Google and Microsoft listed CVE-2026-7946 on May 6, 2026, as a medium-severity Chromium flaw in Chrome before 148.0.7778.96 that could let a remote attacker who had already compromised the renderer bypass site isolation through a crafted HTML page. The phrase “medium severity” is doing a lot of work here, because the vulnerability sits exactly where browser security has spent the last decade trying to build hard internal walls. This is not the kind of bug that usually screams across consumer headlines, but it is the kind that reminds enterprise defenders why browser patching has become operating-system patching in all but name. The uncomfortable lesson is that modern browser security is no longer just about stopping the first exploit; it is about surviving the second step after the first one succeeds.
CVE-2026-7946 is not described as a classic “visit a page and get owned” vulnerability. The public wording says the attacker first needs to have compromised the renderer process, and only then can the crafted HTML page be used to bypass site isolation. That prerequisite is why the score lands in the medium range rather than among the red-alert bugs that promise immediate code execution from a single click.
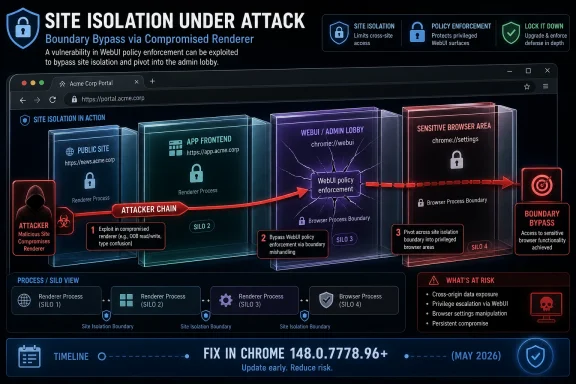
But that distinction can be misleading for anyone who has watched browser exploitation evolve. A modern browser attack chain is often assembled from pieces: one bug to gain code execution in a renderer, another to escape the sandbox, another to cross a boundary the browser had promised would contain the damage. CVE-2026-7946 appears to live in that middle territory, where the attacker is not starting from zero but is trying to turn a beachhead into something more useful.
That is why “medium” should not be read as “low priority.” In isolation, the bug leaks or weakens a containment boundary. In a chain, it can become the part that makes an otherwise limited renderer compromise more valuable.
The CISA-ADP vector published with the entry tells the same story in security shorthand: network attack vector, low complexity, no privileges, user interaction required, and low confidentiality impact. That is not catastrophic on paper. It is also not nothing, especially when the impacted software is Chrome across Windows, macOS, Linux, and ChromeOS before the fixed build.
Spectre made that philosophy urgent. If speculative execution could be abused to infer data across boundaries, then the browser needed stronger boundaries between mutually distrusting web content. Site isolation was Chrome’s answer: put sites in separate process silos, reduce the blast radius, and make the renderer compromise less catastrophic.
That model has held up well enough to become part of the security baseline users rarely think about. The browser does not just render pages; it enforces a geopolitical map of the web, with origins, frames, processes, privileges, and policies standing in for borders.
CVE-2026-7946 is troubling because it points at the bureaucracy of that map. The bug is not described as a raw memory corruption failure. It is “insufficient policy enforcement in WebUI,” which suggests a failure in how the browser applied internal rules to privileged browser-facing interfaces.
That makes WebUI security particularly delicate. If ordinary web content is the public street, WebUI is closer to the administrative lobby. It may still have familiar doors and windows, but the access rules are supposed to be stricter.
The CVE wording says insufficient policy enforcement in WebUI allowed a renderer-compromising attacker to bypass site isolation. That is a compact description, but the implication is clear enough: some internal rule that should have preserved the separation between sites, processes, or privileged contexts did not hold under crafted conditions.
Google has not publicly exposed the full issue details, which is normal for Chromium bugs while users are still being updated. The restraint is defensible; publishing exploit mechanics too early helps attackers more than defenders. But the lack of detail also means administrators must treat the vendor’s boundary description seriously rather than waiting for a proof-of-concept to make the risk feel real.
That is the entire point of the sandboxed renderer model. Web content is too complex, too dynamic, and too exposed to be trusted absolutely. JavaScript engines, layout engines, media parsers, graphics stacks, font handling, extension surfaces, and IPC plumbing all create opportunities for mistakes. The renderer is where much of that attack surface lives.
So when a vulnerability assumes a compromised renderer, it is not assuming science fiction. It is assuming one of the most common starting points in serious browser exploitation.
The security question is what happens next. Can the attacker only disturb the malicious tab? Can they read cross-site data? Can they access internal browser pages? Can they pivot into a more privileged process? CVE-2026-7946 is significant because it appears to weaken a boundary that exists precisely to answer those questions with “no.”
When a Chrome CVE appears in Microsoft’s ecosystem, it reinforces a shift that has already happened: the browser engine is shared infrastructure. Chromium bugs ripple into Edge, embedded web views, managed desktop baselines, and third-party applications that depend on Chromium components.
The CVE itself names Google Chrome on Linux, Mac, Windows, and ChromeOS prior to 148.0.7778.96. Microsoft’s publication of the entry is part of a broader vendor coordination reality, not evidence that this is a Windows-only defect.
That distinction is important for IT teams. The right operational question is not “Is this a Microsoft bug or a Google bug?” It is “Where do Chromium-based browsers and components exist in my environment, and are they actually patched?”
The scale of the security work around Chrome 148 is notable. Contemporary reporting put the number of security fixes above 100, with multiple critical vulnerabilities in the same release family. CVE-2026-7946 is therefore not the headline-grabbing member of the class. It is one of the quieter bugs in a very large patch train.
That quietness is exactly why it deserves attention. Critical memory-safety bugs trigger alarms because they are easy to explain. A medium-severity WebUI policy failure that matters after renderer compromise is harder to put on a dashboard, but it may still be relevant to attackers building chains.
Patch management tends to chase severity labels. Attackers chase composability.
CPEs are supposed to make vulnerabilities machine-readable. In theory, a scanner can map installed products to known vulnerable versions and generate a clean answer. In practice, browser packaging, enterprise channels, embedded runtimes, managed update deferrals, and vendor-specific rebuilds complicate that picture.
Chrome is particularly slippery because the version number is the real anchor. A Windows host, a Mac laptop, a Linux workstation, and a ChromeOS device may all be affected by the same Chromium defect, but the update path, cadence, and administrative control plane differ substantially.
So, yes, organizations may find that asset tools miss something. They may also find that the CPE exists but the installed product data is stale, incomplete, or hidden behind user-level installation paths. The cure is not to obsess over the CPE entry; it is to verify browser versions directly.
That does not make ChromeOS uniquely vulnerable. In some ways, ChromeOS is one of the cleanest examples of a browser-first security model. But it does mean organizations need to watch channel availability and update enforcement, not just CVE publication.
For admins, the practical question is whether devices have actually crossed the fixed-version line. A vulnerability description that says “prior to 148.0.7778.96” is not satisfied by a policy that merely allows updates. It is satisfied by devices reporting the patched build.
This is where consumer security advice and enterprise reality diverge. “Update Chrome” is sufficient advice for an individual user. A fleet owner needs proof, timing, exception handling, rollback awareness, and a plan for devices that sit offline until the worst possible moment.
That is why a site isolation bypass matters even when its stated confidentiality impact is low. The browser is where identities are active, sessions are warm, and cross-origin assumptions are doing constant security work. Weakening those assumptions can be more dangerous than the CVSS line suggests.
Attackers do not need every browser bug to be a full sandbox escape. Sometimes they need a way to read something they should not, influence a privileged flow, or combine a limited renderer foothold with a policy confusion. Modern exploitation often looks less like smashing one giant wall and more like finding three doors that each close imperfectly.
Defenders, meanwhile, have inherited a paradox. The browser is one of the most aggressively updated pieces of software on the endpoint, but it is also one of the most exposed. Fast updates are necessary because the target never stops moving.
That score does not capture every meaningful operational detail. It does not know whether a vulnerable browser is used by a domain admin. It does not know whether the environment runs a high-risk SaaS estate through Chrome. It does not know whether the organization has recently seen browser-based phishing, malvertising, or drive-by attempts.
Nor does it capture exploit chain economics. A medium bug in a heavily deployed browser can be worth more than a high bug in a rarely exposed component. Attackers care about reach, reliability, stealth, and how well a bug combines with others.
The right reading is not “ignore medium.” It is “treat medium browser boundary bugs as patch-now unless there is a better reason not to.”
Chrome 148’s rollout language — coming over days or weeks — is normal, but normal does not mean ideal for every environment. Staged rollout reduces the blast radius of bad updates. It also creates a window in which fixed bugs are known, unfixed clients remain common, and attackers can begin studying the patch delta.
That window is one reason enterprises increasingly need more control, not less. Auto-update is excellent for unmanaged users. Managed environments need rings, telemetry, forced relaunch deadlines, and exception processes that do not become permanent loopholes.
The worst compromise is the one many organizations drift into: updates are automatic in theory, delayed in practice, and unverified in reporting. CVE-2026-7946 is exactly the kind of bug that can disappear from attention before the fleet is actually clean.
That does not mean every Chromium consumer is automatically affected in the same way. A WebUI policy enforcement bug may depend on Chrome-specific internal surfaces, feature flags, or UI plumbing. But the prudent response is to check vendor advisories for every Chromium-derived browser in the estate.
Microsoft Edge deserves special attention in Windows environments because it is both a browser and a platform dependency. Organizations that standardized on Edge may still see the CVE through Chrome-oriented feeds, then need to map the underlying Chromium fix to Edge’s update channel.
Electron is trickier. Many Electron apps lag behind current Chromium builds, and not every Chromium security issue maps cleanly to every embedded app. But security teams should at least know which business-critical apps ship their own browser engine, because “we patched Chrome” does not necessarily mean “we patched Chromium everywhere.”
But restricted details are not secrecy theater. Once a patch is published, attackers can diff code changes, infer the vulnerable path, and build exploit hypotheses. Full public details can accelerate that process, particularly before automatic updates have reached a majority of users.
The practical defender response is to avoid waiting for exploit code. By the time a polished proof-of-concept appears, the patch window has already been wasted. The publication of the CVE, affected version range, and fixed version is enough to act.
There is also no public indication in the supplied CVE details that CVE-2026-7946 is known to be exploited in the wild. That matters. It should temper alarmist claims. It should not slow routine browser patching.
That kind of bug is especially interesting because it sits between software engineering and security design. The code may behave exactly as written. The problem is that the written behavior does not enforce the intended trust model.
WebUI is a natural place for these mismatches. Internal pages need to communicate with browser services. They may be reachable through special schemes, privileged bindings, or navigation rules that ordinary web pages cannot use. Each exception is a small security contract.
CVE-2026-7946 appears to be one of those contracts gone wrong. The lesson for Chromium is narrow and technical. The lesson for everyone else is broader: when web technologies are used to build privileged UI, the web’s threat model comes along for the ride.
For enterprise administrators, the work is less glamorous. Inventory all Chrome installations, confirm channel policy, check whether update deferrals apply, verify active version reporting, and look for unmanaged installs. Pay special attention to systems where users have local installation rights or where browsers are bundled into golden images and nonpersistent desktops.
There is also a communication problem. Users have been trained to ignore relaunch prompts because browser updates arrive constantly. If a fixed build is downloaded but the browser stays open for days, the patch is functionally incomplete.
That is why forced relaunch policies matter. They are annoying. They are also one of the few ways to close the gap between “patched version available” and patched browser actually running.
Security teams should resist the urge to overfit their response to the medium rating. A renderer prerequisite makes exploitation more conditional, but it does not make the bug irrelevant. Browser chains are built from conditional bugs.
Administrators should also avoid assuming that Chrome’s auto-update machinery solves the entire problem. It solves distribution. It does not solve user relaunch behavior, fleet visibility, ChromeOS channel timing, third-party Chromium derivatives, or unmanaged devices.
The right posture is boring by design: update quickly, verify aggressively, and treat missed browser updates as endpoint exposure rather than user preference.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 The Medium Rating Hides the Real Shape of the Risk
The Medium Rating Hides the Real Shape of the Risk
CVE-2026-7946 is not described as a classic “visit a page and get owned” vulnerability. The public wording says the attacker first needs to have compromised the renderer process, and only then can the crafted HTML page be used to bypass site isolation. That prerequisite is why the score lands in the medium range rather than among the red-alert bugs that promise immediate code execution from a single click.But that distinction can be misleading for anyone who has watched browser exploitation evolve. A modern browser attack chain is often assembled from pieces: one bug to gain code execution in a renderer, another to escape the sandbox, another to cross a boundary the browser had promised would contain the damage. CVE-2026-7946 appears to live in that middle territory, where the attacker is not starting from zero but is trying to turn a beachhead into something more useful.
That is why “medium” should not be read as “low priority.” In isolation, the bug leaks or weakens a containment boundary. In a chain, it can become the part that makes an otherwise limited renderer compromise more valuable.
The CISA-ADP vector published with the entry tells the same story in security shorthand: network attack vector, low complexity, no privileges, user interaction required, and low confidentiality impact. That is not catastrophic on paper. It is also not nothing, especially when the impacted software is Chrome across Windows, macOS, Linux, and ChromeOS before the fixed build.
Site Isolation Was the Wall Chrome Built After Spectre
To understand why this bug matters, it helps to remember what site isolation was built to defend. Chrome’s multi-process architecture was not simply a performance trick or a crash-containment feature. It became a security architecture: different sites should live in different renderer processes so that a compromised page from one origin cannot casually inspect or interfere with another.Spectre made that philosophy urgent. If speculative execution could be abused to infer data across boundaries, then the browser needed stronger boundaries between mutually distrusting web content. Site isolation was Chrome’s answer: put sites in separate process silos, reduce the blast radius, and make the renderer compromise less catastrophic.
That model has held up well enough to become part of the security baseline users rarely think about. The browser does not just render pages; it enforces a geopolitical map of the web, with origins, frames, processes, privileges, and policies standing in for borders.
CVE-2026-7946 is troubling because it points at the bureaucracy of that map. The bug is not described as a raw memory corruption failure. It is “insufficient policy enforcement in WebUI,” which suggests a failure in how the browser applied internal rules to privileged browser-facing interfaces.
WebUI Is Where the Browser Stops Being Just a Browser
Chrome’s WebUI surfaces are the browser’s own internal web-like pages: settings, diagnostics, management views, permissions surfaces, and other browser-controlled interfaces that look and behave like web pages but are not ordinary websites. They sit at an awkward intersection. They use web technologies, but they often expose browser internals or privileged functionality.That makes WebUI security particularly delicate. If ordinary web content is the public street, WebUI is closer to the administrative lobby. It may still have familiar doors and windows, but the access rules are supposed to be stricter.
The CVE wording says insufficient policy enforcement in WebUI allowed a renderer-compromising attacker to bypass site isolation. That is a compact description, but the implication is clear enough: some internal rule that should have preserved the separation between sites, processes, or privileged contexts did not hold under crafted conditions.
Google has not publicly exposed the full issue details, which is normal for Chromium bugs while users are still being updated. The restraint is defensible; publishing exploit mechanics too early helps attackers more than defenders. But the lack of detail also means administrators must treat the vendor’s boundary description seriously rather than waiting for a proof-of-concept to make the risk feel real.
The Renderer Compromise Requirement Is a Guardrail, Not a Comfort Blanket
It is tempting to shrug at any browser bug that begins with “after compromising the renderer.” After all, if the attacker is already in the renderer, something has already gone badly wrong. But browser security is built on the assumption that renderers are hostile territory.That is the entire point of the sandboxed renderer model. Web content is too complex, too dynamic, and too exposed to be trusted absolutely. JavaScript engines, layout engines, media parsers, graphics stacks, font handling, extension surfaces, and IPC plumbing all create opportunities for mistakes. The renderer is where much of that attack surface lives.
So when a vulnerability assumes a compromised renderer, it is not assuming science fiction. It is assuming one of the most common starting points in serious browser exploitation.
The security question is what happens next. Can the attacker only disturb the malicious tab? Can they read cross-site data? Can they access internal browser pages? Can they pivot into a more privileged process? CVE-2026-7946 is significant because it appears to weaken a boundary that exists precisely to answer those questions with “no.”
Microsoft’s Appearance in the Advisory Is Not a Footnote
The user-visible source for many Windows administrators will be Microsoft’s Security Update Guide, not Google’s release blog. That matters because Chromium is no longer just Google Chrome’s problem. Microsoft Edge rides the same engine family, and Windows shops increasingly consume Chromium vulnerability intelligence through MSRC, enterprise vulnerability scanners, endpoint management dashboards, and compliance pipelines.When a Chrome CVE appears in Microsoft’s ecosystem, it reinforces a shift that has already happened: the browser engine is shared infrastructure. Chromium bugs ripple into Edge, embedded web views, managed desktop baselines, and third-party applications that depend on Chromium components.
The CVE itself names Google Chrome on Linux, Mac, Windows, and ChromeOS prior to 148.0.7778.96. Microsoft’s publication of the entry is part of a broader vendor coordination reality, not evidence that this is a Windows-only defect.
That distinction is important for IT teams. The right operational question is not “Is this a Microsoft bug or a Google bug?” It is “Where do Chromium-based browsers and components exist in my environment, and are they actually patched?”
Chrome 148 Was a Security Release Wearing a Feature Release’s Jacket
Chrome 148 reached the stable channel for desktop on May 5, 2026, with version 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS. Google’s initial release notes said the update contained fixes and improvements, with security details updated afterward. That staggered disclosure pattern is familiar: ship the update, give the ecosystem time to move, and then fill in the vulnerability ledger.The scale of the security work around Chrome 148 is notable. Contemporary reporting put the number of security fixes above 100, with multiple critical vulnerabilities in the same release family. CVE-2026-7946 is therefore not the headline-grabbing member of the class. It is one of the quieter bugs in a very large patch train.
That quietness is exactly why it deserves attention. Critical memory-safety bugs trigger alarms because they are easy to explain. A medium-severity WebUI policy failure that matters after renderer compromise is harder to put on a dashboard, but it may still be relevant to attackers building chains.
Patch management tends to chase severity labels. Attackers chase composability.
The CPE Question Points to a Bigger Inventory Problem
The NVD change history for CVE-2026-7946 added a vulnerable Chrome CPE up to, but excluding, 148.0.7778.96, combined with operating-system CPEs for Windows, ChromeOS, Linux kernel, and macOS. The page also includes the familiar “Are we missing a CPE?” prompt, which is less a bureaucratic aside than a warning about how messy software inventory has become.CPEs are supposed to make vulnerabilities machine-readable. In theory, a scanner can map installed products to known vulnerable versions and generate a clean answer. In practice, browser packaging, enterprise channels, embedded runtimes, managed update deferrals, and vendor-specific rebuilds complicate that picture.
Chrome is particularly slippery because the version number is the real anchor. A Windows host, a Mac laptop, a Linux workstation, and a ChromeOS device may all be affected by the same Chromium defect, but the update path, cadence, and administrative control plane differ substantially.
So, yes, organizations may find that asset tools miss something. They may also find that the CPE exists but the installed product data is stale, incomplete, or hidden behind user-level installation paths. The cure is not to obsess over the CPE entry; it is to verify browser versions directly.
ChromeOS Makes the Timing More Awkward
ChromeOS is listed in the affected platforms, which adds a wrinkle for schools, kiosks, frontline devices, and tightly managed fleets. A desktop Chrome update can usually be nudged through browser relaunch prompts or endpoint tooling. ChromeOS updates are more deeply tied to the device OS update channel and fleet policy.That does not make ChromeOS uniquely vulnerable. In some ways, ChromeOS is one of the cleanest examples of a browser-first security model. But it does mean organizations need to watch channel availability and update enforcement, not just CVE publication.
For admins, the practical question is whether devices have actually crossed the fixed-version line. A vulnerability description that says “prior to 148.0.7778.96” is not satisfied by a policy that merely allows updates. It is satisfied by devices reporting the patched build.
This is where consumer security advice and enterprise reality diverge. “Update Chrome” is sufficient advice for an individual user. A fleet owner needs proof, timing, exception handling, rollback awareness, and a plan for devices that sit offline until the worst possible moment.
The Browser Has Become the Enterprise Perimeter
A decade ago, browser patching could be treated as desktop hygiene. Today it is perimeter defense. SaaS applications, identity providers, admin consoles, password managers, device enrollment flows, source-code systems, remote access portals, and customer databases all pass through the browser.That is why a site isolation bypass matters even when its stated confidentiality impact is low. The browser is where identities are active, sessions are warm, and cross-origin assumptions are doing constant security work. Weakening those assumptions can be more dangerous than the CVSS line suggests.
Attackers do not need every browser bug to be a full sandbox escape. Sometimes they need a way to read something they should not, influence a privileged flow, or combine a limited renderer foothold with a policy confusion. Modern exploitation often looks less like smashing one giant wall and more like finding three doors that each close imperfectly.
Defenders, meanwhile, have inherited a paradox. The browser is one of the most aggressively updated pieces of software on the endpoint, but it is also one of the most exposed. Fast updates are necessary because the target never stops moving.
Severity Scores Are Useful Until They Become a Substitute for Judgment
CVSS is valuable because it gives security teams a common vocabulary. It is also dangerous when used as a sorting machine without context. CVE-2026-7946’s CISA-ADP base score of 4.3 reflects the information available: user interaction required, no privileges, low confidentiality impact, and no direct integrity or availability impact.That score does not capture every meaningful operational detail. It does not know whether a vulnerable browser is used by a domain admin. It does not know whether the environment runs a high-risk SaaS estate through Chrome. It does not know whether the organization has recently seen browser-based phishing, malvertising, or drive-by attempts.
Nor does it capture exploit chain economics. A medium bug in a heavily deployed browser can be worth more than a high bug in a rarely exposed component. Attackers care about reach, reliability, stealth, and how well a bug combines with others.
The right reading is not “ignore medium.” It is “treat medium browser boundary bugs as patch-now unless there is a better reason not to.”
The Release Cadence Is Now Part of the Security Model
Chrome’s rapid update cadence is sometimes derided as churn, especially by users who feel the browser is always asking to relaunch. But that churn is the security model. The web platform is too large and too adversarial for slow patch cycles to be comfortable.Chrome 148’s rollout language — coming over days or weeks — is normal, but normal does not mean ideal for every environment. Staged rollout reduces the blast radius of bad updates. It also creates a window in which fixed bugs are known, unfixed clients remain common, and attackers can begin studying the patch delta.
That window is one reason enterprises increasingly need more control, not less. Auto-update is excellent for unmanaged users. Managed environments need rings, telemetry, forced relaunch deadlines, and exception processes that do not become permanent loopholes.
The worst compromise is the one many organizations drift into: updates are automatic in theory, delayed in practice, and unverified in reporting. CVE-2026-7946 is exactly the kind of bug that can disappear from attention before the fleet is actually clean.
Edge, Electron, and the Chromium Spillover Problem
Although the public CVE wording names Google Chrome, Chromium vulnerabilities rarely stay emotionally contained inside Chrome. Microsoft Edge, Brave, Vivaldi, Opera, Electron applications, embedded Chromium frameworks, and webview-based tools all inhabit the same broad ecosystem, even when their patch timelines and exposure differ.That does not mean every Chromium consumer is automatically affected in the same way. A WebUI policy enforcement bug may depend on Chrome-specific internal surfaces, feature flags, or UI plumbing. But the prudent response is to check vendor advisories for every Chromium-derived browser in the estate.
Microsoft Edge deserves special attention in Windows environments because it is both a browser and a platform dependency. Organizations that standardized on Edge may still see the CVE through Chrome-oriented feeds, then need to map the underlying Chromium fix to Edge’s update channel.
Electron is trickier. Many Electron apps lag behind current Chromium builds, and not every Chromium security issue maps cleanly to every embedded app. But security teams should at least know which business-critical apps ship their own browser engine, because “we patched Chrome” does not necessarily mean “we patched Chromium everywhere.”
Public Bug Details Are Restricted for a Reason
The Chromium issue tracker reference for CVE-2026-7946 requires permissions, which is common for security bugs while disclosure is controlled. This is often frustrating for defenders who want to understand exploitability, test mitigations, or explain risk to leadership.But restricted details are not secrecy theater. Once a patch is published, attackers can diff code changes, infer the vulnerable path, and build exploit hypotheses. Full public details can accelerate that process, particularly before automatic updates have reached a majority of users.
The practical defender response is to avoid waiting for exploit code. By the time a polished proof-of-concept appears, the patch window has already been wasted. The publication of the CVE, affected version range, and fixed version is enough to act.
There is also no public indication in the supplied CVE details that CVE-2026-7946 is known to be exploited in the wild. That matters. It should temper alarmist claims. It should not slow routine browser patching.
WebUI Bugs Show Why Internal Browser Surfaces Need Threat Modeling
Browser vendors have spent enormous effort hardening engines, sandboxes, IPC layers, and memory allocators. WebUI bugs remind us that policy logic is just as important. A boundary can fail not because a pointer is corrupted, but because a privileged internal page accepts a state transition it should reject.That kind of bug is especially interesting because it sits between software engineering and security design. The code may behave exactly as written. The problem is that the written behavior does not enforce the intended trust model.
WebUI is a natural place for these mismatches. Internal pages need to communicate with browser services. They may be reachable through special schemes, privileged bindings, or navigation rules that ordinary web pages cannot use. Each exception is a small security contract.
CVE-2026-7946 appears to be one of those contracts gone wrong. The lesson for Chromium is narrow and technical. The lesson for everyone else is broader: when web technologies are used to build privileged UI, the web’s threat model comes along for the ride.
The Fix Is Simple; The Assurance Is Not
For individual users, the action is straightforward: update Chrome to 148.0.7778.96 or later, or the corresponding 148.0.7778.97 build where offered on Windows and macOS. Relaunch the browser, verify the version, and do not assume the update has applied merely because it downloaded.For enterprise administrators, the work is less glamorous. Inventory all Chrome installations, confirm channel policy, check whether update deferrals apply, verify active version reporting, and look for unmanaged installs. Pay special attention to systems where users have local installation rights or where browsers are bundled into golden images and nonpersistent desktops.
There is also a communication problem. Users have been trained to ignore relaunch prompts because browser updates arrive constantly. If a fixed build is downloaded but the browser stays open for days, the patch is functionally incomplete.
That is why forced relaunch policies matter. They are annoying. They are also one of the few ways to close the gap between “patched version available” and patched browser actually running.
The Patch Window Is Where Policy Becomes Reality
The operational response to CVE-2026-7946 should be measured but firm. This is not a reason to panic, disable Chrome, or rewrite browser strategy overnight. It is a reason to tighten the update muscle that every organization already knows it needs.Security teams should resist the urge to overfit their response to the medium rating. A renderer prerequisite makes exploitation more conditional, but it does not make the bug irrelevant. Browser chains are built from conditional bugs.
Administrators should also avoid assuming that Chrome’s auto-update machinery solves the entire problem. It solves distribution. It does not solve user relaunch behavior, fleet visibility, ChromeOS channel timing, third-party Chromium derivatives, or unmanaged devices.
The right posture is boring by design: update quickly, verify aggressively, and treat missed browser updates as endpoint exposure rather than user preference.
The Concrete Work Starts at Version 148.0.7778.96
CVE-2026-7946 is a narrow vulnerability, but the response pattern is broad enough to be worth spelling out. The lesson is not that every medium CVE deserves emergency-war-room treatment. The lesson is that browser boundary bugs deserve to be handled with the seriousness of infrastructure defects.- Chrome installations older than 148.0.7778.96 should be treated as vulnerable for this CVE.
- Windows and macOS systems may report 148.0.7778.96 or 148.0.7778.97 depending on the channel and rollout path.
- A downloaded browser update is not complete until Chrome has relaunched into the fixed build.
- Managed ChromeOS fleets need version verification, not just an update policy that permits the fixed release.
- Chromium-based browsers and embedded Chromium runtimes should be checked against their own vendor advisories rather than assumed safe because Chrome has been patched.
- The medium severity rating should not override the fact that site isolation is a core browser containment boundary.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center