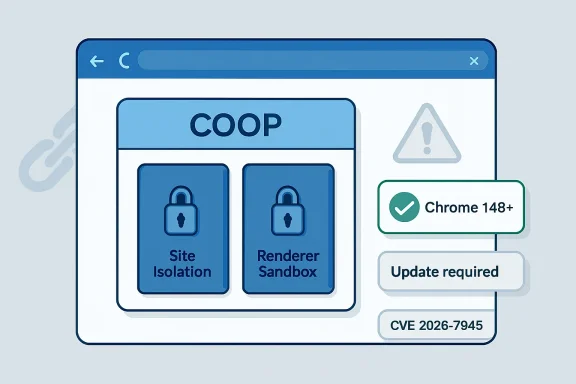
Google and Microsoft disclosed CVE-2026-7945 on May 6, 2026, describing a medium-severity Chromium flaw in Cross-Origin-Opener-Policy handling that affected Chrome before 148.0.7778.96 and could let an attacker who already compromised the renderer bypass site isolation with crafted HTML. That phrasing is doing a lot of work. This is not the kind of bug that lets any random web page immediately own a machine, but it is exactly the kind of boundary failure that matters once a browser exploit chain is already in motion. For Windows users and administrators, the lesson is blunt: browser security is now less about a single catastrophic hole and more about whether the layers behind the first failure still hold.
CVE-2026-7945 arrived as part of Chrome 148, a large stable-channel update that landed in early May with a long list of security fixes across Blink, V8, ANGLE, WebRTC, Site Isolation, Navigation, and other browser subsystems. The affected Chrome threshold is clear: versions before 148.0.7778.96 are in scope, while Chrome 148.0.7778.96 on Linux and 148.0.7778.96/97 on Windows and macOS carry the fix. Microsoft’s publication of the same CVE through MSRC matters because Edge inherits much of this Chromium security surface, even when the user never installs Google Chrome.
The vulnerability is classified by Chromium as medium severity, and CISA’s ADP scoring pegs it at a low CVSS 3.1 base score of 3.1. That number will tempt some patch queues to treat this as administrative background noise. It should not. CVSS is useful for triage, but it can understate the importance of a flaw whose real value appears only when paired with another bug.
The key phrase is “had compromised the renderer process.” In Chromium’s architecture, the renderer is the sandboxed process that handles web content. If an attacker already has code execution there, they have crossed a major threshold, but they still should not be able to freely pierce the browser’s site boundaries. CVE-2026-7945 is about what happens after that first wall cracks.
This is where modern browser hardening gets awkward to explain to non-specialists. The exploit is not the whole story; the containment model is the story. A flaw that weakens containment can be decisive even if it does not start the fire.
For ordinary users, Site Isolation is invisible. There is no dashboard, no celebratory notification, and no obvious switch that says, “Your banking tab is not sharing dangerous memory space with an untrusted page.” But the feature has become one of the reasons a modern browser can survive hostile web content at all. It assumes the web is messy, JavaScript engines are complicated, and rendering engines will continue to produce bugs despite heroic fuzzing and code review.
COOP, short for Cross-Origin-Opener-Policy, is part of this broader isolation vocabulary. It allows a site to control whether a newly opened top-level document shares a browsing context group with another page, affecting relationships such as
The CVE description says the weakness involved insufficient validation of untrusted input in COOP. In plain English, Chromium was not adequately validating something a page could feed into the machinery that helps decide how documents are grouped and isolated. If the renderer was already compromised, crafted HTML could reportedly exploit that weakness to bypass Site Isolation.
That is not “visit a page and instantly lose everything.” It is more like: if an attacker has already found a way into one compartment, this bug may help them open a door that was supposed to remain locked.
A renderer compromise is often the first major step in a browser exploit chain. From there, the attacker wants to escape the sandbox, read cross-origin data, pivot into more privileged browser components, or defeat isolation assumptions that protect other tabs and sites. CVE-2026-7945 sits in that middle layer of the attack path, where exploit reliability and blast radius are decided.
This is why “medium” can be misleading. Medium does not mean harmless. It often means the flaw requires another condition to become dangerous, or that exploitation is complex, or that the immediate impact is narrower than full takeover. In a browser, those caveats are exactly where exploit developers live.
The CISA vector is also instructive. Network attack vector, no privileges required, user interaction required, high attack complexity, low confidentiality impact, no integrity or availability impact. That describes a bug that is hard to use alone and limited in direct effect. It does not describe whether the bug is useful when chained after a renderer exploit.
That distinction is not academic. Browser exploit chains are rarely single-bug affairs anymore. They are assembled from memory corruption, type confusion, policy bypass, race conditions, sandbox escapes, and logic bugs. A boundary bypass can be the quiet part that turns a proof of concept into an operational tool.
COOP gives sites a way to say, in effect, “Do not let this top-level document remain in the same browsing context group as a cross-origin document.” Paired with other headers such as Cross-Origin-Embedder-Policy, it also participates in the browser’s cross-origin isolation model, which gates access to powerful features and reduces exposure to certain classes of attacks. The feature is not merely a developer-facing header; it is part of the browser’s internal traffic control system.
That is why validation matters. If a crafted page can feed unexpected input into COOP handling, the browser may make a wrong decision about whether two documents should share a group or process relationship. In a benign case, that produces weird behavior. In a hostile case, especially after renderer compromise, it can undermine the separation Site Isolation was supposed to enforce.
The tricky part is that COOP must preserve a great deal of web compatibility. Break too much, and sign-in popups, dashboards, embedded workflows, and enterprise web apps start behaving strangely. Permit too much, and the browser keeps dangerous relationships alive. The security boundary is not a wall so much as a continually updated rules engine.
CVE-2026-7945 is therefore a reminder that browser isolation depends on countless small policy decisions. The scary bugs are not always in the flashy JIT compiler or GPU memory path. Sometimes they live in the logic that decides who is allowed to share a room.
Edge complicates the patching picture because many organizations manage it separately from Chrome. Some rely on Microsoft Edge Update, others pin versions through policy, and still others let Windows servicing assumptions blur into browser servicing reality. That is a dangerous blur. Chromium-based browsers update on a cadence that does not wait for Patch Tuesday.
CVE-2026-7945 also illustrates why organizations need asset visibility beyond “which operating system build is installed?” A fully patched Windows machine with an out-of-date browser remains exposed to web-delivered attack chains. The browser is the application most likely to parse hostile input all day, every day, from everywhere.
For administrators, the practical question is not whether this one CVE deserves emergency-war-room treatment. It is whether browsers across the fleet are actually at or beyond the fixed Chromium build. If your tooling cannot answer that quickly, the vulnerability has already found a governance gap.
The same logic applies to non-Google Chromium derivatives. Vendors must ingest upstream fixes, rebuild, test, and ship them. Some do this quickly. Some do not. The farther a browser or embedded runtime drifts from upstream, the more security teams must treat it as a separate exposure rather than an implementation detail.
That scale is both reassuring and unsettling. It is reassuring because Chromium’s security pipeline is clearly finding and fixing large numbers of defects before they become public disasters. It is unsettling because the browser attack surface is enormous, deeply privileged in practice, and fed by untrusted content continuously.
The modern browser is no longer just a document viewer. It is a virtual machine, media stack, graphics pipeline, password manager, identity broker, extension host, remote desktop client, application runtime, and operating-system integration layer. Every new capability creates new policy edges. Every policy edge needs validation.
This is why patch fatigue is so dangerous. Users see yet another browser update and assume it is cosmetic. Administrators see yet another Chromium advisory and assume it can wait for the next routine deployment ring. Attackers see a release note with 127 fixed bugs and start looking for laggards.
The industry has trained people to think of browser updates as background hygiene. That is mostly good. But “automatic” is not the same as “complete,” and “rolling out over the coming days and weeks” is not the same as “deployed on every endpoint that matters.”
In managed environments, deferral policies exist for good reasons. Browser updates can break line-of-business applications, alter authentication behavior, affect extensions, or disrupt kiosk and VDI setups. Sensible IT teams test before broad deployment. The problem is that attackers also test, and they do it against old builds.
For CVE-2026-7945 specifically, the public details are limited because Chromium commonly restricts bug information until most users have updated. That is responsible disclosure practice, not secrecy for its own sake. But it also means defenders are operating with the advisory text, the affected version, the component name, and their own understanding of browser architecture.
That should push teams toward version-based remediation rather than exploit-signature comfort. If the installed version is before the fixed build, it is vulnerable. If the fixed build is not deployed, the theoretical debate over exploitability is less useful than the operational question of why.
This is especially true for security products that rely on self-reported version checks. Vulnerability scanners can tell you Chrome is older than 148.0.7778.96, but they generally are not proving exploitability. That limitation is fine as long as teams understand it. In browser patching, version truth is often the actionable truth.
But risk is contextual. A financial institution with hardened browser policies, rapid update rings, and strong isolation monitoring may treat this as routine. A school district with unmanaged Chrome installations, delayed ChromeOS updates, and students clicking through arbitrary web content may view the same Chromium patch bundle differently. A defense contractor with strict segmentation may care deeply about any path that weakens site boundaries after initial compromise.
The web threat model also punishes complacency. User interaction is not much of a barrier when the interaction is “visit a page.” High complexity does not always remain high once researchers and adversaries study adjacent patches. And renderer compromise, while a major precondition, is not fantasy in a world where browser engines receive critical and high-severity memory-safety fixes every release cycle.
The better framing is this: CVE-2026-7945 is not the first domino. It is a possible later domino. Whether that makes it urgent depends on how likely your environment is to see the earlier domino fall, and how much damage a Site Isolation bypass could enable afterward.
This is why security programs that patch only by CVSS score miss the shape of modern exploitation. Attack chains do not care whether each link is independently dramatic. They care whether the links connect.
Administrators should also look at policy decisions that delay browser updates. A short testing ring is prudent. A long deferral that leaves high-use browsers sitting behind upstream security releases is a liability. The browser deserves a faster lane than many desktop applications because its exposure profile is different.
Extension governance matters too. A renderer compromise is not necessarily caused by an extension, but extensions expand the browser’s trust model and can complicate response. Organizations should know which extensions are installed, which are force-installed, which have broad host permissions, and which are no longer maintained.
Finally, detection teams should not expect CVE-2026-7945 to announce itself neatly. A Site Isolation bypass after renderer compromise may not produce an obvious endpoint alert labeled with this CVE. The defensive signal is more likely to come from browser exploit behavior, suspicious renderer crashes, abnormal child-process activity, credential theft attempts, or web-origin anomalies.
That is unsatisfying, but it is the reality of browser defense. The cleanest control is still to remove the vulnerable build before anyone has to detect the exploit chain.
The next few years of browser defense will not be won by treating every medium Chromium CVE as an emergency, nor by waving them away as noise. It will be won by organizations that understand which “medium” bugs protect the seams between compartments, patch them quickly enough that exploit chains lose useful links, and build update systems that move at the speed of the web rather than the comfort of the monthly calendar.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 The Browser Patch That Looks Small Until You Read the Preconditions
The Browser Patch That Looks Small Until You Read the Preconditions
CVE-2026-7945 arrived as part of Chrome 148, a large stable-channel update that landed in early May with a long list of security fixes across Blink, V8, ANGLE, WebRTC, Site Isolation, Navigation, and other browser subsystems. The affected Chrome threshold is clear: versions before 148.0.7778.96 are in scope, while Chrome 148.0.7778.96 on Linux and 148.0.7778.96/97 on Windows and macOS carry the fix. Microsoft’s publication of the same CVE through MSRC matters because Edge inherits much of this Chromium security surface, even when the user never installs Google Chrome.The vulnerability is classified by Chromium as medium severity, and CISA’s ADP scoring pegs it at a low CVSS 3.1 base score of 3.1. That number will tempt some patch queues to treat this as administrative background noise. It should not. CVSS is useful for triage, but it can understate the importance of a flaw whose real value appears only when paired with another bug.
The key phrase is “had compromised the renderer process.” In Chromium’s architecture, the renderer is the sandboxed process that handles web content. If an attacker already has code execution there, they have crossed a major threshold, but they still should not be able to freely pierce the browser’s site boundaries. CVE-2026-7945 is about what happens after that first wall cracks.
This is where modern browser hardening gets awkward to explain to non-specialists. The exploit is not the whole story; the containment model is the story. A flaw that weakens containment can be decisive even if it does not start the fire.
Site Isolation Is the Seatbelt, Not the Airbag
Chromium’s Site Isolation project was one of the most consequential browser security changes of the last decade. Its core premise is simple enough: sites should not casually share renderer processes, because a compromise in one web origin should not automatically expose another. That separation became especially important after Spectre-style side-channel attacks reminded the industry that process boundaries were not merely tidy engineering abstractions.For ordinary users, Site Isolation is invisible. There is no dashboard, no celebratory notification, and no obvious switch that says, “Your banking tab is not sharing dangerous memory space with an untrusted page.” But the feature has become one of the reasons a modern browser can survive hostile web content at all. It assumes the web is messy, JavaScript engines are complicated, and rendering engines will continue to produce bugs despite heroic fuzzing and code review.
COOP, short for Cross-Origin-Opener-Policy, is part of this broader isolation vocabulary. It allows a site to control whether a newly opened top-level document shares a browsing context group with another page, affecting relationships such as
window.opener and cross-origin popup interactions. That may sound esoteric, but the browser’s handling of opener relationships is one of the places where web compatibility, developer convenience, and security boundaries collide.The CVE description says the weakness involved insufficient validation of untrusted input in COOP. In plain English, Chromium was not adequately validating something a page could feed into the machinery that helps decide how documents are grouped and isolated. If the renderer was already compromised, crafted HTML could reportedly exploit that weakness to bypass Site Isolation.
That is not “visit a page and instantly lose everything.” It is more like: if an attacker has already found a way into one compartment, this bug may help them open a door that was supposed to remain locked.
The Medium Label Hides a Chain-Building Primitive
Security teams tend to reserve urgency for critical remote code execution, privilege escalation, and known exploited zero-days. That instinct is understandable. Patch bandwidth is finite, change windows are political, and browser updates can still break brittle enterprise workflows. But browsers are attacked as systems, not as individual CVE entries.A renderer compromise is often the first major step in a browser exploit chain. From there, the attacker wants to escape the sandbox, read cross-origin data, pivot into more privileged browser components, or defeat isolation assumptions that protect other tabs and sites. CVE-2026-7945 sits in that middle layer of the attack path, where exploit reliability and blast radius are decided.
This is why “medium” can be misleading. Medium does not mean harmless. It often means the flaw requires another condition to become dangerous, or that exploitation is complex, or that the immediate impact is narrower than full takeover. In a browser, those caveats are exactly where exploit developers live.
The CISA vector is also instructive. Network attack vector, no privileges required, user interaction required, high attack complexity, low confidentiality impact, no integrity or availability impact. That describes a bug that is hard to use alone and limited in direct effect. It does not describe whether the bug is useful when chained after a renderer exploit.
That distinction is not academic. Browser exploit chains are rarely single-bug affairs anymore. They are assembled from memory corruption, type confusion, policy bypass, race conditions, sandbox escapes, and logic bugs. A boundary bypass can be the quiet part that turns a proof of concept into an operational tool.
COOP Is Where Web Compatibility Meets Browser Containment
Cross-Origin-Opener-Policy exists because the web’s windowing model was designed in a more innocent era. Pages can open other pages, hold references to them, navigate them in limited ways, and communicate through controlled channels. Those capabilities are useful for sign-in flows, payment windows, productivity apps, and federated services, but they also create opportunities for cross-site leaks and confusing opener relationships.COOP gives sites a way to say, in effect, “Do not let this top-level document remain in the same browsing context group as a cross-origin document.” Paired with other headers such as Cross-Origin-Embedder-Policy, it also participates in the browser’s cross-origin isolation model, which gates access to powerful features and reduces exposure to certain classes of attacks. The feature is not merely a developer-facing header; it is part of the browser’s internal traffic control system.
That is why validation matters. If a crafted page can feed unexpected input into COOP handling, the browser may make a wrong decision about whether two documents should share a group or process relationship. In a benign case, that produces weird behavior. In a hostile case, especially after renderer compromise, it can undermine the separation Site Isolation was supposed to enforce.
The tricky part is that COOP must preserve a great deal of web compatibility. Break too much, and sign-in popups, dashboards, embedded workflows, and enterprise web apps start behaving strangely. Permit too much, and the browser keeps dangerous relationships alive. The security boundary is not a wall so much as a continually updated rules engine.
CVE-2026-7945 is therefore a reminder that browser isolation depends on countless small policy decisions. The scary bugs are not always in the flashy JIT compiler or GPU memory path. Sometimes they live in the logic that decides who is allowed to share a room.
Microsoft’s Role Is Not a Footnote for Windows Shops
The user-facing brand may be Chrome, but the Windows estate is full of Chromium. Microsoft Edge, Electron applications, embedded web views, and enterprise tooling all live in the gravitational field of Chromium’s security work. When MSRC tracks a Chromium CVE, Windows administrators should read it as part of the Windows security story, not as a Google-only advisory.Edge complicates the patching picture because many organizations manage it separately from Chrome. Some rely on Microsoft Edge Update, others pin versions through policy, and still others let Windows servicing assumptions blur into browser servicing reality. That is a dangerous blur. Chromium-based browsers update on a cadence that does not wait for Patch Tuesday.
CVE-2026-7945 also illustrates why organizations need asset visibility beyond “which operating system build is installed?” A fully patched Windows machine with an out-of-date browser remains exposed to web-delivered attack chains. The browser is the application most likely to parse hostile input all day, every day, from everywhere.
For administrators, the practical question is not whether this one CVE deserves emergency-war-room treatment. It is whether browsers across the fleet are actually at or beyond the fixed Chromium build. If your tooling cannot answer that quickly, the vulnerability has already found a governance gap.
The same logic applies to non-Google Chromium derivatives. Vendors must ingest upstream fixes, rebuild, test, and ship them. Some do this quickly. Some do not. The farther a browser or embedded runtime drifts from upstream, the more security teams must treat it as a separate exposure rather than an implementation detail.
The 127-Fix Chrome 148 Drop Shows the Scale of the Problem
Chrome 148 was not a tidy one-CVE maintenance release. Google’s release notes list 127 security fixes, including critical issues such as an integer overflow in Blink and use-after-free flaws in Mobile and Chromoting, plus numerous high- and medium-severity bugs across rendering, graphics, media, networking, storage, UI, and developer tooling. CVE-2026-7945 is one tile in a mosaic.That scale is both reassuring and unsettling. It is reassuring because Chromium’s security pipeline is clearly finding and fixing large numbers of defects before they become public disasters. It is unsettling because the browser attack surface is enormous, deeply privileged in practice, and fed by untrusted content continuously.
The modern browser is no longer just a document viewer. It is a virtual machine, media stack, graphics pipeline, password manager, identity broker, extension host, remote desktop client, application runtime, and operating-system integration layer. Every new capability creates new policy edges. Every policy edge needs validation.
This is why patch fatigue is so dangerous. Users see yet another browser update and assume it is cosmetic. Administrators see yet another Chromium advisory and assume it can wait for the next routine deployment ring. Attackers see a release note with 127 fixed bugs and start looking for laggards.
The industry has trained people to think of browser updates as background hygiene. That is mostly good. But “automatic” is not the same as “complete,” and “rolling out over the coming days and weeks” is not the same as “deployed on every endpoint that matters.”
The Real Risk Is the Delay Between Upstream and Reality
Google’s stable-channel update began rolling out in the first week of May 2026. That phrase, “rolling out,” is doing almost as much work as “renderer compromise.” It means not everyone receives the update at the same moment, and it means enterprise controls can stretch the exposure window further.In managed environments, deferral policies exist for good reasons. Browser updates can break line-of-business applications, alter authentication behavior, affect extensions, or disrupt kiosk and VDI setups. Sensible IT teams test before broad deployment. The problem is that attackers also test, and they do it against old builds.
For CVE-2026-7945 specifically, the public details are limited because Chromium commonly restricts bug information until most users have updated. That is responsible disclosure practice, not secrecy for its own sake. But it also means defenders are operating with the advisory text, the affected version, the component name, and their own understanding of browser architecture.
That should push teams toward version-based remediation rather than exploit-signature comfort. If the installed version is before the fixed build, it is vulnerable. If the fixed build is not deployed, the theoretical debate over exploitability is less useful than the operational question of why.
This is especially true for security products that rely on self-reported version checks. Vulnerability scanners can tell you Chrome is older than 148.0.7778.96, but they generally are not proving exploitability. That limitation is fine as long as teams understand it. In browser patching, version truth is often the actionable truth.
Low CVSS Does Not Mean Low Priority for Every Environment
The CISA ADP score of 3.1 reflects real constraints. Exploitation requires user interaction, high attack complexity, and an already compromised renderer. The immediate confidentiality impact is rated low, with no direct integrity or availability impact in the vector. On paper, that belongs below the screaming-red tier.But risk is contextual. A financial institution with hardened browser policies, rapid update rings, and strong isolation monitoring may treat this as routine. A school district with unmanaged Chrome installations, delayed ChromeOS updates, and students clicking through arbitrary web content may view the same Chromium patch bundle differently. A defense contractor with strict segmentation may care deeply about any path that weakens site boundaries after initial compromise.
The web threat model also punishes complacency. User interaction is not much of a barrier when the interaction is “visit a page.” High complexity does not always remain high once researchers and adversaries study adjacent patches. And renderer compromise, while a major precondition, is not fantasy in a world where browser engines receive critical and high-severity memory-safety fixes every release cycle.
The better framing is this: CVE-2026-7945 is not the first domino. It is a possible later domino. Whether that makes it urgent depends on how likely your environment is to see the earlier domino fall, and how much damage a Site Isolation bypass could enable afterward.
This is why security programs that patch only by CVSS score miss the shape of modern exploitation. Attack chains do not care whether each link is independently dramatic. They care whether the links connect.
The Enterprise Answer Is Boring, Which Is Why It Works
The right response is not panic. It is disciplined browser lifecycle management. Chrome should be at 148.0.7778.96 or later, with Windows and macOS systems receiving 148.0.7778.96/97 or later depending on channel, and Linux systems receiving 148.0.7778.96 or later. Edge and other Chromium-based browsers should be checked against their vendor-fixed releases rather than assumed safe because Windows Update has run.Administrators should also look at policy decisions that delay browser updates. A short testing ring is prudent. A long deferral that leaves high-use browsers sitting behind upstream security releases is a liability. The browser deserves a faster lane than many desktop applications because its exposure profile is different.
Extension governance matters too. A renderer compromise is not necessarily caused by an extension, but extensions expand the browser’s trust model and can complicate response. Organizations should know which extensions are installed, which are force-installed, which have broad host permissions, and which are no longer maintained.
Finally, detection teams should not expect CVE-2026-7945 to announce itself neatly. A Site Isolation bypass after renderer compromise may not produce an obvious endpoint alert labeled with this CVE. The defensive signal is more likely to come from browser exploit behavior, suspicious renderer crashes, abnormal child-process activity, credential theft attempts, or web-origin anomalies.
That is unsatisfying, but it is the reality of browser defense. The cleanest control is still to remove the vulnerable build before anyone has to detect the exploit chain.
Chrome 148 Turns a Medium Bug Into a Fleet Management Test
CVE-2026-7945 is not the loudest flaw in the Chrome 148 security release, but it is one of the better tests of whether an organization understands browser risk as architecture rather than arithmetic. The concrete action is straightforward, but the reasoning behind it matters.- Chrome installations older than 148.0.7778.96 should be treated as vulnerable and moved to a fixed build without waiting for NVD to publish its own independent score.
- Microsoft Edge and other Chromium-based browsers should be verified separately because Chromium fixes do not protect users until each downstream vendor ships and installs the patched code.
- The vulnerability requires a prior renderer compromise, which lowers standalone severity but increases its relevance as a chain component in real browser attacks.
- Site Isolation and COOP are containment mechanisms, so a bypass can matter even when it does not provide direct code execution by itself.
- Browser update deferrals should be short, explicit, and monitored, because “automatic update” is not the same as verified fleet compliance.
- Security teams should prioritize version visibility over speculative exploit debate, since the fixed-version boundary is the most reliable operational fact currently available.
The next few years of browser defense will not be won by treating every medium Chromium CVE as an emergency, nor by waving them away as noise. It will be won by organizations that understand which “medium” bugs protect the seams between compartments, patch them quickly enough that exploit chains lose useful links, and build update systems that move at the speed of the web rather than the comfort of the monthly calendar.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center