Google and Microsoft disclosed CVE-2026-7955 on May 6, 2026, a medium-severity Chromium GPU flaw fixed in Google Chrome before version 148.0.7778.96 and tracked by Microsoft because Edge inherits the same Chromium codebase. The bug is not the headline-grabbing remote-code-execution monster that usually drives emergency patching, but it is exactly the kind of browser weakness enterprise defenders should stop dismissing as “only medium.” Its value is not in breaking into the browser by itself; its value is in what it may reveal after another exploit has already put an attacker inside the renderer sandbox. In modern browser security, that second step is often where the real campaign begins.
CVE-2026-7955 is described as an uninitialized use in Chromium’s GPU component. In plain English, some part of the browser’s graphics pipeline could expose data that had not been properly cleared before being reused, allowing a remote attacker with a compromised renderer process to obtain potentially sensitive information from process memory through a crafted HTML page.
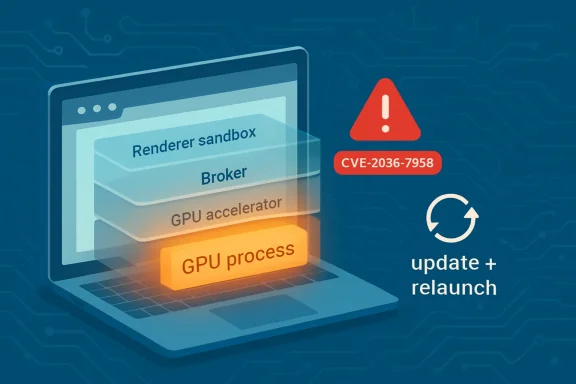
That condition matters because Chrome and Edge are not single-process applications anymore. They are compartmentalized systems: renderer processes handle web content, broker processes enforce privileges, and GPU processes accelerate rendering, video, WebGL, WebGPU, canvas operations, and a growing amount of browser-visible computation. The security model assumes that hostile web content will eventually find bugs in the renderer, so the browser’s job is to keep that foothold boxed in.
CVE-2026-7955 weakens that assumption. It does not appear, from the public description, to hand an attacker direct code execution. But it may let an attacker who already has renderer compromise peer into memory that should not be visible. That makes it a classic exploit-chain ingredient: not the lockpick, but the flashlight.
The uncomfortable truth for Windows administrators is that Chromium has become part of the operating environment whether or not an organization thinks of itself as a “Chrome shop.” Chrome, Edge, Electron apps, WebView2-based business tools, browser extensions, and embedded web surfaces all broaden the practical blast radius of Chromium bugs. A medium Chromium CVE can become a fleet hygiene issue very quickly.
A modern browser does not merely paint text and images. It decodes video, runs shader programs, composites layers, handles WebGL and WebGPU workloads, processes canvas data, and talks through translation layers such as ANGLE to reach Direct3D, OpenGL, Vulkan, Metal, or platform-specific driver stacks. Each of those boundaries is a negotiation between web-exposed APIs, browser validation code, operating-system graphics interfaces, and vendor GPU drivers.
That complexity is why “uninitialized use in GPU” deserves more attention than the phrase initially suggests. Uninitialized memory bugs are old, almost boring, software defects: a program reads data before setting it to a known safe value. In a browser GPU context, however, the relevant question is not whether the defect is conceptually novel. It is what kind of data may be adjacent, what process boundary is involved, and whether the leak helps defeat address randomization, expose cross-origin artifacts, or reveal information useful for a later sandbox escape.
The public CVE wording says the attacker must already have compromised the renderer process. That requirement is important, but it is not comforting. Browser exploit chains routinely begin in the renderer because that is where arbitrary websites get the most direct interaction with parsing, scripting, layout, media, and graphics code. Once there, attackers want primitives: memory disclosure, type confusion, address leaks, policy bypasses, and eventually code execution outside the sandbox.
CVE-2026-7955 sits in that middle territory. It is not necessarily the vulnerability that starts the intrusion. It is the vulnerability that may make the next stage more reliable.
That is how browser risk often hides in plain sight. A release containing critical memory-corruption bugs naturally draws attention to the top of the advisory. Security teams triage by severity because they have to; patch queues are endless, maintenance windows are scarce, and every update has operational consequences. But chained exploitation does not respect the neat order of a CVSS table.
The CISA-ADP vector for CVE-2026-7955 gives it a 5.3 medium score under CVSS 3.1, with network attack vector, high attack complexity, no privileges required, user interaction required, unchanged scope, high confidentiality impact, and no integrity or availability impact. That is a revealing combination. The bug is not scored as easy to exploit, and it does not claim system takeover. But the confidentiality impact is high, meaning the concern is meaningful information exposure, not mere application noise.
The most telling phrase is “who had compromised the renderer process.” That single condition demotes the score while simultaneously explaining why serious attackers may care. It says this is not a standalone drive-by-to-system exploit. It also says the vulnerability is relevant precisely in the scenario defenders worry about most: a hostile page has already gained a foothold inside the browser.
For WindowsForum readers, that distinction should shape the patch conversation. If you are protecting unmanaged home systems, the instruction is simple: update the browser and relaunch it. If you are managing hundreds or thousands of endpoints, the question is whether your vulnerability management process treats browser component flaws as a fast lane or lets them wait for the next comfortable desktop patch cycle.
This is where the modern Windows security model becomes messier than old Patch Tuesday muscle memory. Edge updates are not the same thing as cumulative Windows updates. Chrome updates are not the same thing as Microsoft Defender platform updates. WebView2 runtimes may update independently again. In many environments, the browser is now a high-frequency security component that moves on a different clock from the operating system.
That creates a governance gap. Some organizations have strong controls for monthly Windows servicing but weaker visibility into browser build drift. Others allow Chrome and Edge to self-update but delay relaunches for days because users keep sessions open. Still others pin versions for compatibility and forget that pinning a browser is not like pinning a line-of-business DLL. On the web, old code is exposed to hostile input all day long.
CVE-2026-7955 is a useful audit prompt because it is specific and measurable. Chrome prior to 148.0.7778.96 is affected according to the CVE description. Edge administrators should verify the corresponding Microsoft Edge release carrying the Chromium fix rather than assuming Windows Update alone handled it. The practical question is not whether the CVE has a scary enough name. The practical question is whether endpoints are running a Chromium build that postdates the fix.
The answer may vary across normal Chrome, Extended Stable, Edge Stable, Edge Extended Stable, unmanaged Chromium builds, and Linux distribution packages. That variation is why CPE data in vulnerability databases often lags or looks incomplete around newly published browser CVEs. The software ecosystem moves faster than the enrichment layer that tries to describe it.
A CPE can tell a tool that Google Chrome before a certain version is vulnerable on Windows, Linux, or macOS. It may not capture every embedded Chromium runtime, every portable browser, every Electron application, every custom Chromium build, or every third-party product that borrowed the vulnerable code and ships updates on its own timetable. In other words, the CPE is a map, not the terrain.
This distinction has become more important as the browser has dissolved into the application platform. Microsoft Teams, Slack, Discord, Visual Studio Code, countless admin consoles, identity portals, VPN dashboards, and helpdesk systems all depend on web technologies somewhere in the stack. Not all of them expose the same attack surface as full Chrome or Edge, and not all are affected by this specific CVE. But an organization that only inventories “browsers” is already behind the architecture.
For CVE-2026-7955 specifically, the public description names Google Chrome prior to 148.0.7778.96 and Microsoft tracks the issue for Chromium-based Edge. That is enough to drive immediate browser patching. It is not enough to declare every Chromium-derived surface safe. The responsible move is to use the CVE as a trigger for checking the browser estate first, then reviewing whether any managed applications bundle Chromium components that require separate vendor updates.
Security teams often ask whether a missing CPE means a product is not affected. The better default is the reverse: absence from the database means the database has not proven the product affected, not that engineering has proven it safe. That distinction saves time when the next Chromium advisory lands, because the workflow becomes evidence-based rather than CPE-dependent.
The renderer is the browser’s blast chamber. It processes hostile HTML, JavaScript, CSS, images, fonts, media, and increasingly complex graphics workloads. Chrome’s site isolation and sandboxing improvements have made renderer compromise less catastrophic than it used to be, but they have not made renderer bugs irrelevant. They have changed the attacker’s job from “get code execution” to “get code execution and then escape the box.”
Information leaks are one way to make that job easier. Modern exploit mitigations rely heavily on uncertainty: address space layout randomization, pointer authentication on some platforms, heap hardening, process isolation, and permission boundaries all make exploitation less deterministic. If an attacker can leak useful process memory, some of that uncertainty disappears.
That is why a confidentiality-only flaw can matter in an exploit chain even if it does not corrupt data or crash the application. The leak may reveal memory layout, stale objects, cross-origin data, tokens, graphics buffers, or other artifacts depending on the exact bug. The public record for CVE-2026-7955 does not provide enough detail to say what was practically exposed. Google’s linked Chromium issue is restricted, as is common until enough users are patched.
The lack of technical detail should not be misread as lack of risk. Browser vendors deliberately hold back exploit specifics to avoid handing attackers a recipe while update adoption is still in progress. That opacity is frustrating for defenders who want to prioritize precisely, but it is also part of the patching bargain. When the vendor says the affected version is before 148.0.7778.96, the actionable intelligence is the version boundary.
That does not mean CVE-2026-7955 is a driver vulnerability. The CVE names Chromium’s GPU component, not NVIDIA, AMD, Intel, Apple, or Mesa. But the broader attack surface is shaped by the handoff between browser validation and graphics execution. The more capability the web gains through APIs like WebGL and WebGPU, the more important it becomes that every layer initializes, validates, clears, and isolates data correctly.
For sysadmins, this is another argument against treating browser updates and driver updates as unrelated hygiene chores. A fully patched browser sitting on years-old graphics drivers may still have a larger graphics attack surface than necessary. A current GPU driver running under an outdated browser is no better. The security posture is the combination, not the individual version number that happens to be easiest to scan.
The enterprise complication is that graphics drivers are often among the most carefully delayed updates in business fleets. CAD workstations, medical-imaging systems, trading desks, conference-room PCs, and VDI environments may all carry GPU-specific compatibility risks. That is understandable. It is also why the browser’s GPU sandbox and rapid patch cadence matter so much: they are the more frequently serviced line of defense in an area where driver updates may move slowly.
CVE-2026-7955 should therefore be seen as part of a wider pattern, not a one-off curiosity. GPU acceleration has become a first-class browser feature, and first-class features become first-class attack surfaces. The web’s visual layer is now security-relevant infrastructure.
That sounds trivial until you look at real office behavior. Users keep browsers open for weeks. They suspend laptops instead of rebooting. They treat tab state as working memory. They dismiss update prompts because the browser is where their work lives. In organizations that pride themselves on rapid patch deployment, browser relaunch latency is often the hidden delay.
Administrators have tools to address that delay, but they come with social cost. Managed Chrome and Edge policies can notify users, enforce relaunch windows, and eventually force restarts. The tighter the window, the more likely users are to lose unsaved web app state. The looser the window, the longer the vulnerable code remains live. Browser patching is no longer just package delivery; it is user-session management.
That tradeoff should be explicit. A medium-severity confidentiality bug like CVE-2026-7955 may not justify the same emergency disruption as an actively exploited critical zero-day. But if it ships alongside critical fixes in the same Chrome 148 security release, the fleet decision should be based on the bundle, not the single CVE. In practice, most enterprises are not choosing whether to patch CVE-2026-7955 alone. They are choosing how quickly to take the entire stable-channel security update.
Home users should also remember that Chromium-based browsers are not all updated by the same mechanism. Chrome’s menu can show the current version under About Google Chrome. Edge has a similar About Microsoft Edge page. Linux distributions may ship Chromium through repository packages, snaps, or other channels. If the reported version remains below the fixed boundary, the system is not done.
They should not keep urgency out of the room. In exploit engineering, sequence matters. A vulnerability that is mediocre by itself can be excellent in combination with another bug. A memory disclosure primitive may be the difference between an unreliable crash and a stable exploit chain. A sandbox-adjacent information leak may not be the star of the advisory, but it may be part of the attacker’s route map.
This is especially true for browsers because the attacker controls so much input. A crafted HTML page can combine markup, script, media, graphics calls, timing, memory pressure, and user interaction into a single delivery vehicle. Even when a CVE says “user interaction required,” that interaction may be nothing more exotic than visiting a page or opening a link in a browser that processes content automatically.
The operational lesson is not to inflate every medium CVE into an emergency. It is to stop reading severity as a synonym for usefulness. Defenders should ask what role a bug plays. Does it provide initial access, privilege escalation, sandbox escape, information disclosure, persistence, or detection evasion? CVE-2026-7955 appears to live in the information-disclosure tier, but in a browser exploit chain that tier can be strategically important.
A good vulnerability management program therefore treats browser advisories as packages of risk. The top CVEs tell you why the release is urgent. The medium CVEs tell you how broad and complex the attack surface has become. Together, they tell you whether your patch process is keeping up with the software your users expose to the open web every hour.
For Windows administrators, Edge deserves special attention because it lives in a Microsoft-managed world but follows Chromium’s security tempo. Many organizations have learned to track Windows cumulative updates, Defender updates, Office updates, and firmware advisories. Edge sits across those categories: it is a Microsoft product, a Chromium product, an application runtime, and in many workflows the default gateway to identity, SaaS, and administration portals.
Chrome brings its own management surface, especially in mixed environments where developers, power users, or business units install it alongside Edge. That coexistence is not inherently bad. It becomes risky when one browser is managed and the other is merely tolerated. Attackers do not care which icon the user clicks; they care which exposed parser, renderer, extension, or GPU path is vulnerable.
A mature response starts with inventory. Which browsers are installed? Which channels are allowed? Which versions are running? How quickly do they update? How long do users defer relaunches? Which machines are stuck because of policy, compatibility, offline status, or broken update services? Those questions are unglamorous, but they matter more than arguing whether a 5.3 score sounds scary.
The answer should also include detection. Security teams can watch for outdated browser versions, abnormal child processes, suspicious renderer crashes, exploit-kit traffic, and unusual GPU process behavior where telemetry allows. CVE-2026-7955 itself may not have public exploitation detail, but browser exploit attempts often leave surrounding signals. Patch first, then hunt where exposure was longest.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 The Medium Bug That Belongs in a High-Risk Patch Window
The Medium Bug That Belongs in a High-Risk Patch Window
CVE-2026-7955 is described as an uninitialized use in Chromium’s GPU component. In plain English, some part of the browser’s graphics pipeline could expose data that had not been properly cleared before being reused, allowing a remote attacker with a compromised renderer process to obtain potentially sensitive information from process memory through a crafted HTML page.That condition matters because Chrome and Edge are not single-process applications anymore. They are compartmentalized systems: renderer processes handle web content, broker processes enforce privileges, and GPU processes accelerate rendering, video, WebGL, WebGPU, canvas operations, and a growing amount of browser-visible computation. The security model assumes that hostile web content will eventually find bugs in the renderer, so the browser’s job is to keep that foothold boxed in.
CVE-2026-7955 weakens that assumption. It does not appear, from the public description, to hand an attacker direct code execution. But it may let an attacker who already has renderer compromise peer into memory that should not be visible. That makes it a classic exploit-chain ingredient: not the lockpick, but the flashlight.
The uncomfortable truth for Windows administrators is that Chromium has become part of the operating environment whether or not an organization thinks of itself as a “Chrome shop.” Chrome, Edge, Electron apps, WebView2-based business tools, browser extensions, and embedded web surfaces all broaden the practical blast radius of Chromium bugs. A medium Chromium CVE can become a fleet hygiene issue very quickly.
The GPU Is No Longer Just Drawing the Web
For years, browser GPU bugs were easy to mentally file under graphics weirdness: crashes, black rectangles, driver instability, the kind of thing users complained about after a bad update. That view is outdated. The GPU process is now one of the browser’s most important attack surfaces because the web increasingly treats graphics hardware as a general-purpose accelerator.A modern browser does not merely paint text and images. It decodes video, runs shader programs, composites layers, handles WebGL and WebGPU workloads, processes canvas data, and talks through translation layers such as ANGLE to reach Direct3D, OpenGL, Vulkan, Metal, or platform-specific driver stacks. Each of those boundaries is a negotiation between web-exposed APIs, browser validation code, operating-system graphics interfaces, and vendor GPU drivers.
That complexity is why “uninitialized use in GPU” deserves more attention than the phrase initially suggests. Uninitialized memory bugs are old, almost boring, software defects: a program reads data before setting it to a known safe value. In a browser GPU context, however, the relevant question is not whether the defect is conceptually novel. It is what kind of data may be adjacent, what process boundary is involved, and whether the leak helps defeat address randomization, expose cross-origin artifacts, or reveal information useful for a later sandbox escape.
The public CVE wording says the attacker must already have compromised the renderer process. That requirement is important, but it is not comforting. Browser exploit chains routinely begin in the renderer because that is where arbitrary websites get the most direct interaction with parsing, scripting, layout, media, and graphics code. Once there, attackers want primitives: memory disclosure, type confusion, address leaks, policy bypasses, and eventually code execution outside the sandbox.
CVE-2026-7955 sits in that middle territory. It is not necessarily the vulnerability that starts the intrusion. It is the vulnerability that may make the next stage more reliable.
Chrome 148 Was a Security Release Wearing a Routine Update’s Clothes
Google’s stable desktop update to Chrome 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS landed in early May with a large security payload. Public reporting and Google’s release notes described more than a hundred fixes in the release, including several critical vulnerabilities elsewhere in Chromium. CVE-2026-7955 was one item in that long list, assigned Chromium’s medium severity rather than critical or high.That is how browser risk often hides in plain sight. A release containing critical memory-corruption bugs naturally draws attention to the top of the advisory. Security teams triage by severity because they have to; patch queues are endless, maintenance windows are scarce, and every update has operational consequences. But chained exploitation does not respect the neat order of a CVSS table.
The CISA-ADP vector for CVE-2026-7955 gives it a 5.3 medium score under CVSS 3.1, with network attack vector, high attack complexity, no privileges required, user interaction required, unchanged scope, high confidentiality impact, and no integrity or availability impact. That is a revealing combination. The bug is not scored as easy to exploit, and it does not claim system takeover. But the confidentiality impact is high, meaning the concern is meaningful information exposure, not mere application noise.
The most telling phrase is “who had compromised the renderer process.” That single condition demotes the score while simultaneously explaining why serious attackers may care. It says this is not a standalone drive-by-to-system exploit. It also says the vulnerability is relevant precisely in the scenario defenders worry about most: a hostile page has already gained a foothold inside the browser.
For WindowsForum readers, that distinction should shape the patch conversation. If you are protecting unmanaged home systems, the instruction is simple: update the browser and relaunch it. If you are managing hundreds or thousands of endpoints, the question is whether your vulnerability management process treats browser component flaws as a fast lane or lets them wait for the next comfortable desktop patch cycle.
Microsoft’s Role Is a Reminder That Edge Is Chromium With a Windows Address
The MSRC entry for CVE-2026-7955 exists because Microsoft Edge is Chromium-based. Microsoft does not need to have written the vulnerable GPU code for Windows administrators to own the remediation problem. When a Chromium bug lands upstream, Edge customers still need to know whether their deployed browser channel contains the fix.This is where the modern Windows security model becomes messier than old Patch Tuesday muscle memory. Edge updates are not the same thing as cumulative Windows updates. Chrome updates are not the same thing as Microsoft Defender platform updates. WebView2 runtimes may update independently again. In many environments, the browser is now a high-frequency security component that moves on a different clock from the operating system.
That creates a governance gap. Some organizations have strong controls for monthly Windows servicing but weaker visibility into browser build drift. Others allow Chrome and Edge to self-update but delay relaunches for days because users keep sessions open. Still others pin versions for compatibility and forget that pinning a browser is not like pinning a line-of-business DLL. On the web, old code is exposed to hostile input all day long.
CVE-2026-7955 is a useful audit prompt because it is specific and measurable. Chrome prior to 148.0.7778.96 is affected according to the CVE description. Edge administrators should verify the corresponding Microsoft Edge release carrying the Chromium fix rather than assuming Windows Update alone handled it. The practical question is not whether the CVE has a scary enough name. The practical question is whether endpoints are running a Chromium build that postdates the fix.
The answer may vary across normal Chrome, Extended Stable, Edge Stable, Edge Extended Stable, unmanaged Chromium builds, and Linux distribution packages. That variation is why CPE data in vulnerability databases often lags or looks incomplete around newly published browser CVEs. The software ecosystem moves faster than the enrichment layer that tries to describe it.
The Missing-CPE Anxiety Is Really an Asset-Inventory Problem
The user-facing NVD text around CVE-2026-7955 includes the familiar vulnerability-database uncertainty: affected software configurations may still be loading, enrichment may not be complete, and users are invited to report missing CPEs. That can look like a clerical issue, but for defenders it points to a deeper problem. CPEs are useful for scanners, not sufficient for reality.A CPE can tell a tool that Google Chrome before a certain version is vulnerable on Windows, Linux, or macOS. It may not capture every embedded Chromium runtime, every portable browser, every Electron application, every custom Chromium build, or every third-party product that borrowed the vulnerable code and ships updates on its own timetable. In other words, the CPE is a map, not the terrain.
This distinction has become more important as the browser has dissolved into the application platform. Microsoft Teams, Slack, Discord, Visual Studio Code, countless admin consoles, identity portals, VPN dashboards, and helpdesk systems all depend on web technologies somewhere in the stack. Not all of them expose the same attack surface as full Chrome or Edge, and not all are affected by this specific CVE. But an organization that only inventories “browsers” is already behind the architecture.
For CVE-2026-7955 specifically, the public description names Google Chrome prior to 148.0.7778.96 and Microsoft tracks the issue for Chromium-based Edge. That is enough to drive immediate browser patching. It is not enough to declare every Chromium-derived surface safe. The responsible move is to use the CVE as a trigger for checking the browser estate first, then reviewing whether any managed applications bundle Chromium components that require separate vendor updates.
Security teams often ask whether a missing CPE means a product is not affected. The better default is the reverse: absence from the database means the database has not proven the product affected, not that engineering has proven it safe. That distinction saves time when the next Chromium advisory lands, because the workflow becomes evidence-based rather than CPE-dependent.
Renderer Compromise Is the Assumption, Not the Edge Case
The phrase “attacker who had compromised the renderer process” can sound like a limiting condition that makes CVE-2026-7955 less urgent. In one sense, it does. A vulnerability requiring a prior renderer compromise is less immediately dangerous than a bug that allows code execution from a clean browser state. But mature browser attackers build chains because the browser is designed to force them to build chains.The renderer is the browser’s blast chamber. It processes hostile HTML, JavaScript, CSS, images, fonts, media, and increasingly complex graphics workloads. Chrome’s site isolation and sandboxing improvements have made renderer compromise less catastrophic than it used to be, but they have not made renderer bugs irrelevant. They have changed the attacker’s job from “get code execution” to “get code execution and then escape the box.”
Information leaks are one way to make that job easier. Modern exploit mitigations rely heavily on uncertainty: address space layout randomization, pointer authentication on some platforms, heap hardening, process isolation, and permission boundaries all make exploitation less deterministic. If an attacker can leak useful process memory, some of that uncertainty disappears.
That is why a confidentiality-only flaw can matter in an exploit chain even if it does not corrupt data or crash the application. The leak may reveal memory layout, stale objects, cross-origin data, tokens, graphics buffers, or other artifacts depending on the exact bug. The public record for CVE-2026-7955 does not provide enough detail to say what was practically exposed. Google’s linked Chromium issue is restricted, as is common until enough users are patched.
The lack of technical detail should not be misread as lack of risk. Browser vendors deliberately hold back exploit specifics to avoid handing attackers a recipe while update adoption is still in progress. That opacity is frustrating for defenders who want to prioritize precisely, but it is also part of the patching bargain. When the vendor says the affected version is before 148.0.7778.96, the actionable intelligence is the version boundary.
GPU Bugs Sit at the Intersection of Browser, Driver, and Operating System
One reason GPU vulnerabilities are awkward to reason about is that the browser is only one layer in a multi-vendor stack. On Windows, Chromium’s graphics work may flow through ANGLE and Direct3D before it reaches the GPU driver. On macOS, the path may involve Metal. On Linux, it may involve Mesa, proprietary drivers, Vulkan, or OpenGL variants. The web page is portable; the graphics stack underneath is not.That does not mean CVE-2026-7955 is a driver vulnerability. The CVE names Chromium’s GPU component, not NVIDIA, AMD, Intel, Apple, or Mesa. But the broader attack surface is shaped by the handoff between browser validation and graphics execution. The more capability the web gains through APIs like WebGL and WebGPU, the more important it becomes that every layer initializes, validates, clears, and isolates data correctly.
For sysadmins, this is another argument against treating browser updates and driver updates as unrelated hygiene chores. A fully patched browser sitting on years-old graphics drivers may still have a larger graphics attack surface than necessary. A current GPU driver running under an outdated browser is no better. The security posture is the combination, not the individual version number that happens to be easiest to scan.
The enterprise complication is that graphics drivers are often among the most carefully delayed updates in business fleets. CAD workstations, medical-imaging systems, trading desks, conference-room PCs, and VDI environments may all carry GPU-specific compatibility risks. That is understandable. It is also why the browser’s GPU sandbox and rapid patch cadence matter so much: they are the more frequently serviced line of defense in an area where driver updates may move slowly.
CVE-2026-7955 should therefore be seen as part of a wider pattern, not a one-off curiosity. GPU acceleration has become a first-class browser feature, and first-class features become first-class attack surfaces. The web’s visual layer is now security-relevant infrastructure.
The Patch Is Simple; The Relaunch Is the Part Everyone Forgets
For individual users, remediation is boring in the best possible way: update Chrome to 148.0.7778.96 or later, or ensure the equivalent fixed Edge version is installed, and relaunch the browser. The relaunch matters because downloaded browser updates often do not fully replace the running process until the application restarts. A patched binary sitting idle on disk does not protect a long-lived vulnerable browser session.That sounds trivial until you look at real office behavior. Users keep browsers open for weeks. They suspend laptops instead of rebooting. They treat tab state as working memory. They dismiss update prompts because the browser is where their work lives. In organizations that pride themselves on rapid patch deployment, browser relaunch latency is often the hidden delay.
Administrators have tools to address that delay, but they come with social cost. Managed Chrome and Edge policies can notify users, enforce relaunch windows, and eventually force restarts. The tighter the window, the more likely users are to lose unsaved web app state. The looser the window, the longer the vulnerable code remains live. Browser patching is no longer just package delivery; it is user-session management.
That tradeoff should be explicit. A medium-severity confidentiality bug like CVE-2026-7955 may not justify the same emergency disruption as an actively exploited critical zero-day. But if it ships alongside critical fixes in the same Chrome 148 security release, the fleet decision should be based on the bundle, not the single CVE. In practice, most enterprises are not choosing whether to patch CVE-2026-7955 alone. They are choosing how quickly to take the entire stable-channel security update.
Home users should also remember that Chromium-based browsers are not all updated by the same mechanism. Chrome’s menu can show the current version under About Google Chrome. Edge has a similar About Microsoft Edge page. Linux distributions may ship Chromium through repository packages, snaps, or other channels. If the reported version remains below the fixed boundary, the system is not done.
CVSS Scores Tell You Severity, Not Sequence
CVSS is useful, but it is often a poor narrator. CVE-2026-7955’s medium score reflects constraints that are real: user interaction is required, attack complexity is high, the renderer must already be compromised, and the public impact is confidentiality rather than integrity or availability. Those facts should keep panic out of the room.They should not keep urgency out of the room. In exploit engineering, sequence matters. A vulnerability that is mediocre by itself can be excellent in combination with another bug. A memory disclosure primitive may be the difference between an unreliable crash and a stable exploit chain. A sandbox-adjacent information leak may not be the star of the advisory, but it may be part of the attacker’s route map.
This is especially true for browsers because the attacker controls so much input. A crafted HTML page can combine markup, script, media, graphics calls, timing, memory pressure, and user interaction into a single delivery vehicle. Even when a CVE says “user interaction required,” that interaction may be nothing more exotic than visiting a page or opening a link in a browser that processes content automatically.
The operational lesson is not to inflate every medium CVE into an emergency. It is to stop reading severity as a synonym for usefulness. Defenders should ask what role a bug plays. Does it provide initial access, privilege escalation, sandbox escape, information disclosure, persistence, or detection evasion? CVE-2026-7955 appears to live in the information-disclosure tier, but in a browser exploit chain that tier can be strategically important.
A good vulnerability management program therefore treats browser advisories as packages of risk. The top CVEs tell you why the release is urgent. The medium CVEs tell you how broad and complex the attack surface has become. Together, they tell you whether your patch process is keeping up with the software your users expose to the open web every hour.
The Sensible Windows Response Is Faster Browser Governance, Not Panic
The practical response to CVE-2026-7955 is not dramatic, but it is disciplined. Confirm versions, force or encourage relaunches, verify Edge separately from Chrome, watch for managed-channel lag, and do not assume that an incomplete CPE listing is a clean bill of health. The more important response is cultural: browsers need to be governed like core infrastructure, not like user preferences.For Windows administrators, Edge deserves special attention because it lives in a Microsoft-managed world but follows Chromium’s security tempo. Many organizations have learned to track Windows cumulative updates, Defender updates, Office updates, and firmware advisories. Edge sits across those categories: it is a Microsoft product, a Chromium product, an application runtime, and in many workflows the default gateway to identity, SaaS, and administration portals.
Chrome brings its own management surface, especially in mixed environments where developers, power users, or business units install it alongside Edge. That coexistence is not inherently bad. It becomes risky when one browser is managed and the other is merely tolerated. Attackers do not care which icon the user clicks; they care which exposed parser, renderer, extension, or GPU path is vulnerable.
A mature response starts with inventory. Which browsers are installed? Which channels are allowed? Which versions are running? How quickly do they update? How long do users defer relaunches? Which machines are stuck because of policy, compatibility, offline status, or broken update services? Those questions are unglamorous, but they matter more than arguing whether a 5.3 score sounds scary.
The answer should also include detection. Security teams can watch for outdated browser versions, abnormal child processes, suspicious renderer crashes, exploit-kit traffic, and unusual GPU process behavior where telemetry allows. CVE-2026-7955 itself may not have public exploitation detail, but browser exploit attempts often leave surrounding signals. Patch first, then hunt where exposure was longest.
The Concrete Moves Before This Advisory Disappears Into the Feed
CVE-2026-7955 will probably not be remembered as one of the defining browser vulnerabilities of 2026. That is precisely why it is useful. It is an ordinary-looking Chromium flaw that exposes how much of endpoint security now depends on fast, boring, repeatable browser maintenance.- Organizations should verify that Google Chrome is updated to 148.0.7778.96 or later on Linux and to the fixed 148.0.7778.96/97 line on Windows and macOS.
- Microsoft Edge administrators should confirm the Edge release that incorporates the Chromium fix instead of assuming a Windows cumulative update remediated the browser.
- Security teams should treat renderer-prerequisite information leaks as exploit-chain risks, not as harmless disclosures.
- Managed environments should measure relaunch latency because an installed browser update may not protect users until the running browser restarts.
- Asset inventories should account for Chromium-derived runtimes and applications where feasible, because CPE coverage may lag behind real-world exposure.
- GPU-related browser bugs should prompt renewed attention to graphics drivers, WebGL and WebGPU exposure, and the broader hardware-accelerated attack surface.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center