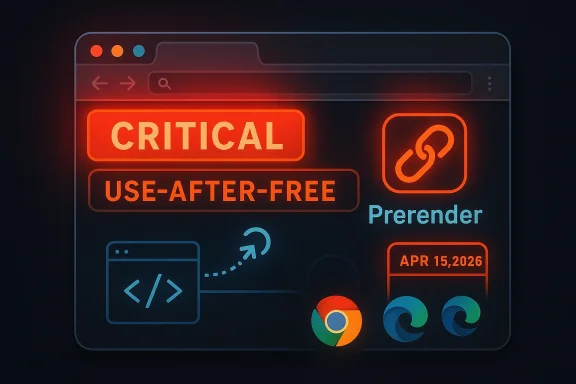
The latest Chromium security cycle has put CVE-2026-6299 under a harsh spotlight because it combines three things defenders hate to see together: a use-after-free bug, a critical Chromium severity rating, and a fix that lands in a browser engine used by far more than just Google Chrome. According to the public advisory captured in Microsoft’s Security Update Guide, the flaw affects Google Chrome prior to 147.0.7727.101 and can let a remote attacker execute arbitrary code through a crafted HTML page. Google’s Stable Channel bulletin confirms that the fix shipped on April 15, 2026, alongside a broader security update for desktop Chrome. gleblog.com]
Chromium vulnerabilities tend to matter quickly, but this one matters in a familiar and uncomfortable way: it lives in the browser’s rendering pipeline, where attacker-controlled content arrives first and hardening assumptions are thinnest. Prerender is designed to make browsing faster by preparing pages before the user actively opens them, but any performance feature that speculatively loads content also enlarges the attack surface. A flaw in that layer is especially significant because it can be reached by a crafted Hns the attack vector is not exotic or hardware-specific; it is the web itself.
The timing also matters. Google’s April 15 Stable Channel update for desktop Chrome 147.0.7727.101/102 came during a release cycle that already included multiple serious memory-safety repairs, and Google noted that the patch set covered 31 security fixes overall. That context suggests CVE-2026-6299 is not an isolated paper cut but part of a broader pattern in which browser internals continue to absorb a steady stream of memory corruption bugs.
Microsoft’s Security Update Guide now lists the issue as well, reflecting how Chromium-origin bugs propagate into downstream products and patch workflows. Microsoft has repeatedly documented that it surfaces Chromium CVEs in the guide so customers can understand when Edbased deployments inherit the fix. That mechanism is important because many enterprise environments do not track Chrome alone; they track the entire Chromium family.
The practical takeaway is straightforward: even without evidence in the public record that this flaw was exploited in the wild, the combination of remote ial, a critical* severity label, and a browser component that operates close to page loading logic means administrators should treat it as an urgent patch item. In browser security, ordinary-looking* HTML is often enough to weaponize an otherwise mundane memory bug.
The Prerender angle is important because prerendering is inherently speculative. The browser prepares a page before the user commits to it, which means there are more state transitions, more cancellation paths, and more opportunities for lifetime mistakes. In that sense, prerendering is a performance optimization with a built-in security tax, and attackers routinely look for those margins. Fast paths often become fragile paths.
The browser vendor’s description also matters because it narrows the attack scenario. A crafted HTML page means the adversary does not need local access, a malicious extension, or a special device configuration. Instead, the victim only needs to render attacker-controlled content, which is exactly the sort of condition that makes browser bugs scale into real-world risk.
The disclosure pattern is also consistent with Chrome’s broader security behavior: Google often limits bug detail until most users are protected, and the release notes make clear that access to some details can be restricted while updates propagate. That delay is a standard defensive practice, but it leaves defenders balancing visibility against the risk of premature exploitation.
Microsoft’s entry arrived at roughly the same time, reflecting the normal downstream mirror effect for Chromium CVEs. Microsoft has explained that it includes Chromium-assigned CVEs in the Security Update Guide because Edge and related products consume Chromium code and therefore need clear remediation visibility. That mapping is crucial for enterprises that rely on Microsoft’s update ecosystem rather than watching Chrome release notes directly.
The result is a reminder that the security disclosure clock now runs o: the upstream Chromium fix and the downstream product listing. When those line up, defenders get a cleaner operational picture. When they do not, patch prioritization becomes messy very quickly.
That does not mean prerender is itself unsafe by design. It does mean that any defect in the feature is likely to sit in a hot zone for exploitation. The browser may already be parsing attacker-controlled content, allocating DOM structures, and coordinating navigation state when the bug fires, which is why a single lifetime mistake can have outsized consequences. Complexity is the attacker’s friend.
From a defender’s point of view, the lesson is not to disable every speed feature blindly. It is to recognize that modern browser optimization is inseparable from security engineering. If a feature touches rendering, navigation, or speculative loading, it inherits a higher risk burden than simpler code paths.
This is also why browser vendors keep investing in memory safety hardening, sandboxing, and process isolation. Even if a bug is triggered by normal web content, the goal is to keep the blast radius limited. CVE-2026-6299 is a reminder that those layers matter because they are often the only thing standing between a malformed HTML page and full compromise.
A successful exploit would likely start with a website, ad, or embedded content that convinces the browser to load malicious HTML. Because the bug is in a browser component rather than a plug-in, the attacker’s delivery chain can be very ordinary. That is precisely why browser CVEs are so often turned into mass-exploitation opportunities.
The severity also deserves attention because Chrome’s own Critical label is not just a rhetorical flourish. In practice, browser teams reserve that classification for defects that can plausibly lead to serious compromise, especially when remote code execution is on the table. The issue here is not just a crash; it is the possibility that malicious web content could be turned into code execution.
For users who rely on Chrome’s auto-update mechanism, the most important thing is to verify that the browser has actually restarted and applied the new build. Desktop browsers often download a fix quietly but do not activate it until relaunch. That small operational gap is enough to keep a machine exposed longer than the user expects.
The lesson is simple but worth repeating: installed is not the same as protected. If Chrome is still running an older session, the vulnerable code may still be active.
That becomes even more important in regulated or segmented environments where browser deployment is controlled by software distribution rings, group policy, or application compatibility checks. A patch may be published upstream on April 15, but an enterprise image might not receive the corrected browser until days later. Those delays can be operationally necessary, but they also leave a narrow attack window.
Other Chromium-based browsers inherit the same basic concern, even when their vendors do not mirror the CVE in a public portal exactly the way Microsoft does. The key point is architectural: if the browser is built on Chromium, upstream memory-safety fixes are not optional garnish; they are core security maintenance.
That is why defenders should not treat this as “just a Chrome issue.” It is a Chromium ecosystem issue, and that ecosystem includes enterprise browsers, embedded web shells, kiosk deployments, and application wrappers that are easy to forget until a security bulletin forces them back into view.
It is also worth separating managed and unmanaged devices. Managed Windows fleets may pick up Edge updates through centralized channels, while user-managed laptops and contractors might lag for days. The weakest link in browser patching is rarely the CVE itself; it is distribution inconsistency.
Because the bug is in a browser component, compensating controls are limited. Network filtering can reduce exposure to known malicious sites, but it cannot fully protect against a legitimate site compromise, malicious ad insertion, or a user following a crafted link. That is why patching remains the primary control.
The broader significance is that Chrome’s security story is not just about one bug class but about a structural engineering problem. The vendor can harden sandboxing, improve fuzzing, and reduce attack surface, but the sheer size of the codebase means some vulnerabilities will keep escaping into stable builds. That is the uncomfortable reality.
At the same time, the steady cadence of fixes also shows that Chromium’s disclosure model is functioning. Bugs are being found, assigned, patched, and published quickly enough that defenders can respond. That does not eliminate risk, but it does shorten the lifetime of many vulnerabilities.
For the market, this creates a strange but familiar dynamic: Chrome remains trusted because it is aggressively patched, yet its dominance means every flaw attracts huge attention. Rivals such as Edge inherit the same engine-level issues, so the browser market competes on distribution speed and operational discipline as much as on features.
There is also a platform implication. Web applications, identity providers, and SaaS tools depend on browser stability, so every serious browser CVE can ripple into enterprise workflows. One vulnerable browser build may not only expose endpoints; it can also force emergency rescheduling of user training, support windows, and maintenance freezes.
The competitive irony is that Chromium’s dominance makes its bugs everyone’s problem while also making its fixes everyone’s benefit. That shared codebase model has reduced fragmentation, but it has also concentrated risk in a single engine architecture. That concentration is efficient and fragile at the same time.
For consumers, the market implication is simpler. Users increasingly expect browsers to auto-heal security problems with minimal interruption. That expectation is valid, but it can also mask the reality that the underlying risk remains high until the update actually lands and the browser restarts.
More broadly, this CVE is another test of how well browser vendors can keep speculative-loading features safe without sacrificing performance. If Prerender continues to attract memory-safety defects, that will strengthen the case for deeper architectural hardening. If the patch lands cleanly and quickly, it becomes another data point in favor of Chromium’s existing response model.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Chromium vulnerabilities tend to matter quickly, but this one matters in a familiar and uncomfortable way: it lives in the browser’s rendering pipeline, where attacker-controlled content arrives first and hardening assumptions are thinnest. Prerender is designed to make browsing faster by preparing pages before the user actively opens them, but any performance feature that speculatively loads content also enlarges the attack surface. A flaw in that layer is especially significant because it can be reached by a crafted Hns the attack vector is not exotic or hardware-specific; it is the web itself.The timing also matters. Google’s April 15 Stable Channel update for desktop Chrome 147.0.7727.101/102 came during a release cycle that already included multiple serious memory-safety repairs, and Google noted that the patch set covered 31 security fixes overall. That context suggests CVE-2026-6299 is not an isolated paper cut but part of a broader pattern in which browser internals continue to absorb a steady stream of memory corruption bugs.
Microsoft’s Security Update Guide now lists the issue as well, reflecting how Chromium-origin bugs propagate into downstream products and patch workflows. Microsoft has repeatedly documented that it surfaces Chromium CVEs in the guide so customers can understand when Edbased deployments inherit the fix. That mechanism is important because many enterprise environments do not track Chrome alone; they track the entire Chromium family.
The practical takeaway is straightforward: even without evidence in the public record that this flaw was exploited in the wild, the combination of remote ial, a critical* severity label, and a browser component that operates close to page loading logic means administrators should treat it as an urgent patch item. In browser security, ordinary-looking* HTML is often enough to weaponize an otherwise mundane memory bug.
What CVE-2026-6299 Actually Is
At a technical level, CVE-2026-6299 is a use-after-free in Prerender, which is one of the classic memory-safety bug classes that keep appearing in Chromium and other large C++ codebasestext says the issue allowed a remote attacker to execute arbitrary code via a crafted HTML page, and the Chromium security severity is listed as Critical. Microsoft’s Security Update Guide mirrors that public description for downstream visibility.Why use-after-free bugs remain dangerous
A use-after-free occurs when software continues to reference memory after it has been released and possibly reallocated for something else. In a browser, that can become more thae content, scripting timing, and renderer-state transitions can be coordinated in ways that let an attacker shape memory reuse. That is why the label use-after-free still triggers immediate attention in browser security circles.The Prerender angle is important because prerendering is inherently speculative. The browser prepares a page before the user commits to it, which means there are more state transitions, more cancellation paths, and more opportunities for lifetime mistakes. In that sense, prerendering is a performance optimization with a built-in security tax, and attackers routinely look for those margins. Fast paths often become fragile paths.
The browser vendor’s description also matters because it narrows the attack scenario. A crafted HTML page means the adversary does not need local access, a malicious extension, or a special device configuration. Instead, the victim only needs to render attacker-controlled content, which is exactly the sort of condition that makes browser bugs scale into real-world risk.
Timeline and Disclosure
Google published the relevant fix in the April 15, 2026 Stable Channel update for desktop Chrome, where the company noted the move to 147.0.7727.101/102 on Windows and Mac and 147.0.7727.101 on Linux. The security section of that bulletin explicitly lists CVE-2026-6299 as a critical use-after-free in Prerender.The release cadence tells a bigger story
The Chrome team’s bulletin also said the fix would roll out over the coming days and weeks. That rolling-release model is normal, but it also means the practical exposure window can differ wildly between users who auto-update quickly and organizations that deliberately stage updates. In other words, patch availability does not instantly equal patch coverage.The disclosure pattern is also consistent with Chrome’s broader security behavior: Google often limits bug detail until most users are protected, and the release notes make clear that access to some details can be restricted while updates propagate. That delay is a standard defensive practice, but it leaves defenders balancing visibility against the risk of premature exploitation.
Microsoft’s entry arrived at roughly the same time, reflecting the normal downstream mirror effect for Chromium CVEs. Microsoft has explained that it includes Chromium-assigned CVEs in the Security Update Guide because Edge and related products consume Chromium code and therefore need clear remediation visibility. That mapping is crucial for enterprises that rely on Microsoft’s update ecosystem rather than watching Chrome release notes directly.
The result is a reminder that the security disclosure clock now runs o: the upstream Chromium fix and the downstream product listing. When those line up, defenders get a cleaner operational picture. When they do not, patch prioritization becomes messy very quickly.
Why Prerender Matters
Prerender is not the flashiest browser subsystem, but it is strategically important because it sits at the intersection of speed and prediction. It helps pages appear more responsive, which is a user-facing win, yet it also means the browser is doing work on pages before the user has actually chosen to visit them. That behavior expands the amount of code executing in a speculative state, and speculative states tend to be where memory lifetime bugs hide.Performance features and attack surface
Security engineers have long understood that features meant to smooth performance often create more complicated object lifetimes. More asynchronous transitions, more cache invalidation, and more event-driven cancellation paths all increase the odds that one object gets freed while another part of the program still thinks it owns it. Prerender is exactly the kind of mechanism where that failure mode can emerge.That does not mean prerender is itself unsafe by design. It does mean that any defect in the feature is likely to sit in a hot zone for exploitation. The browser may already be parsing attacker-controlled content, allocating DOM structures, and coordinating navigation state when the bug fires, which is why a single lifetime mistake can have outsized consequences. Complexity is the attacker’s friend.
From a defender’s point of view, the lesson is not to disable every speed feature blindly. It is to recognize that modern browser optimization is inseparable from security engineering. If a feature touches rendering, navigation, or speculative loading, it inherits a higher risk burden than simpler code paths.
This is also why browser vendors keep investing in memory safety hardening, sandboxing, and process isolation. Even if a bug is triggered by normal web content, the goal is to keep the blast radius limited. CVE-2026-6299 is a reminder that those layers matter because they are often the only thing standing between a malformed HTML page and full compromise.
Impact on Chrome Users
For consumer users, the headline is simple: update Chrome immediately. Google’s bulletin identifies all vulnerable builds before 147.0.7727.101, and the public description says the issue can lead to arbitrary code execution. That is the sort of language that should trigger prompt patching even in the absence of confirmed active exploitation. ([chromereleases.googleblog.com](Stable Channel Update for Desktop## What the risk looks like in practiceA successful exploit would likely start with a website, ad, or embedded content that convinces the browser to load malicious HTML. Because the bug is in a browser component rather than a plug-in, the attacker’s delivery chain can be very ordinary. That is precisely why browser CVEs are so often turned into mass-exploitation opportunities.
The severity also deserves attention because Chrome’s own Critical label is not just a rhetorical flourish. In practice, browser teams reserve that classification for defects that can plausibly lead to serious compromise, especially when remote code execution is on the table. The issue here is not just a crash; it is the possibility that malicious web content could be turned into code execution.
For users who rely on Chrome’s auto-update mechanism, the most important thing is to verify that the browser has actually restarted and applied the new build. Desktop browsers often download a fix quietly but do not activate it until relaunch. That small operational gap is enough to keep a machine exposed longer than the user expects.
The lesson is simple but worth repeating: installed is not the same as protected. If Chrome is still running an older session, the vulnerable code may still be active.
Impact on Microsoft Edge and Other Chromium Browsers
For enterprise environments, CVE-2026-6299 is larger than a single Chrome patch because Microsoft Edge and many other browsers share the Chromium engine. Microsoft’s Security Update Guide exists precisely to help customers map upstream Chromium disclosures to downstream products and patch timelines. That is why the same vulnerability can appear in Microsoft’s guide even though Google assigned and fixed it upstream.Why downstream visibility matters
In many organizations, Edge is the default browser and Chrome is secondary, or Chrome is blocked while Chromium-based web apps still depend on Edge WebView components. In those environments, an upstream Chromium CVE is not an abstract engineering note; it is a live endpoint-management problem. Security teams need to know whether the downstream build has already absorbed the fix.That becomes even more important in regulated or segmented environments where browser deployment is controlled by software distribution rings, group policy, or application compatibility checks. A patch may be published upstream on April 15, but an enterprise image might not receive the corrected browser until days later. Those delays can be operationally necessary, but they also leave a narrow attack window.
Other Chromium-based browsers inherit the same basic concern, even when their vendors do not mirror the CVE in a public portal exactly the way Microsoft does. The key point is architectural: if the browser is built on Chromium, upstream memory-safety fixes are not optional garnish; they are core security maintenance.
That is why defenders should not treat this as “just a Chrome issue.” It is a Chromium ecosystem issue, and that ecosystem includes enterprise browsers, embedded web shells, kiosk deployments, and application wrappers that are easy to forget until a security bulletin forces them back into view.
Enterprise Patch Strategy
CVE-2026-6299 fits squarely into the class of vulnerabilities that justify rapid enterprise action because the exploit path is web-delivered and the consequence can be code execution. In practice, organizations should treat it as a top-tier browser remediation item, especially if their users routinely receive untrusted HTML content through the browser, email previews, web apps, or shared collaboration tools.A sensible response plan
- Confirm browser build numbers across Chrome, Edge, and any Chromium-based specialized browser.
- Accelerate rollout of Chrome 147.0.7727.101/102 or the corresponding downstream fix.
- Restart browsers and endpoints where needed so the patched code is actually loaded.
- Review exposure paths such as webmail, external collaboration portals, and internet-facing content workflows.
- Monitor for anomalies that could suggest attempted exploitation, especially in high-risk user groups.
It is also worth separating managed and unmanaged devices. Managed Windows fleets may pick up Edge updates through centralized channels, while user-managed laptops and contractors might lag for days. The weakest link in browser patching is rarely the CVE itself; it is distribution inconsistency.
Because the bug is in a browser component, compensating controls are limited. Network filtering can reduce exposure to known malicious sites, but it cannot fully protect against a legitimate site compromise, malicious ad insertion, or a user following a crafted link. That is why patching remains the primary control.
How This Fits Chromium’s Broader Security Pattern
CVE-2026-6299 is part of a much larger story: Chromium’s recurring struggle with memory safety in a codebase that must balance speed, compatibility, and security. Google has spent years hardening the browser, but the recurring appearance of use-after-free, heap overflow, and out-of-bounds bugs shows how difficult it is to make legacy C++ rendering systems robust at scale.Memory safety remains the central challenge
Browser engines process hostile input continuously, often at enormous speed, and they do so while juggling complex object graphs. That makes them fertile ground for lifetime errors. If a feature allocates an object, queues a callback, and then tears down the state before the callback fires, the stage is set for use-after-free.The broader significance is that Chrome’s security story is not just about one bug class but about a structural engineering problem. The vendor can harden sandboxing, improve fuzzing, and reduce attack surface, but the sheer size of the codebase means some vulnerabilities will keep escaping into stable builds. That is the uncomfortable reality.
At the same time, the steady cadence of fixes also shows that Chromium’s disclosure model is functioning. Bugs are being found, assigned, patched, and published quickly enough that defenders can respond. That does not eliminate risk, but it does shorten the lifetime of many vulnerabilities.
For the market, this creates a strange but familiar dynamic: Chrome remains trusted because it is aggressively patched, yet its dominance means every flaw attracts huge attention. Rivals such as Edge inherit the same engine-level issues, so the browser market competes on distribution speed and operational discipline as much as on features.
Competitive and Market Implications
Security incidents like CVE-2026-6299 also affect how browsers are perceived in the marketplace. A vendor’s ability to respond quickly to engine bugs can become a differentiator, especially for enterprise customers who care less about branding and more about update reliability, policy control, and rollback behavior. Google’s fast release, combined with Microsoft’s downstream tracking, demonstrates how much the modern browser market depends on coordinated maintenance.Why this matters beyond one CVE
Browsers increasingly compete on trust economics. A browser that patches quickly earns confidence, but a browser that inherits upstream fixes slowly can become operationally expensive for IT departments. That cost is not just security risk; it is help-desk load, change-management friction, and business continuity disruption.There is also a platform implication. Web applications, identity providers, and SaaS tools depend on browser stability, so every serious browser CVE can ripple into enterprise workflows. One vulnerable browser build may not only expose endpoints; it can also force emergency rescheduling of user training, support windows, and maintenance freezes.
The competitive irony is that Chromium’s dominance makes its bugs everyone’s problem while also making its fixes everyone’s benefit. That shared codebase model has reduced fragmentation, but it has also concentrated risk in a single engine architecture. That concentration is efficient and fragile at the same time.
For consumers, the market implication is simpler. Users increasingly expect browsers to auto-heal security problems with minimal interruption. That expectation is valid, but it can also mask the reality that the underlying risk remains high until the update actually lands and the browser restarts.
Strengths and Opportunities
The positive side of this story is that the ecosystem responded quickly and transparently enough for defenders to act. Chrome shipped a fix, Microsoft surfaced the same vulnerability in its guide, and the public record gives administrators enough detail to make patching decisions without waiting for guesswork. That is how browser security is supposed to work, even when the bug itself is ugly.- Fast upstream remediation reduces the window for mass exploitation.
- Microsoft’s downstream tracking helps Edge and enterprise customers align patch plans.
- Clear version boundaries make it easier to identify vulnerable systems.
- The Critical rating helps organizations prioritize accurately.
- Public disclosure of the component improves threat modeling for Prerender-related paths.
- Browser auto-update systems can shrink exposure when they are actually allowed to complete.
- Security telemetry can be tuned around a well-defined browser version change.
Risks and Concerns
The downside is that browser bugs of this kind are still fundamentally high-impact events. A single crafted page can be enough to trigger a memory corruption chain, and the affected component sits close to core browsing behavior, which makes triage urgent but not always easy. In practice, the biggest risk is that organizations underestimate how many places Chromium lives in their environment.- Delayed restarts can leave patched browsers effectively vulnerable.
- Downstream lag in Edge or embedded Chromium builds can prolong exposure.
- User interaction requirements may lull teams into thinking the issue is low urgency.
- Silent web delivery means phishing or ad compromise can be enough.
- Complex enterprise fleets make version auditing difficult.
- Speculative features like prerender can enlarge attack surface in subtle ways.
- Memory-safety bugs remain hard to eliminate completely in large browser engines.
What to Watch Next
The immediate question is not whether Chrome has a fix — it does — but how quickly the ecosystem converges on the patched version. In the next few days, defenders should be watching adoption curves, downstream vendor advisories, and any signs that researchers or threat actors are chaining this bug with other browser weaknesses. Google’s release notes and Microsoft’s Security Update Guide are the key operational reference points for that monitoring.More broadly, this CVE is another test of how well browser vendors can keep speculative-loading features safe without sacrificing performance. If Prerender continues to attract memory-safety defects, that will strengthen the case for deeper architectural hardening. If the patch lands cleanly and quickly, it becomes another data point in favor of Chromium’s existing response model.
Things to monitor closely
- Chrome and Edge version rollouts across managed fleets
- Restart compliance after browser updates
- Any exploit chatter tied to crafted HTML delivery
- Additional Chromium CVEs appearing in the same release wave
- Enterprise WebView deployments that may lag behind desktop browsers
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center