Google has published CVE-2026-5876, a medium-severity Chromium/Chrome vulnerability that can leak cross-origin information through a crafted HTML page by abusing the browser’s Navigation subsystem. The issue affects Google Chrome versions prior to 147.0.7727.55, and the record was added to the CVE list and NVD on April 8, 2026. Microsoft’s Security Update Guide has also surfaced the advisory, underscoring that this is the kind of browser flaw enterprise defenders need to treat as a priority patch item. The root weakness is tagged CWE-1300, Improper Protection of Physical Side Channels, which is a strong hint that the bug is not a classic memory-corruption crash, but a data-exposure problem rooted in timing, observation, or other side-channel behavior.
Chrome and Chromium security advisories have increasingly featured side-channel and information-leakage issues alongside the more familiar memory-safety bugs such as use-after-free and out-of-bounds writes. That shift matters because browser exploit chains have grown more sophisticated, and attackers often do not need a single dramatic crash when a smaller data leak can unlock the next step in a campaign. In practical terms, a leak that crosses origin boundaries can help an attacker reconstruct sensitive state, fingerprint users, or weaken site isolation defenses before a more direct exploit lands.
The Chrome team’s public release notes show that the March 2026 and early April 2026 cadence already included multiple security fixes and standard release-channel promotions, which is normal for a browser at this scale. Chrome 147 was moving through the beta and stable pipeline in March 2026, and the stable desktop line had already advanced through 146.x before the 147 branch became the relevant hardened build family. That timeline matters because a vulnerability like CVE-2026-5876 is only actionable if administrators know exactly which version closes the gap and which release channel has received the fix.
Microsoft’s treatment of the CVE is also telling. MSRC’s Security Update Guide exists to consolidate security intelligence, including third-party CVEs that affect Microsoft-managed ecosystems or enterprise environments where browsers are a core dependency. Microsoft has previously emphasized that the guide is designed as a central place for CVE tracking, advisory publication, and standardized weakness taxonomy, including CWE data. That makes the presence of CVE-2026-5876 in the Microsoft ecosystem a reminder that browser vulnerabilities are no longer “just Chrome problems”; they are enterprise risk issues that can touch managed Windows fleets, virtual desktops, and browser-based line-of-business apps.
The weakness classification itself is useful. CWE-1300 points to a category of flaws where the software fails to sufficiently protect against side-channel observation. In browser terms, that can involve timing behavior, navigation state, rendering differences, or other observable effects that should not reveal cross-origin information. The security significance is subtle but serious: the attacker may not need direct access to the victim origin if the browser accidentally creates a measurable signal.
The Chrome security severity label is Medium, which should not be misread as “low risk.” Browser vendors often reserve higher labels for conditions more likely to produce direct compromise, but medium-severity leaks can still be highly valuable in a real exploit chain. An attacker who can infer cross-origin state may be able to turn an otherwise blocked avenue into a practical intrusion path. That is the danger of information leakage bugs: they are often the quiet enablers, not the final act.
The change history also references a Chromium issue, 41485206, and a Chrome Releases post announcing the stable desktop update that includes the fix. That gives defenders a useful breadcrumb trail: one source identifies the product floor version, while the other anchors the issue in the browser vendor’s own release notes. When a browser flaw affects a major enterprise software estate, those two signals are often enough to begin mitigation planning even before formal patch validation is complete.
Another practical point is that browser updates may roll out gradually. Chrome stable updates commonly propagate over days or weeks, which means some endpoints will remain exposed even after the vendor has released a fix. In managed environments, administrators often need to accelerate deployment through enterprise channels rather than waiting on consumer auto-update behavior.
This is why browser security teams spend so much time reducing observable differences between trusted and untrusted contexts. If navigation timing, rendering state, or process behavior differs enough, an attacker can build a reliable classifier from the output. The exploit may never touch protected data directly; instead, it watches the browser’s reactions and infers the answer. That’s what makes these bugs deceptively dangerous.
Another reason to take this seriously is that cross-origin leakage can affect a wide range of user activity. Browsers are now used for admin portals, finance systems, healthcare apps, source-code platforms, and internal dashboards. If a side-channel leak reveals whether a user is logged in, what page they are on, or how a navigation path behaves, the attacker may gain a surprisingly rich profile of the victim’s session.
The practical takeaway is simple. Users should let Chrome update automatically, restart the browser after the fix is downloaded, and avoid delaying patch installation. In a browser world, “later” often means “while still exploitable.”
This is also why browser patch speed matters more in enterprises than on consumer machines. A delayed update can create a persistence window across thousands of endpoints, and a browser bug is especially problematic because employees may interact with web content all day long. In effect, the attack surface is constantly in use.
This is also why modern browser security programs increasingly treat privacy and integrity as intertwined. A leak that reveals cross-origin behavior can undermine the assumptions behind site isolation and same-origin enforcement, even if it does not technically “break” those features outright. The bug does not need to shatter the wall if it can show the intruder where the weak seam is.
The third step is monitoring for exploit patterns, though that is harder here than with a classic crash bug. Side channels are often quiet, so defenders may need to lean more on patch hygiene and web reputation controls than on endpoint detection. Prevention beats detection when the bug is designed to leave a faint footprint.
For defenders, the next few weeks should focus on version compliance and operational discipline. For vendors, the lesson is to keep reducing browser observability wherever feasible, because the side-channel surface is unlikely to disappear on its own. The web is too dynamic, too stateful, and too heavily optimized for attackers not to keep probing these edges.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Background
Background
Chrome and Chromium security advisories have increasingly featured side-channel and information-leakage issues alongside the more familiar memory-safety bugs such as use-after-free and out-of-bounds writes. That shift matters because browser exploit chains have grown more sophisticated, and attackers often do not need a single dramatic crash when a smaller data leak can unlock the next step in a campaign. In practical terms, a leak that crosses origin boundaries can help an attacker reconstruct sensitive state, fingerprint users, or weaken site isolation defenses before a more direct exploit lands.The Chrome team’s public release notes show that the March 2026 and early April 2026 cadence already included multiple security fixes and standard release-channel promotions, which is normal for a browser at this scale. Chrome 147 was moving through the beta and stable pipeline in March 2026, and the stable desktop line had already advanced through 146.x before the 147 branch became the relevant hardened build family. That timeline matters because a vulnerability like CVE-2026-5876 is only actionable if administrators know exactly which version closes the gap and which release channel has received the fix.
Microsoft’s treatment of the CVE is also telling. MSRC’s Security Update Guide exists to consolidate security intelligence, including third-party CVEs that affect Microsoft-managed ecosystems or enterprise environments where browsers are a core dependency. Microsoft has previously emphasized that the guide is designed as a central place for CVE tracking, advisory publication, and standardized weakness taxonomy, including CWE data. That makes the presence of CVE-2026-5876 in the Microsoft ecosystem a reminder that browser vulnerabilities are no longer “just Chrome problems”; they are enterprise risk issues that can touch managed Windows fleets, virtual desktops, and browser-based line-of-business apps.
The weakness classification itself is useful. CWE-1300 points to a category of flaws where the software fails to sufficiently protect against side-channel observation. In browser terms, that can involve timing behavior, navigation state, rendering differences, or other observable effects that should not reveal cross-origin information. The security significance is subtle but serious: the attacker may not need direct access to the victim origin if the browser accidentally creates a measurable signal.
What the CVE Says
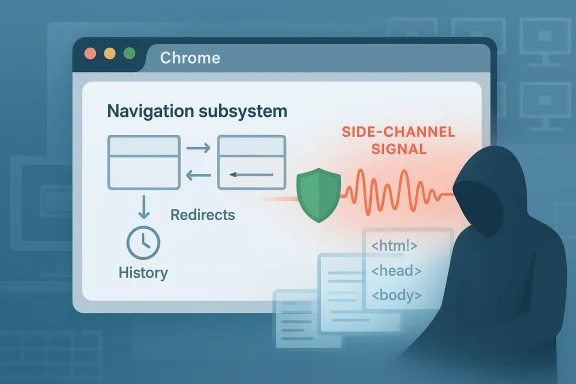
The published description is concise but important: “Side-channel information leakage in Navigation” in Chrome prior to 147.0.7727.55 allowed a remote attacker to leak cross-origin data through a crafted HTML page. That wording tells us several things at once. First, the attack surface is the browser’s navigation logic, not a plugin or external library. Second, the payload is apparently web-delivered, which means a victim only has to visit a hostile page. Third, the outcome is data leakage, not necessarily code execution.Why “cross-origin” is the critical phrase
In the browser security model, origin separation is the foundation that keeps one site from reading another site’s secrets. If a flaw allows cross-origin data to leak, the issue threatens the basic trust boundary that powers everything from webmail to banking to SaaS dashboards. Even a partial leak can be enough to expose tokens, state, or browsing behavior, and that is why side-channel issues are so often treated as architectural rather than merely cosmetic.The Chrome security severity label is Medium, which should not be misread as “low risk.” Browser vendors often reserve higher labels for conditions more likely to produce direct compromise, but medium-severity leaks can still be highly valuable in a real exploit chain. An attacker who can infer cross-origin state may be able to turn an otherwise blocked avenue into a practical intrusion path. That is the danger of information leakage bugs: they are often the quiet enablers, not the final act.
Why Navigation is a sensitive subsystem
Navigation is one of the browser’s most security-sensitive code paths because it sits between user intent, history state, process isolation, prerendering, redirects, and cross-origin transitions. Small differences in how navigation is handled can become visible to malicious scripts as timing signals, state transitions, or access patterns. Chrome has spent years hardening this area, which is exactly why a navigation-side channel matters: it implies there is still measurable behavior left to exploit.- The flaw is web-triggerable through a crafted HTML page.
- The leak crosses origin boundaries, which raises severity beyond a normal page bug.
- The vulnerability is in Navigation, a core browser subsystem.
- The issue is fixed in Chrome 147.0.7727.55 and later.
- The weakness class is CWE-1300, not a memory corruption category.
Timeline and Disclosure
The NVD entry says the CVE was received, published, and last modified on April 8, 2026. That timing is important because it usually means the vendor disclosure and the CVE publication were closely aligned, which reduces the window in which defenders are operating in total uncertainty. The Chromium security ecosystem often publishes release notes and bug references around the same time as the CVE appears in public databases.The change history also references a Chromium issue, 41485206, and a Chrome Releases post announcing the stable desktop update that includes the fix. That gives defenders a useful breadcrumb trail: one source identifies the product floor version, while the other anchors the issue in the browser vendor’s own release notes. When a browser flaw affects a major enterprise software estate, those two signals are often enough to begin mitigation planning even before formal patch validation is complete.
Why disclosure timing matters for enterprise teams
Enterprise vulnerability teams rarely wait for perfect clarity. Instead, they look for a reliable answer to three questions: is the issue real, what version fixes it, and how quickly can we get there? For CVE-2026-5876, the answer is unusually straightforward because the fixed version is explicitly called out and the issue has a clean web-delivery path. That clarity is useful, but it also means the mitigation decision should happen quickly.Another practical point is that browser updates may roll out gradually. Chrome stable updates commonly propagate over days or weeks, which means some endpoints will remain exposed even after the vendor has released a fix. In managed environments, administrators often need to accelerate deployment through enterprise channels rather than waiting on consumer auto-update behavior.
- April 8, 2026: CVE published in NVD.
- April 8, 2026: Chromium issue and reference material surfaced in the record.
- Chrome 147.0.7727.55: fixed build threshold identified in the advisory.
- Enterprise rollout window: likely longer than most security teams prefer.
- Residual risk: endpoints that delay updates remain exploitable.
Technical Analysis
The most notable part of this bug is not that it leaks data, but that it leaks it through a side channel rather than a direct access-control failure. That distinction matters because side channels often bypass the safeguards developers think they have already enforced. If the browser reveals a subtle difference in behavior when navigating across origins, a malicious page may use repeated measurements to infer information that should remain opaque.How a crafted HTML page can become an attack tool
A crafted HTML page is one of the simplest exploitation vehicles on the web. It can embed elements, trigger navigation transitions, measure timing, and observe whether certain paths execute as expected. Even when direct script access is blocked by the same-origin policy, the attacker may still learn from what the browser does around the restriction, which is exactly the type of opportunity side-channel bugs create.This is why browser security teams spend so much time reducing observable differences between trusted and untrusted contexts. If navigation timing, rendering state, or process behavior differs enough, an attacker can build a reliable classifier from the output. The exploit may never touch protected data directly; instead, it watches the browser’s reactions and infers the answer. That’s what makes these bugs deceptively dangerous.
Why “medium” does not mean “minor”
Chrome’s severity labels often reflect the immediate exploitability class and likely impact, not the long-term value of the bug to an advanced adversary. A medium-rated leak can be pivotal if it helps an attacker cross a trust boundary, confirm victim state, or support a follow-on exploit chain. In modern browser offense, leakage frequently acts as the reconnaissance phase for the real compromise.Another reason to take this seriously is that cross-origin leakage can affect a wide range of user activity. Browsers are now used for admin portals, finance systems, healthcare apps, source-code platforms, and internal dashboards. If a side-channel leak reveals whether a user is logged in, what page they are on, or how a navigation path behaves, the attacker may gain a surprisingly rich profile of the victim’s session.
- Side channels exploit observable behavior, not broken authentication.
- Navigation is exposed to timing and state-based inference.
- Cross-origin leakage can aid session profiling and attack chaining.
- Browser hardening reduces risk, but it rarely eliminates all signals.
- Subtle leaks can be more useful than loud crashes for sophisticated attackers.
Impact on Users
For ordinary users, the immediate concern is not that their device will suddenly be taken over by this issue. The published description points to information leakage, so the more likely risk is exposure of cross-origin state or browsing-related information rather than full browser compromise. That said, information leaks can still be highly privacy-sensitive, especially if the attacker can combine them with fingerprinting or social engineering.Consumer risk profile
Consumers are most at risk when they browse to untrusted pages, follow malicious links, or interact with hostile ads and embedded content. A browser flaw like this can be entirely silent from the user’s perspective, which makes it harder to detect than a crash or obvious redirect. The result is a stealthy attack surface: the victim may never realize a page extracted useful state from the session.The practical takeaway is simple. Users should let Chrome update automatically, restart the browser after the fix is downloaded, and avoid delaying patch installation. In a browser world, “later” often means “while still exploitable.”
What users should notice
Most users won’t see a visible symptom. That makes this class of issue particularly frustrating, because “nothing happened” does not mean “nothing was exposed.” A page can still use side effects, timing, or navigation artifacts to infer information without producing any alert, warning, or pop-up.- No obvious crash is expected.
- No user prompt is likely to appear.
- The attack can be silent and passive.
- Risk rises when visiting unknown or hostile sites.
- Updating the browser is the main defense.
Impact on Enterprises
For enterprises, the issue is larger than endpoint patching. Chrome and Chromium are embedded into managed desktops, kiosk systems, VDI environments, and browser-first SaaS workflows, which means a browser leak can affect a wide operational footprint. When the vulnerability concerns cross-origin data, security teams should think in terms of data exposure, not just browser health.Why managed environments care more
Enterprise users often operate with privileged web sessions: identity dashboards, admin consoles, cloud management portals, and internal single-sign-on flows. If a hostile page can leak cross-origin information, even a small signal may reveal whether a privileged app is open, whether a user is authenticated, or which navigation path the browser has taken. Those details can be fused into a broader attack plan.This is also why browser patch speed matters more in enterprises than on consumer machines. A delayed update can create a persistence window across thousands of endpoints, and a browser bug is especially problematic because employees may interact with web content all day long. In effect, the attack surface is constantly in use.
Administrative response priorities
- Confirm the fleet includes Chrome 147.0.7727.55 or later.
- Accelerate deployment for managed endpoints that lag behind auto-update.
- Audit remote work and VDI pools, where browser patch drift is common.
- Re-check web filtering and phishing defenses, since delivery is via HTML.
- Review monitoring assumptions; silent leaks may not trigger endpoint alerts.
- Coordinate with business units that rely on browser-based admin tools.
Comparative Context
CVE-2026-5876 also fits a familiar pattern in Chromium’s recent security history. The browser has dealt with a steady flow of memory-safety bugs, policy enforcement flaws, and other navigation-related problems, showing that the navigation layer remains a persistent source of risk. Earlier March 2026 release notes included another Navigation issue, which underscores that this is a security-sensitive subsystem with repeated hardening pressure.How this compares with more familiar Chrome bugs
A heap buffer overflow can often be framed as a direct exploitability concern. A side-channel leak is more nuanced: it may not deliver code execution, but it can supply the insight an attacker needs to make a separate exploit possible. That difference matters strategically, because high-end adversaries do not always need the loudest bug; they need the most useful one.This is also why modern browser security programs increasingly treat privacy and integrity as intertwined. A leak that reveals cross-origin behavior can undermine the assumptions behind site isolation and same-origin enforcement, even if it does not technically “break” those features outright. The bug does not need to shatter the wall if it can show the intruder where the weak seam is.
Why side-channel bugs are hard to eliminate
Side-channel mitigation is difficult because browsers are extraordinarily complex and highly optimized. Every optimization, timing decision, or cache interaction can introduce a signal that an attacker might eventually measure. In practice, the industry reduces risk by narrowing observability, isolating processes, and standardizing behavior, but it cannot guarantee total silence.- Memory corruption is easier to recognize; side channels are easier to overlook.
- Navigation bugs are especially dangerous because they sit near trust boundaries.
- Repeated fixes suggest the subsystem is under continuous attack pressure.
- Privacy bugs often become exploit-chain enablers.
- The long tail of browser hardening is never fully done.
What Defenders Should Do Now
The immediate defense is straightforward: move affected systems to Chrome 147.0.7727.55 or later. Because the issue is web-delivered, patching the browser is the most effective control, and waiting for user action alone is a poor strategy. Where auto-update is unreliable, administrators should validate versions directly and force remediation.Practical response steps
- Verify Chrome version baselines across the fleet.
- Prioritize internet-facing and high-risk user groups.
- Push browser updates through managed software channels.
- Restart browsers after patching to ensure the new build is active.
- Watch for any delayed-update pockets in VDI or kiosk systems.
- Remind users that suspicious HTML pages can still be dangerous even without downloads or prompts.
The third step is monitoring for exploit patterns, though that is harder here than with a classic crash bug. Side channels are often quiet, so defenders may need to lean more on patch hygiene and web reputation controls than on endpoint detection. Prevention beats detection when the bug is designed to leave a faint footprint.
Strengths and Opportunities
This disclosure is frustrating, but it also demonstrates that the browser security ecosystem is working the way it should: vendors are finding, patching, and publishing issues before they become an even larger problem. The public record gives defenders a clean version floor, a clear weakness classification, and enough context to act without waiting for speculation to settle. That’s the right balance between transparency and operational security.- The fix is tied to a specific Chrome build.
- The issue is publicly documented with a clear attack surface.
- The vulnerability has a well-defined CWE classification.
- Enterprises can use the advisory to drive version compliance.
- Security teams get a chance to patch before wider abuse emerges.
- The disclosure reinforces the value of browser hygiene.
- The advisory helps normalize attention on privacy-impacting browser bugs.
Risks and Concerns
The biggest concern is that users and administrators may underreact because the label says Medium and the issue sounds abstract. Side-channel bugs are easy to dismiss until they are chained into something more serious, and web-delivered leaks are exactly the kind of flaw that advanced actors like to quietly weaponize. Another concern is uneven patch adoption, especially in environments with managed desktops, VDI, or remote users who do not restart browsers promptly.- Patch lag leaves some endpoints exposed after release.
- The bug may be underestimated because it is not a crash.
- Silent exploitation is harder to notice than overt compromise.
- Browser-based workflows increase the blast radius.
- Cross-origin leakage can support attack chaining.
- User behavior, not just software state, shapes exposure.
- Legacy management processes may miss nontraditional browser risks.
Looking Ahead
The broader lesson from CVE-2026-5876 is that browser security has moved well beyond the era of “just patch the crash.” The modern threat model includes privacy, isolation, timing, and information flow, and a flaw in any one of those layers can become the opening an attacker needs. Chrome’s steady stream of navigation and side-channel fixes suggests that the browser team is still actively tightening one of the most sensitive parts of the product.For defenders, the next few weeks should focus on version compliance and operational discipline. For vendors, the lesson is to keep reducing browser observability wherever feasible, because the side-channel surface is unlikely to disappear on its own. The web is too dynamic, too stateful, and too heavily optimized for attackers not to keep probing these edges.
- Verify Chrome 147.0.7727.55+ deployment status.
- Push remaining devices through managed update workflows.
- Watch for related browser-side privacy or navigation advisories.
- Reassess browser hardening assumptions in enterprise estates.
- Treat silent leaks as real security events, not theoretical curiosities.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center