wrong layer.
A robust resolver path should reject clearly invalid data, preserve memory safety, and avoid converting parsing errors into undefined behavior. If any of those properties fail, even a routine reverse lookup can become an attack surface. Microsoft’s choice of wording suggests the company wants defenders to focus on response validation rather than on any one exploit technique.
This also means log correlation becomes important. If a reverse-lookup anomaly appears alongside service instability, packet captures and resolver traces will matter more than the CVE headline. In practice, defenders should treat the advisory as a cue to observe how their own workloads behave, not as a definitive description of every possible failure.
In operational terms, the question is not merely whether a patch is available. It is whether the patch can be deployed without breaking systems that have quietly depended on legacy resolver behavior for years. That balancing act is common in infrastructure updates, and it is one reason phased rollout remains the sane approach for enterprise patching.
Microsoft’s recent security-disclosure model has also become more transparent and more machine-readable, which helps defenders react faster when an issue lands. The company has been expanding the Security Update Guide and related advisory mechanisms to make CVE data easier to consume programmatically, and that matters because organizations increasingly automate patch intake. Better metadata is not a cure, but it is a meaningful upgrade to the response process.
That is why defenders should avoid dismissing this class of issue as low priority simply because the title sounds mundane. Mundane bugs in core infrastructure often create the most frustrating downstream support cases. They are also the ones most likely to be overlooked in busy environments until a particular application starts behaving badly.
For rivals and adjacent ecosystems, the lesson is similar. DNS correctness is a shared responsibility across operating systems, libraries, and applications. In a market where identity, telemetry, and zero-trust architectures rely on dependable name resolution, vendors that can prove robust handling of edge-case responses gain credibility.
Another important signal will be whether third-party trackers, security researchers, or application vendors identify concrete exploitation or compatibility patterns. That kind of follow-on analysis often determines how aggressively enterprises prioritize deployment. In the meantime, the safe assumption is that any code path depending on reverse DNS deserves review, especially in systems that still use legacy networking APIs.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Reverse DNS remains one of those infrastructure features that most people only notice when it fails. Applications call gethostbyaddr or its reentrant sibling gethostbyaddr_r to translate an IP address back into a hostname, often for audit logs, access controls, or “who is this client?” checks. Those calls are old, widely embedded, and still present in a surprising amount of enterprise software because they are easy to use and often deeply inherited from earlier network stacks.Microsoft’s own Security Update Guide has become the canonical place where these issues are tracked, with the company increasingly centralizing CVE and advisory information in that portal and its associated feeds. Microsoft says the guide is a one-stop source for security update information, including CVEs and additional advisory data that may not fit the standard CVE format, which makes it the right place to watch for nuance around cases like this one. That matters because a short CVE title often hides a broader operational story about impact, exploitability, and what exactly breaks when the edge case is hit.
The naming of gethostbyaddr and gethostbyaddr_r also points to a familiar tension in platform engineering: backwards compatibility versus modern safety. Resolver APIs from earlier network eras can be brittle when confronted with today’s heterogeneous DNS environments, where split-horizon configurations, response truncation, recursive chains, and security products all influence what comes back from a lookup. A flaw in response handling is therefore not just a parser bug; it is a reminder that name resolution still sits on a stack of assumptions built for a much simpler internet.
Microsoft has not framed this as one of the high-drama classes that dominate headlines, such as a remote code execution in a server daemon or a wormable protocol bug. Instead, the description suggests a correctness or validation failure in the way the APIs interpret DNS data. That kind of bug can be just as important in the enterprise, because it may create false trust, false negatives, crashes, or application misbehavior in code paths that are difficult to test exhaustively.
Why reverse lookups still matter
Reverse lookups are often used as a secondary signal rather than the sole basis for trust. Even so, organizations commonly pipe the resulting hostnames into SIEMs, VPN gateways, mail systems, and admin consoles, where a bad answer can create confusion or a policy mismatch. In other words, a small DNS parsing defect can become a broad operational problem once it crosses layers.- Logging pipelines may record the wrong host identity.
- Authentication workflows may make decisions on incomplete data.
- Monitoring tools may misclassify clients or endpoints.
- Automation scripts may fail if they assume clean resolver behavior.
- Legacy applications may expose the bug because they still use older libc-style interfaces.
Overview
A Microsoft CVE that references resolver functions usually deserves careful reading because these APIs sit at the boundary between application code and network-trusted input. The functions named in CVE-2026-4437 are not obscure internals; they are standard interfaces that have existed for decades and are used by both native software and middleware. When Microsoft says they “may incorrectly handle DNS response,” the likely takeaway is that a particular response structure, size, or content pattern is not being processed safely or as intended.That wording is intentionally broad, and that breadth is important. It leaves open several possible failure modes: an application may receive a malformed result, a lookup may return misleading data, or a library may mishandle memory or state while parsing the answer. The public description alone does not tell us which of those paths applies, so defenders should avoid overfitting the advisory into a single scenario that the vendor has not confirmed.
Microsoft’s security documentation ecosystem has gradually moved toward faster publication, better filtering, and machine-readable advisory data. That shift is useful here because it encourages defenders to think about vulnerability intelligence as a live operational feed rather than a static bulletin. If an issue is described in terse terms on the first day, later metadata and revisions often provide the real clues about severity and affected surfaces.
There is also a broader pattern in Microsoft’s recent CVE catalog: many issues in March 2026 are affecting infrastructure primitives rather than end-user apps alone. That reflects the reality of modern Windows environments, where networking, graphics, kernel, and identity components all sit on critical-path code. Even when a bug is not obviously remote code execution, it can still matter because it touches foundational behavior used by countless downstream processes.
The immediate enterprise question is therefore not “Can an attacker pop a shell with this?” but rather “What business logic depends on trustworthy reverse DNS?” That shift in framing is crucial, because resolver bugs frequently become enabling conditions for other failures. In a large environment, they can also undermine incident response by making host attribution less reliable than teams assume.
What the advisory wording suggests
The phrase “incorrectly handle DNS response” implies Microsoft is warning about a validation or parsing issue rather than a protocol redesign. That usually means the fix will be relatively surgical, but the operational impact may be outsized if many applications share the same resolver path. It is the classic small bug, wide blast radius problem.- The issue appears to be in the response-handling path.
- The affected surface likely includes applications that rely on the Windows networking stack.
- The risk may be amplified in environments with heavy DNS dependency.
- Legacy code paths are often the hardest to audit and replace.
- The practical impact may vary widely by application behavior.
Technical Significance
A resolver bug becomes interesting because DNS is not simply a naming service; it is a trust boundary. Applications often assume that if a lookup succeeds, the returned data is structurally valid, logically consistent, and safe to use. When an API mishandles a response, that assumption can fail in ways that are subtle, intermittent, and difficult to reproduce.One consequence is that response-handling bugs can create security ambiguity. If a host lookup returns the wrong record, software may log an incorrect peer identity or associate a request with the wrong system. If the bug instead causes the API to reject valid data, the result can be availability impact: failed lookups, degraded service, or fallback behavior that was never meant to be a security boundary.
Why legacy resolver APIs are fragile
The gethostbyaddr family predates many of the safety improvements developers now expect from networking libraries. Its design reflects an older world where IPv4 was dominant, response formats were simpler, and applications were less defensive about malformed input. Even today, these interfaces survive because replacing them can be expensive and risky in enterprise codebases that have accumulated decades of compatibility debt.That makes a security bulletin like this one a warning shot for software vendors as much as for customers. Any code that wraps or depends on these APIs should be reviewed for assumptions about null termination, fixed buffer sizes, and error handling. Especially in mixed environments, the same endpoint may be used by old line-of-business software, system utilities, and third-party agents that each interpret failures differently.
Operational impact pathways
The interesting part of resolver bugs is how they cascade. A malformed DNS answer can surface first as a logging anomaly, then as an authentication edge case, then as a broken automation script, and finally as an incident-response blind spot. The bug is still “just DNS” at the source, but the organizational impact is much broader.- Incorrect host attribution can undermine audit trails.
- Unexpected errors can break monitoring or inventory tools.
- Fallback logic may choose weaker or less trustworthy paths.
- Security controls that rely on reverse lookup may misfire.
- Distributed systems can see inconsistent behavior across nodes.
Enterprise Exposure
Enterprise environments are more likely than consumer PCs to feel this kind of issue because they run software that still depends on old network abstractions. Domain controllers, SIEM collectors, proxy services, mail gateways, EDR agents, inventory tools, and VPN concentrators all tend to perform name lookups in the background. If one of those components relies on a buggy resolver path, the effect may appear sporadically and only under certain network conditions.The problem is compounded by the fact that many organizations still use reverse DNS as a convenience signal even when they know it is not authoritative. An internal dashboard might display a hostname rather than an IP address because it is easier for operators to read. That is harmless until the lookup path starts returning inconsistent answers, at which point people may chase phantom issues in the wrong layer.
Where defenders should look first
Security teams should begin with anything that uses reverse lookup as a gate, not just as a label. That includes homegrown apps, appliances running Windows-based components, and custom scripts that were never rewritten after the move to newer APIs. If the output of a reverse DNS call affects policy, the bug matters more than if it only affects a cosmetic field.- Inventory services that call gethostbyaddr or gethostbyaddr_r.
- Identify whether the lookup result is used for display only or for decision-making.
- Review any code that parses or stores reverse-lookup results.
- Test behavior under malformed, truncated, or unusual DNS responses.
- Confirm whether fallback behavior could create a security gap.
Why enterprise impact can outstrip consumer impact
Consumer systems usually have fewer custom services making these calls directly. Enterprises, by contrast, accumulate helper applications, line-of-business software, and admin tooling that often outlive the assumptions under which they were written. That makes a seemingly narrow resolver defect more likely to cause real operational pain in business environments than on a typical home PC.- More legacy software means more exposure to old APIs.
- More automation means more dependence on predictable lookup behavior.
- More logging and telemetry means more places for bad data to spread.
- More security controls mean more chances for a malformed response to cause confusion.
- More bespoke integration means more code paths to audit.
DNS Response Handling
The core of this advisory is the phrase “may incorrectly handle DNS response.” That usually signals that the trust relationship between resolver and application is weaker than it should be. DNS is inherently distributed and dynamic, so software that consumes it must be resilient to malformed, incomplete, or surprising replies.A robust resolver path should reject clearly invalid data, preserve memory safety, and avoid converting parsing errors into undefined behavior. If any of those properties fail, even a routine reverse lookup can become an attack surface. Microsoft’s choice of wording suggests the company wants defenders to focus on response validation rather than on any one exploit technique.
Common failure modes in resolver code
Resolver bugs often appear in a handful of recognizable forms. They may mishandle buffer boundaries, misinterpret record lengths, or fail to distinguish between a valid but unexpected response and a truly malformed one. Sometimes the failure is not a crash at all, but a logic error that causes applications to accept data they should have rejected.- Length miscalculation can corrupt memory or truncate output.
- State confusion can return stale or mixed results.
- Validation gaps can allow malformed packets to be processed.
- Error propagation bugs can convert a failed lookup into a misleading success.
- Reentrancy issues can show up under concurrent load.
Why DNS bugs are hard to reproduce
DNS problems are notoriously environment-dependent. The same query may succeed on one network, fail on another, or behave differently behind a recursive resolver, a caching proxy, or a security appliance. That makes bugs like CVE-2026-4437 frustrating for operators because they can vanish in lab testing and reappear only under real production conditions.This also means log correlation becomes important. If a reverse-lookup anomaly appears alongside service instability, packet captures and resolver traces will matter more than the CVE headline. In practice, defenders should treat the advisory as a cue to observe how their own workloads behave, not as a definitive description of every possible failure.
Patch Management Strategy
The best response to a resolver CVE is rarely dramatic, but it does need to be disciplined. Administrators should first determine which Windows builds and dependent applications are covered by the March 2026 security release, then prioritize systems that perform network identity lookups at scale. The update guide exists specifically to help teams map CVEs to products and remediation paths, which is why Microsoft has invested so much in centralizing those advisories.In operational terms, the question is not merely whether a patch is available. It is whether the patch can be deployed without breaking systems that have quietly depended on legacy resolver behavior for years. That balancing act is common in infrastructure updates, and it is one reason phased rollout remains the sane approach for enterprise patching.
Recommended rollout sequence
A cautious rollout should start with low-risk systems that are representative of production behavior. Once the patch is validated, move to servers and endpoints that perform heavy reverse lookups or host business-critical services. This is especially important when the vulnerable function may be used by multiple applications on the same machine.- Review Microsoft’s update entry for the affected products.
- Test the patch on a representative lab or pilot ring.
- Verify reverse DNS behavior for your highest-value applications.
- Watch for resolver timeouts, logging anomalies, and service restarts.
- Expand deployment in stages rather than in one fleet-wide push.
What to verify after installation
Even after patching, validation should continue. A resolver bug may have side effects that are not immediately obvious, especially if the fix changes how edge-case responses are handled. Teams should compare baseline behavior before and after installation to ensure no hidden dependencies break.- Reverse lookups return expected hostnames.
- Error handling still behaves cleanly in custom apps.
- SIEM and audit logs continue to show usable attribution.
- Monitoring agents do not report DNS-related instability.
- Authentication and access-control workflows remain unchanged.
Broader Security Context
This CVE fits a larger pattern in which foundational Windows components are being scrutinized not just for overt exploits but for correctness under edge conditions. That is a healthy sign, even if it makes the security catalog look noisy. Modern systems fail in the seams, and DNS is one of the widest seams in the stack.Microsoft’s recent security-disclosure model has also become more transparent and more machine-readable, which helps defenders react faster when an issue lands. The company has been expanding the Security Update Guide and related advisory mechanisms to make CVE data easier to consume programmatically, and that matters because organizations increasingly automate patch intake. Better metadata is not a cure, but it is a meaningful upgrade to the response process.
Why “just a bug” still matters
It is tempting to rank vulnerabilities only by whether they enable obvious remote compromise. But infrastructure bugs that alter identity, logging, or trust decisions can have long-tail effects that are harder to quantify and equally damaging. A false hostname in the wrong place can influence investigations, access rules, and automated remediation.That is why defenders should avoid dismissing this class of issue as low priority simply because the title sounds mundane. Mundane bugs in core infrastructure often create the most frustrating downstream support cases. They are also the ones most likely to be overlooked in busy environments until a particular application starts behaving badly.
Competitive and market implications
For Microsoft, the presence of a resolver advisory reinforces a long-term reality: Windows is still judged not only by headline product features but by the reliability of the plumbing. Enterprises compare operating systems and management stacks partly on how predictably they behave under stress. If core networking APIs are patched cleanly and transparently, that supports trust in the platform.For rivals and adjacent ecosystems, the lesson is similar. DNS correctness is a shared responsibility across operating systems, libraries, and applications. In a market where identity, telemetry, and zero-trust architectures rely on dependable name resolution, vendors that can prove robust handling of edge-case responses gain credibility.
Strengths and Opportunities
This advisory also highlights where organizations can improve beyond the immediate patch. The best response is not just to install updates, but to use the event as a forcing function for modernization. That can help reduce the chance that the next resolver bug becomes a production incident.- Inventory legacy resolver usage across endpoints and server workloads.
- Replace deprecated APIs with safer modern equivalents where possible.
- Audit security controls that rely on reverse DNS as a trust signal.
- Improve logging so IP, hostname, and service identity are recorded together.
- Expand test coverage for malformed and truncated DNS responses.
- Use phased patch rings to reduce rollout risk.
- Document fallback behavior in apps that depend on name resolution.
Risks and Concerns
The biggest risk is not that every system will fail at once, but that the bug will surface selectively and be mistaken for something else. That can delay remediation and send admins chasing network ghosts when the root cause is actually in the resolver layer. As with many infrastructure CVEs, the operational footprint may be wider than the advisory title implies.- Legacy applications may rely on undocumented resolver quirks.
- Reverse DNS trust may be embedded in policy or logging workflows.
- Edge-case failures may appear only under production DNS patterns.
- Partial fixes in one tier can leave downstream systems exposed.
- Troubleshooting time may increase if teams do not recognize the symptom set.
- Patch regression risk is real in software that has used these APIs for years.
- Misattribution in logs could complicate incident response.
Looking Ahead
The main thing to watch is whether Microsoft later publishes richer technical detail or revised severity guidance for CVE-2026-4437. The initial advisory language is sparse, which is common early in the disclosure cycle, but defenders should monitor the update guide for product scope changes or clarifications. If the bug turns out to affect more resolver-adjacent code than the title implies, the operational significance could widen quickly.Another important signal will be whether third-party trackers, security researchers, or application vendors identify concrete exploitation or compatibility patterns. That kind of follow-on analysis often determines how aggressively enterprises prioritize deployment. In the meantime, the safe assumption is that any code path depending on reverse DNS deserves review, especially in systems that still use legacy networking APIs.
- Watch for Microsoft advisory revisions and any added technical notes.
- Monitor application logs for DNS-related anomalies after patching.
- Test business-critical software that performs reverse lookups.
- Review legacy code that still calls gethostbyaddr-family functions.
- Confirm that security controls do not depend too heavily on reverse DNS.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: