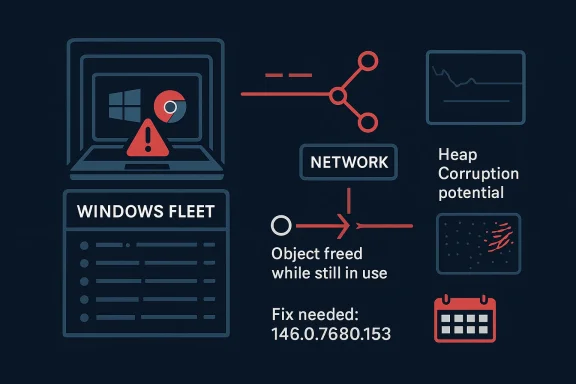
Chromium’s CVE-2026-4454 is the kind of browser bug that can quietly become an enterprise headache long after the initial patch lands. Google describes it as a use-after-free in Network that could let a remote attacker potentially trigger heap corruption through a crafted HTML page, and it affects Chrome prior to 146.0.7680.153. Microsoft has surfaced the same issue in its Security Update Guide, which is a strong signal that downstream Chromium consumers on Windows should treat the fix as operationally relevant, not just theoretical housekeeping rs because browser vulnerabilities in networking code tend to sit at the intersection of exposure and reach. A flaw in the Network component can be exercised by normal browsing activity, which means the attack path is often as simple as persuading a user to load a malicious page. That makes the issue especially important for Windows environments where Chrome, Edge, and Chromium-derived applications are part of the daily software mix. The patch threshold is clear, the attack surface is broad, and the remediation window is short .
At the same time, closure tells its own story. Google’s March 2026 stable-channel cadence shows a fast-moving security release train, with Chrome 146 promoted to stable on March 10, 2026 and later desktop updates addressing additional security issues in the same branch. In that context, CVE-2026-4454 is not an isolated event; it is part of a broader hardening cycle around a major browser generation that is still settling into the stable channel (chromereleases.googleblog.com).
Chromium has spent years evolving into the de facto browser platform for Windows, macOS, Linux, and Android. Chrome, Edge, Brave, Vivaldi, Opera, and numerous embedded web views all inherit large portions of that codebase, which means one upstream security fix can ripple across millions of endpoints. That architecture brings enormous advantages in consistency and update velocity, but it also means that a flaw in a core subsystem like Network can instantly become a supply-chain event.
Use-after-free bugs remain one of the browser world’s most persistent memory-safety problems because they arise at the boundary between object lifetime management and attacker-controlled timing. In practical terms, the vulnerability is triggered when code continues to use an object after it has been freed, creating the possibility of memory reuse, state confusion, or controlled corruption. For a browser, that can translate into process instability, denial of service, or, in the worst case, exploitable memory corruption.
Google’s Chrome release notes show a familiar pattern: the company withholds some details until a majority of users are protected, while still flagging the severity and the affected version range. That approach balances transparency with defensive delay, and it has become standard practice for browser vendors because the gap between public disclosure and patch adoption is often when exploitation risk rises the fastest. Chrome’s March 2026 security updates also show that Google is willing to move quickly when high-severity issues surface in the stable branch (chromereleases.googleblog.com).
Microsoft’s inclusion of Chromium CVEs in the Security Update Guide is also part of the modern patching picture. Microsoft has explicitly said that CVE details and CWE information may be mirrored into its update ecosystem to help customers track vulnerabilities across products that embed Chromium code. That means Windows administrators cannot safely treat Chrome and Edge as separate security universes; they are linked by a common engine and, in many cases, by the same remediation logic.
The specific significance of CVE-2026-4454 is that it sits in Network, not in a niche subsystem most people never touch. Network-layer browser code is attractive to attackers because it processes hostile input constantly, often before user awareness or policy enforcement has a chance to help. A malformed page is enough; no plug-in, no extension, and no exotic user action is required.
The version floor matters because it gives defenders a concrete decision point. If an estate is running anything earlier than 146.0.7680.153, the browser should be treated as exposed until the relevant update is deployed and confirmed. In a large Windows environment, that verification step matters almost as much as the patch itself, because patch management failures often happen at the layer between download and actual execution.
Google’s March 2026 stable-channel notes reinforce that reality. Chrome 146 moved to stable on March 10, 2026, and the release stream continued to absorb fixes over the following days and weeks. That means a “current” Chrome install in the real world can lag behind the latest patched build for a nontrivial amount of time, especially in enterprises with deferred updates or testing rings (chromereleases.googleblog.com).
This matters because “network bug” sounds narrower than it really is. In browser engineering terms, network code is often the first place a malicious page can influence parser state, request lifetimes, connection reuse, or response handling. A use-after-free there is especially valuable to attackers because it can occur before higher-level mitigations have had a chance to normalize the data stream.
In a successful exploitation chain, the goal is usually to move from a predictable crash or corrupt state into something more controllable. The exact outcome depends on allocator behavior, browser build details, and sandbox barriers, but the initial step is often the same: get the target to process malformed content in a vulnerable code path. That is why defenders cannot safely dismiss a use-after-free as “just a crash.”
Consumers, by contrast, are more likely to experience the vulnerability as a single device problem: a malicious site, a browser crash, or a momentary compromise attempt. That is serious enough on its own, but it usually lacks the network adjacency and data concentration of corporate environments. The difference is not in the vulnerability itself; it is in what the browser is allowed to reach once it is opened.
Second, patch verification should be specific. It is not enough to know that the browser was updated sometime this month. Administrators should confirm the exact Chrome or Chromium build number and ensure it meets or exceeds 146.0.7680.153. In environments with staggered rollout policies, it is entirely possible for some devices to remain exposed after the patch has been approved centrally.
Another common error is overlooking embedded Chromium stacks. Electron apps, custom in-house desktop clients, kiosk software, and certain updater components may also ship their own browser engine copies. Those environments need separate vendor verification because a “Chrome patched” event does not automatically mean every Chromium consumer is safe.
That creates a competitive paradox. On one hand, Chromium-based browsers benefit from a massive security investment base, rapid hardening, and shared fixes. On the other hand, that same shared stack means vendors cannot differentiate themselves by ignoring upstream risk. If Chrome is exposed, then Edge and other Chromium consumers must show not just equivalent protection but often equivalent communication quality.
Browsers that are not directly part of Google’s release line still inherit the pressure. If they bundle Chromium, they must move quickly to avoid appearing out of step with upstream security. If they use a fork or delay adoption, they carry the extra burden of proving that their build is equivalent in security posture.
It will also be worth watching whether this vulnerability appears in future threat reports or if Google later notes in-the-wild exploitation. Chrome has already shown in March 2026 that it will say when an issue is being exploited, which changes the urgency profile dramatically. Even absent that signal, high-severity remote memory bugs in browser networking code deserve prompt action because the exploitation path is straightforward and the attack surface is enormous (chromereleases.googleblog.com).
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
At the same time, closure tells its own story. Google’s March 2026 stable-channel cadence shows a fast-moving security release train, with Chrome 146 promoted to stable on March 10, 2026 and later desktop updates addressing additional security issues in the same branch. In that context, CVE-2026-4454 is not an isolated event; it is part of a broader hardening cycle around a major browser generation that is still settling into the stable channel (chromereleases.googleblog.com).
 Background
Background
Chromium has spent years evolving into the de facto browser platform for Windows, macOS, Linux, and Android. Chrome, Edge, Brave, Vivaldi, Opera, and numerous embedded web views all inherit large portions of that codebase, which means one upstream security fix can ripple across millions of endpoints. That architecture brings enormous advantages in consistency and update velocity, but it also means that a flaw in a core subsystem like Network can instantly become a supply-chain event.Use-after-free bugs remain one of the browser world’s most persistent memory-safety problems because they arise at the boundary between object lifetime management and attacker-controlled timing. In practical terms, the vulnerability is triggered when code continues to use an object after it has been freed, creating the possibility of memory reuse, state confusion, or controlled corruption. For a browser, that can translate into process instability, denial of service, or, in the worst case, exploitable memory corruption.
Google’s Chrome release notes show a familiar pattern: the company withholds some details until a majority of users are protected, while still flagging the severity and the affected version range. That approach balances transparency with defensive delay, and it has become standard practice for browser vendors because the gap between public disclosure and patch adoption is often when exploitation risk rises the fastest. Chrome’s March 2026 security updates also show that Google is willing to move quickly when high-severity issues surface in the stable branch (chromereleases.googleblog.com).
Microsoft’s inclusion of Chromium CVEs in the Security Update Guide is also part of the modern patching picture. Microsoft has explicitly said that CVE details and CWE information may be mirrored into its update ecosystem to help customers track vulnerabilities across products that embed Chromium code. That means Windows administrators cannot safely treat Chrome and Edge as separate security universes; they are linked by a common engine and, in many cases, by the same remediation logic.
The specific significance of CVE-2026-4454 is that it sits in Network, not in a niche subsystem most people never touch. Network-layer browser code is attractive to attackers because it processes hostile input constantly, often before user awareness or policy enforcement has a chance to help. A malformed page is enough; no plug-in, no extension, and no exotic user action is required.
Why this class of bug keeps returning
Memory corruption in browsers has not disappeared because browsers still juggle speed, compatibility, and sandbox boundaries at a scale most software never faces. That tension creates subtle lifetime bugs, especially in code that parses complex, attacker-shaped inputs. The more edge cases a browser supports, the more opportunities there are for a reference to outlive the object behind it.- Use-after-free flaws often turn on precise timing and object reuse.
- Network-facing code is exposed to untrusted inputs by design.
- Crafted HTML remains a simple delivery vehicle for hostile content.
- Heap corruption is dangerous because it can destabilize or subvert execution.
- Browser sandboxes help, but do not erase, memory-safety risk.
What Google Disclosed
Google’s description of CVE-2026-4454 is concise but serious: a use-after-free in the Network component of Chrome prior to 146.0.7680.153 could allow a remote attacker to potentially exploit heap corruption through a cra*Chromium security severity: High** label signals that the issue is not cosmetic and not merely a crash bug. It sits in the category of flaws that security teams typically prioritize alongside other remote, user-triggered browser memory issues .The version floor matters because it gives defenders a concrete decision point. If an estate is running anything earlier than 146.0.7680.153, the browser should be treated as exposed until the relevant update is deployed and confirmed. In a large Windows environment, that verification step matters almost as much as the patch itself, because patch management failures often happen at the layer between download and actual execution.
Versioning and rollout reality
Chrome’s release cadence is fast enough that organizations often discover they have multiple supported versions in flight at once. That is not a sign of poor governance by itself; it is simply the result of staggered rollouts, managed update policies, and offline endpoints. The challenge is that security teams must now track branch lineage as carefully as they track CVE names.Google’s March 2026 stable-channel notes reinforce that reality. Chrome 146 moved to stable on March 10, 2026, and the release stream continued to absorb fixes over the following days and weeks. That means a “current” Chrome install in the real world can lag behind the latest patched build for a nontrivial amount of time, especially in enterprises with deferred updates or testing rings (chromereleases.googleblog.com).
- Chrome prior to 146.0.7680.153 is the exposed line.
- High severity implies rapid remediation should be normal.
- Remote exploitation raises the urgency above local-only bugs.
- Crafted HTML lowers attacker friction.
- Heap corruption increases the potential blast radius.
Why the Network Component Is So Sensitive
The Network component is a privileged chokepoint in any browser architecture because it sits between attacker-controlled bytes and the rest of the rendering engine. It is expected to parse, validate, buffer, redirect, cache, and hand off content in a way that preserves both correctness and isolation. When that code fails, the consequences can cascade into memory management mistakes elsewhere in the stack.This matters because “network bug” sounds narrower than it really is. In browser engineering terms, network code is often the first place a malicious page can influence parser state, request lifetimes, connection reuse, or response handling. A use-after-free there is especially valuable to attackers because it can occur before higher-level mitigations have had a chance to normalize the data stream.
Attack chain potential
A crafted HTML page is not a dramatic delivery mechanism, but it is a practical one. An adversary can place the malicious content behind a phishing lure, an ad slot, a compromised site, or a redirected chain from an otherwise legitimate page. That simplicity is why browser memory bugs remain such a durable offensive tool.In a successful exploitation chain, the goal is usually to move from a predictable crash or corrupt state into something more controllable. The exact outcome depends on allocator behavior, browser build details, and sandbox barriers, but the initial step is often the same: get the target to process malformed content in a vulnerable code path. That is why defenders cannot safely dismiss a use-after-free as “just a crash.”
What defenders should infer
Security teams should read this CVE as a sign that Google’s fuzzing, sanitizers, and internal validation caught a memory-safety weakness in a live code path before it matured into a publicly visible outbreak. Chrome release notes repeatedly mention the use of AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, and AFL in that development ecosystem, which underscores how much modern browser security depends on automated finding and rapid patching (chromereleases.googleblog.com).- Network code is attack surface, not plumbing.
- Early parsing layers are especially dangerous.
- Memory corruption often begins with a logic bug.
- User interaction is usually minimal in browser exploitation.
- Browser telemetry and fuzzing are security controls in practice.
The Windows and Edge Ans, the relevance extends beyond Google Chrome. Microsoft’s Security Update Guide is already tracking the vulnerability, which is exactly what happens when a Chromium-origin issue is relevant to Microsoft Edge or other Microsoft-managed Chromium consumers. Microsoft has been explicit that it publishes browser-related vulnerability data to help customers map upstream Chromium fixes into downstream Windows products.
That matters because many organizations think in product silos, while attackers think in engine families. If Edge and Chrome share a vulnerable Chromium codebase revision, then the practical remediation logic becomes parallel: update the browser channel, verify the build number, and confirm the fleet has actually absorbed the fix. For enterprise Windows administrators, the issue is less “Which browser did we buy?” and more “Which Chromium line are our users actually running?”Enterprise exposure vs consumer exposure
Enterprise risk is often higher than consumer risk because managed browsers live inside dense identity, SaaS, and productivity workflows. A compromised browser session in an enterprise environment can touch mail, CRM, ticketing, cloud consoles, and internal portals in a matter of minutes. Consumers face the same engine flaw, but enterprises usually face the broader consequence chain.Consumers, by contrast, are more likely to experience the vulnerability as a single device problem: a malicious site, a browser crash, or a momentary compromise attempt. That is serious enough on its own, but it usually lacks the network adjacency and data concentration of corporate environments. The difference is not in the vulnerability itself; it is in what the browser is allowed to reach once it is opened.
Why Microsoft’s tracking matters
Microsoft’s update-guide model is useful because it gives Windows admins a second verification layer. Even when the original disclosure comes from Google, the Microsoft page can help answer a more practical question: has the downstream product line incorporated the fix yet? That distinction is especially important for organizations that standardize on Edge but still maintain Chrome for specific workflows or compatibility reasons.- Edge and Chrome share Chromium risk, even if deployment paths differ.
- Windows fleets often run both browsers, multiplying governance complexity.
- Managed update rings can delay remediation.
- Security guides help confirm downstream ingestion.
- Version verification is as important as patch approval.
Patch Management Implications
The first operational lesson from CVE-2026-4454 is that browser patching must move from “desktop hygiene” to security control. Organizations that treat browser updates as optional convenience fixes are leaving a high-value attack vector open. Because the issue is remote and user-triggerable, waiting until the next routine maintenance window can be a bad bet.Second, patch verification should be specific. It is not enough to know that the browser was updated sometime this month. Administrators should confirm the exact Chrome or Chromium build number and ensure it meets or exceeds 146.0.7680.153. In environments with staggered rollout policies, it is entirely possible for some devices to remain exposed after the patch has been approved centrally.
A practical triage sequence
A disciplined response usually starts with inventory, then version checking, then deployment, then validation. The sequence matters because each step can reveal a different failure point. A browser that is installed but not updated, updated but not restarted, or restarted but pinned by policy can all leave gaps.- Inventory Chrome, Edge, and other Chromium-based browsers.
- Check exact build numbers against the fixed version.
- Push the update through the normal endpoint-management channel.
- Force or confirm browser restarts where required.
- Re-scan the fleet to ensure the vulnerable version is gone.
Common patching pitfalls
The biggest mistake is assuming auto-update equals immediate protection. In reality, many browsers defer installation until restart, and some enterprise configurations slow or gate updates by policy. Offline systems, VDI environments, and application-locked workstations can lag even longer.Another common error is overlooking embedded Chromium stacks. Electron apps, custom in-house desktop clients, kiosk software, and certain updater components may also ship their own browser engine copies. Those environments need separate vendor verification because a “Chrome patched” event does not automatically mean every Chromium consumer is safe.
- Restart requirements can delay effective remediation.
- Managed policies can freeze vulnerable versions in place.
- Embedded Chromium apps need separate review.
- Fleet-wide version audits should be routine.
- Attackers do not care whether the browser is “mostly” updated.
Competitive and Ecosystem Impact
Security disclosures like CVE-2026-4454 shape more than patch queues; they also shape market expectations. Chromium’s scale means that one upstream flaw can pressure every vendor that rides the same engine to respond quickly and communicate clearly. The browser ecosystem has effectively become a shared security commons, with one upstream project bearing a large share of the initial discovery burden.That creates a competitive paradox. On one hand, Chromium-based browsers benefit from a massive security investment base, rapid hardening, and shared fixes. On the other hand, that same shared stack means vendors cannot differentiate themselves by ignoring upstream risk. If Chrome is exposed, then Edge and other Chromium consumers must show not just equivalent protection but often equivalent communication quality.
What rivals have to do
The immediate competitive response is largely procedural: ingest the fix, verify the build, and publish the downstream status. But the reputational effect can be significant because enterprises judge vendors partly by how plainly they explain vulnerability exposure. Clear version guidance builds trust. Ambiguity creates friction.Browsers that are not directly part of Google’s release line still inherit the pressure. If they bundle Chromium, they must move quickly to avoid appearing out of step with upstream security. If they use a fork or delay adoption, they carry the extra burden of proving that their build is equivalent in security posture.
Broader market consequences
This CVE also reinforces the market reality that browser security is now a platform story, not a product story. The engine underneath the app matters as much as the logo on the icon. That is good news for standardization, but it also means enterprises need stronger visibility into the component supply chain.- Chromium dominance turns upstream fixes into ecosystem events.
- Downstream vendors compete on patch speed and clarity.
- Enterprises increasingly evaluate browser engines, not just browser brands.
- Forks and delays increase governance overhead.
- Shared codebases amplify both good fixes and bad bugs.
Strengths and Opportunities
The upside of a disclosure like this is that it gives defenders a concrete target and a clear validation point. Security teams do not have to guess whether protection exists; they can check the build, confirm the patch, and close the ticket. The event also reinforces good patch hygiene across Chrome, Edge, and any other Chromium-derived software in the environment.- A fixed version is clearly identified.
- The vulnerability class is well understood.
- Browser vendors can distribute remediation quickly.
- Windows admins can align Chrome and Edge response plans.
- Security tooling can easily inventory browser versions.
- The disclosure strengthens executive urgency around browser patching.
- It encourages better downstream communication from vendors.
Risks and Concerns
The concern, as always with browser memory bugs, is that the disclosed issue may be only one symptom of a broader parsing or lifetime-management weakness. Use-after-free flaws can be especially unpredictable because exploitability depends on heap behavior, mitigation layers, and the exact browser build in circulation. That uncertainty is precisely why high-severity browser bugs should be handled aggressively.- Heap corruption can be a precursor to code execution.
- Phishing or drive-by delivery lowers attacker effort.
- Delayed patch adoption leaves a wide exposure window.
- Embedded Chromium consumers may be overlooked.
- Enterprise update policies can unintentionally prolong risk.
- Public disclosure may attract rapid exploit development.
- Version confusion between stable, extended, and managed channels can hide vulnerable endpoints.
Looking Ahead
The next thing to watch is whether downstream vendors, especially Microsoft, expose more explicit status information for Chromium consumers on Windows. That matters because enterprises often need more than a CVE name; they need a plain answer about whether their current branch is still vulnerable. If Microsoft and other vendors keep improving the traceability from upstream Chrome fixes to downstream shipping builds, administrators will gain a much better handle on remediation timing.It will also be worth watching whether this vulnerability appears in future threat reports or if Google later notes in-the-wild exploitation. Chrome has already shown in March 2026 that it will say when an issue is being exploited, which changes the urgency profile dramatically. Even absent that signal, high-severity remote memory bugs in browser networking code deserve prompt action because the exploitation path is straightforward and the attack surface is enormous (chromereleases.googleblog.com).
- Confirm whether Chrome is at or above 146.0.7680.153.
- Check Microsoft Edge build status on Windows fleets.
- Audit embedded Chromium applications separately.
- Re-run version compliance checks after restart.
- Monitor for any later exploit-in-the-wild reporting.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center