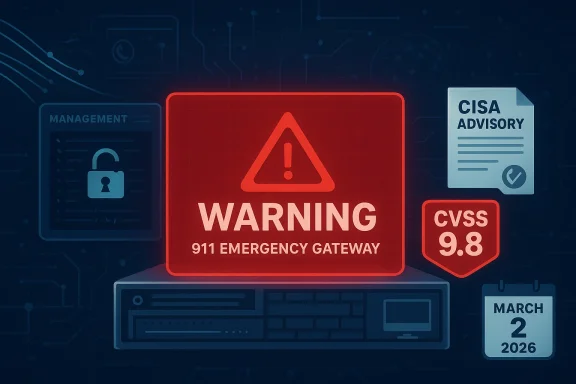
Intrado’s 911 Emergency Gateway is facing a severe security issue that could let an attacker with existing network access reach the management interface without authentication, then read, modify, or delete files. CISA says the flaw affects Emergency Gateway 5.x, 6.x, and 7.x, assigns it CVSS 9.8, and notes that Intrado released a software update on March 2, 2026 to address the issue. The advisory is especially important because this is emergency-services infrastructure, not ordinary enterprise software, and the potential impact includes compromise of a critical communications pathway.
The center of this story is CVE-2026-6074, a path traversal flaw in Intrado 911 Emergency Gateway that CISA describes as allowing an attacker with existing network access to reach the EGW management interface without authentication. Once inside that interface, successful exploitation could let the attacker read, modify, or delete files, which is a serious integrity and availability problem even before you factor in the emergency-services setting. CISA’s advisory places the issue in the Emergency Services sector and notes worldwide deployment, which means the blast radius is potentially broad.
This is not the kind of vulnerability that lives only on paper. Emergency gateway systems sit in the operational path of 911-related services, where reliability, access control, and predictable behavior matter more than almost anywhere else in enterprise technology. A path traversal issue in a web management layer may sound like a familiar application bug, but in a system tied to public safety communications, it becomes a trust-boundary failure. In practical terms, that means an attacker may not need to break the core service to create damage; they may only need to subvert the control plane.
The timing also matters. CISA’s notice says Intrado released a patch on March 2, 2026, more than seven weeks before the advisory’s initial publication on April 23, 2026. That gap suggests defenders have already had an opportunity to remediate, but it also means there may be organizations that missed the vendor update, especially if they treat emergency communications gear as specialized infrastructure owned by a different team. That kind of ownership gap is often where critical vulnerabilities linger longer than they should.
There is a second lesson here as well: management interfaces remain one of the most dangerous parts of a device stack. The advisory does not describe a complicated exploit chain or a subtle edge-case crash. Instead, it points to a direct path traversal condition that can expose the management interface itself, which is exactly the sort of issue that can turn a supposedly internal appliance into a high-value target. That is why CISA’s mitigation language leans heavily on network exposure reduction, segmentation, and access control.
The affected versions are clearly spelled out: Intrado 911 Emergency Gateway 7.x, 6.x, and 5.x. CISA marks the product as known affected and lists the vendor as Intrado, headquartered in the United States, with worldwide deployment. That combination matters because it means the issue is not confined to one region or one niche customer segment. It is a global operational concern with a specific remediation path.
The severity is also amplified by the trust model of emergency communications equipment. Devices like EGW are expected to be stable, available, and reliable; they are not supposed to become writable attack surfaces for opportunistic intruders. If an attacker can delete files or alter configuration through the management interface, they may be able to undermine not just a single device but the integrity of the service environment around it. That is a systemic risk, not a cosmetic one.
The advisory’s wording suggests an attacker could access the management interface itself without authentication. That detail is crucial, because it implies the flaw is not merely about privilege misuse after login. It is about bypassing the normal trust boundary entirely. Once that boundary is crossed, even seemingly limited file operations can have outsized operational consequences.
CISA also notes that the products are deployed worldwide. That matters because the operational and legal response will vary across jurisdictions, but the exposure pattern is likely to be similar: legacy deployments, mixed ownership, and uneven patch coordination. In other words, even when the fix is available, rollout can be slowed by change-control procedures, regional support models, or the fear of interrupting live emergency operations. That is a classic risk-management bottleneck in critical infrastructure.
The broader point is that critical communications platforms often sit in the uncomfortable space between IT and life-safety operations. They are expected to be secure enough to resist attack, yet stable enough that administrators hesitate to touch them. That hesitation is understandable, but it also creates an opening for attackers who thrive on delay. CISA’s advisory is effectively a warning that waiting is the wrong strategy.
CISA’s advisory gives organizations a clear point of contact as well: Intrado E911 Support. That is useful because some critical infrastructure deployments need vendor confirmation about versioning, rollout impact, or configuration specifics before they can move. Still, the existence of support channels should not be used as a reason to delay initial containment steps. If the gateway is exposed beyond its intended trust zone, that exposure should be reduced immediately while patch validation proceeds.
A practical response should be two-track: remediate the software and reduce reachability. In a critical services environment, those steps reinforce each other. If a patch is delayed, segmentation buys time; if segmentation is imperfect, the patch reduces the residual risk. The important point is that no single control should be expected to carry the whole burden.
CISA also reminds organizations to use secure remote-access methods such as VPNs when remote access is needed, but only as part of a broader defense-in-depth model. That caveat is important. VPNs can help, but they do not magically neutralize a vulnerable management interface if the endpoint itself is weak or if the internal network is too flat. Trust the VPN, and you still trust the device behind it is not a safe assumption.
It also creates a useful opportunity for organizations to audit how their emergency communications gear is actually deployed. Many environments discover hidden assumptions only when a security notice forces the issue. If teams use this moment to tighten management access, clean up network boundaries, and refresh ownership of critical appliances, the disclosure can produce benefits beyond the patch itself.
A second concern is that organizations may assume the device is safe because it is not exposed to the public internet. That is a dangerous half-truth. CISA’s advisory explicitly says the attacker needs existing network access, which means any compromised internal host, broad VLAN, vendor path, or weakly segmented support channel could become a launch point. Internal exposure is still exposure.
The third concern is operational delay. Emergency systems are often patched cautiously, and that caution is sensible. But a cautious patch process can become an excuse for indefinite postponement if there is no clear owner or no current inventory. No public exploitation reported does not mean safe; it only means the window to act is still open.
It will also be worth watching whether this advisory prompts broader scrutiny of emergency communications appliances and their management planes. Historically, many organizations focus on the visible service and treat the admin interface as a private implementation detail. Incidents like this show that the implementation detail is often the real target. If defenders use the advisory to narrow access, verify ownership, and harden segmentation, they may reduce more than one future risk.
Source: CISA Intrado 911 Emergency Gateway (EGW) | CISA
 Overview
Overview
The center of this story is CVE-2026-6074, a path traversal flaw in Intrado 911 Emergency Gateway that CISA describes as allowing an attacker with existing network access to reach the EGW management interface without authentication. Once inside that interface, successful exploitation could let the attacker read, modify, or delete files, which is a serious integrity and availability problem even before you factor in the emergency-services setting. CISA’s advisory places the issue in the Emergency Services sector and notes worldwide deployment, which means the blast radius is potentially broad.This is not the kind of vulnerability that lives only on paper. Emergency gateway systems sit in the operational path of 911-related services, where reliability, access control, and predictable behavior matter more than almost anywhere else in enterprise technology. A path traversal issue in a web management layer may sound like a familiar application bug, but in a system tied to public safety communications, it becomes a trust-boundary failure. In practical terms, that means an attacker may not need to break the core service to create damage; they may only need to subvert the control plane.
The timing also matters. CISA’s notice says Intrado released a patch on March 2, 2026, more than seven weeks before the advisory’s initial publication on April 23, 2026. That gap suggests defenders have already had an opportunity to remediate, but it also means there may be organizations that missed the vendor update, especially if they treat emergency communications gear as specialized infrastructure owned by a different team. That kind of ownership gap is often where critical vulnerabilities linger longer than they should.
There is a second lesson here as well: management interfaces remain one of the most dangerous parts of a device stack. The advisory does not describe a complicated exploit chain or a subtle edge-case crash. Instead, it points to a direct path traversal condition that can expose the management interface itself, which is exactly the sort of issue that can turn a supposedly internal appliance into a high-value target. That is why CISA’s mitigation language leans heavily on network exposure reduction, segmentation, and access control.
What CISA Disclosed
CISA’s advisory is unusually blunt about the outcome of exploitation. The agency says successful exploitation could allow an attacker to access the EGW management interface without authentication and then read, modify, or delete files. That is a concise way of saying the problem is not just a crash or a nuisance; it is a gateway to direct control over stored data and configuration state. When the vulnerable surface is a management interface, file access is rarely just file access.The affected versions are clearly spelled out: Intrado 911 Emergency Gateway 7.x, 6.x, and 5.x. CISA marks the product as known affected and lists the vendor as Intrado, headquartered in the United States, with worldwide deployment. That combination matters because it means the issue is not confined to one region or one niche customer segment. It is a global operational concern with a specific remediation path.
Why the severity is so high
A CVSS 9.8 score generally indicates the sort of flaw defenders dread: network reachable, low complexity, no privileges needed, and severe impact. In this case, the vector aligns with a management-plane vulnerability that can be hit over the network, with no user interaction and no prior authorization. That makes the attack path alarmingly efficient if the interface is reachable.The severity is also amplified by the trust model of emergency communications equipment. Devices like EGW are expected to be stable, available, and reliable; they are not supposed to become writable attack surfaces for opportunistic intruders. If an attacker can delete files or alter configuration through the management interface, they may be able to undermine not just a single device but the integrity of the service environment around it. That is a systemic risk, not a cosmetic one.
- Unauthenticated access is the main red flag.
- File read/write/delete capability raises the impact far beyond denial of service.
- Management interface exposure makes the flaw especially dangerous in flat internal networks.
- Emergency-services context raises the stakes for uptime and public safety.
- Vendor patch availability gives defenders a concrete remediation target.
Why Path Traversal Matters Here
Path traversal is one of those bug classes that people sometimes underestimate because it looks old-fashioned. But on a management appliance, it can be devastating. If an attacker can manipulate file paths so the system steps outside intended directories, they may access configuration files, logs, credentials, update artifacts, or other sensitive content that was never meant to be exposed.Management-plane exposure is the real problem
In an ordinary web app, a traversal bug might lead to data leakage. In a device like EGW, the management interface may also control settings, update mechanisms, and service behavior. That means file access can quickly become configuration tampering, and configuration tampering can become service disruption. The line between “read a file” and “change the system” is much thinner in embedded and appliance environments than in consumer software.The advisory’s wording suggests an attacker could access the management interface itself without authentication. That detail is crucial, because it implies the flaw is not merely about privilege misuse after login. It is about bypassing the normal trust boundary entirely. Once that boundary is crossed, even seemingly limited file operations can have outsized operational consequences.
- Traversal bugs often expose configuration and credential material.
- On appliances, file access can affect service state as well as data.
- An attacker who reaches the management interface may inherit admin-like leverage.
- In public-safety infrastructure, even short-lived compromise can be costly.
- Internal-only is not a security model if the interface is reachable from any trusted segment.
The Emergency Services Context
This vulnerability lands in the Emergency Services sector, and that alone changes how defenders should think about it. Emergency communications systems are built around assumptions of continuity, auditability, and rapid response. If the control plane of that environment can be reached without authentication, even by someone who already has network access, the threat is more serious than the headline severity score suggests.Why this sector is different
Emergency-services technology tends to be deployed in environments where downtime is not merely inconvenient. It can affect call handling, routing, or the ability to support public safety operations. That makes availability a mission-critical concern, but it also makes integrity especially important. If a malicious actor can alter files or delete them, the result may be degraded service, corrupted configuration, or a delayed recovery path.CISA also notes that the products are deployed worldwide. That matters because the operational and legal response will vary across jurisdictions, but the exposure pattern is likely to be similar: legacy deployments, mixed ownership, and uneven patch coordination. In other words, even when the fix is available, rollout can be slowed by change-control procedures, regional support models, or the fear of interrupting live emergency operations. That is a classic risk-management bottleneck in critical infrastructure.
The broader point is that critical communications platforms often sit in the uncomfortable space between IT and life-safety operations. They are expected to be secure enough to resist attack, yet stable enough that administrators hesitate to touch them. That hesitation is understandable, but it also creates an opening for attackers who thrive on delay. CISA’s advisory is effectively a warning that waiting is the wrong strategy.
Intrado’s Patch and Customer Response
Intrado’s March 2, 2026 software update is the key remediation item CISA highlights. That means there is no mystery about the primary fix path: affected customers should move to the vendor’s addressed build as quickly as operationally possible. The fact that the vendor has already released an update is helpful, but only if organizations actually inventory their deployments and apply it.Why patching may still lag
In practice, emergency-services environments often operate with stricter maintenance windows than ordinary enterprise systems. Teams may need validation, coordination with operations staff, or approval from multiple stakeholders before modifying the gateway. That makes a seemingly straightforward patch into a procedural event, and procedural events are where vulnerabilities sometimes survive the longest. The patch exists is not the same thing as the patch is everywhere it needs to be.CISA’s advisory gives organizations a clear point of contact as well: Intrado E911 Support. That is useful because some critical infrastructure deployments need vendor confirmation about versioning, rollout impact, or configuration specifics before they can move. Still, the existence of support channels should not be used as a reason to delay initial containment steps. If the gateway is exposed beyond its intended trust zone, that exposure should be reduced immediately while patch validation proceeds.
A practical response should be two-track: remediate the software and reduce reachability. In a critical services environment, those steps reinforce each other. If a patch is delayed, segmentation buys time; if segmentation is imperfect, the patch reduces the residual risk. The important point is that no single control should be expected to carry the whole burden.
Defensive Priorities for Operators
CISA’s recommended practices are familiar to anyone who follows ICS advisories, but they are especially relevant here because the vulnerable component is a management interface. The first priority is to minimize network exposure so the device is not reachable from unnecessary networks, especially not from the internet. The second is to ensure control-system networks and remote devices sit behind firewalls and are isolated from business networks wherever practical.What operators should focus on first
The advisory’s guidance makes the response order fairly clear. Start by identifying every affected EGW instance, then verify version status, then confirm whether the management interface is reachable from broad internal segments, vendor support paths, or any public endpoint. After that, move into patching and post-patch validation. That sequence reduces the chance of both blind remediation and accidental service disruption.CISA also reminds organizations to use secure remote-access methods such as VPNs when remote access is needed, but only as part of a broader defense-in-depth model. That caveat is important. VPNs can help, but they do not magically neutralize a vulnerable management interface if the endpoint itself is weak or if the internal network is too flat. Trust the VPN, and you still trust the device behind it is not a safe assumption.
- Inventory all Intrado EGW deployments.
- Confirm whether any system is running 5.x, 6.x, or 7.x.
- Restrict management access to the smallest possible network set.
- Apply the March 2, 2026 vendor update.
- Review logs for unusual access or file activity.
- Re-check segmentation after remediation to prevent regression.
Strengths and Opportunities
The upside of this disclosure is that it gives defenders a narrow and practical remediation target. The affected product families are named clearly, the vulnerable condition is identified, and the vendor has already shipped an update. That makes this a situation where disciplined asset management can materially reduce risk instead of merely documenting it.It also creates a useful opportunity for organizations to audit how their emergency communications gear is actually deployed. Many environments discover hidden assumptions only when a security notice forces the issue. If teams use this moment to tighten management access, clean up network boundaries, and refresh ownership of critical appliances, the disclosure can produce benefits beyond the patch itself.
- Clear affected-version range.
- Vendor remediation already available.
- Strong CISA mitigation guidance.
- Chance to validate emergency-services asset inventory.
- Opportunity to revisit remote-access policy.
- Good forcing function for management-plane segmentation.
- Helpful trigger for post-installation security review.
Risks and Concerns
The biggest risk is underestimation. A path traversal issue can sound routine to teams that are used to web application flaws, but in a critical emergency gateway it can translate to direct control over files and potentially the management interface itself. If the vulnerability is treated as merely administrative noise, it may stay reachable longer than it should.A second concern is that organizations may assume the device is safe because it is not exposed to the public internet. That is a dangerous half-truth. CISA’s advisory explicitly says the attacker needs existing network access, which means any compromised internal host, broad VLAN, vendor path, or weakly segmented support channel could become a launch point. Internal exposure is still exposure.
The third concern is operational delay. Emergency systems are often patched cautiously, and that caution is sensible. But a cautious patch process can become an excuse for indefinite postponement if there is no clear owner or no current inventory. No public exploitation reported does not mean safe; it only means the window to act is still open.
- Internal network access may be easier to obtain than defenders assume.
- Patch ownership may be split between teams, slowing response.
- Legacy deployments may be harder to inventory than current ones.
- Management interfaces are often over-permitted by design.
- File access in a gateway can become service disruption quickly.
- Delay increases the odds that an opportunistic attacker gets there first.
- Critical-infrastructure environments cannot rely on hope as a control.
Looking Ahead
The next thing to watch is how quickly organizations close the gap between patch availability and actual deployment. For some, that will be straightforward. For others, especially those with change-control gates or distributed emergency-services environments, the real work will be proving where the gateway is, how it is reachable, and whether the patch can be applied without disrupting live operations. That is where the risk-management conversation becomes operational.It will also be worth watching whether this advisory prompts broader scrutiny of emergency communications appliances and their management planes. Historically, many organizations focus on the visible service and treat the admin interface as a private implementation detail. Incidents like this show that the implementation detail is often the real target. If defenders use the advisory to narrow access, verify ownership, and harden segmentation, they may reduce more than one future risk.
- Confirm every deployed Intrado EGW instance and version.
- Verify the March 2, 2026 patch has been applied.
- Restrict management access to tightly controlled networks.
- Review logs for unauthorized file or interface access.
- Validate that no weak internal paths still reach the gateway.
- Reassess vendor-support and remote-maintenance pathways.
- Update incident response plans for emergency-services appliances.
Source: CISA Intrado 911 Emergency Gateway (EGW) | CISA